Data Security
-
 285
285Tor Hires Top Privacy Advocate Shari Steele As New Executive Director
Tor has hired a former Electronic Frontier Foundation (EFF) executive director to lead its project that is aimed for making the cyber...
-
 276
276MIT Creates Untraceable Anonymous Messaging System Called Vuvuzela
Researchers are still looking for a Tor alternative.Scientists at the MIT Computer Science and Artificial Intelligence Laboratory (CSAIL) have created an anonymous...
-
 161
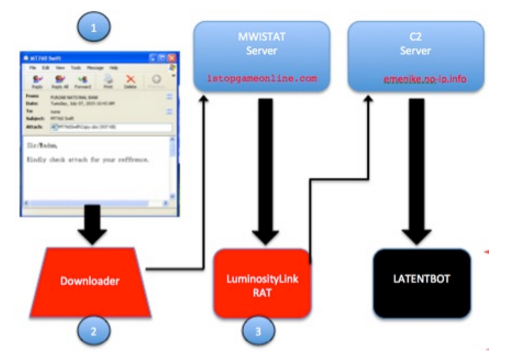
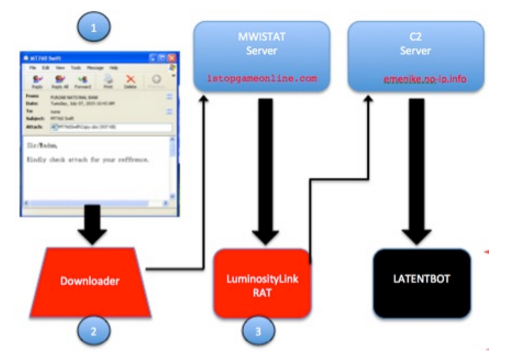
161LATENTBOT, one the highly obfuscated backdoor in the wild
Experts at FireEye have discovered a stealthy botnet relying on a backdoor called LATENTBOT has compromised companies around. Experts at FireEye have discovered...
-

 1.7K
1.7K“Vuvuzela” SMS Text Messaging System More Secure Than Tor
MIT researchers claim they have developed “Vuvuzela” SMS Text Messaging System which is way more secure than Tor and provides guaranteed untraceable communication....
-

 105
105Tor Hires a New Leader to Help It Combat the War on Privacy
THE TOR PROJECT is entering a crucial phase in its nearly 10-year existence. In the wake of the Edward Snowden leaks, it...
-

 197
197The Anonymous GitHub Clone That Runs on the Dark Web
Meet Jeff Becker and his creation: git.psi.i2p. Lots of people seek anonymity these days, for various reasons, may it be because of abusive...
-
 201
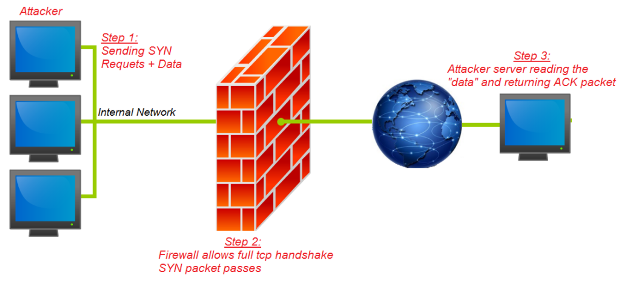
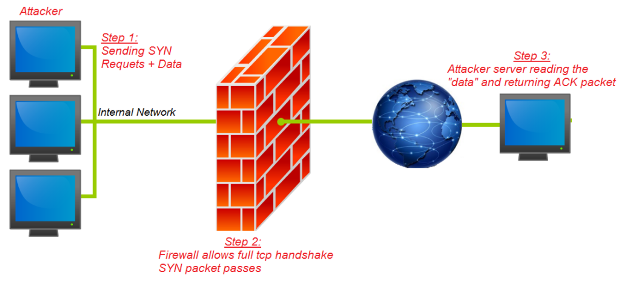
201FireStorm: Severe Security Flaw Discovered in Next Generation Firewalls
BugSec Group and Cynet discovered a severe vulnerability in Next Generation Firewalls. Head of Offensive Security Stas Volfus uncovered the vulnerability, code-named...
-
 159
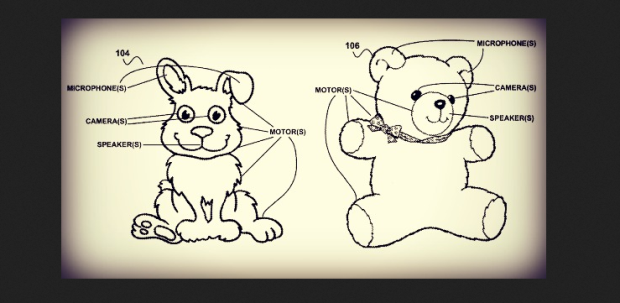
159British spooks ‘could hack into children’s toys for spying’
Tech expert warns that ‘smart toys’ could be hacked in to under powers being proposed in draft Investigatory Powers Bill. Britain’s intelligence...
-

 207
207APT Group Upgrades Malware from the Black Market into Dangerous Backdoor
Cyber-espionage group targeted companies in Asia. Details about the operations of a new cyber-espionage group are emerging, and this gang has been buying...
-

 96
96New Spy Banker Trojan Telax abusing Google Cloud Servers
Introduction Zscaler ThreatLabZ has been closely monitoring a new Spy Banker Trojan campaign that has been targeting Portuguese-speaking users in Brazil. The...
-

 153
153FBI head: terror fight requires open backdoors to encrypted user data
FBI director James Comey called on tech companies to create backdoor access to their users’ data on Wednesday, arguing it was necessary...
-

 167
167Hacker Lexicon: Malvertising, the Hack That Infects Computers Without a Click
MALVERTISING IS WHEN hackers buy ad space on a legitimate website, and, as the name suggests, upload malicious advertisements designed to hack...
-

 157
157Researchers Found Windows’ Malware Similar To The One Used by NSA
NSA’s one of the known snooping tactics is installing a malware into hard drive’s firmware which makes the deletion of the malware...
-

 253
253Bitcoin’s Creator Satoshi Nakamoto Is Probably This Unknown Australian Genius
EVEN AS HIS face towered 10 feet above the crowd at the Bitcoin Investor’s Conference in Las Vegas, Craig Steven Wright was,...
-

 123
123Security Flaw in Honeywell Gas Detectors Can Virtually Kill People
After hacking nuclear plants, Refrigerator, House Arrest Ankle Bracelet, Smartphones GPS Signals, Electronic Skateboards, Driverless Cars, Jeep, Computer Controlled Sniper Rifle and Jeep Cherokee etc, it is now time...
-

 209
209Learn how Eliot from Mr.robot hacked into to his therapist’s new boyfriend’s email and bank accounts
Social engineering is a pretty important item in a hacker’s toolkit.in Mr robot there was a time, we see Elliot, using social...
-

 85
85Personal data of Dutch telecom providers extremely poorly protected: how I could access 12+ million records #phonehousegate
On September 11, 2015 I visited Media Markt in Utrecht Hoog Catherijne, a well-known electronics shop in The Netherlands. Since summer 2014, the biggest independent Dutch...
-
 170
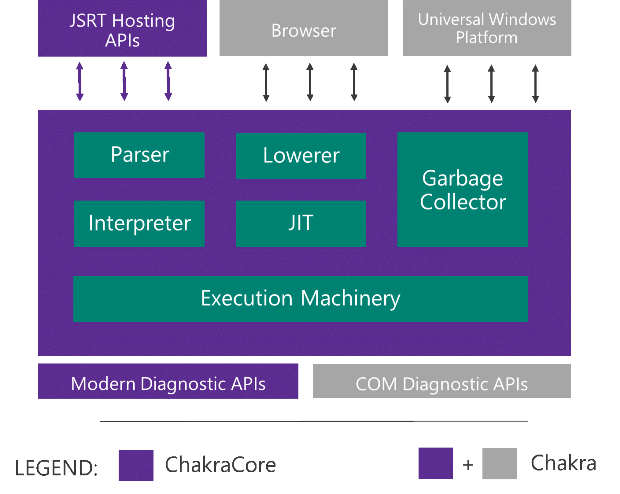
170Microsoft Edge’s JavaScript engine to go open-source
Today at JSConf US Last Call in Florida, we announced that we will open-source the core components of Chakra as ChakraCore, which...
-
 154
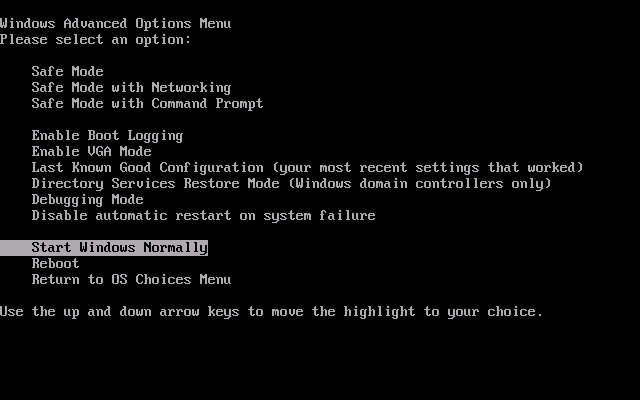
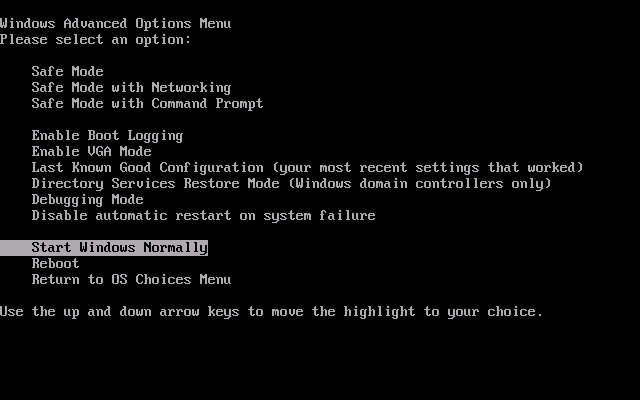
154“Nemesis” malware hijacks PC’s boot process to gain stealth, persistence
Bootkit targeting banks and payment card processors hard to detect and remove. Malware targeting banks, payment card processors, and other financial services...
-

 347
347Fallout 4 Pirated Copy Leads To Bitcoin Theft
People who download stuff from torrents and other cracked software providing websites have a very bad news because a user recently downloaded...
-

 226
226France proposes to ban Tor and forbid free Wi-Fi
Proposed French Law Would Ban TOR In Response to Paris Terror Attacks France is looking to tighten its censorship laws after the...






