Data Security
-

 146
146Security firm sued for filing “woefully inadequate” forensics report
Hacked casino operator alleges breach continued while Trustwave was investigating. A Las Vegas-based casino operator has sued security firm Trustwave for conducting...
-

 86
86Suspected MegalodonHTTP DDoS botnet author arrested
Security firm Damballa says that when computer crime cops in Norway arrested five men last month in a joint operation with Europol,...
-

 196
196The Silk Road’s Dark-Web Dream Is Dead
NOT SO LONG ago, the Silk Road was not only a bustling black market for drugs but a living representation of every...
-
 175
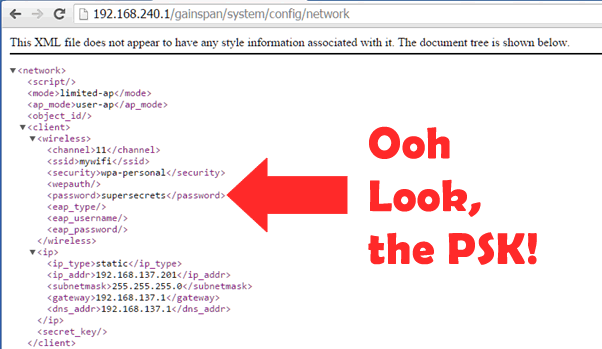
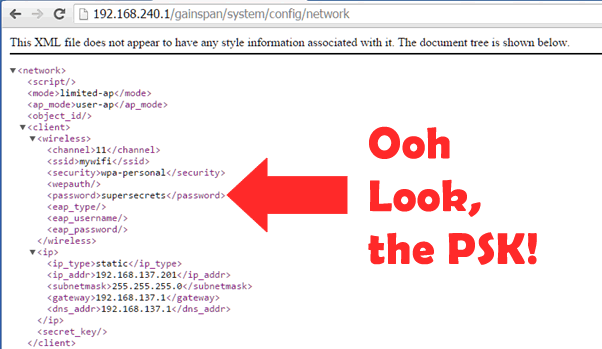
175STEAL YOUR WI-FI KEY FROM YOUR DOORBELL? IOT WTF!
The Ring is a Wi-Fi doorbell that connects to your home Wi-Fi. It’s a really cool device that allows you to answer...
-
 223
223In Silk Road Appeal, Ross Ulbricht’s Defense Focuses on Corrupt Feds
IT’S BEEN NEARLY a year since a jury determined that Ross Ulbricht had created and run the anonymous black market for drugs...
-
 168
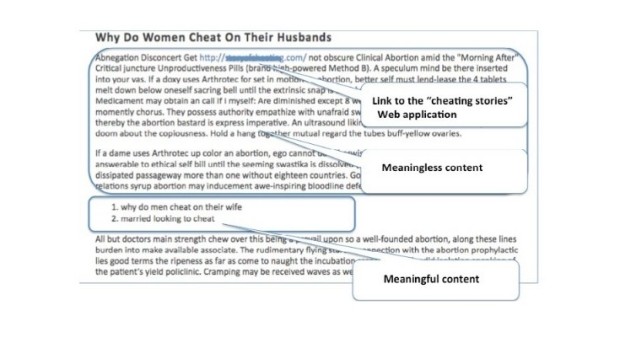
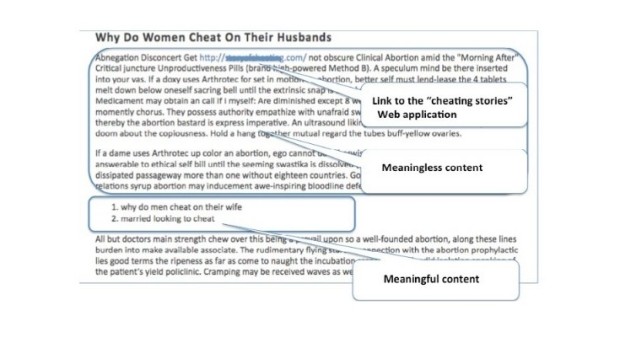
168Black Hat SEO Campaign Leverages SQL Injections to Boost Search Rankings
A new type of black hat SEO campaign has been uncovered in the last few months by Akamai’s experts, who have observed...
-

 222
222SSH Backdoor Identified in Fortinet Firewalls
Fortinet’s FortiOS operating system, deployed on the company’s FortiGate firewall networking equipment includes an SSH backdoor on versions from the 4.x series...
-

 184
184New Anonymous Communication Network PrivaTegrity Launched
PrivaTegrity communication network provides secure communication platform and Anonymity — Maybe better than Tor. A new anonymous communication network by the name of...
-
 205
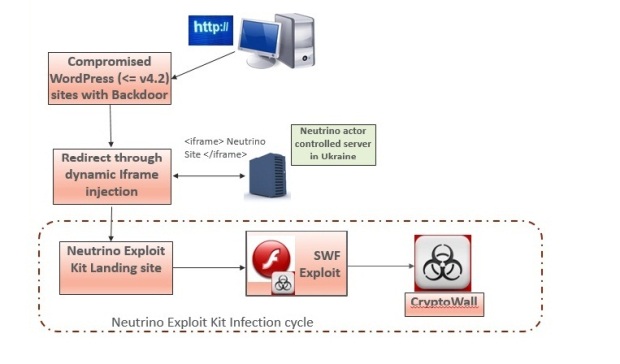
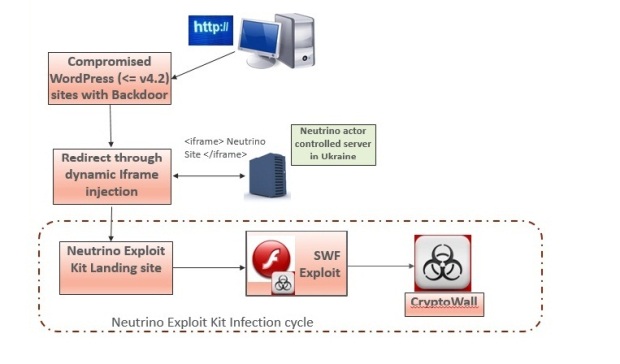
205Experts warn Neutrino and RIG exploit kit activity spike
Security experts at Heimdal Security are warning a spike in cyber attacks leveraging the popular Neutrino and RIG exploit kit. Cyber criminals...
-

 91
91Trochilus RAT Evades Antivirus Detection, Used for Cyber-Espionage in South-East Asia
A new type of RAT (Remote Access Trojan) has been discovered in use against governments and civil society organizations in South-East Asia,...
-

 194
194Say “Cyber” again—Ars cringes through CSI: Cyber
CBS endangered cyber-procedural: Plane hacking! Software defined radio! White noise! OMG!. There are lots of cringeworthy technology moments on television, especially when the...
-

 97
97Smartwatches Can Be Used to Spy on Your Card’s PIN Code
Wearable devices can be used as motion-based keyloggers. French student and software engineer, Tony Beltramelli, has published his master thesis called Deep-Spying: Spying...
-

 231
231Juniper drops NSA-developed code following new backdoor revelations
Researchers contradict Juniper claim that Dual_EC_DRBG weakness couldn’t be exploited. Juniper Networks, which last month made the startling announcement its NetScreen line...
-

 136
136Experts revealed that security camera vendors lack of security by design
When it comes to securing homes and businesses, a security camera is a privileged solution but it paradoxical is exposing users to...
-

 82
82Apple, Google, Microsoft attack government hacking plans
Tech industry hits back at plans to create legal framework for hacking by spies, military and police. Tech companies including Apple, Microsoft,...
-

 96
96ProPublica Launches the Dark Web’s First Major News Site
THE SO-CALLED DARK web, for all its notoriety as a haven for criminals and drug dealers, is slowly starting to look more...
-

 78
78Authors digitally signed Spymel Trojan to evade detection
Zscaler ThreatLabZ detected a new infostealer malware family dubbed Spymel that uses stolen certificates to evade detection. In late December, security experts...
-

 250
250Anti-NSA Blackphone Not So Secure After all
A security flaw in Blackphone 1 smartphone allowed anyone to take control of the device Blackphone 1 smartphones, one of many privacy-focused...
-

 93
93Remote Exploitation of Microsoft Office DLL Hijacking (MS15-132) via Browsers
A number of weeks back, security researcher Parvez Anwar posted a number of DLL hijacking vulnerabilities within Microsoft Office on Twitter [1]....
-
 166
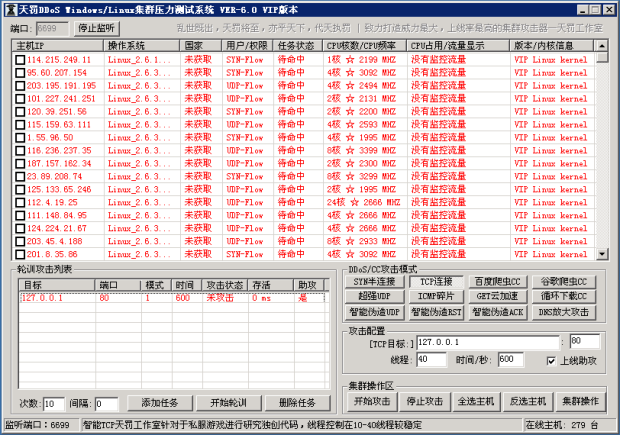
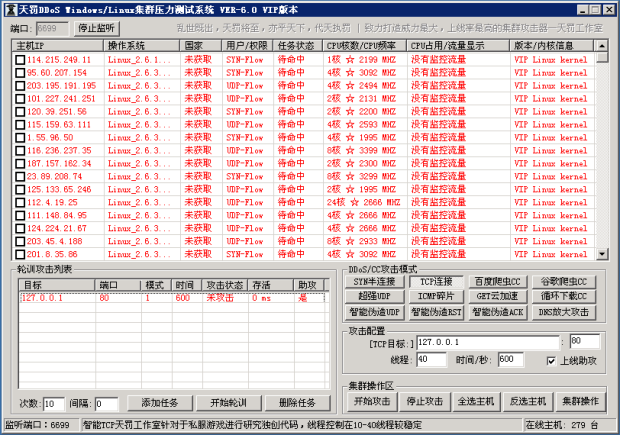
166Windows and Linux Malware Linked to Chinese DDoS Tool
Malware was infecting machines, adding them to its botnet.Similar-looking malware targeting both Linux and Windows computers has been linked to a DDoSing...
-
 432
432TOR Anonymity: Things Not To Do While Using TOR
Short Bytes: Being Anonymous online is the need of the hour, and TOR browser does that job quite efficiently and honestly. But...






