Data Security
-
 226
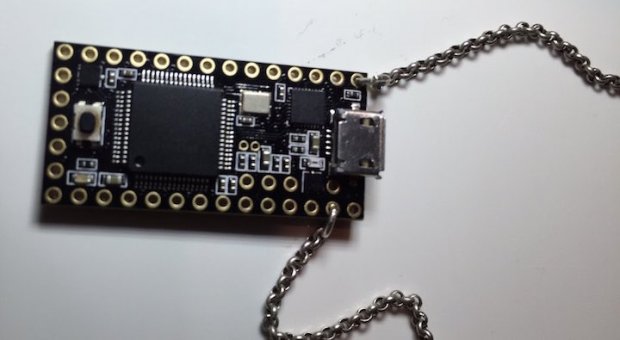
226USBDriveby: A Necklace That Can Hack Your PC In Just 60 Seconds
Short Bytes: In a video found on the YouTube channel of Samy Kamkar, a USB drive beaded in a necklace has been shown...
-
 289
289Series of Security Bugs Force Malwarebytes to Start Bug Bounty Program
Good news for security researchers you can now earn some good money by reporting security bugs to Malwarebytes — Thanks to its...
-

 155
155DMA Locker: New Ransomware, But No Reason To Panic
DMA Locker is another ransomware that appeared at the beginning of this year. For now it has been observed to be active...
-

 215
215Wikileaks’ Julian Assange could be a free man this Friday, Thanks to UN
Wikileaks founder Julain Assange can be a free man this Friday — His fate depends on the decision from United Nation’s Working Group...
-

 148
148Microsoft makes Windows 10 a ‘recommended update’ for Windows 7 and 8.1 users
Microsoft has been accused of pushing Windows 10 rather aggressively, and the company’s latest move is going to do nothing to silence...
-

 165
165Corrupt Silk Road Investigator Re-Arrested for Allegedly Trying to Flee the US
JUST WHEN THE Silk Road’s saga of dirty money and double-dealing seemed to be winding down, one of the federal agents who...
-

 273
273Audit shows Department of Homeland Security 6 billion U.S. Dollar firewall not so effective against hackers
A multi-billion U.S. Dollar firewall run by the Department of Homeland Security meant to detect and prevent nation-state hacks against the government...
-

 302
302Your HP Printer’s Hard Drive Can Be Used by Hackers To Host Malicious Files
Security researcher Chris Vickery has discovered that hackers can abuse HP LaserJet Printers and host malicious files on their hard drive. The famous...
-

 79
79JSPatch hot patching technique puts iOS users at risk
Security experts at FireEye are warning attackers can exploit the JSPatch hot patching technique to serve malicious code and put iOS users...
-

 173
173Are Hackers Keeping a Hidden Stash on Your HP Printer’s Hard Drive?
Unprotected HP printer HDDs can be abused if not protected. Security researcher Chris Vickery has discovered that HP LaserJet printers may be abused...
-

 276
276Snowden Leak Proves That NSA And GCHQ Spied On Israeli Drones Using Open Source Tools
Short Bytes: According to the latest documents provided by Edward Snowden to The Intercept, NSA and GCHQ were involved in surveillance activities...
-

 116
116WhatsApp To Get End-To-End Encryption And Facebook Integration Soon
WhatsApp is working on making your chats more secure by introducing end-to-end encryption along with a much deeper Facebook integration. A developer...
-

 235
235From Linux to Windows – New Family of Cross-Platform Desktop Backdoors Discovered
Recently we came across a new family of cross-platform backdoors for desktop environments. First we got the Linux variant, and with information...
-
 180
180Certain MediaTek phones contain a dangerous debug backdoor
MediaTek may not be on the short list of SoC companies whose chips you seek out when buying a new phone, but...
-
 121
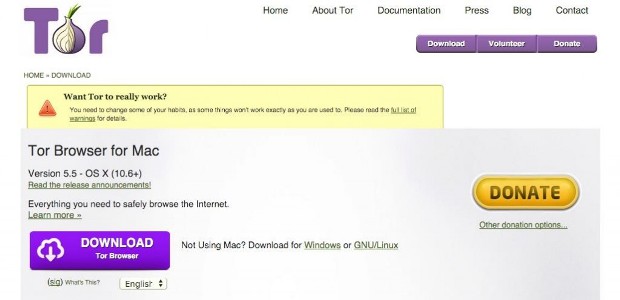
121Tor Announces Official Release of Tor Browser 5.5 With New Features
Short Bytes: Tor Browser 5.5 is the first stable release in the 5.5 series of Tor. It is released for all the...
-
 106
106Facebook Patches Critical XSS Bug That Led to Total Account Compromise
Facebook patched the issue in about six hours. British security researcher Jack Whitton has identified a critical XSS (cross-site scripting) vulnerability on Facebook...
-

 289
289Sydney Data Center Targeted By FinFisher Spyware
In 2013, the Australian government was accused of spying on Indonesia thanks to the documents leaked by Edward Snowden. Now, it looks...
-

 74
74BackBox Linux 4.5 OS comes with pre-installed new hacking tools
New Hacking Tools To Come Preinstalled With BackBox Linux 4.5 Security-Oriented OS. The release of BackBox Linux 4.5 has been announced by...
-

 172
172SHAREit for Windows and Android Vulnerabilities
Lenovo Security Advisory: LEN-4058Potential Impact: Remote browsing of file system, unauthorized access of transferred files and denial of service attack that could crash the...
-
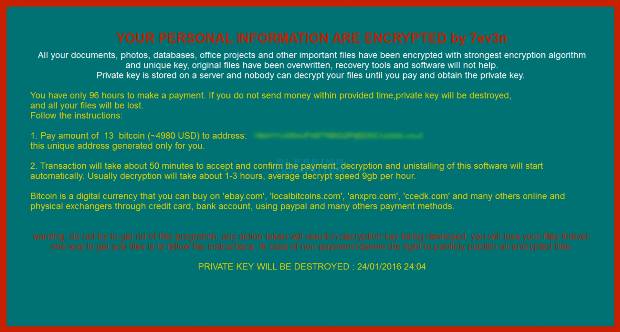
 71
717ev3n Ransomware trashes your PC and then demands 13 Bitcoins
A new ransomware has been spotted called 7ev3n that encrypts your data and demands 13 bitcoins to decrypt your files. A 13 bitcoin...
-

 133
133Simple Yet Efficient Linux Backdoor Trojan Discovered
Linux. BackDoor.Xunpes trojan lets cyber-crooks take control and execute commands on your Linux machine. Threats to Linux computers are now appearing on a...






