Data Security
-

 158
158Suckfly: Revealing the secret life of your code signing certificates
A China-based APT group has an insatiable appetite for stolen code-signing certificates. Many security-minded organizations utilize code signing to provide an additional layer...
-

 241
241#OpTrump: Anonymous Declares “Total War” Against Donald Trump From April 1
Short Bytes: The decentralized hacktivist group Anonymous has again tied their shoelaces to run after the Republican Presidential candidate Donald Trump. In...
-

 102
102Mouse movements are enough to track down Tor users
TOR’s Anonymity Promise Slashed- Users can be Tracked with their Mouse Movements! TOR is used by probably millions of Internet users simply...
-

 71
71Placing a skimmer on Gas Station Card Scanner in less than 3 seconds
Attack ATM is very simple for criminals, a video released by Miami Beach Police shows two men installing a credit card skimmer...
-

 86
86Hackers Hijack Instagram Accounts to Steal Tens of Thousands of Euros
Two teenagers were behind the whole hacking scheme. At the end of last week, Dutch police arrested two suspects on allegations of hacking...
-
 99
99Microsoft stops accepting Bitcoin in Windows Store
In 2014, Redmond reckoned Bitcoin was the future. It once also said that about Zune. Back in November 2014 Microsoft announced that it...
-
 110
110How to Hack Any Windows 7 User Password.
This is a how to to change any user password on a windows 7 computer. If you forgot your password you can...
-

 210
210How JavaScript Functions And Mouse Movements Can Reveal TOR Users’ True Identity
Short Bytes: While TOR software suite promises enhanced privacy and security, researchers have found new ways like TOR user fingerprinting to unmask...
-

 165
165Flash – aaah-aarrgh! Patch now as hackers exploit fresh holes
Flash, I love you, but we only have fourteen hours to save everyone’s computers. Adobe has urged users to patch their Windows, OS...
-

 185
185PlayStation 4 capable of booting Linux due to the latest hack
This hack can boot Linux on PlayStation 4 This is not the first time that fail0verflow announced it had successfully hacked Sony’s PlayStation...
-

 253
253Tracking users on the Tor Network through mouse movements
A security researcher has devised a new technique to track users by analyzing the mouse movements, even when surfing on the Tor...
-

 124
124How to exploit TFTP protocol to launch powerful DDoS amplification attacks
A group of security researchers from the Edinburgh Napier University elaborated a new DDoS amplification technique relying on the TFTP protocol. A...
-

 192
192Boffins bust biometrics with inkjet printer
Printed electronics makes the perfect fake fingerprint. Boffins from Michigan State University have loaded up an inkjet printer with cartridges designed for printing...
-

 92
92KeRanger Ransomware Is Actually Linux.Encoder Ported for Macs
It appears that the KeRanger Mac ransomware has roots in Linux, not Windows, as many were expecting to. A big surprise was revealed...
-

 189
189NatWest tightens online banking security after hacks’ ‘hack’ exposé
Step 1. Simply take over a victim’s mobile phone number. NatWest is tightening up its internet banking systems after security shortcomings were exposed...
-

 209
209Bangladesh Bank Says Hackers Stole Its Money from US Federal Reserve Account
Federal Reserve officials deny the incident took place. Serious accusations have been made today by Bangladesh’s central bank, which has said that hackers...
-

 166
166Car Hacking Really Is For Dummies With This Sexy (And Free) Software
Craig Smith does car hacking as safely as possible. The softly-spoken security researcher doesn’t take risks like cutting cars’ power on public roads, as...
-
 98
98How to Remove KeRanger Ransomware from Your Mac
ome users might be able to remove KeRanger before it starts its encryption process and locks up all their files. Yesterday, the first...
-

 259
259How to Connect Android to PC/Mac Without WiFi
Quite a few times, you might need to display Android screen on your PC or Mac to to play games, stream video...
-

 162
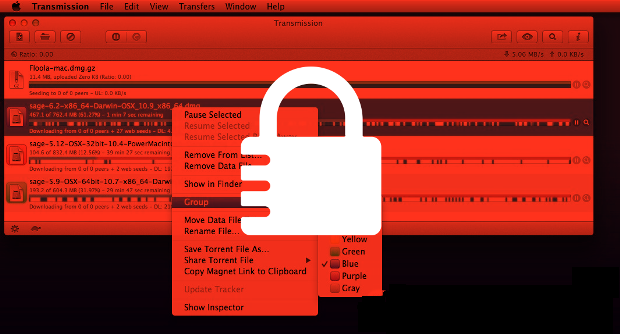
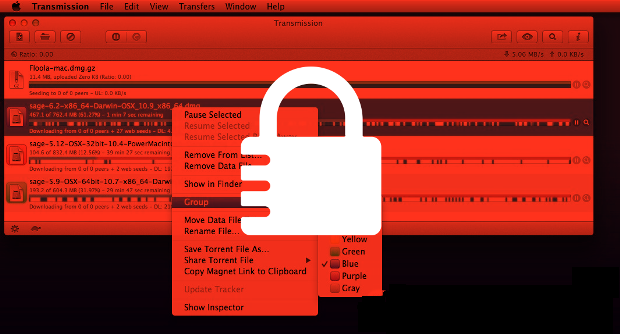
162First Fully Functional Mac Ransomware Spread via Transmission BitTorrent Client
Someone hijacked the Transmission BitTorrent client project website to spread ransomware to Mac OS X users. Over the weekend, a malicious party has...
-

 74
74Macro Malware Dridex, Locky Using Forms to Hide Code
The resurgence and continued prevalence of macro malware could be linked to several factors, one of which is their ability to bypass traditional antimalware...






