Data Security
-

 326
326Alert Gamers: RAT Activity Identified in Steam Stealer Malware Scam
Alert: The previously discussed Steam Stealer malware is way bigger than we thought — The malwarE is also embedded with a remote...
-

 172
172Panama Papers: Mossack Fonseca leak reveals elite’s tax havens
A huge leak of confidential documents has revealed how the rich and powerful use tax havens to hide their wealth. Eleven million...
-

 196
196Top Firefox extensions can hide silent malware using easy pre-fab tool
The fix? No patch, just destroy all extensions. Black Hat Asia The most popular Firefox extensions with millions of active users are open...
-

 159
159Rokku Ransomware Encrypts each file with its own Unique Key
The Rokku Ransomware is a new infection currently being spread in email attachments. When infected, a victim’s data files will be encrypted and...
-

 164
164Hacking connected lightbulbs to breach Air-Gapped networks
Two of security researchers have shown how hackers can target connected lightbulbs to exfiltrate sensitive data from Air-Gapped networks. Two of security...
-
 184
184Petya – Taking Ransomware To The Low Level
Petya is different from the other popular ransomware these days. Instead of encrypting files one by one, it denies access to the...
-

 183
183UK cops tell suspect to hand over crypto keys in US hacking case
Lauri Love faces extradition to US over hitting Federal Reserve, among others. At a court hearing earlier this month, the UK’s National Crime...
-

 261
261The Artist Using Museums to Amplify Tor’s Anonymity Network
FOR THE PAST few years, Trevor Paglen has been at the vanguard of a movement of fine artists who have led gallery-goers...
-
 149
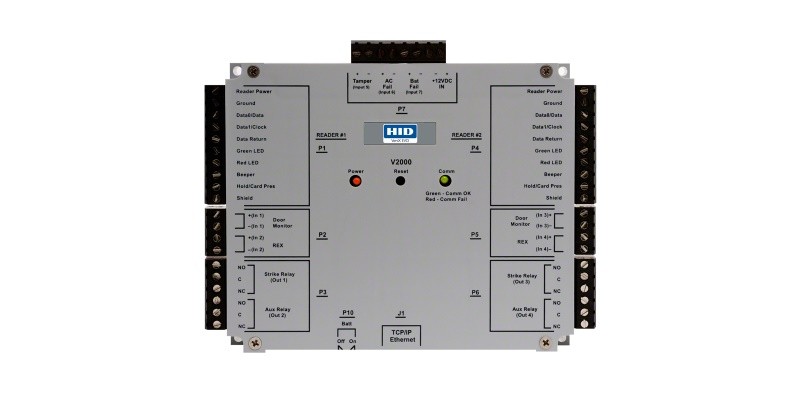
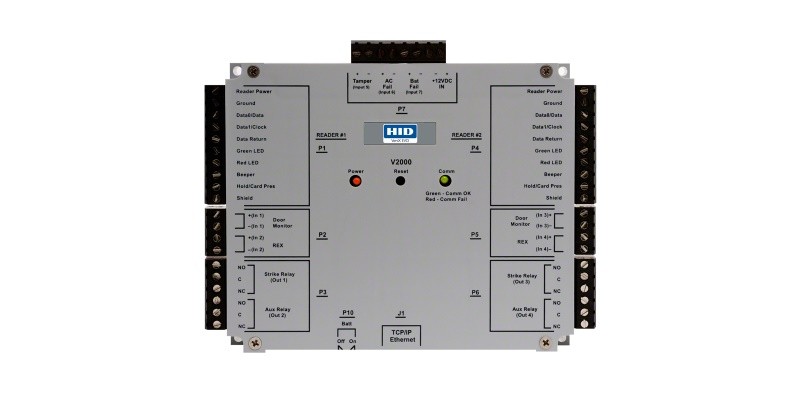
149Hackers Can Unlock Any HID Door Controller with One UDP Packet
Hacking like in the movies! Sometimes it’s that easy.If you ever want to impress your friends and hack doors with one command...
-

 173
173The code to bypass Apple System Integrity Protection security mechanism fits in a Tweet
Security researchers from SentinelOne have discovered a security vulnerability affecting the Apple System Integrity Protection (SIP). Security researcher Pedro Vilaça from SentinelOne...
-

 151
151Marine Corps Cyberspace Warfare Group, the new hacker unit
The United States Marine Corps has launched on March 25th a new hacker support unit named Marine Corps Cyberspace Warfare Group. It is...
-

 182
182Hacker exposes thousands of insecure desktops that anyone can remotely view
VNC Roulette allows you to randomly view insecure desktops accessible over the internet. Recently, a new website has come up on the Internet,...
-

 158
158Chinese Hacker Accused Of Stealing F-35 Fighter Lauded As Hero In China
Chinese state media is full of praise for the hacker accused of stealing a US F-35 Fighter Plane. A state-run media last Wednesday...
-
 111
111Feds request Judge to review the order to reveal TOR Exploit Code
FBI is fighting back against the federal judge’s order to reveal the Tor Exploit and with DoJ filed a sealed motion requesting...
-

 142
142Taiwan targeted with new cyberespionage back door Trojan
Backdoor.Dripion was custom developed, deployed in a highly targeted fashion, and used command and control servers disguised as antivirus company websites. In...
-

 167
167Hacker Known As Weev Claims Responsibility for Anti Semitic Printer Blast
In-brief: Andrew Auernheimer, an online provocateur who uses the handle “Weev,” has taken credit for causing 30,000 Internet connected printers to spew...
-
 202
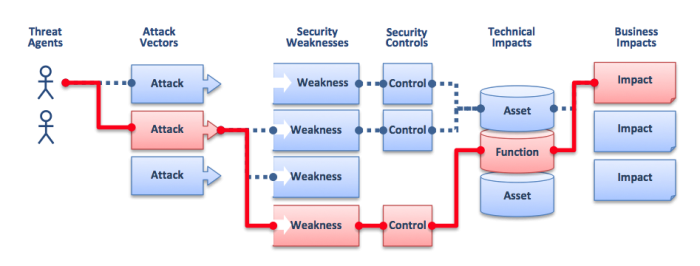
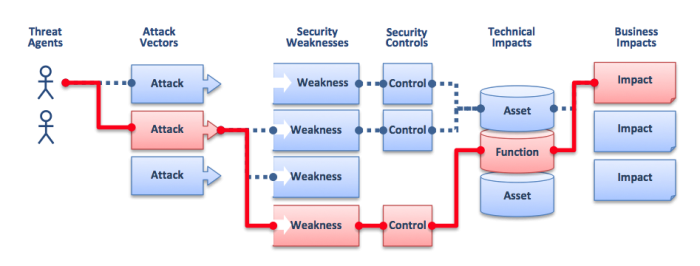
202What are web application security risks & attacks?
The websites and web applications are mission-critical business systems that must operate without security problems to process corporate confidential information. And to...
-
 216
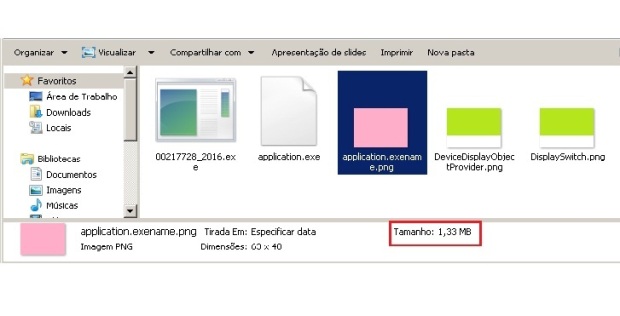
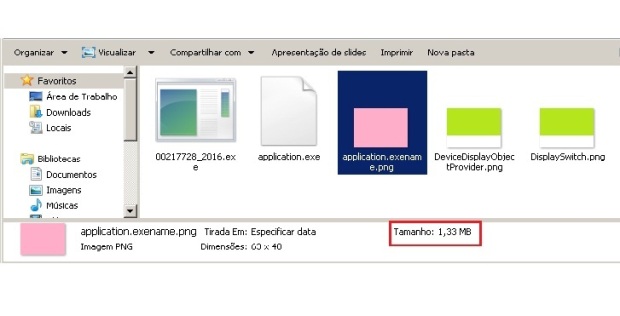
216PNG Embedded – Malicious payload hidden in a PNG file
One of the most complex tasks for the cybercriminals is to ensure their malicious code goes undetected by antivirus and achieves its...
-
 116
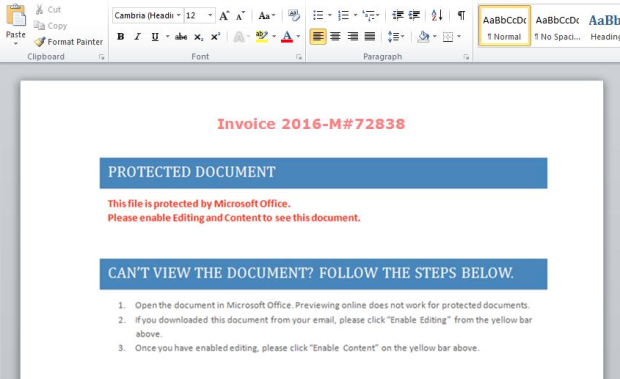
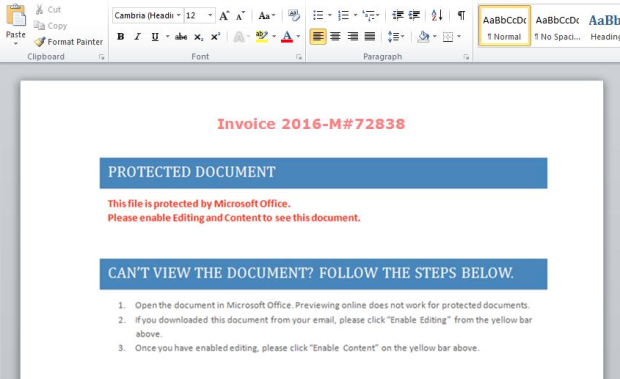
116“PowerWare,” New Ransomware Written in PowerShell, Targets Organizations via Microsoft Word
The Carbon Black Threat Research Team has recently discovered a new family of ransomware, which they dubbed “PowerWare,” that targets organizations via...
-

 69
69The Art of the Maktub Locker Ransomware
A new ransomware has been discovered by security researcher Yonathan Klijnsma called Maktub Locker that shows the most attention to detail that I have...
-

 109
109Billions at risk of computer hack due to wireless mouse
Researchers say that wireless mouse could expose billions of computers to hacking Bastille Networks, a startup cyber security company that looks to better...






