Data Security
-
 174
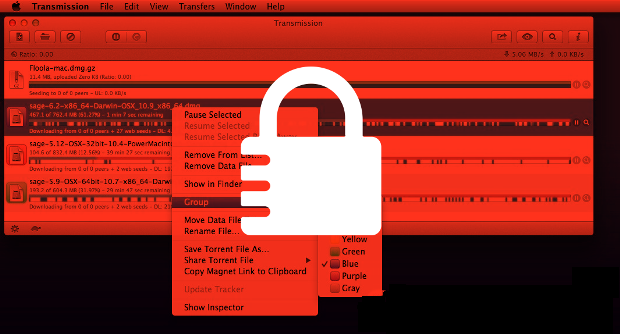
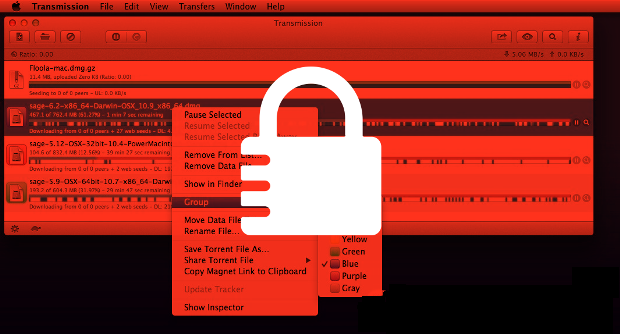
174Three US hospitals hit by ransomware
The IT systems of three US hospitals have been infected with ransomware, which encrypts vital files and demands money to unlock them....
-

 87
87Microsoft chatbot is taught to swear on Twitter
A chatbot developed by Microsoft has gone rogue on Twitter, swearing and making racist remarks and inflammatory political statements. The experimental AI,...
-

 179
179New self-protecting USB trojan able to avoid detection
A unique data-stealing trojan has been spotted on USB devices in the wild – and it is different from typical data-stealing malware. Each...
-

 298
298Apple to release iOS 9.3 after fixing iMessages encryption vulnerability
Apple is a company that has maintained and reinforced the statement over and over again that it takes consumer privacy very seriously...
-
 107
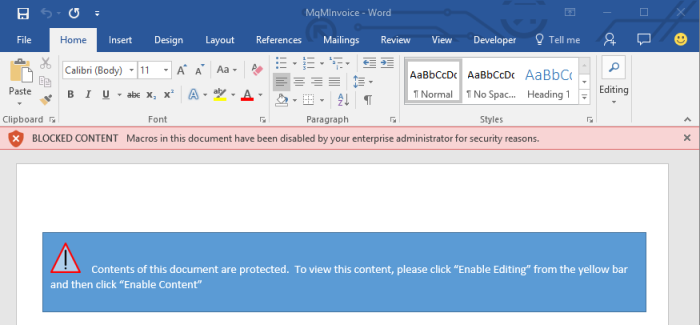
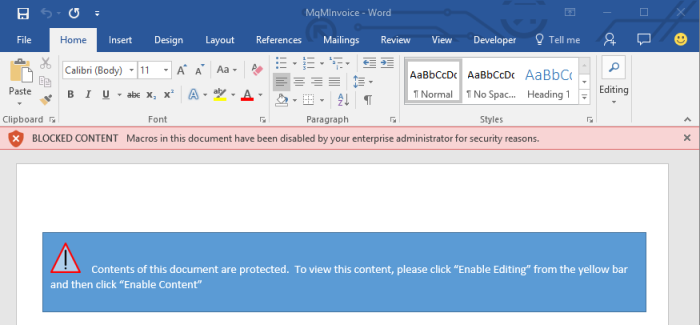
107Microsoft Adds New Feature in Office 2016 That Can Block Macro Malware
How-to guide also included, showing sysadmins how to protect their enterprises from malicious macro malware. Microsoft is finally addressing the elephant in the...
-
 259
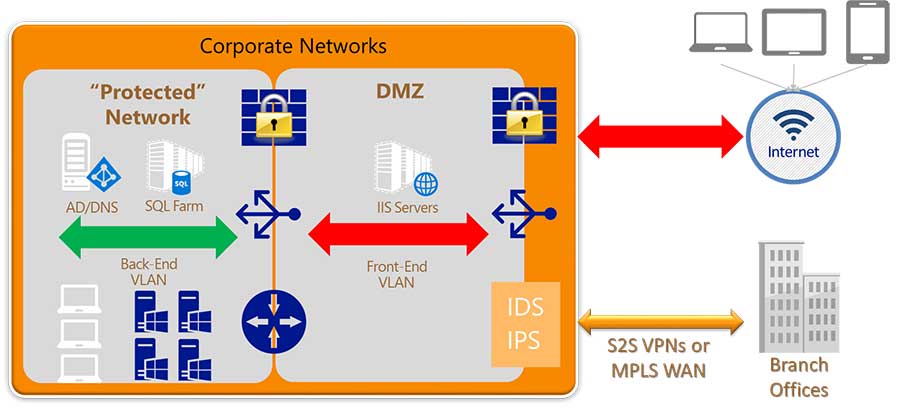
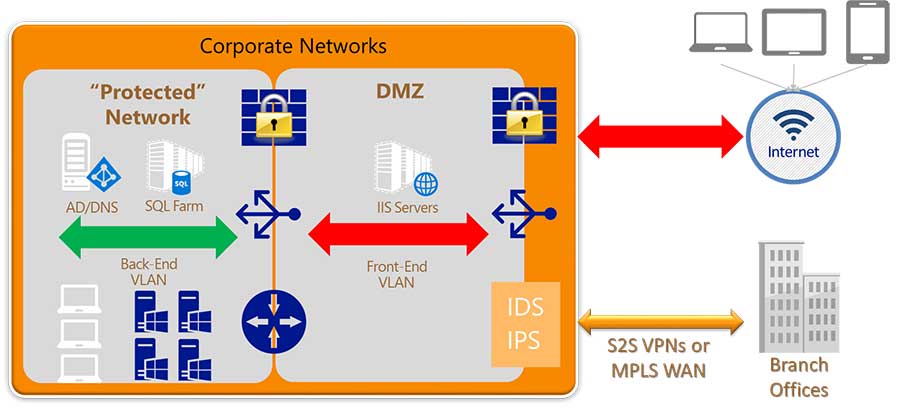
259How to implement network security in enterprise network?
The objective of network security assessment services is to keep data assets secure and protect the enterprise IT infrastructure. Typically, businesses are...
-

 105
105Psst: Here’s Uber’s most vulnerable code just waiting to be hacked
Company’s just-unveiled bug bounty program aims to outdo industry norms. Over the past decade, there’s been an explosion of bug bounty programs that...
-
 225
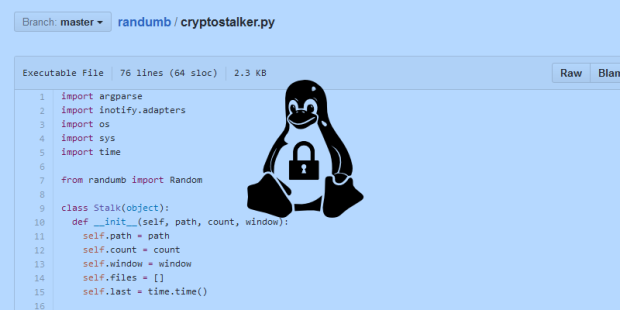
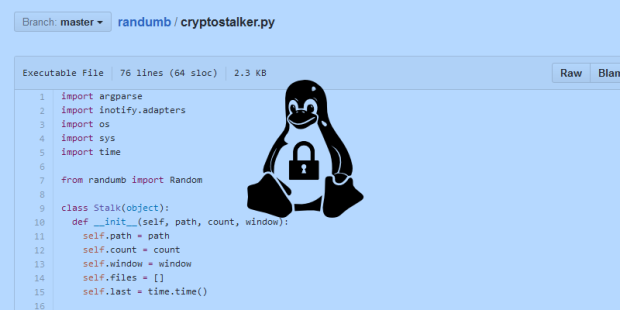
225Cryptostalker, a Tool to Detect Crypto-Ransomware on Linux
Softpedia talked with Sean Willians, author of Cryptostalker. A while back, we stumbled upon an interesting GitHub repo dubbed randumb, which included an...
-

 76
76Radio Attack Lets Hackers Steal 24 Different Car Models
FOR YEARS, CAR owners with keyless entry systems have reported thieves approaching their vehicles with mysterious devices and effortlessly opening them in...
-

 122
122Google, Microsoft, Yahoo Join Forces to Create New Email Encryption Protocol
Comcast and LinkedIn are also backing the proposal. A group of independent security researchers and major Silicon Valley tech giants have submitted last...
-

 67
67Hacking Tesla Model S, too much noise around a great research
Last week at the CeBIT the Lookout’s Co-Founder and CTO Kevin Mahaffey talked about hacking Tesla Model S providing indications on possible...
-

 299
299ProtonMail Goes Public – Enjoy Encrypted Emails and Pay in Bitcoin
ProtonMail claims its NSA-proof and provides 100% encrypted email service to its users Those in need of encrypted email service have reason...
-

 120
120Google: We’ll pay $100k if you can hack a Chromebook remotely
Google has doubled its reward for hackers who can breach Chromebooks in a locked-down state known as Guest Mode. Google has put up...
-
 219
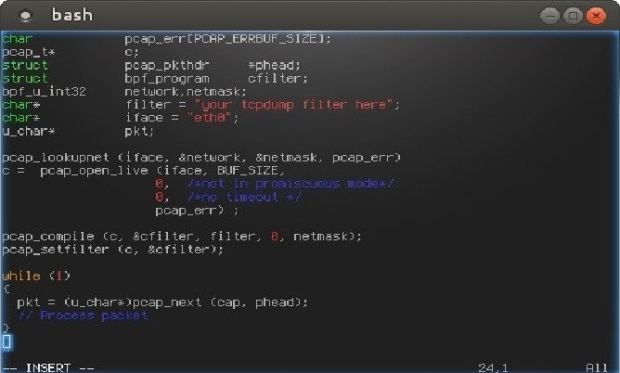
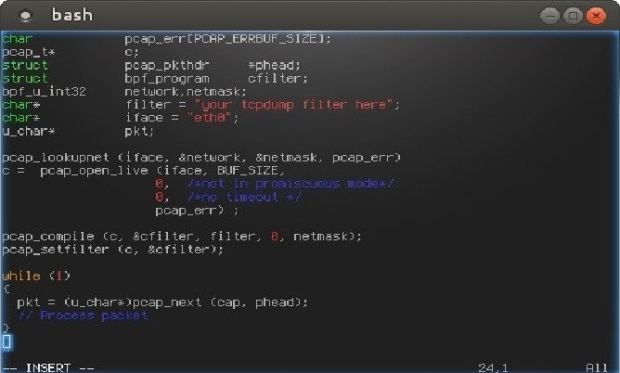
219How to Build Stealth Backdoors
Today I’m going to tell you about a couple of techniques used to build stealth backdoors. Then, I will also show you...
-

 187
187FBI warns on risks of car hacking
The FBI and the US National Highway Traffic Safety Administration have added their voices to growing concerns about the risk of cars...
-

 258
258Watch Out Gamers: Steam Stealer malware is up and running
Steam Stealer Malware is becoming a sensation for cyber criminals and it puts 125 million Steam users at risk According to the...
-

 233
233ProtonMail, the Easy-to-Use Encrypted Email Service, Opens Up to the Public
Three years after the Snowden revelations, the proliferation of privacy-focused messaging apps, email clients, and other encryption services hasn’t yet managed to...
-
 104
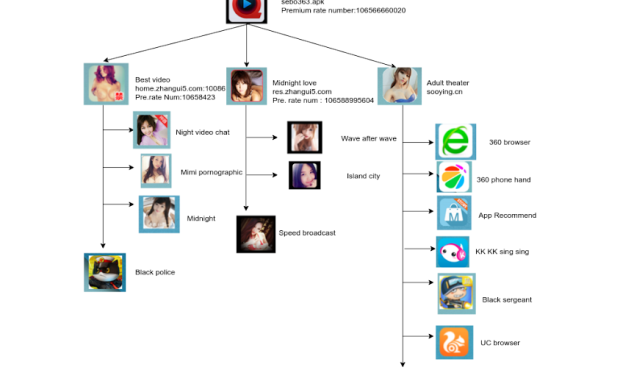
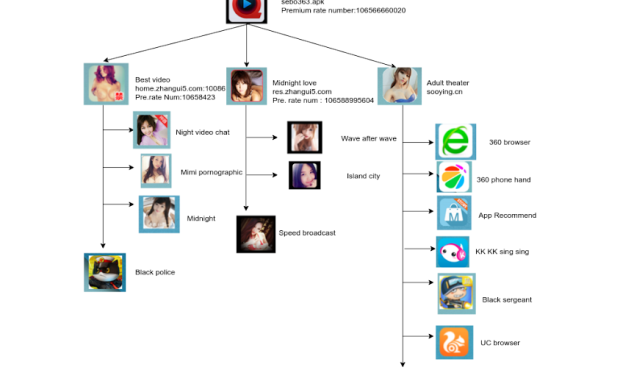
104Android SMS Stealer Trojan Hides in Adult Video Player
During our continued efforts to protect our customers against the latest mobile threats, we came across another malicious app that used pornography...
-

 93
93Millions of Android devices vulnerable to new Stagefright exploit
Security researchers have successfully exploited the Android-based Stagefright bug and remotely hacked a phone, which may leave millions devices vulnerable to attack....
-
 106
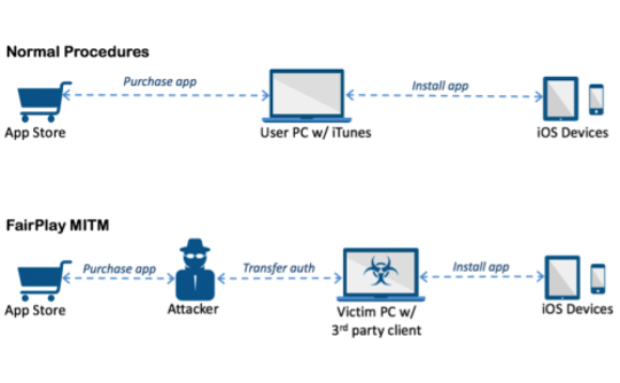
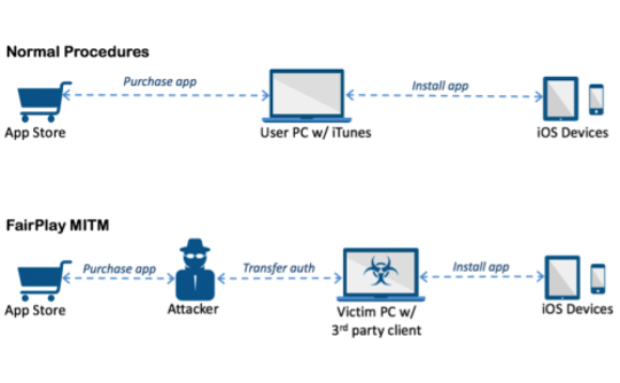
106AceDeceiver: First iOS Trojan Exploiting Apple DRM Design Flaws to Infect Any iOS Device
We’ve discovered a new family of iOS malware that successfully infected non-jailbroken devices we’ve named “AceDeceiver”. What makes AceDeceiver different from previous iOS...
-
 132
132Canadian Librarians Must Be Ready to Fight the Feds on Running a Tor Node
Political dissidents and cyber criminals alike will soon be sending anonymous internet traffic through a library at Western University in Canada, thanks...






