Data Security
-

 196
196Gmail to warn you if your friends aren’t using secure e-mail
Messages coming to or from non-encrypted sources will be flagged by Google. Google has confirmed a number of changes to Gmail with...
-

 168
168IRS website attack nets e-filing credentials for 101,000 taxpayers
Breach comes a year after a previous hack compromised 300,000 people. The US Internal Revenue Service was the target of a malware attack...
-

 362
36210 Famous Bug Bounty Hunters of All Time
If you are following HackRead you must be aware of what is bug bounty and how it works but did you know...
-

 188
188Hearthstone add-ons, cheating tools come with data-stealing malware
Attackers have disguised information-stealing and Bitcoin malware as third-party add-ons and cheats for Blizzard’s online card game. Hearthstone, a free-to-play card game...
-

 3.6K
3.6KHow to Hack the Power Grid Through Home Air Conditioners
TENERIFE, SPAIN—THERE ARE many ways we know of to cause a blackout. You could hack industrial equipment to spin a generator out...
-

 312
312Vigilante Hackers Fight Lizard Squad For Control Of 150,000 Home Routers
Home routers with little to no security are far too common. They’re dangerous from a number of perspectives: as peeping holes for spying on people’s...
-

 163
163Facebook Hacking Tool Is Here To Hack Your Accounts, But Here’s A Catch
Short Bytes: Your desire to master the art of Facebook hacking can harm you in a big way. Recently, a variant of Remtasu...
-
 192
192Oxford School District Victim of hacker’s “Crypto-Ransomware”
Oxford, Miss. (TLV)—Sunday, Feb 7, The Oxford School District was attacked by an “unknown hacker” using “crypto-ransomware.” OSD has shut down all...
-
 198
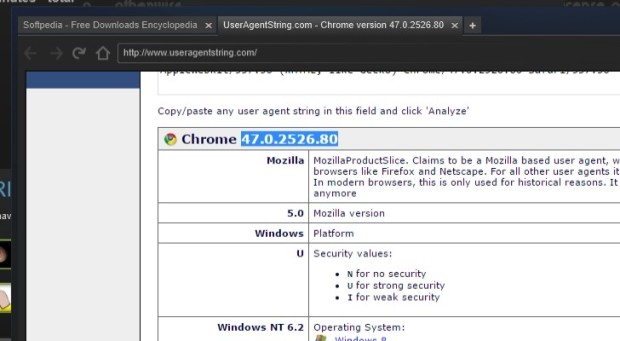
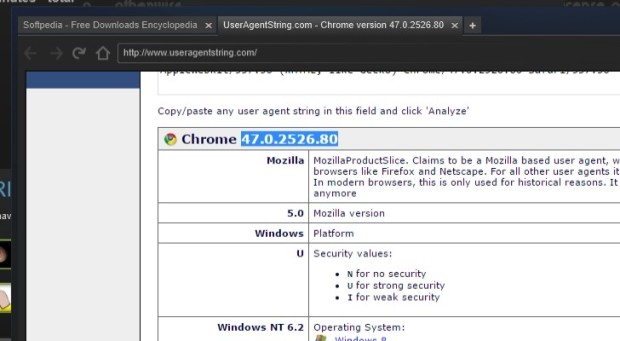
198Steam Uses Out-of-Date Chromium Browser with Security Feature Disabled
Steam’s built-in browser runs in a no-sandbox mode. The latest version of the Steam gaming client is employing an outdated Web browser that...
-

 290
290Hackers leaked DHS staff records, 200GB of files are in their hands
A hacker accessed an employee’s email account at the Department of Justice and stole 200GB of files including records of 9,000 DHS...
-

 89
89Hacking Microsoft SQL Server Without a Password
During a recent penetration test, I was performing some packet captures and noticed some unencrypted Microsoft SQL Server (MSSQL) traffic. The syntax was...
-
 185
185Dyre crackdown, the biggest effort to date by Russian authorities against cybercrime
Russian authorities raided offices of a Russian film distribution and production company as part of an operation against the Dyre gang. Russian...
-

 338
338New Malware Targets Skype Users, Saves Screenshots, Records Conversations
The internet is abuzz with news about a new backdoor Trojan that is equipped with such advanced features that it can steal...
-

 182
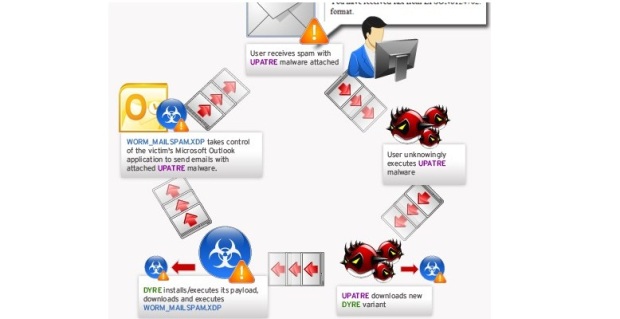
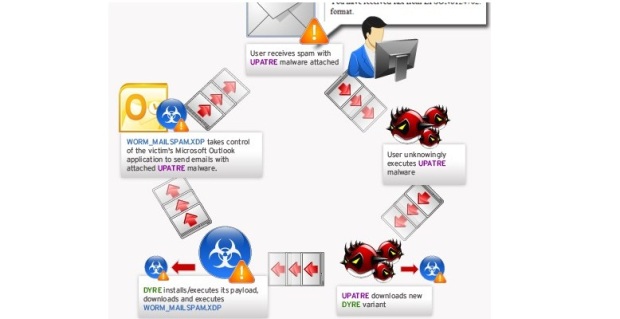
182Brazilian companies receive more than 40,000 spam emails in infostealer campaign
Spam campaign targets Portuguese-speaking firms in Brazil and other regions to deliver malware and steal sensitive data. Symantec has observed an ongoing...
-

 212
212Julian Assange’s 3.5-Year Detainment in Embassy Ruled Unlawful
THREE AND A half years after he sought temporary asylum in the Ecuadorean embassy in London only to find himself a captive...
-

 178
178Australian NSW Government Department of Resources and Energy under attack. Is it Chinese cyber espionage?
According to the NSW Government Department of Resources and Energy Chinese hackers have launched a malware-based attack on its network in December....
-
 204
204Dell Adds Boot Scanner to Protect Users Against Bootkit Malware
Dell and Cylance join the fight against bootkits. Dell has announced a partnership with Cylance, which will add a new security layer for...
-

 101
101Hack Like a Pro: Digital Forensics for the Aspiring Hacker
In this tutorial, we will explore where and what the forensic investigator can find information about the activities of the suspect in...
-

 1.1K
1.1KSomeone (Mostly) 3-D Printed a Working Semi-Automatic Gun
FOR THE LAST three years, the evolution of firearms has been playing out all over again in plastic form: Deadly, working guns...
-

 102
102Possible Encryption Backdoor Discovered in Socat Networking Utility
Backdoor code was committed by a former Oracle employee. Developers of Socat, a *NIX-based networking utility, have discovered and patched a security bug...
-

 258
258Python-based Crawler Reveals That Dark Web Sites Are Most Commonly Used for Crime
Short Bytes: The Dark Web is the World Wide Web content that exists in the darkness. The Dark Web consists of networks...






