Data Security
-
 58
58Russian bank employees received fake job offers in targeted email attack
Employees at six Russian banks were sent spoofed emails delivering Trojan.Ratopak in a narrow, targeted attack. In December 2015, employees from several...
-
 103
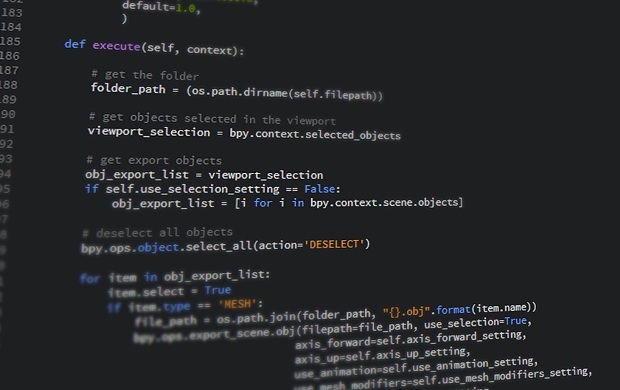
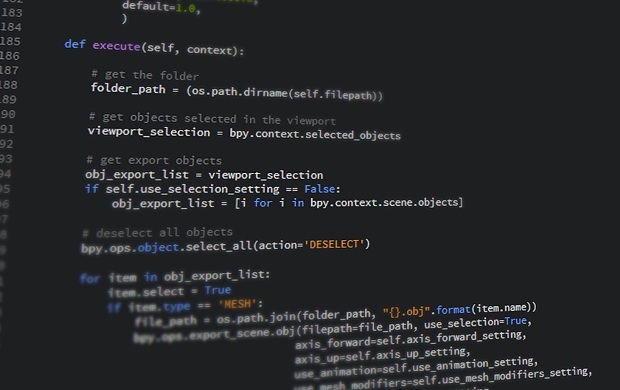
103Hack This: Scripting Deeper, Better Hacks in Python
Part of the point in presenting small, hack-minded tutorials a la “Edit an Image in Python” or “Send an Email from Python”...
-

 292
292GPS hacking (PART 1)
GPS hacking has alway been a hot topic on security conferences over the past few years. But the contents are over academic...
-
 94
94Linux Mint was hacked, website served malicious ISO on Saturday
The Linux Mint website had been hacked, on Saturday, intruders were able to compromise it and serve malicious ISO of Linux Mint...
-
 110
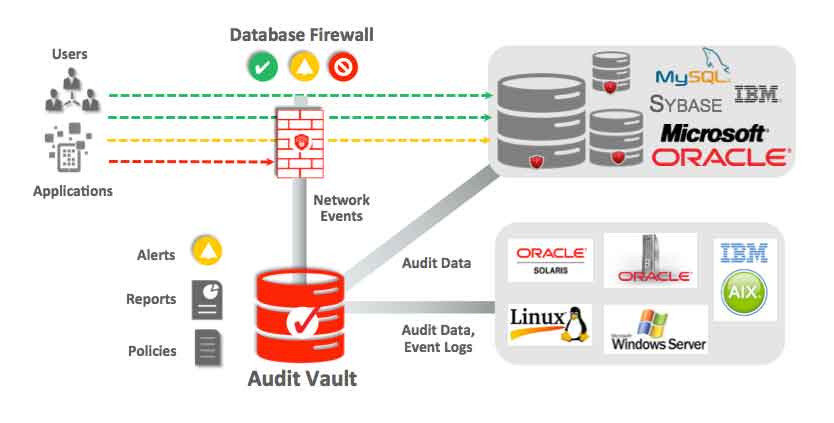
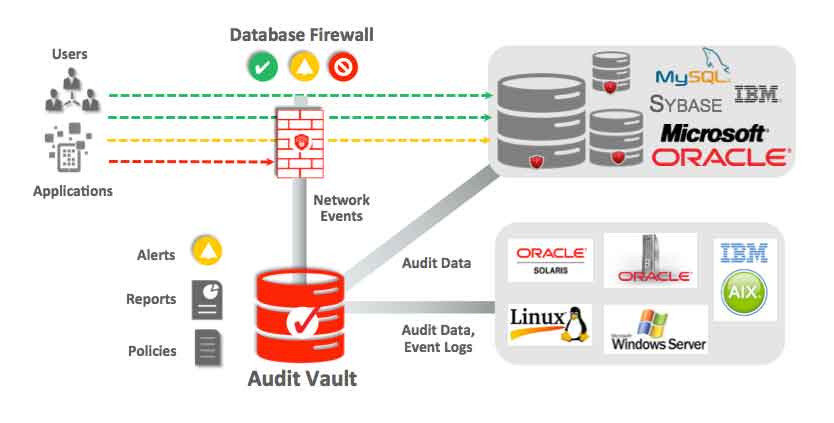
110How to secure databases?
Databases can be a treasure trove of confidential data. Normally most databases contain confidential information, private data of companies, people, intellectual property,...
-

 148
148Protect your iPhone from the clutches of the FBI by switching to longer passcodes
Protect your iPhone from the clutches of the FBI by switching to longer passcodes The on-going tussle between the FBI and Apple...
-

 103
103Hackers paid $17,000 in bitcoin ransom by L.A. hospital to get back medical records
Los Angeles hospital paid hackers $17,000 ransom in Bitcoins to decrypt medical records. We had earlier reported that hackers had infected the Hollywood Presbyterian...
-

 193
193Remotely Disabling a Wireless Burglar Alarm
Countless movies feature hackers remotely turning off security systems in order to infiltrate buildings without being noticed. But how realistic are these...
-

 121
121Southampton University Creates 5D Storage Disc That Can Store 360TB Data
The mindblowing invention will revolutionise the way we store data Last year the researchers came up with a processor capable of transmitting...
-

 272
272The NSA’s SKYNET program may be killing thousands of innocent people
“Ridiculously optimistic” machine learning algorithm is “completely bullshit,” says expert. In 2014, the former director of both the CIA and NSA proclaimed that...
-
 227
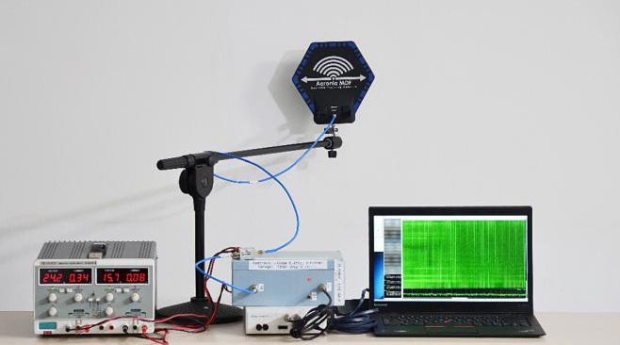
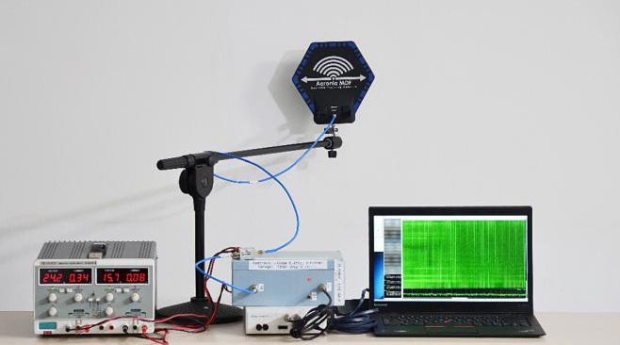
227How White Hat Hackers Stole Crypto Keys from an Offline Laptop in Another Room
Last year, it was revealed that hackers can steal data from any computer via heat and how some technologies can hack into...
-
 241
241GCHQ is allowed to hack into computers and smartphones
GCHQ is legally allowed to hack into computers, tablets and smartphones owned by the public, a tribunal has ruled, after a legal...
-

 114
114Skimmers Hijack ATM Network Cables
If you have ever walked up to an ATM to withdraw cash only to decide against it after noticing a telephone or...
-

 279
279Password Security — Who’s to Blame for Weak Passwords? Users, Really?
Password Security — Who’s to Blame for Weak Passwords? Users, Really? The vulnerability of people falling into the traps of online miscreants...
-
 216
216Russian Hackers Spying On Your Linux PC Using Sophisticated Malware “Fysbis”
Linux Backdoor Called Fysbis Used by Russian Hackers. A new malware family known as Fysbis (or Linux.BackDoor.Fysbis) is aiming Linux machines by setting...
-

 166
166Man charged of Laundering $19.6 Million earned with PBX system hacking
Pakistani citizen Muhammad Sohail Qasmani admits laundering Millions from massive computer hacking and telecommunications fraud scheme. A Pakistani citizen, Muhammad Sohail Qasmani...
-
 181
181Kaspersky Researcher Shows How He Hacked His Hospital While Sitting In His Car
Short Bytes: When we visit a hospital, we put our complete trust in our doctor and the medical equipment that he/she uses....
-
 121
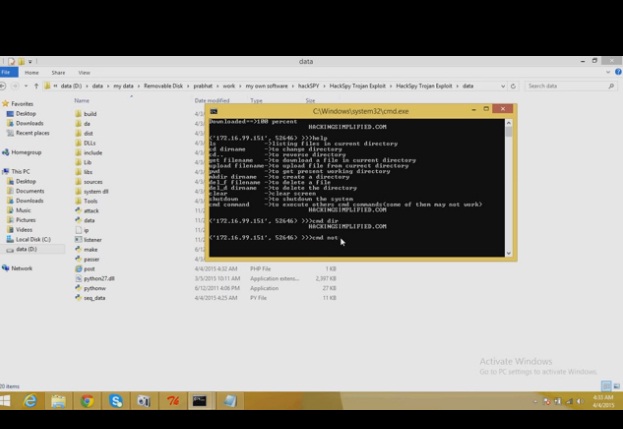
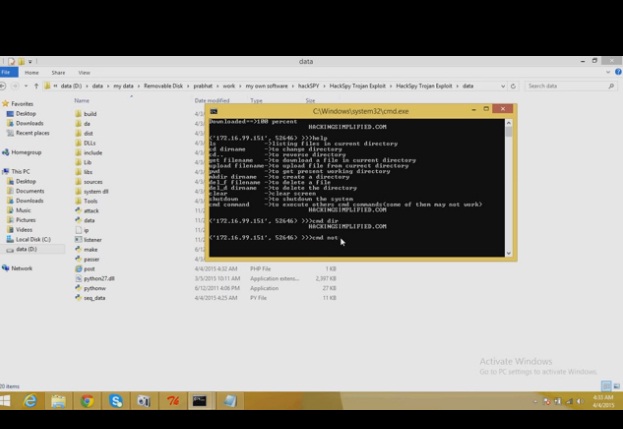
121HackSpy Trojan Exploit
HackSpy Trojan Exploit this tool make undetectable trojan virus….which can help you to spy on other computers…….. this version consists of a trojan...
-
 302
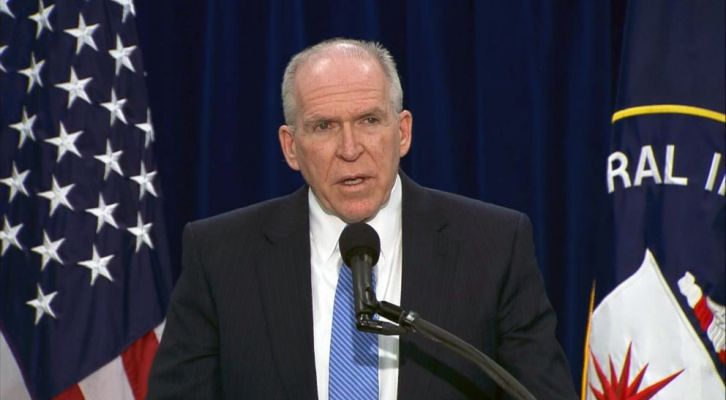
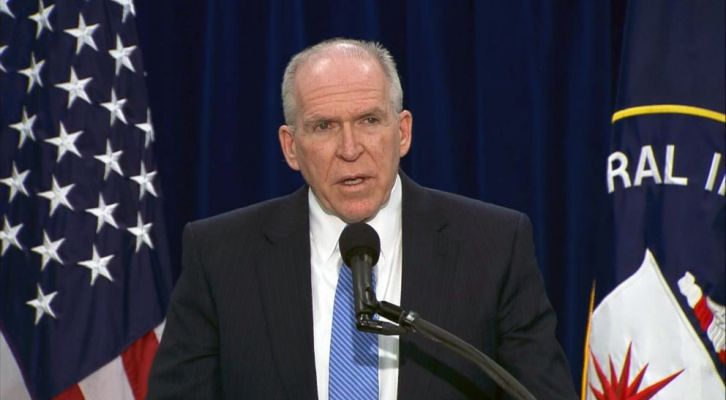
302UK police arrested teenage hacker who allegedly hacked CIA and FBI officials
UK Police and FBI have arrested a teenager suspected to be Cracka, the hacker who hacked the CIA Director John Brennan. The...
-

 176
176NYPD Admits To Using Cell Phone Spy Tool More Than 1000 Times Since 2008
The New York Police Department has admitted to using controversial cell phone spying systems known as Stingrays—which can be used to track...
-

 103
103IBM Researchers Hack Into A Smart Building To Highlight The Backdoors Created For Hackers
This smart building was hacked by IBM researchers to show hacking risks associated with Internet of Things. IBM security researchers are warning...






