Data Security
-
 333
333History of Hacking: 10 Best Hackers From The Past And What Happened To Them
Short Bytes: History of hacking always fascinates us as it tells us about the best hackers from the earlier times. But is...
-
 110
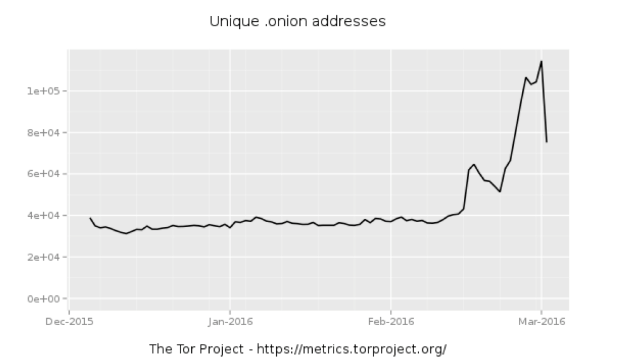
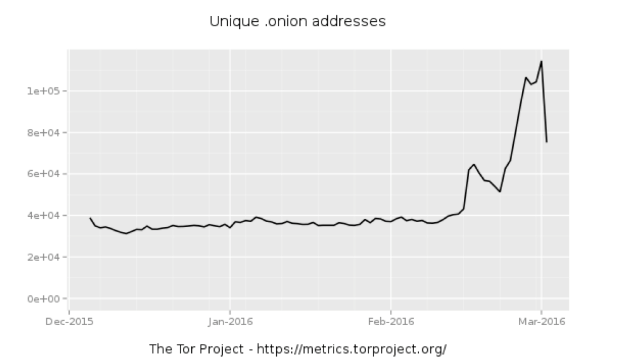
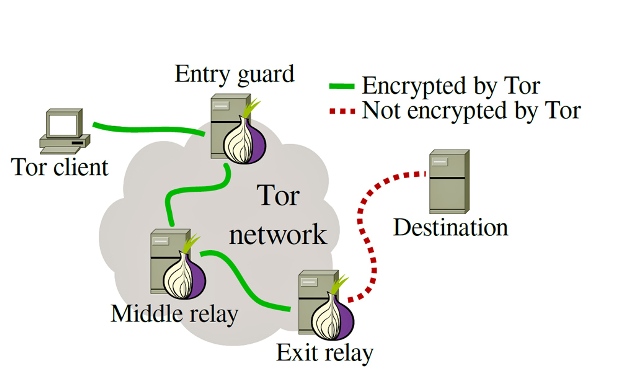
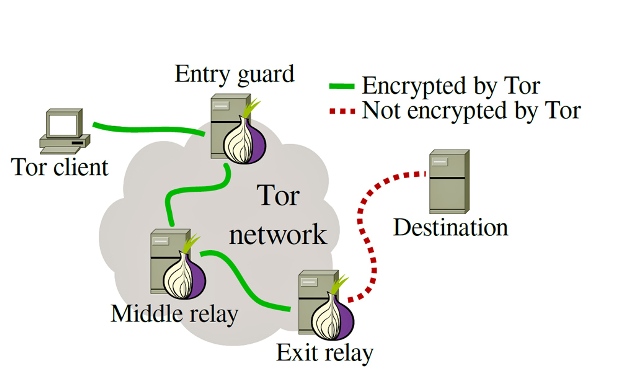
110Whole lotta onions: Number of Tor hidden sites spikes—along with paranoia
What’s driving the surge in hidden services—is it government tampering? In recent weeks, the number of “hidden services”—usually Web servers and other Internet...
-

 172
172Popular WordPress Plugin Comes With a Backdoor, Steals Site Admin Credentials
Last summer we shared a story about the SweetCaptcha WordPress plugin injecting ads and causing malvertising problems for websites that leveraged the plugin....
-

 122
122$17 smartwatch includes a backdoor in the pairing app
A group of researchers that analyzed security of a number of smart watches discovered a $17 smartwatch is sold with a backdoor...
-

 91
91Sea Pirates Hacked Shipping Company to Plan Attacks, Find Valuable Cargo
Sea pirates hire hacker to break into shipping company’s CMS. A curious case reported by Verizon’s RISK Team shows that even those lowly...
-

 93
93Windows Built-In PDF Reader Exposes Edge Browser to Hacking
WinRT PDF exposes users to drive-by attacks. WinRT PDF, the default PDF reader for Windows 10, opens Edge users to a new series...
-
 132
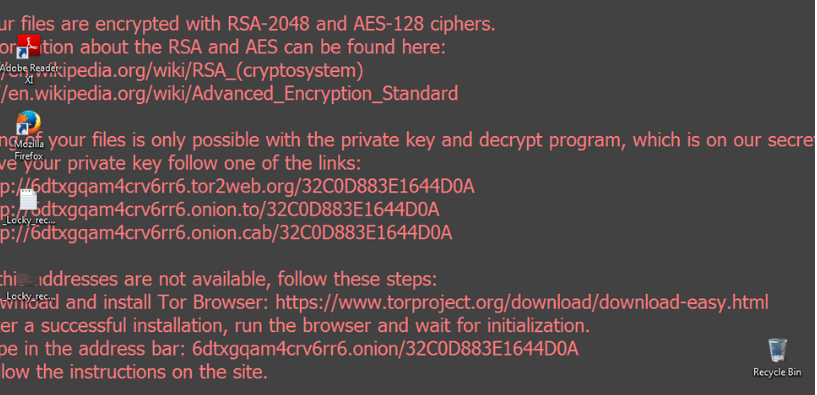
132Look Into Locky
Locky is a new ransomware that has been released (most probably) by the Dridex gang (source). Not surprisingly, it is well prepared,...
-
 143
143Facebook Latin America’s Vice-President Arrested By Brazilian Police
Short Bytes: Brazilian police have arrested Diego Dzodan, Facebook’s Latin American regional vice-president, for failing to provide WhatsApp messages related to a case...
-

 107
107Facebook Video Spam Teases Adult Videos…and Leaked iPhone?
Spam posts on Facebook are nothing new. Since videos continue to be a staple form of entertainment—a whopping 8 billion views per...
-

 75
75Largely undetected Mac malware suggests disgraced HackingTeam has returned
Until recently, sample wasn’t detected by any of the top antivirus programs. Researchers have uncovered what appears to be newly developed Mac malware...
-

 86
86How to do security vulnerability testing?
If your corporate network is connected to the Internet, you are doing business on the Internet, you manage web applications that keep...
-
 218
218A journalist has been hacked on a plane while writing an Apple-FBI story
The journalist Steven Petrow had his computer hacked while on a plane, it was a shocking experience that raises the discussion on...
-
 98
98Tor takes aim against malicious nodes on the network
‘Sybil’ nodes could be used to de-anonymise traffic. The Tor Project is working with Princeton University boffins to try and identify possibly malicious...
-

 86
86FBI could use 3 other hacks on killer’s iPhone besides an Apple backdoor
Other than an Apple backdoor hack, FBI could use 3 other hacks on killer’s iPhone. According to hardware-security experts, there are at least...
-

 132
132Security cameras and bank accounts can be hacked with an email as demonstrated by a hacker
All it takes to hack security cameras and bank accounts is an email, demonstrates a hacker. What happens when you challenge a series...
-

 99
99The DoD funded the Carnegie Mellon University’s research on Tor Hacking
A judge has confirmed that US Departement of Defense funded the Carnegie Mellon University to conduct research on the Tor hacking. In...
-

 101
101This journo got hacked while covering the FBI vs Apple iPhone hack story
Journalist gets hacked while writing the FBI vs Apple iPhone hack story. The recent United States court’s order to Apple for hack San...
-

 200
200Remotely hacking a Nissan LEAF via vulnerable APIs
The security expert Troy Hunt discovered that it is possible to remotely control features of a Nissan Leaf via API. The popular...
-
 210
210Ricochet peer-to-peer messenger uses power of the dark web to escape metadata
Ricochet is the most secure encrypted anonymous messenger that sends no metadata. The security experts have approved a new internet messaging tool...
-

 170
170Google, Red Hat discover critical DNS security flaw that enables malware to infect entire internet
Google and security firm Red Hat have discovered a critical security flaw in the Internet’s Domain Name System (DNS) that affects a...
-
 141
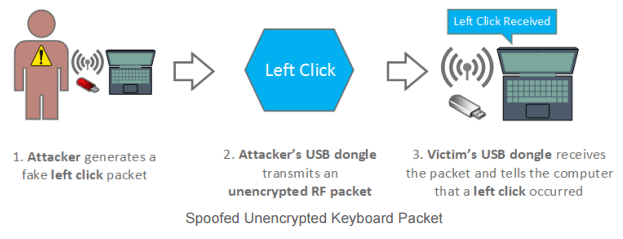
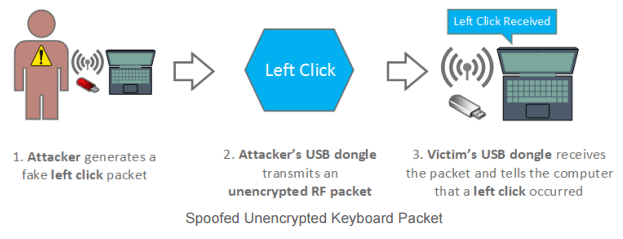
141Mousejack attack – Hijack Wireless Mouse/Keyboard Dongles from 100 meters to control PCs
Mousejack attack – Researchers at Bastille firm demonstrated how to hack computers by exploiting a flaw in many wireless mouse and keyboard...






