Hack Tools
-

 219
219malwaresearch – A command line tool to find and download malware
A Tool developed for searching malwares at openmalware.org by command line, allowing specific malware to be downloaded via shell. The tool was...
-
 113
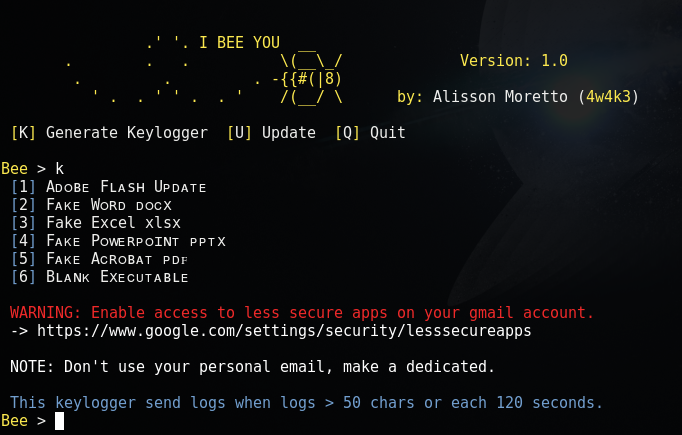
113BeeLogger – Generate Email Keyloggers
Beelogger allows you to generate a keylogger in a document format which can be executed via emails Features Send logs each 120...
-

 86
86Insanity Framework – Generate Payloads and Control Remote Machines
With the dynamics of persuasion that prove effective in a pentest, several painstaking means of making a payload has emerged, Insanity Framework...
-
 180
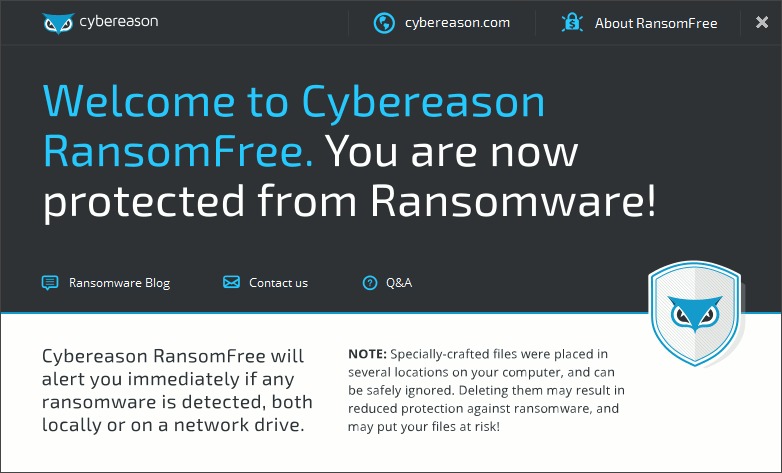
180RansomFree – Protects Your Computer Against Ransomware Attacks
RansomFree is a new tool that promises to stop ransomware attacks before they can get busy encrypting all of your data. Instead...
-
 184
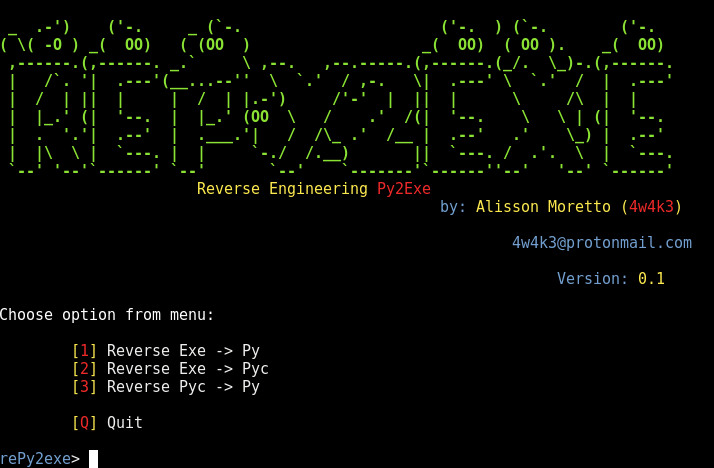
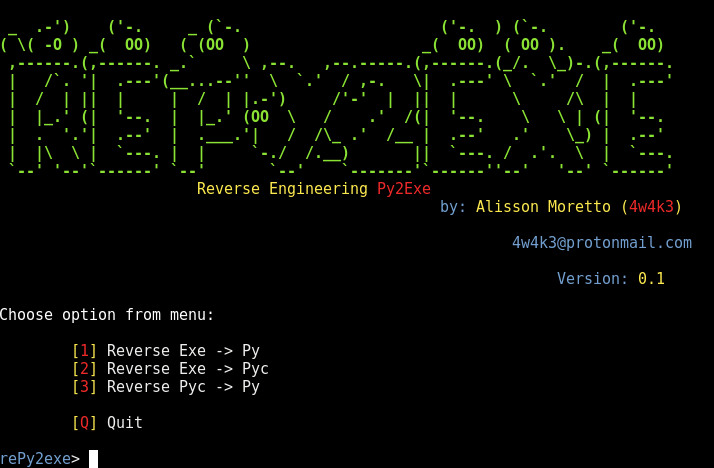
184rePy2exe – A Reverse Engineering Tool for py2exe applications
Reverse Engineering Tool for py2exe applications. Prerequisites cmake git python2.7 Cloning git clone https://github.com/4w4k3/rePy2exe.git Running python rePy2exe.py or python2.7 rePy2exe.py Authors Alisson...
-
 87
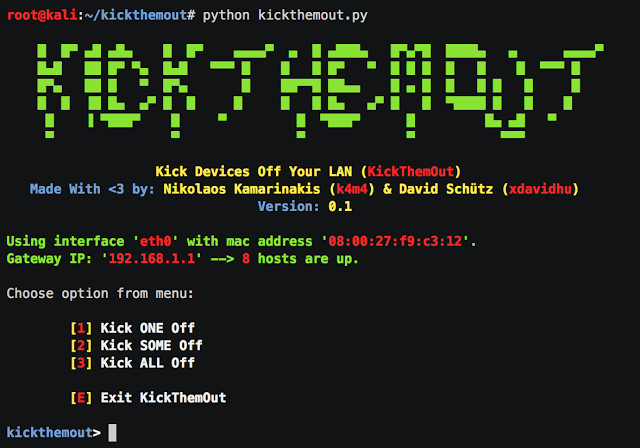
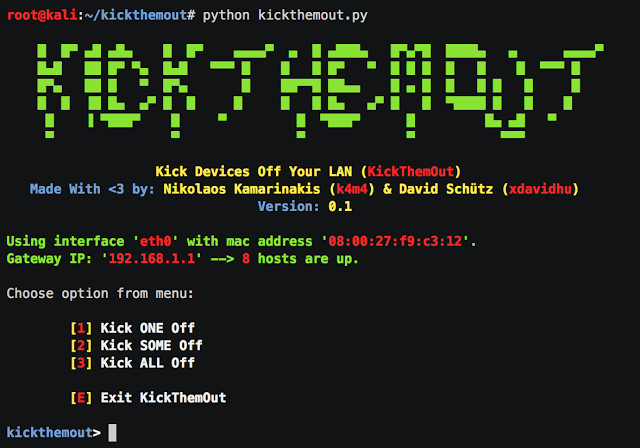
87KickThemOut – Kick Devices Off Your Network
A tool to kick devices off of your network and enjoy all the bandwidth for yourself. It allows you to select specific...
-

 168
168Stitch – A Cross Platform Python Remote Administration Tool
This is a cross platform python framework which allows you to build custom payloads for Windows, Mac OSX and Linux as well....
-

 171
171Wifijammer – Continuously Jam All Wifi Clients/Routers
Continuously jam all wifi clients and access points within range. The effectiveness of this script is constrained by your wireless card. Alfa...
-

 233
233Burp Suite Professional 1.7.14 – The Leading Toolkit for Web Application Security Testing
Burp Suite is an integrated platform for performing security testing of web applications. Its various tools work seamlessly together to support the...
-
 200
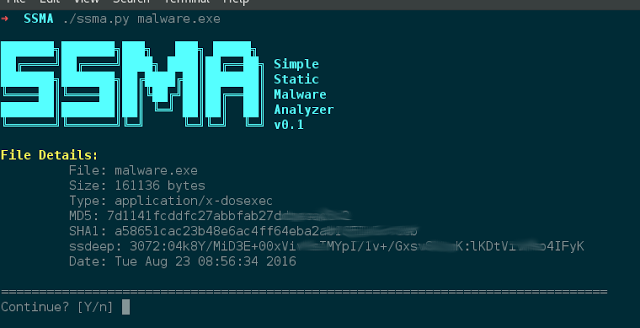
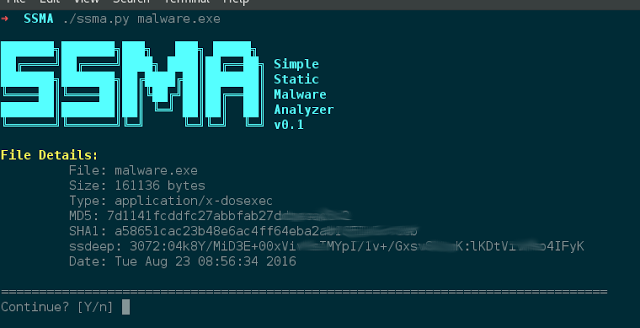
200SSMA – Simple Static Malware Analyzer
SSMA is a simple malware analyzer written in Python 3. Features: Searches for websites, e-mail addresses, IP addresses in the strings of...
-

 126
126Serpico – SimplE RePort wrIting and COllaboration tool
Serpico is a penetration testing report generation and collaboration tool. It was developed to cut down on the amount of time it...
-
 243
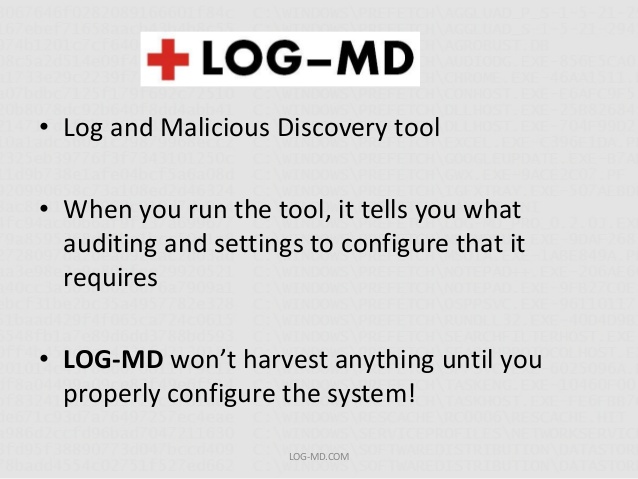
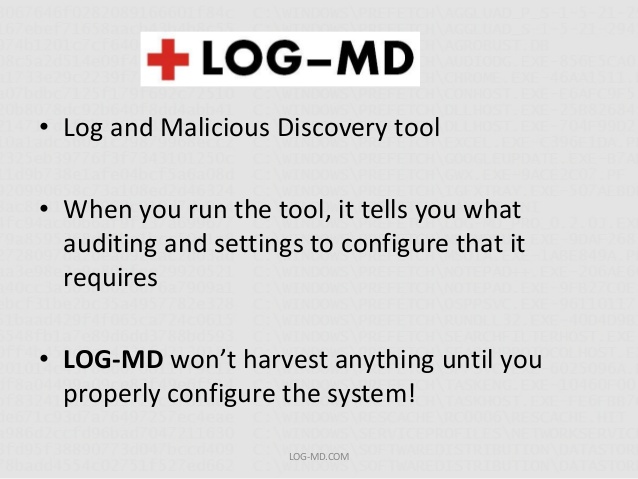
243LOG-MD – Log Malicious Detection tool
LOG-MD was designed for Windows based systems to audit log and advanced audit policy settings and guide users to enable and configure...
-
 194
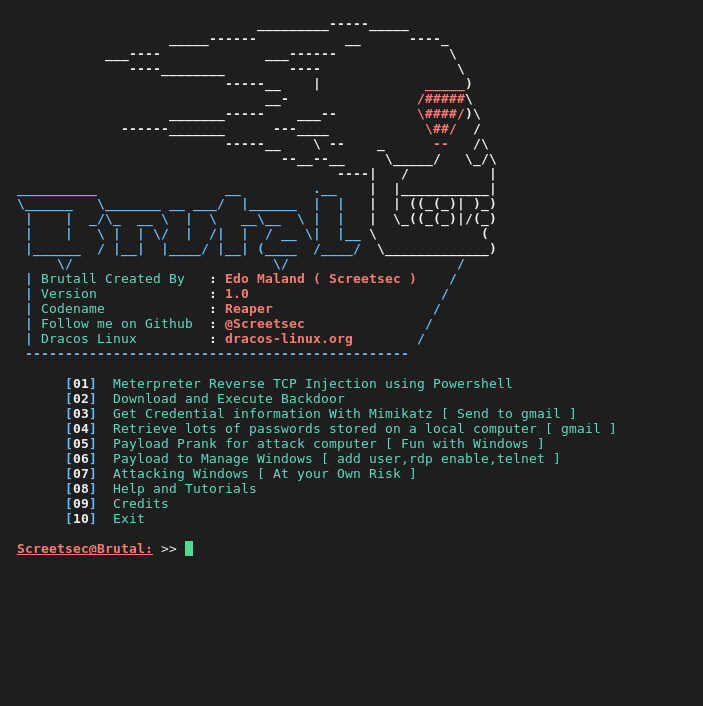
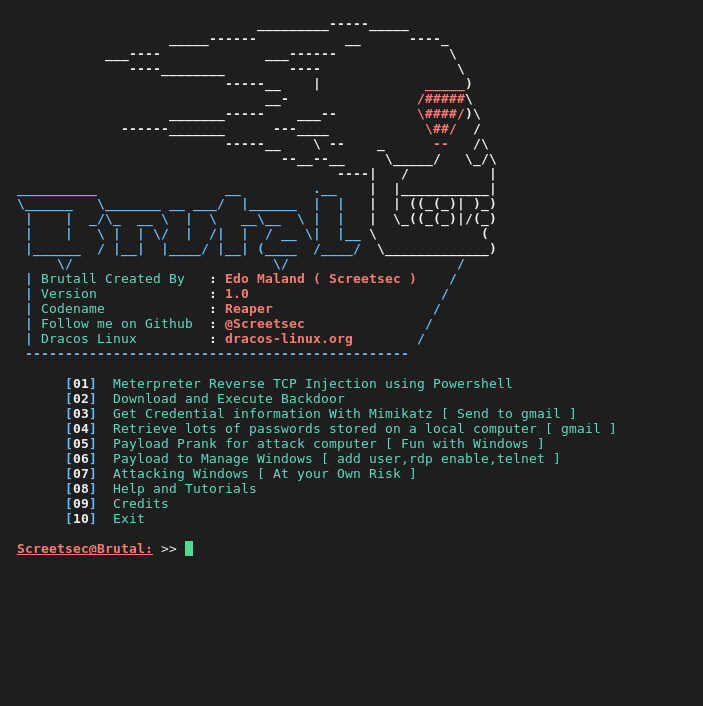
194Brutal – Toolkit to quickly create various payloads,powershell and virus attacks
Brutal is extremely useful for executing scripts on a target machine without the need for human-to-keyboard interaction ( HID -ATTACK )...
-
 192
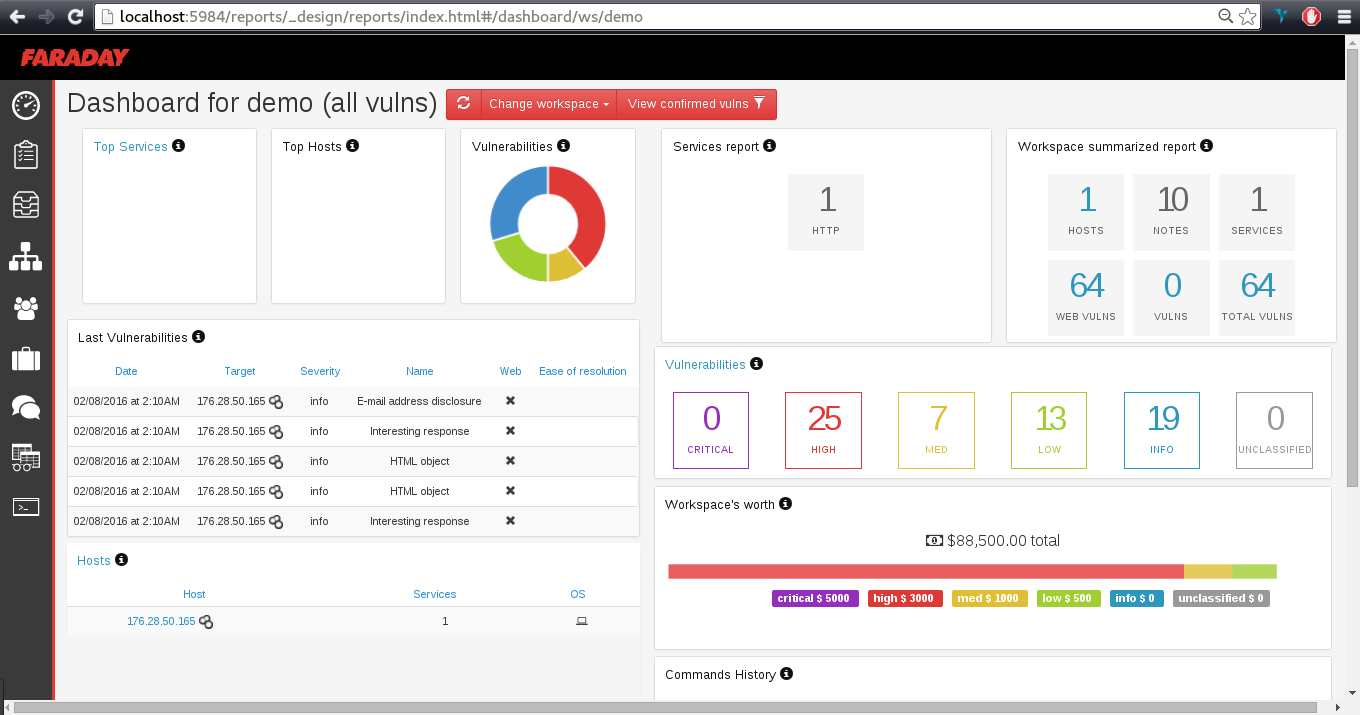
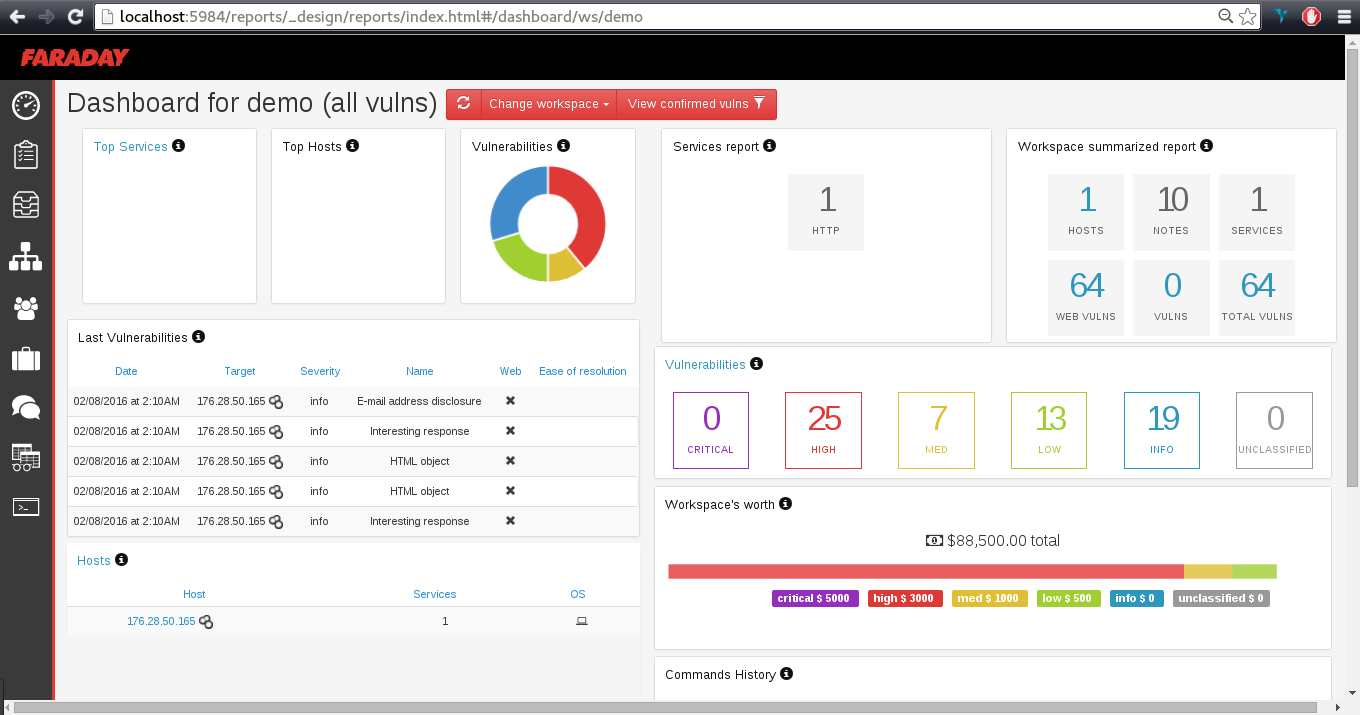
192Faraday – Penetration Test and Vulnerability Management Platform
Faraday introduces a new concept – IPE (Integrated Penetration-Test Environment) a multiuser Penetration test IDE. Designed for distribution, indexation and analysis of...
-
 105
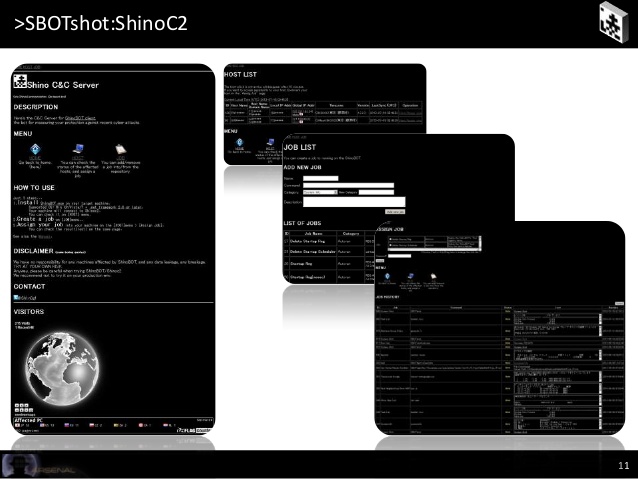
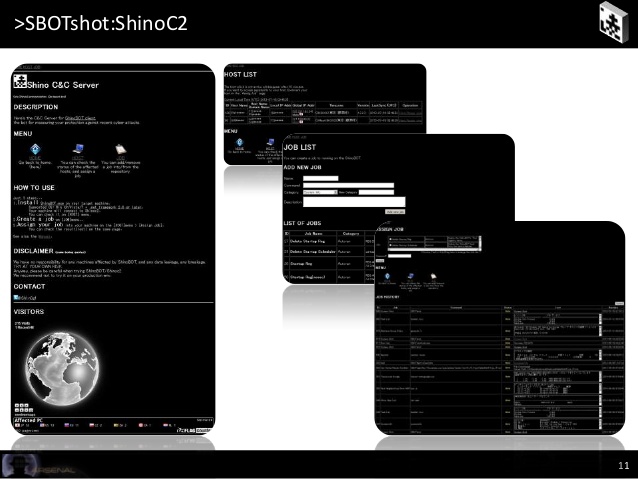
105ShinoBOT – The Rat/Bot Malware Simulator
Are you sure that you can detect an APT malware? YES or NO, whichever, try ShinoBOT; this is a BOT or RAT...
-

 113
113Radium Keylogger – Python keylogger with multiple features
Keylogging is the malicious action of spying on the keyboard input of a target user. This is done in secret by malware...
-
 99
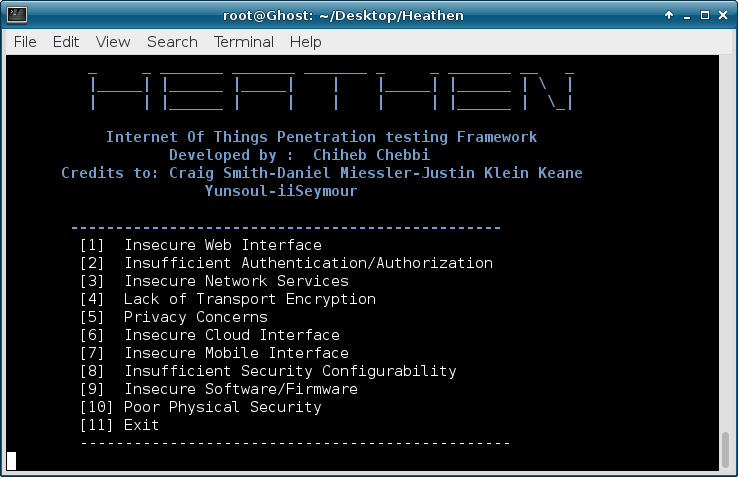
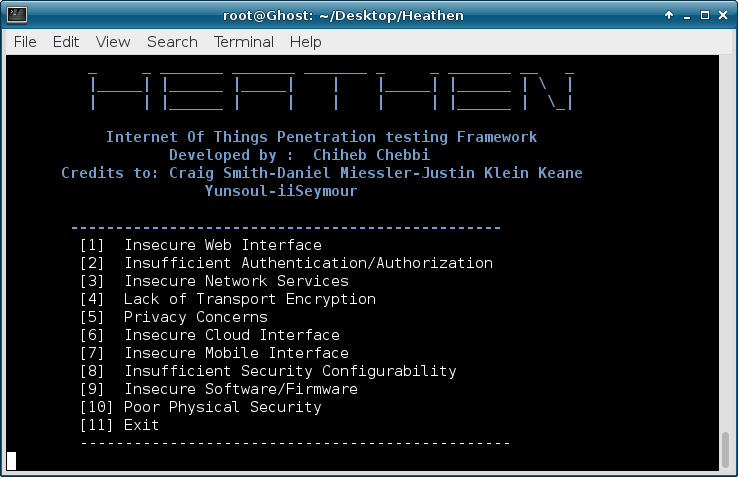
99Heathen – IoT Pentesting Framework
Heathen Internet of Things Penetration Testing Framework developed as a research project, which automatically help developers and manufacturers build more secure products in...
-
 315
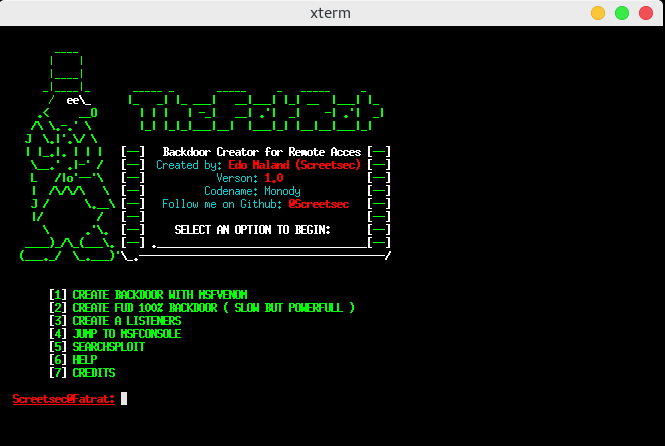
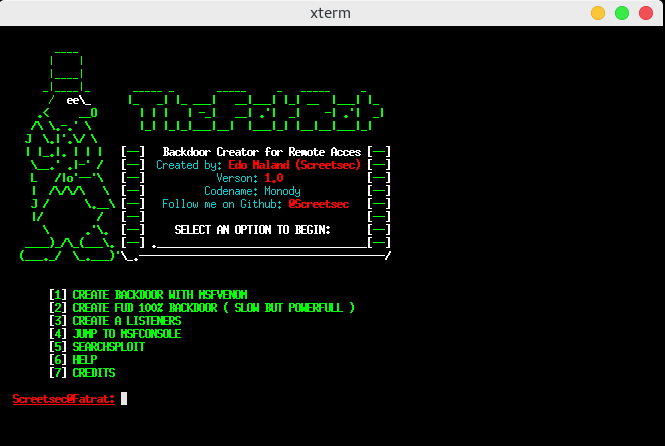
315TheFatRat – Easy Tool to Generate Backdoor
Easy tool for generate backdoor with msfvenom ( part of metasploit framework ) and program compiles a C program with a meterpreter...
-
 286
286Gcat – A stealthy Backdoor that uses Gmail as the C&C server
A stealthy Python based backdoor that uses Gmail as a command and control server. Requirements A Gmail account (Use a dedicated account!...
-
 213
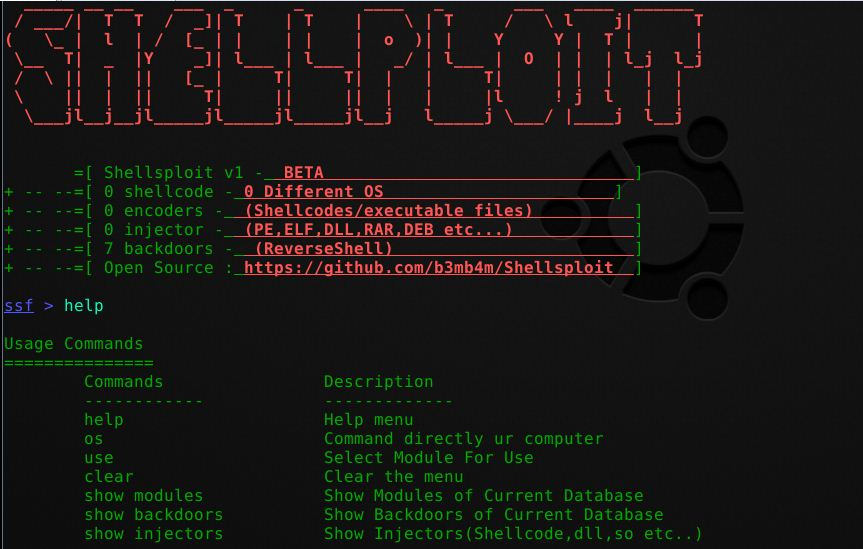
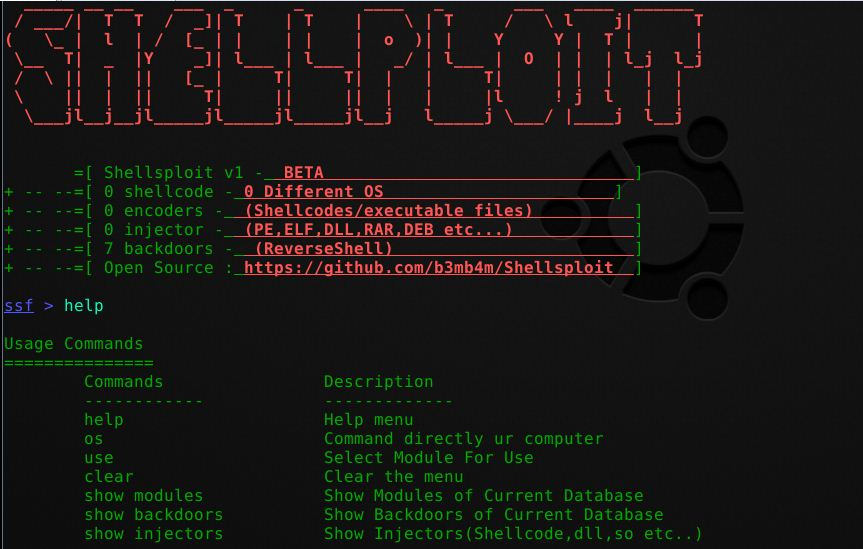
213Shellsploit – New Generation Exploit Development Kit
Shellsploit let’s you generate customized shellcodes, backdoors, injectors for various operating system and let’s you obfuscate every byte via encoders. Install/Uninstall If...
-

 200
200Spiderfoot – Open Source Intelligence Automation Tool
SpiderFoot is an open source intelligence automation tool. Its goal is to automate the process of gathering intelligence about a given target....






