Hack Tools
-
 261
261DAws – Advanced Web Shell
DAws is an advanced web shell with a lot of features. There are multiple things that make DAws better than every Web...
-

 262
262SpookFlare – Meterpreter Loader Generator
SpookFlare is a loader generator for Meterpreter Reverse HTTP and HTTPS stages. SpookFlare has custom encrypter with string obfuscation and run-time code...
-

 344
344Hashcat – Fastest and Most Advanced Password Recovery Utility
hashcat is the world’s fastest and most advanced password recovery utility, supporting five unique modes of attack for over 200 highly-optimized hashing algorithms....
-

 174
174Cain & Abel – Tool For Hackers
Cain & Abel is an amazing tool that is specifically designed for network administrators and penetration testers to recover various kinds of...
-

 191
191MITM Router – Man in the middle Router
Turns any linux computer into a public Wi-Fi network that silently mitms all http traffic. Runs inside a Docker container using hostapd, dnsmasq, and mitmproxy to...
-

 259
259MeterSSH – Meterpreter over SSH
MeterSSH is a way to take shellcode, inject it into memory then tunnel whatever port you want to over SSH to mask...
-

 210
210Vulscan – nMap Vulnerability Scanner
Vulscan is a module which enhances nmap to a vulnerability scanner. The nmap option -sV enables version detection per service which is...
-
 261
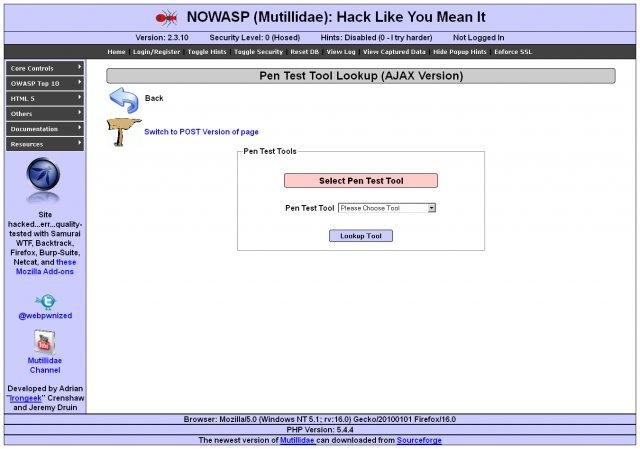
261NOWASP Mutillidae II Web Pentest Practice Application v2.6.30
OWASP Mutillidae II is a free, open source, deliberately vulnerable web-application providing a target for web-security enthusiest.Mutillidae can be installed on Linux and...
-

 102
102Excalibur – An Eternalblue exploit payload based on Powershell
Excalibur is an Eternalblue exploit based “Powershell” for the Bashbunny project. It’s purpose is to reflect on how a “simple” USB drive...
-
 150
150The Mole – Automatic SQL Injection Exploitation Tool
The Mole is an automatic SQL Injection exploitation tool. Only by providing a vulnerable URL and a valid string on the site...
-

 101
101v3n0m – Popular Pentesting Scanner
v3n0m is a free and open source scanner. Evolved from baltazar’s scanner, it has adapted several new features that improve functionality and...
-
 221
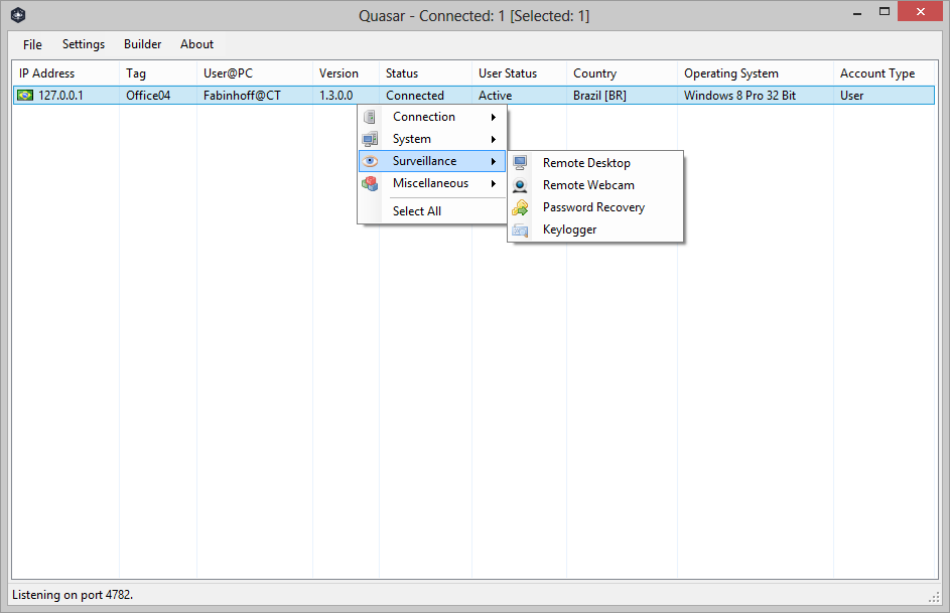
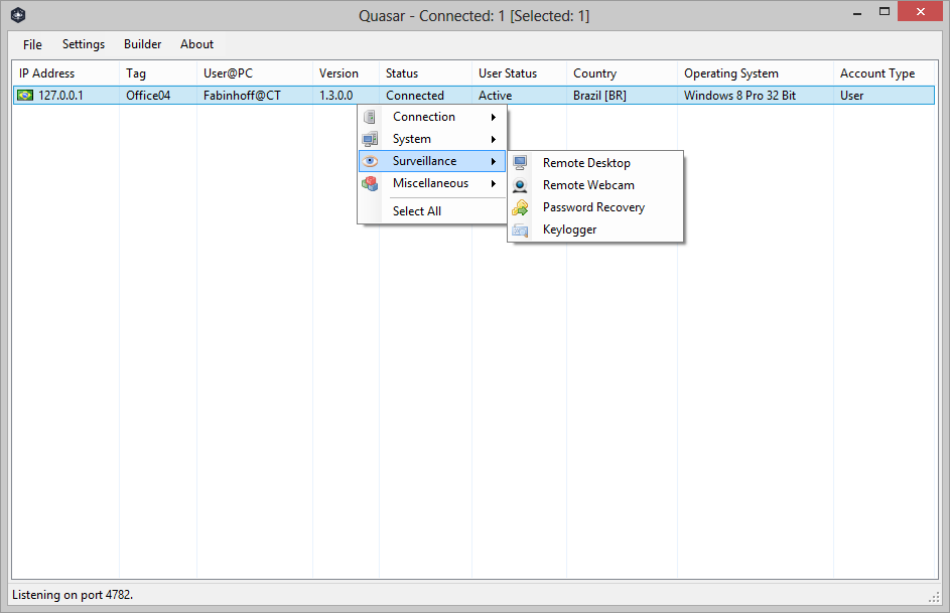
221QuasarRAT – Open-Source Remote Administration Tool for Windows
Quasar is a fast and light-weight remote administration tool coded in C#. Providing high stability and an easy-to-use user interface, Quasar is...
-
 166
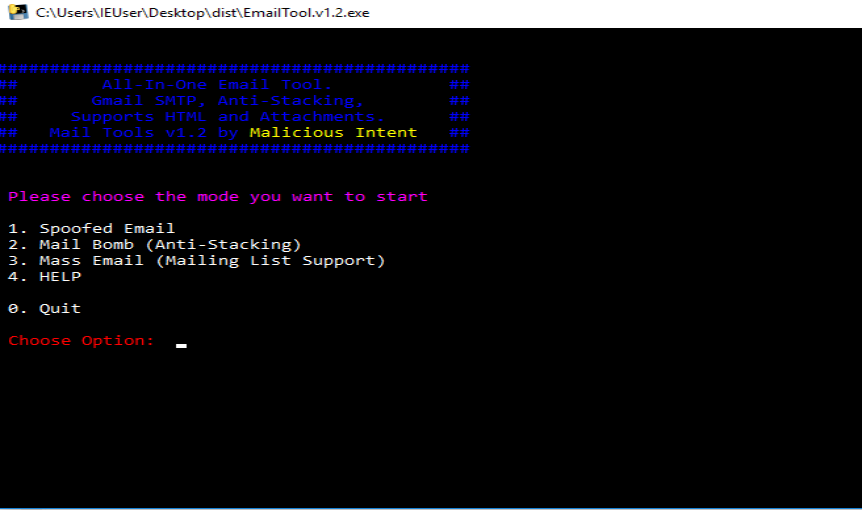
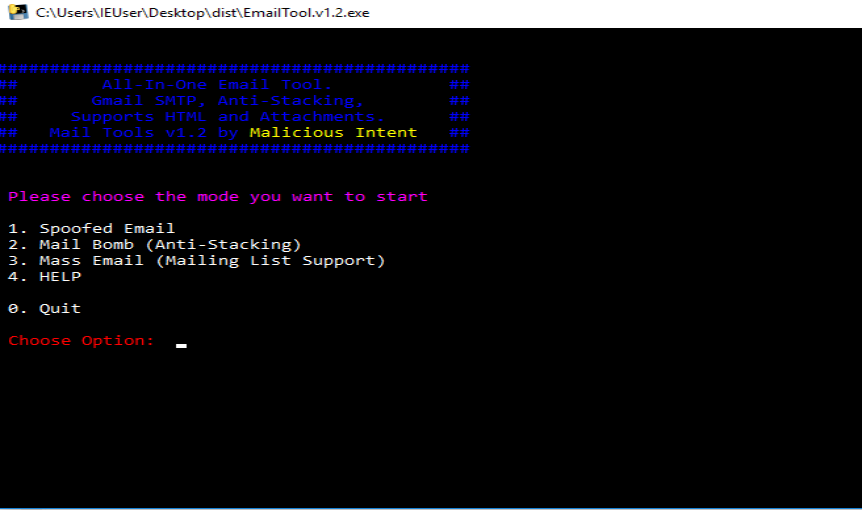
166Mail Tool v1.2 – E-mail spoofing tool
An all-in-one Email spoofing tool that works on Windows and Linux (via Wine).This tool is standalone and doesn’t require you to have...
-
 159
159Responder – An LLMNR, NBT-NS, and mDNS Poisoner
Responder an LLMNR, NBT-NS and MDNS poisoner. It will answer to specific NBT-NS (NetBIOS Name Service) queries based on their name suffix....
-

 177
177Cartero – Social Engineering Framework
A robust Phishing Framework with a full featured CLI interface. The project was born out necessity through of years of engagements with...
-
 219
219EvilURL – An unicode domain phishing generator for IDN Homograph Attack
(IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by...
-

 108
108WIG – Web Application Information Gathering Tool
WIG (WebApp Information Gatherer) is a web application information gathering tool, which can identify numerous Content Management Systems and other administrative applications....
-

 212
212Empire – Powershell Exploitation kit with Web Interface
Empire is a post-exploitation framework that includes a pure-PowerShell2.0 Windows agent, and a pure Python 2.6/2.7 Linux/OS X agent. The framework offers...
-
 249
249SQLiv – Massive SQL Injection Vulnerability Scanner
Massive SQL Injection Vulnerability Scanner Features multiple domain scanning with SQL injection dork by Bing, Google, or Yahoo targetted scanning by providing...
-

 193
193IoTivity – Open-Source IoT Framework
Each day more and more devices are coming online, adding to the ever-growing Internet of Things (IoT). Analysts agree the IoT will...
-
 183
183Faker.js – Generate Massive Amounts of Fake Data
Generate massive amounts of fake data in Node.js and the browser. Demo https://cdn.rawgit.com/Marak/faker.js/master/examples/browser/index.html Hosted API Microservice http://faker.hook.io Supports all Faker API Methods Full-Featured Microservice Hosted by hook.io curl...






