Hack Tools
-
 273
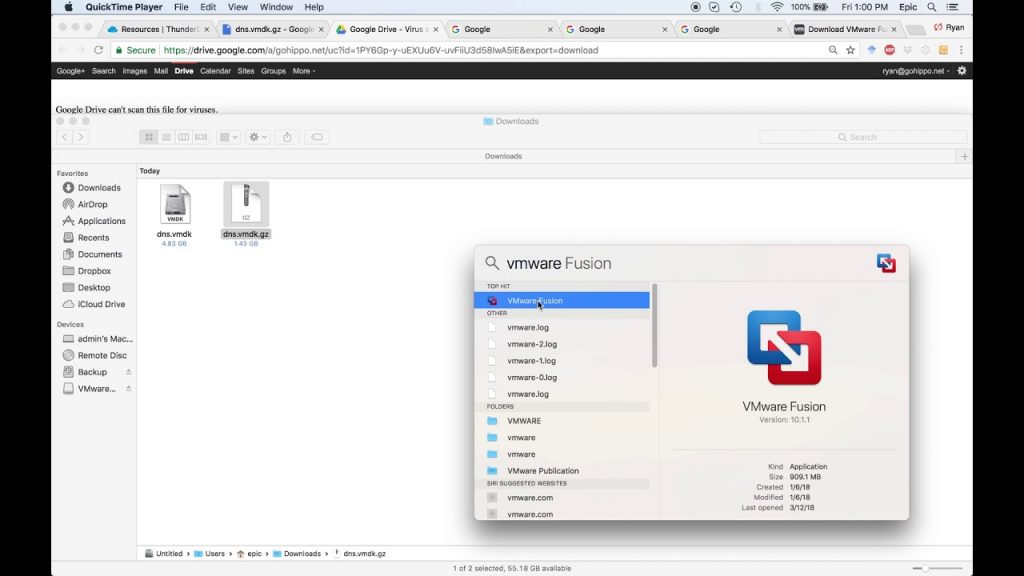
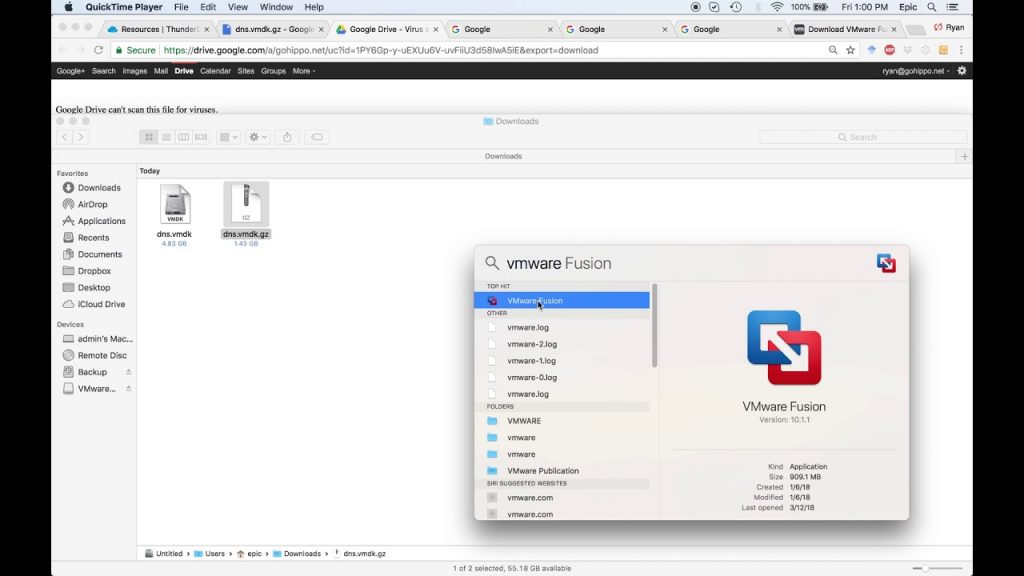
273ThunderDNS – Tool To Forward TCP Traffic Over DNS Protocol
This tool can forward TCP traffic over DNS protocol. Non-compile clients + socks5 support. Run Setting up NS records on our domain:...
-

 318
318Scavenger – A Post-Exploitation Scanning/Mapping Tool
SCAVENGER is a multi-threaded post-exploitation scanning tool for mapping systems and finding “interesting” and most frequently used files, folders and services. Once...
-

 274
274Real-time File Scanning System: Strelka
Strelka is a real-time file scanning system used for threat hunting, threat detection, and incident response. Based on the design established by...
-
 212
212AutoRDPwn – The Shadow Attack Framework
AutoRDPwn is a script created in Powershell and designed to automate the Shadow attack on Microsoft Windows computers. This vulnerability allows a...
-

 227
227Xenoscan – Open source memory scanner written in C++
XenoScan is a memory scanner which can be used to scan the memory of processes to locate the specific locations of important...
-

 203
203DVR-Exploiter : DVR-Exploiter a Bash Script Program Exploit The DVR’s
DVR-Exploiter a Bash Script Program Exploit The DVR’s Based on CVE-2018-999. [*] Exploit Title: DVR Credentials Exposed [*] Date: 09/04/2018 [*] Exploit...
-
 217
217Pwned – A Command-Line Tool For Querying The ‘Have I been Pwned?’ Service
A command-line tool for querying Troy Hunt’s Have I been pwned ? service using the hibp Node.js module. Pwned Installation Download and...
-

 229
229DbgShell – PowerShell Front-End for Windows Debugger Engine
The main impetus for DbgShell is that it’s just waaaay too hard to automate anything in the debugger. There are facilities today to assist...
-
 162
162Telegram Vulners Bot – Exploit Search Engine And Security Feed In Your Pocket
Vulners Bot is a Telegram interface for popular vulnerability database. It gives you availability of searching for exploits, tools, patches and many...
-
 223
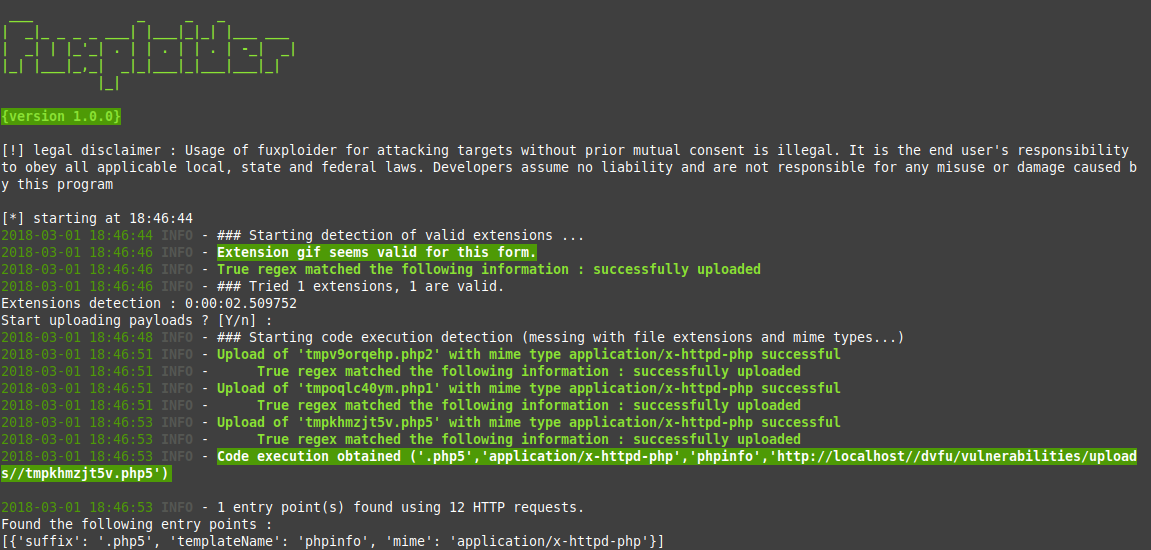
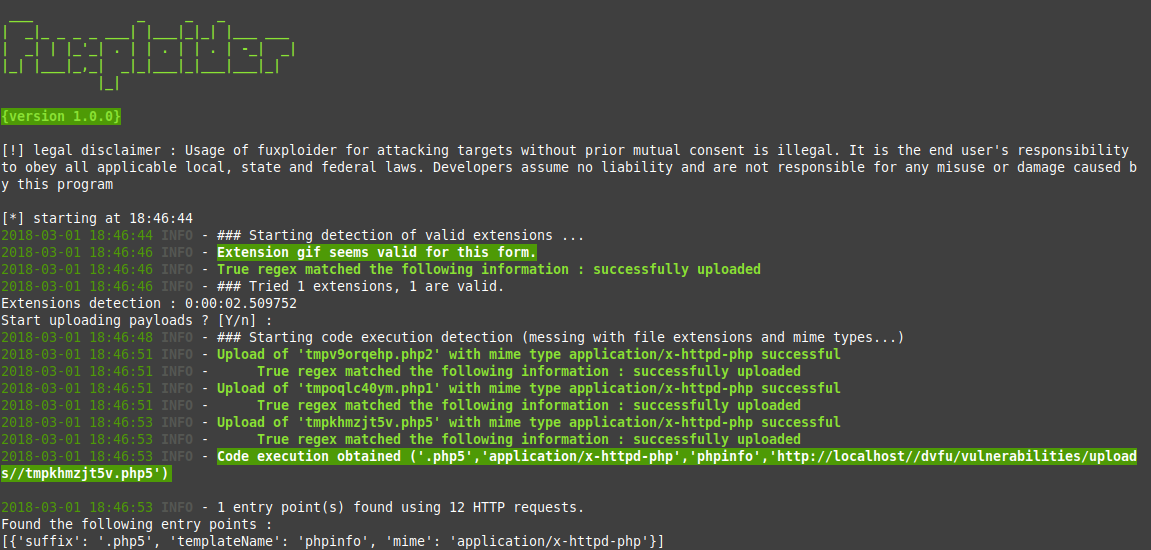
223Fuxploider – File upload vulnerability scanner and exploitation tool.
Fuxploider is an open source penetration testing tool that automates the process of detecting and exploiting file upload forms flaws. This tool...
-

 156
156Leaked? 1.1 – A Checking tool for Hash codes and Passwords leaked
Leaked? is A Checking tool for Hash codes and Passwords leaked, use API from @webtobesocial.Leaked? can work in any OS if they...
-
 228
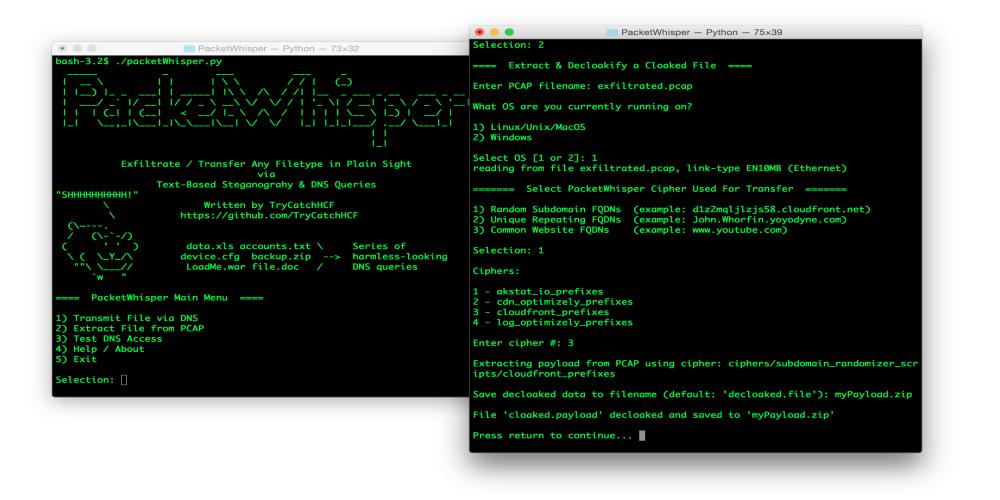
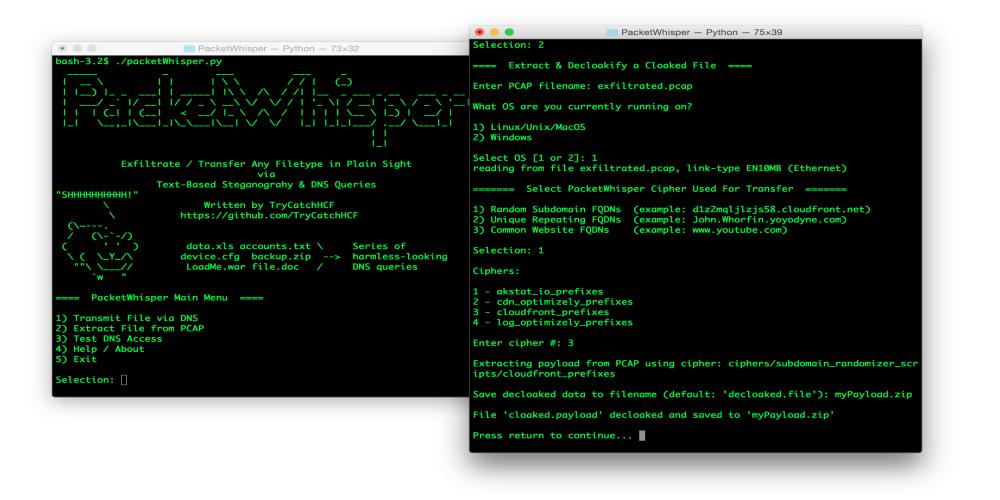
228PacketWhisper Exfiltration Toolset
PacketWhisper – Stealthily Transfer Data & Defeat Attribution Using DNS Queries & Text-Based Steganography, without the need for attacker-controlled Name Servers or...
-
 224
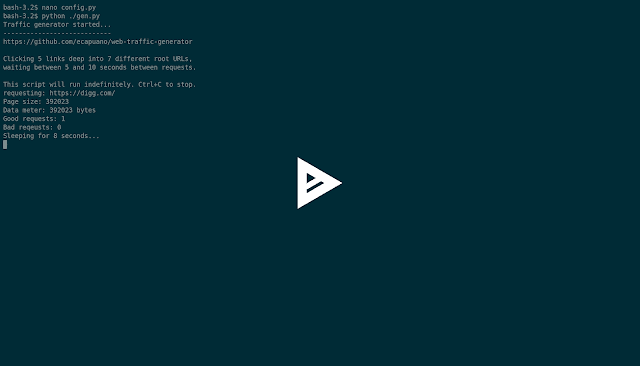
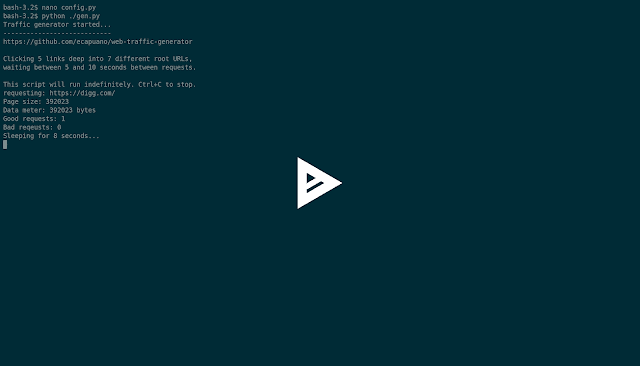
224Web Traffic Generator – A quick and dirty HTTP/S “organic” traffic generator.
Just a simple (poorly written) Python script that aimlessly “browses” the internet by starting at pre-defined rootURLs and randomly “clicking” links on...
-
 189
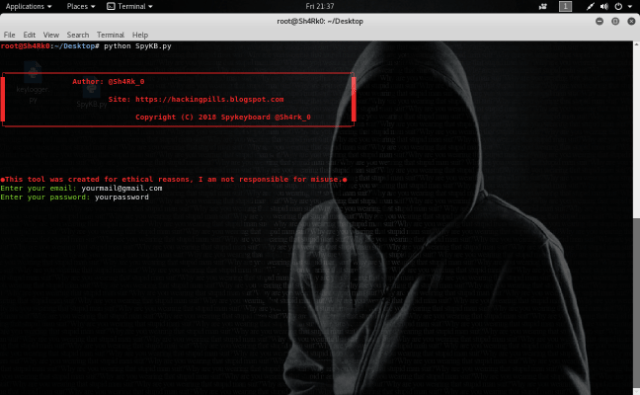
189Spykeyboard – Keylogger Which Sends Data to Gmail
Spykeyboard is a script which allows us to generate an undetectable keylogger which sends the captured keys to our gmail mail. Once...
-

 174
174Rootstealer – Trick To Inject Commands On Root Terminal
Rootstealer is an example of new attack using X11. This tool is used to detect when linux users open terminal with root...
-
 220
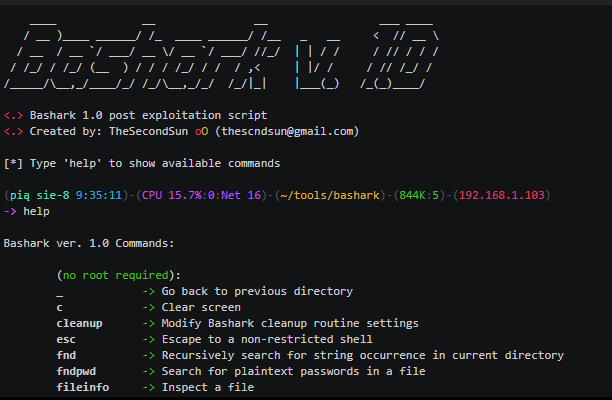
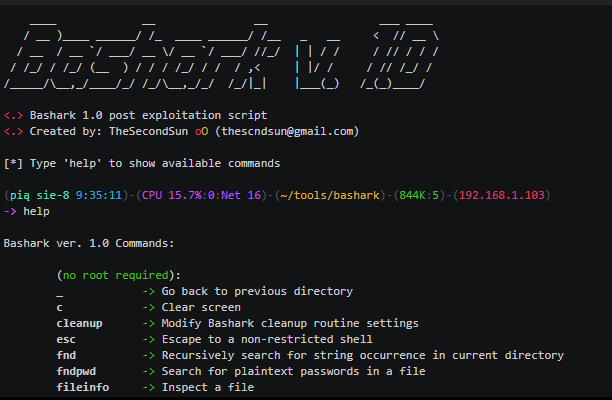
220Bashark- Post Exploitation Toolkit Written in Pure Bash
Bashark aids Pentesters and Security Researchers during the post-exploitation phase of security audits. Usage To launch Bashark on compromised host, simply source...
-
 215
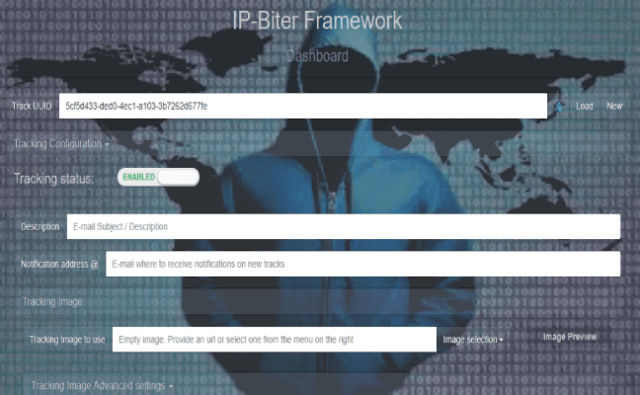
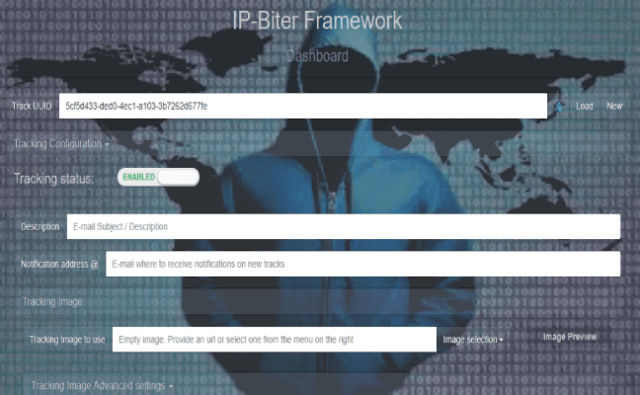
215IP-Biter : The Hacker-friendly E-Mail Tracking Framework
IP-Biter is an open source, easy to deploy, tracking framework that generate high configurable and unique tracking images and links to embed...
-

 237
237Evilginx – Advanced Man in the Middle Attack Framework
Evilginx is an attack framework for setting up phishing pages. Instead of serving templates of sign-in pages lookalikes, Evilginx becomes a relay between...
-
 170
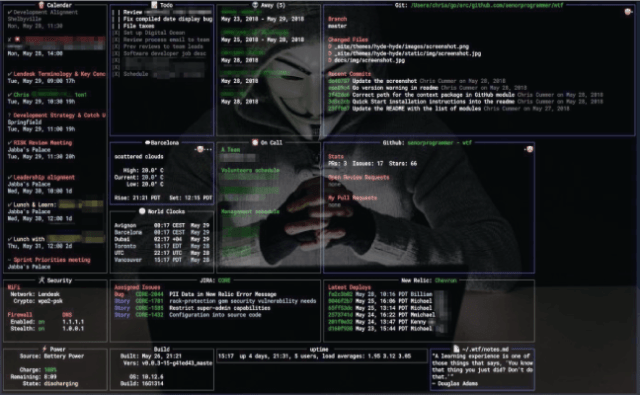
170WTF – A Personal Information Dashboard For Your Terminal
WTF is a personal terminal-based dashboard utility, designed for displaying infrequently-needed, but very important, daily data. WTF Installation There are two ways...
-
 193
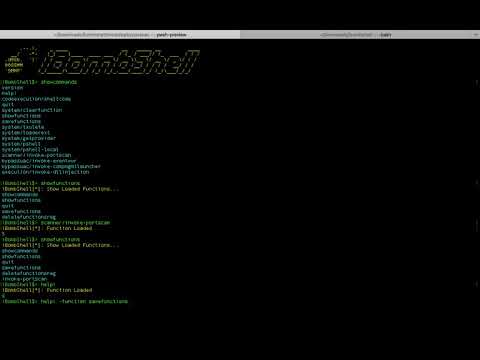
193ibombshell – Dynamic Remote Shell
ibombshell is a tool written in Powershell that allows you to have a prompt at any time with post-exploitation functionalities (and in...
-
 318
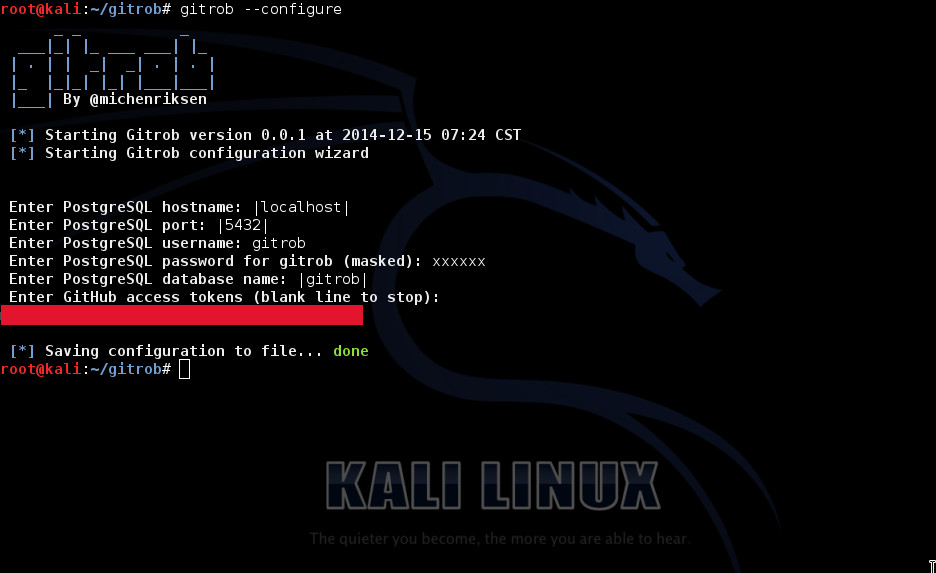
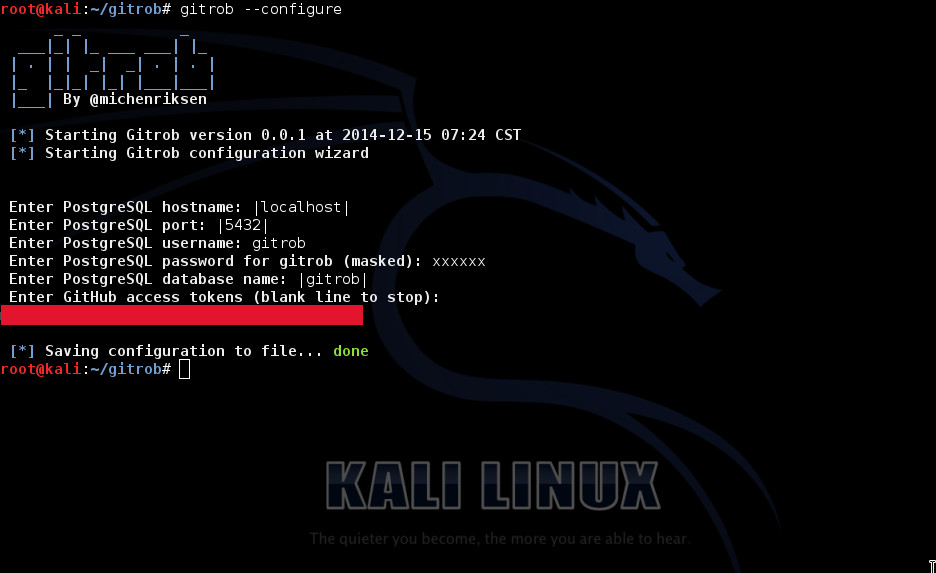
318Gitrob – Reconnaissance Tool for GitHub Organizations
Gitrob is a command line device which will help organizations and security professionals discover delicate data lingering in publicly accessible recordsdata on...






