Hack Tools
-
 194
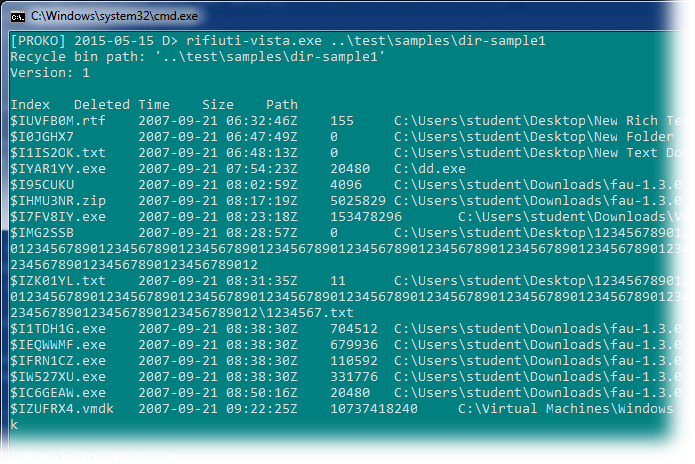
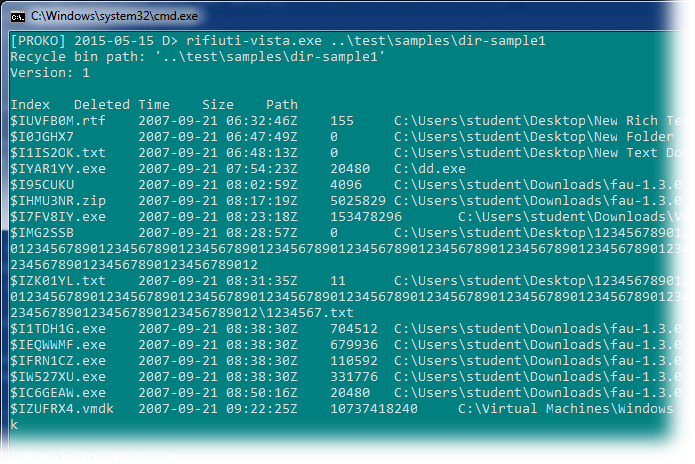
194Rifiuti2 – Windows Recycle Bin analyser
Rifiuti2 is a for analyzing Windows Recycle Bin INFO2 file. Analysis of Windows Recycle Bin is usually carried out during Windows computer...
-
 294
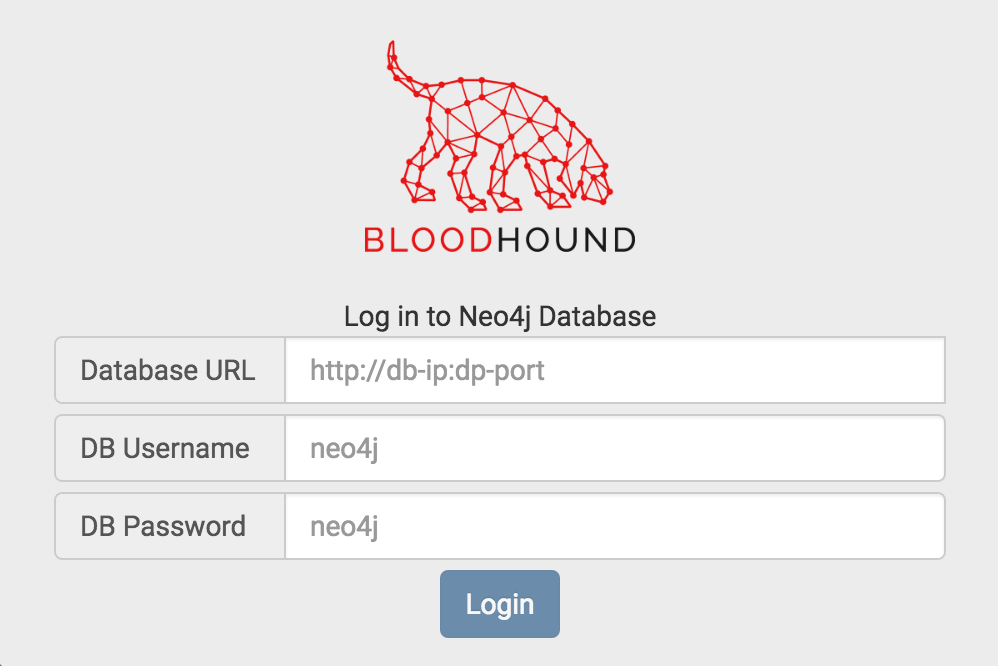
294Bloodhound v2.2 – Active Directory Toolkit
BloodHound is a single page Javascript web application, built on top of Linkurious, compiled with Electron, with a Neo4jdatabase fed by a PowerShell ingestor. BloodHound...
-
 346
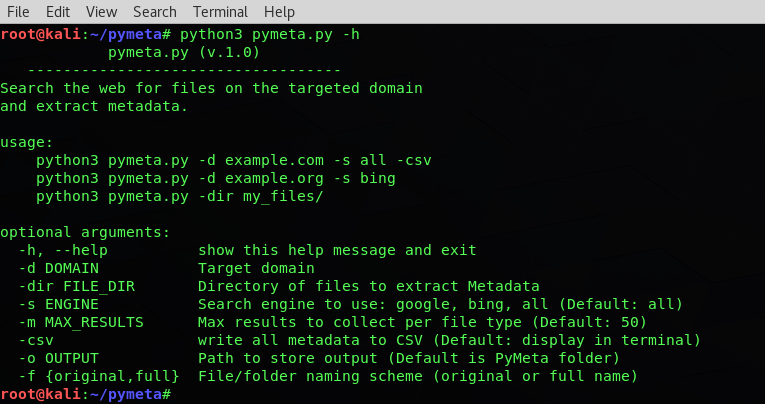
346PyMeta – Domain Metadata Extractor
Pymeta will search the web for files on a domain to download and extract metadata. This technique can be used to identify:...
-

 197
197Bandit – Designed to Find Common Security Issues in Python Code
Bandit is a tool designed to find common security issues in Python code. To do this Bandit processes each file, builds an...
-

 225
225AMIRA – Automated Malware Incident Response & Analysis
AMIRA is a service for automatically running the analysis on the OSXCollector output files. The automated analysis is performed via OSXCollector Output...
-
 232
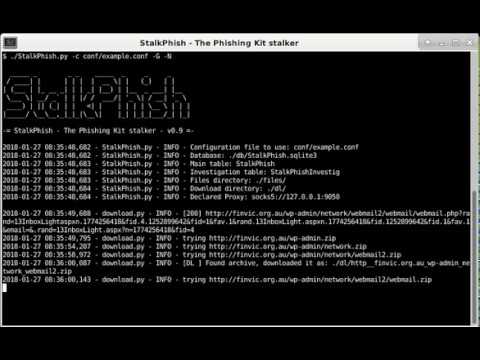
232StalkPhish – Harvesting Phishing Kits for Investigations.
StalkPhish is a tool created for searching into free OSINT databases for specific phishing kits URL. More, StalkPhish is designed to try...
-
 208
208Cryptr – Shell Utility for Encrypting and Decrypting Files using OpenSSL
A simple shell utility for encrypting and decrypting files using OpenSSL. Installation git clone https://github.com/nodesocket/cryptr.git ln -s "$PWD"/cryptr/cryptr.bash /usr/local/bin/cryptr Bash tab completion...
-

 239
2390xsp Mongoose – Linux Privilege Escalation Enumeration Toolkit
Using 0xsp mongoose you will be able to scan targeted operating system for any possible way for privilege escalation attacks,starting from collecting...
-
 329
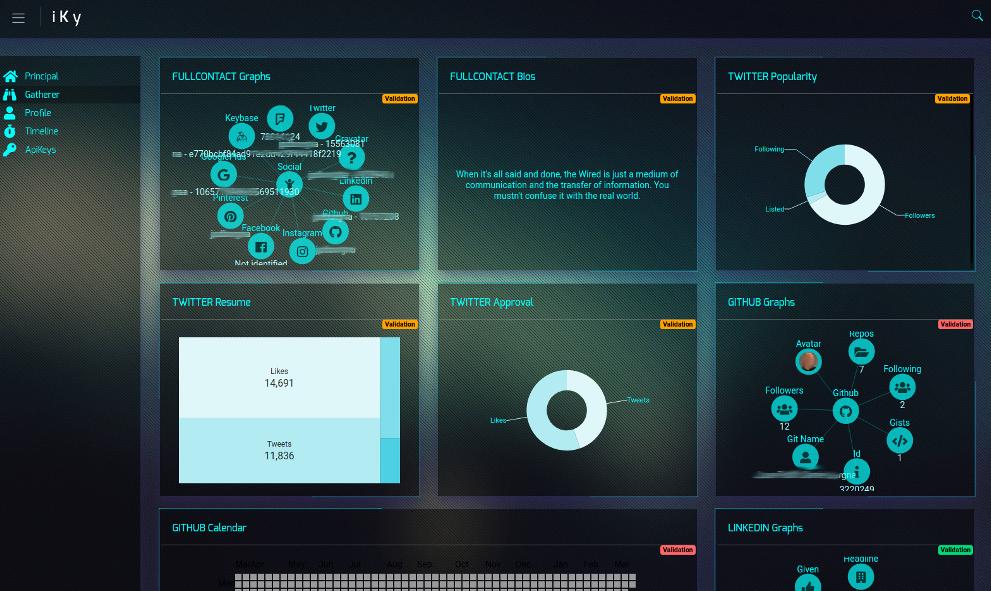
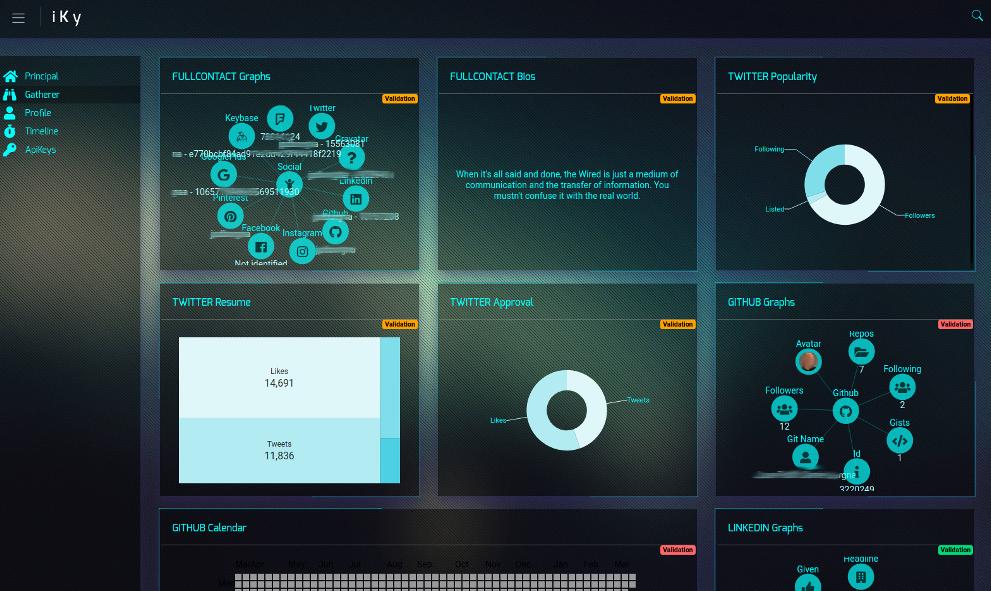
329Project iKy – Email Information Gathering Tool with a Visual Interface
Project iKy is a tool that collects information from an email and shows results in a nice visual interface. Video Demo Installation...
-

 216
216PivotSuite – A Network Pivoting Toolkit
PivotSuite is a portable, platform independent and powerful network pivoting toolkit, Which helps Red Teamers / Penetration Testers to use a compromised...
-
 197
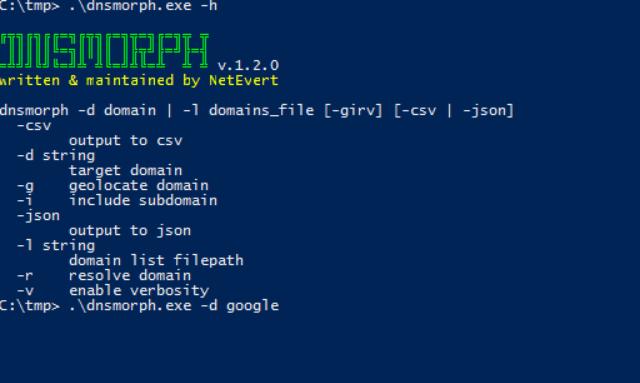
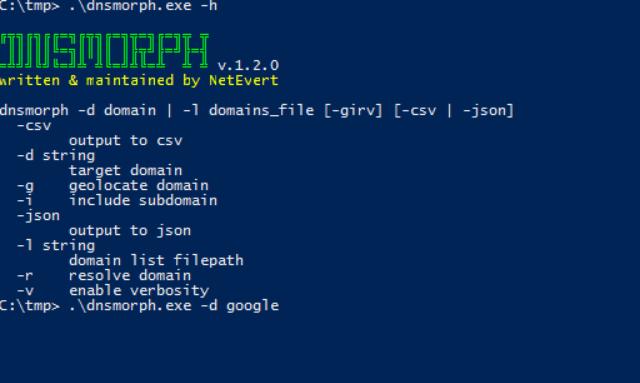
197DNSmorph – Domain Name Permutation Engine
DNSMORPH is a domain name permutation engine, inspired by dnstwist. It is written in Go making for a compact and very fast...
-
 167
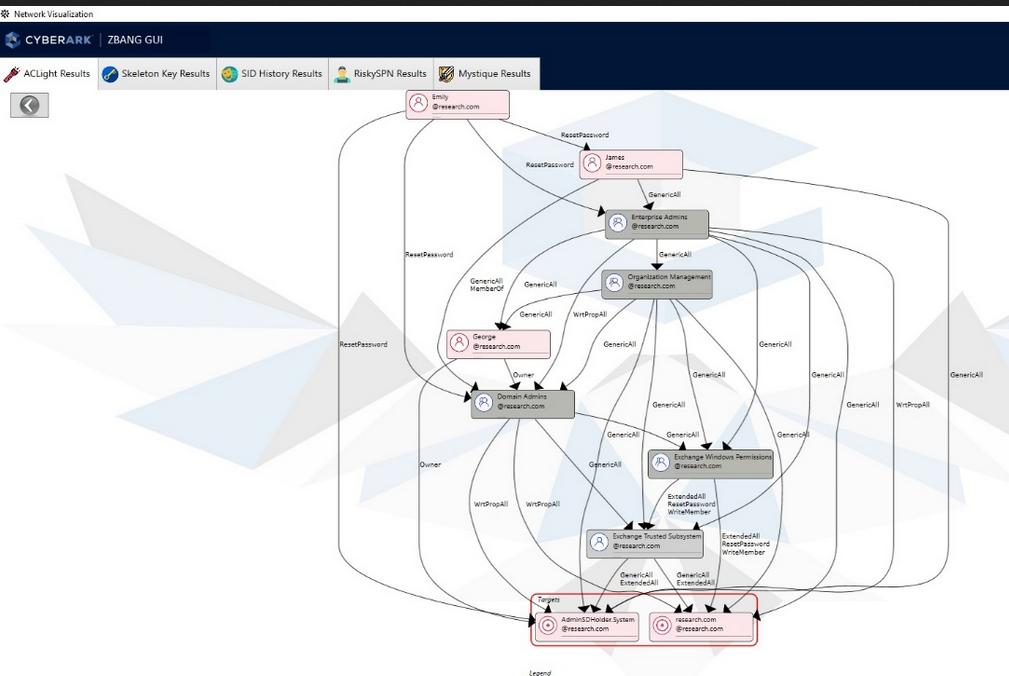
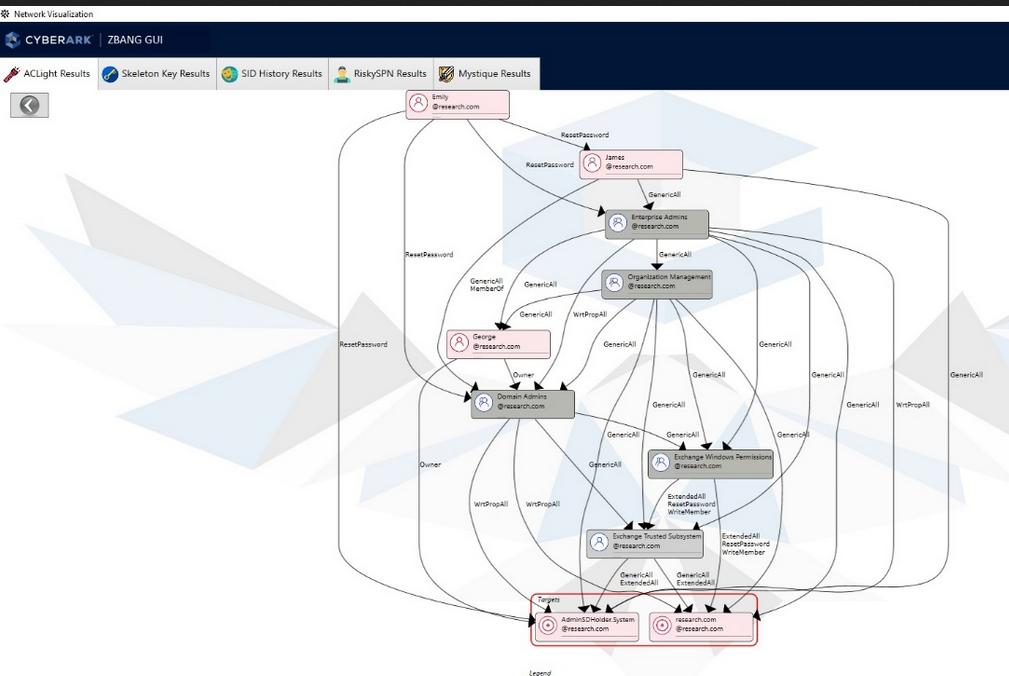
167zBang – Risk Assessment Tool that Detects Potential Privileged Account Threats
Organizations and red teamers can utilize zBang to identify potential attack vectors and improve the security posture of the network. The results...
-

 259
259CanaryTokens – Implant Honeypots in your Network
Network breaches happen. From mega-corps, to governments. From unsuspecting grandmas to well known security pros. This is (kinda) excusable. What isn’t excusable,...
-
 434
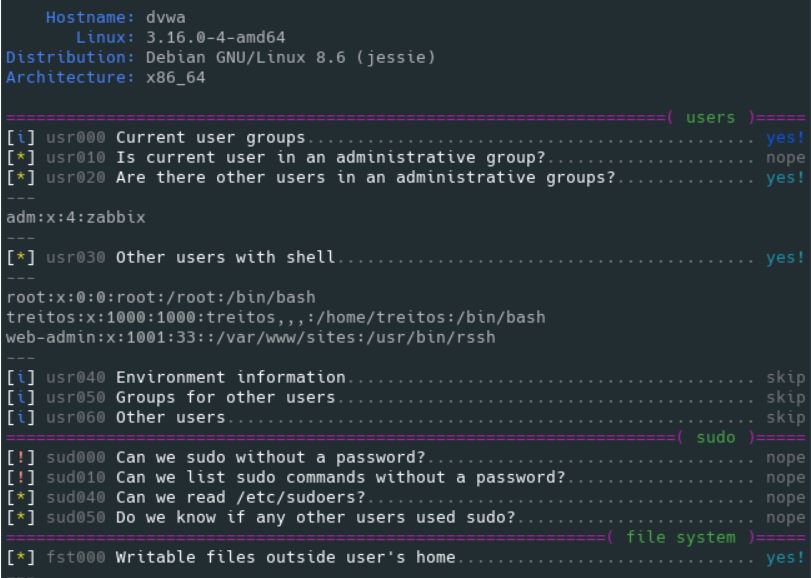
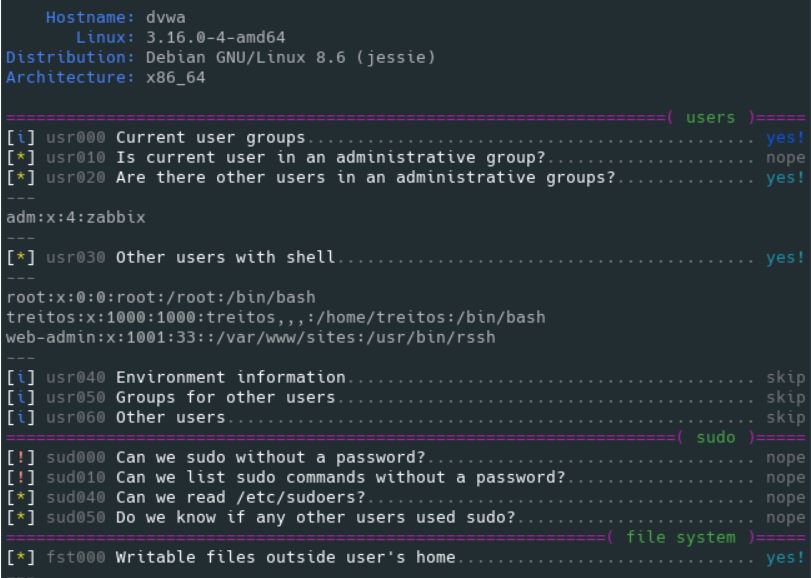
434Linux Smart Enumeration – Enumeration Tool for Pentesting and CTFs with Verbosity Levels
Linux enumeration tools for pentesting and CTFs. This project was inspired by https://github.com/rebootuser/LinEnum and uses many of its tests. Unlike LinEnum, lse...
-
 272
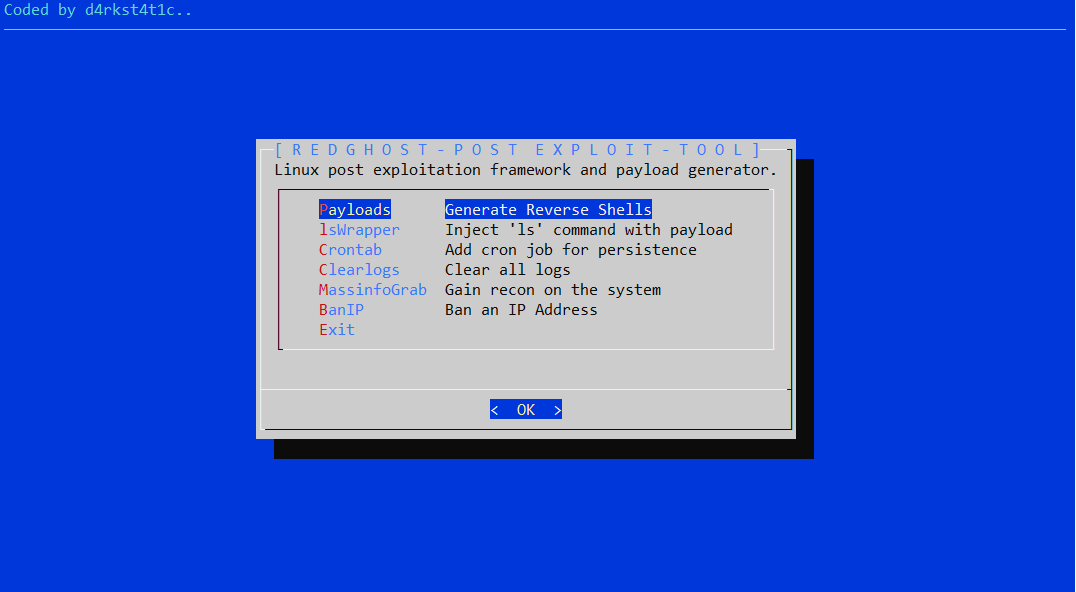
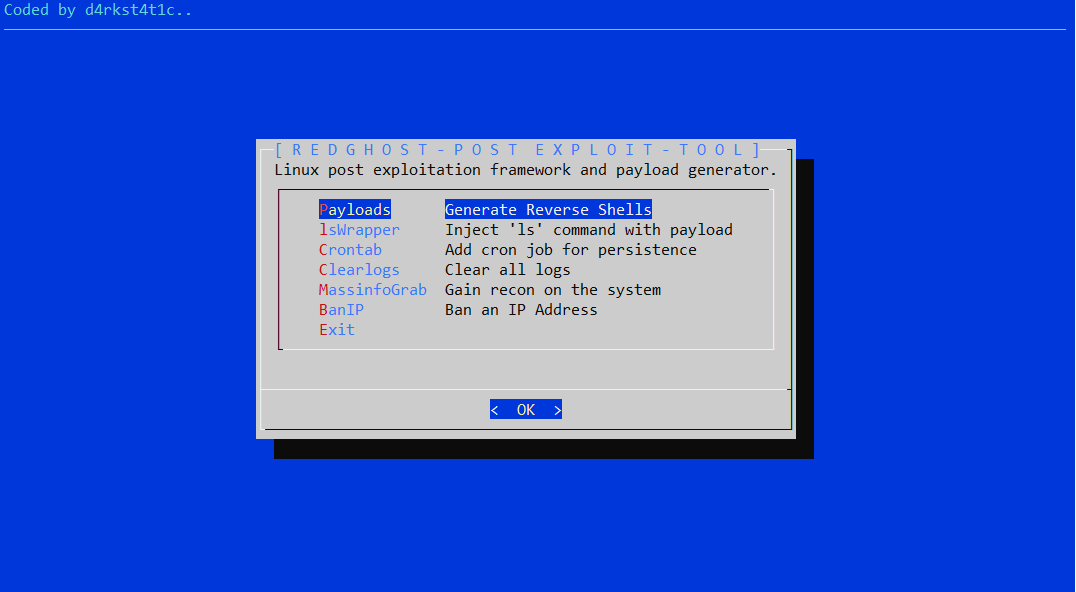
272RedGhost – Linux Post Exploitation Framework
Linux post exploitation framework designed to assist red teams in gaining persistence, reconnaissance and leaving no trace. RedGhost Features Payloads Function to...
-
 245
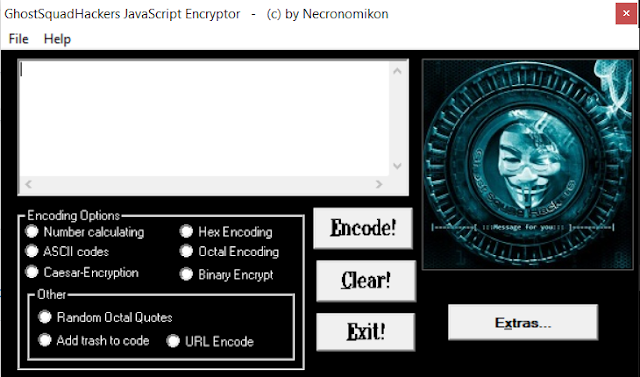
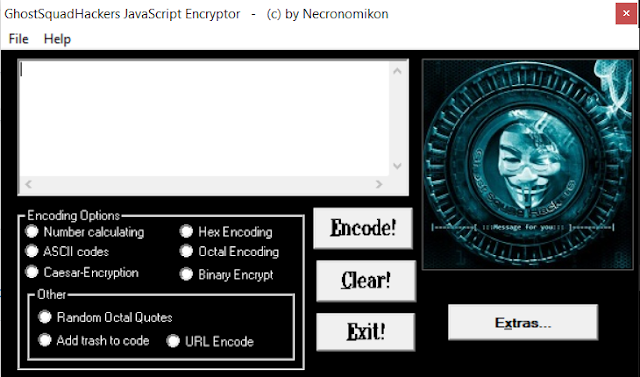
245GhostSquadHackers – Encrypt/Encode Your Javascript Payloads
This tool is meant to encode and encrypt your javascript code/payloads. Features Number Calculating ASCII codes Caeser-Encryption Hex Encoding Octal encoding Binary...
-

 357
357Kippo – SSH Honeypot
Kippo is a medium interaction SSH honeypot designed to log brute force attacks and, most importantly, the entire shell interaction performed by...
-
 175
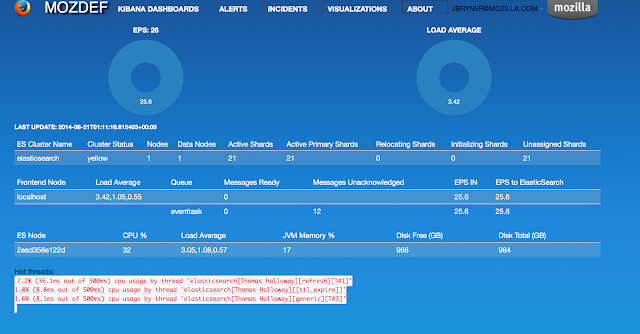
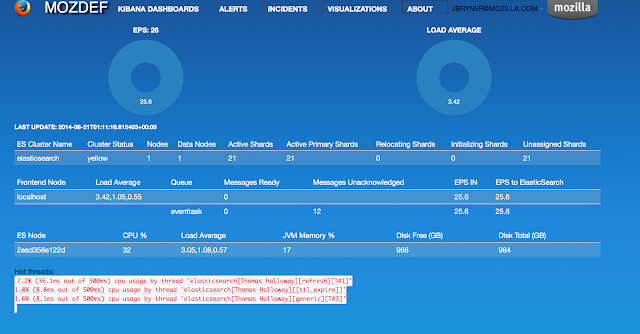
175MozDef: Mozilla Enterprise Defense Platform
The Mozilla Enterprise Defense Platform (MozDef) seeks to automate the security incident handling process and facilitate the real-time activities of incident handlers....
-
 217
217Terminus – A Terminal for a more Modern Age
Terminus is a highly configurable terminal emulator for Windows, macOS and Linux Features Theming and color schemes Fully configurable shortcuts Split panes...
-

 201
201RKHunter – Scans Linux for Rootkits & Backdoors
Rootkit Hunter is a scanner tool for Linux that scans for backdoors, rootkits and local exploits on your systems. Installs all dependencies...
-

 207
207Pacu – AWS Exploitation Framework
Pacu is an open source AWS exploitation framework created and maintained by Rhino Security Labs to assist in offensive security testing against...






