Hack Tools
-

 3.9K
3.9KSeeker v1.1.9 – Accurately Locate Smartphones Using Social Engineering
Concept behind Seeker is simple, just like we host phishing pages to get credentials why not host a fake page that requests...
-
 759
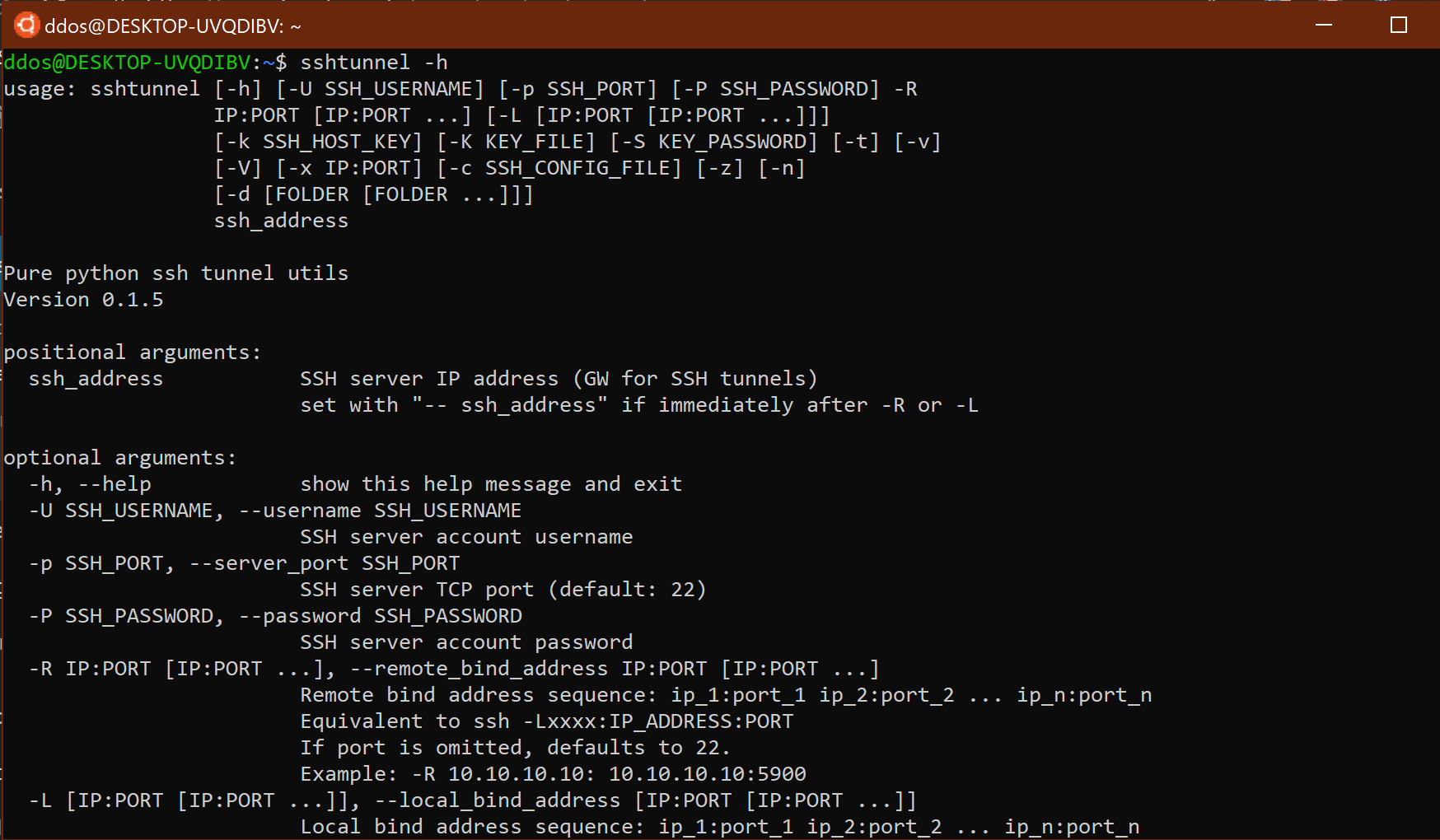
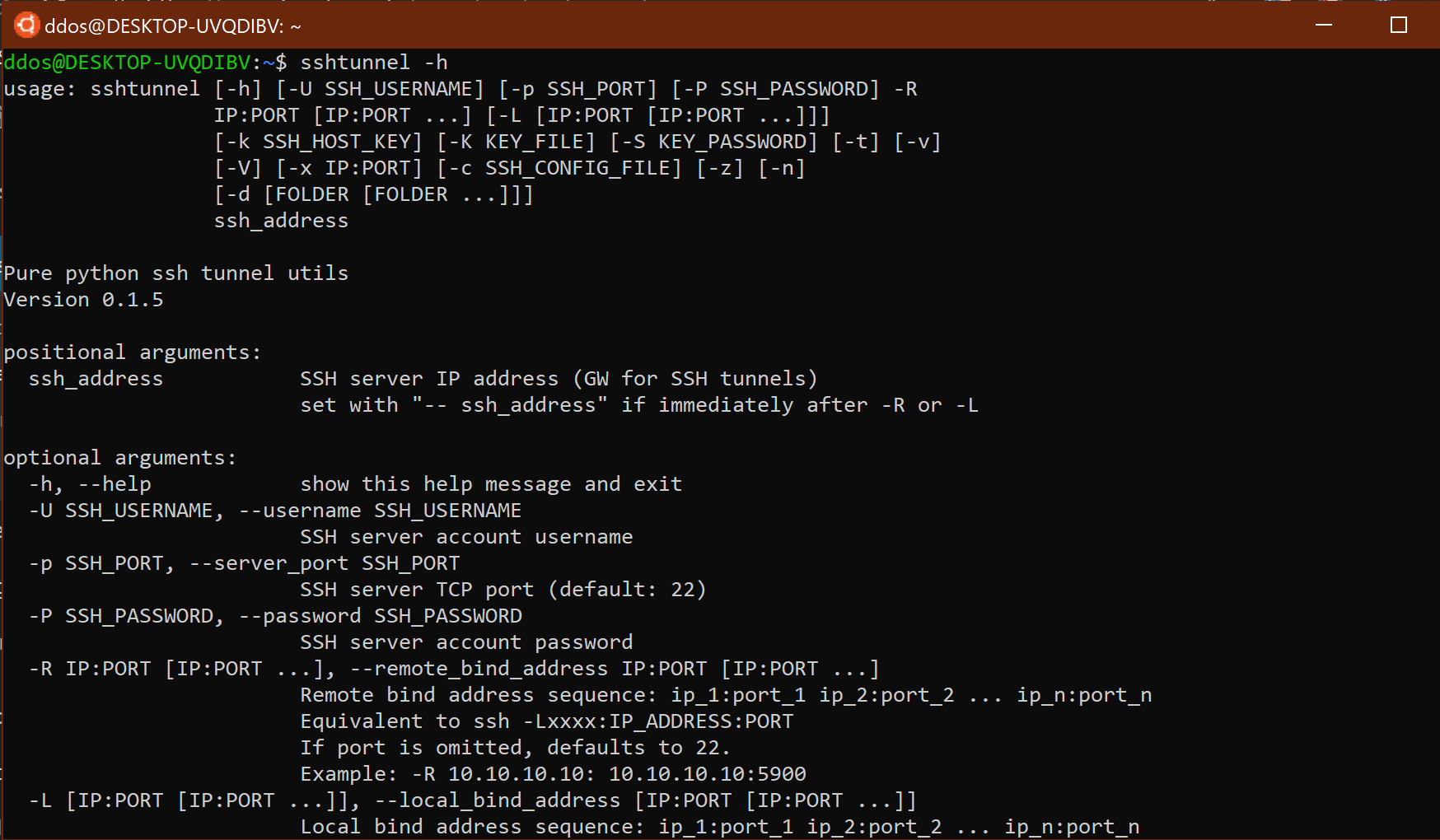
759ssh tunnel: SSH tunnels to remote server
ssh tunnel SSH tunnels to a remote server.API allows either initializing the tunnel and starting it or using a with context, which...
-
 1.9K
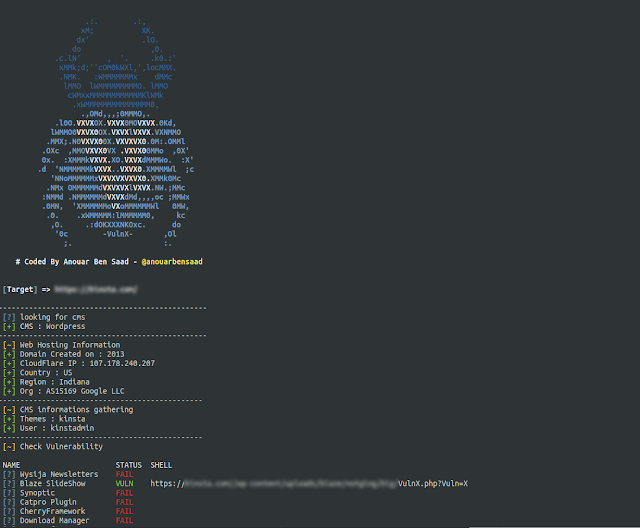
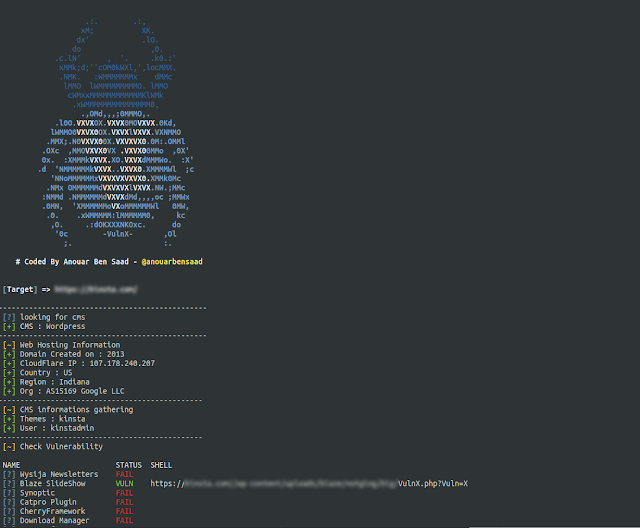
1.9KVulnx v1.9 – An Intelligent Bot Auto Shell Injector That Detect Vulnerabilities In Multiple Types Of CMS (WordPress, Joomla, Drupal, Prestashop…)
Vulnx is An Intelligent Bot Auto Shell Injector that detect vulnerabilities in multiple types of Cms, fast cms detection,informations gathering and vulnerabilitie...
-
 3.6K
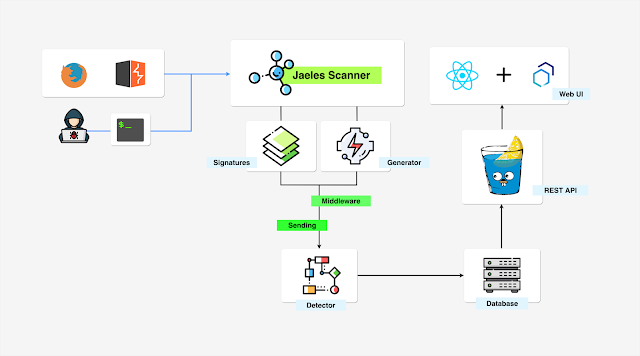
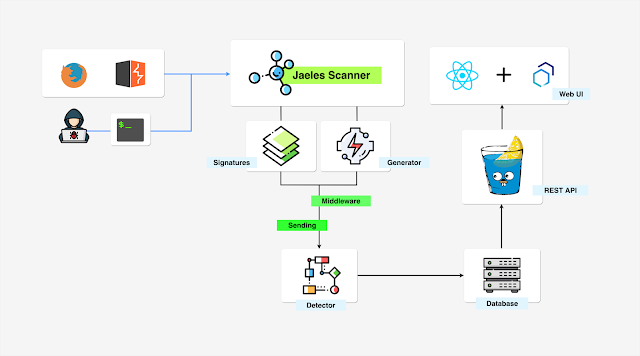
3.6KJaeles – The Swiss Army Knife For Automated Web Application Testing
Jaeles is a powerful, flexible and easily extensible framework written in Go for building your own Web Application Scanner.Installation go get -u...
-

 2.5K
2.5Kmihari v0.15 releases: a sidekick tool for TheHive for monitoring malicious hosts continuously
mihari mihari is a sidekick tool for TheHive for monitoring malicious hosts (C2 / landing page/phishing, etc.) continuously. How it works mihari makes a...
-

 4.4K
4.4Kkubesec v2.3.1 alpha releases: Security risk analysis for Kubernetes resources
kubesec Security risk analysis for Kubernetes resources Changelog v2.3.1 alpha 76b2707 Modified the GH actions release to work with go modules b96a1d6 Swapped goreleaser...
-

 4.3K
4.3KRFI/LFI Payload List
As with many exploits, remote and local file inclusions are only a problem at the end of the encoding. Of course it...
-

 3.6K
3.6KSigma Hunting App: containing Sigma detection rules
Sigma Hunting App A Splunk App containing Sigma detection rules, which can be updated dynamically from a Git repository. Motivation Most of...
-
 3.9K
3.9KEvil-Winrm v1.9 – The Ultimate WinRM Shell For Hacking/Pentesting
This shell is the ultimate WinRM shell for hacking/pentesting. WinRM (Windows Remote Management) is the Microsoft implementation of WS-Management Protocol. A standard...
-
 4.9K
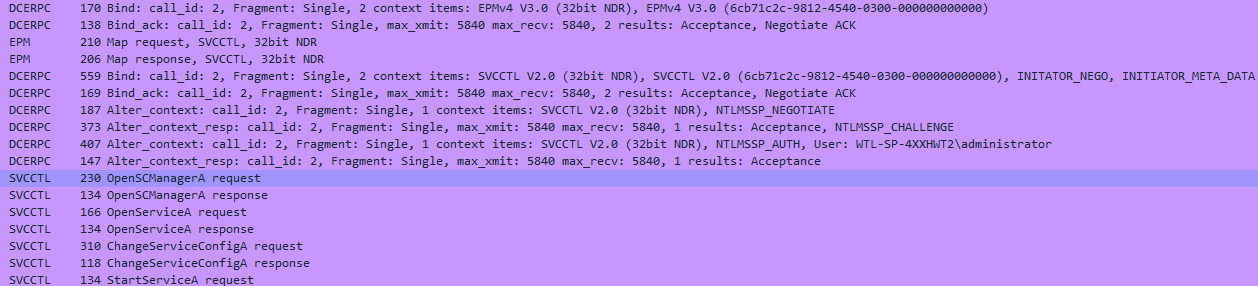
4.9KSCShell: Fileless lateral movement tool to run command
SCShell Fileless lateral movement tool that relies on ChangeServiceConfigA to run command. The beauty of this tool is that it doesn’t perform...
-
 3.5K
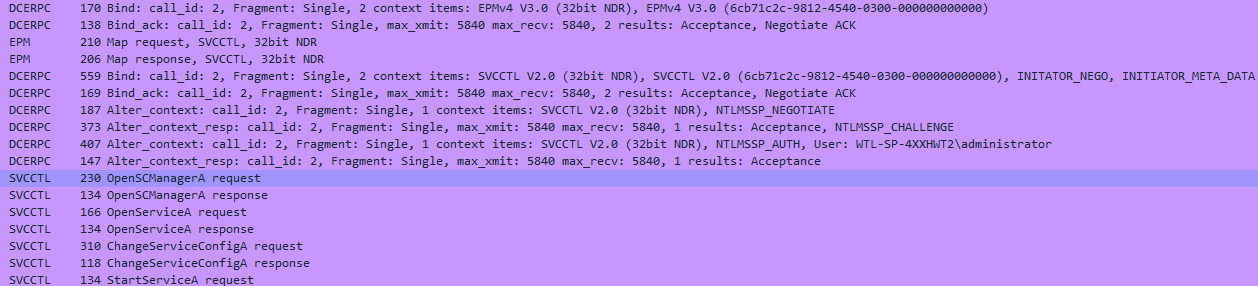
3.5KRainbow Crackalack – Rainbow Table Generation And Lookup Tools
This project produces open-source code to generate rainbow tables as well as use them to look up password hashes. While the current...
-
 4.0K
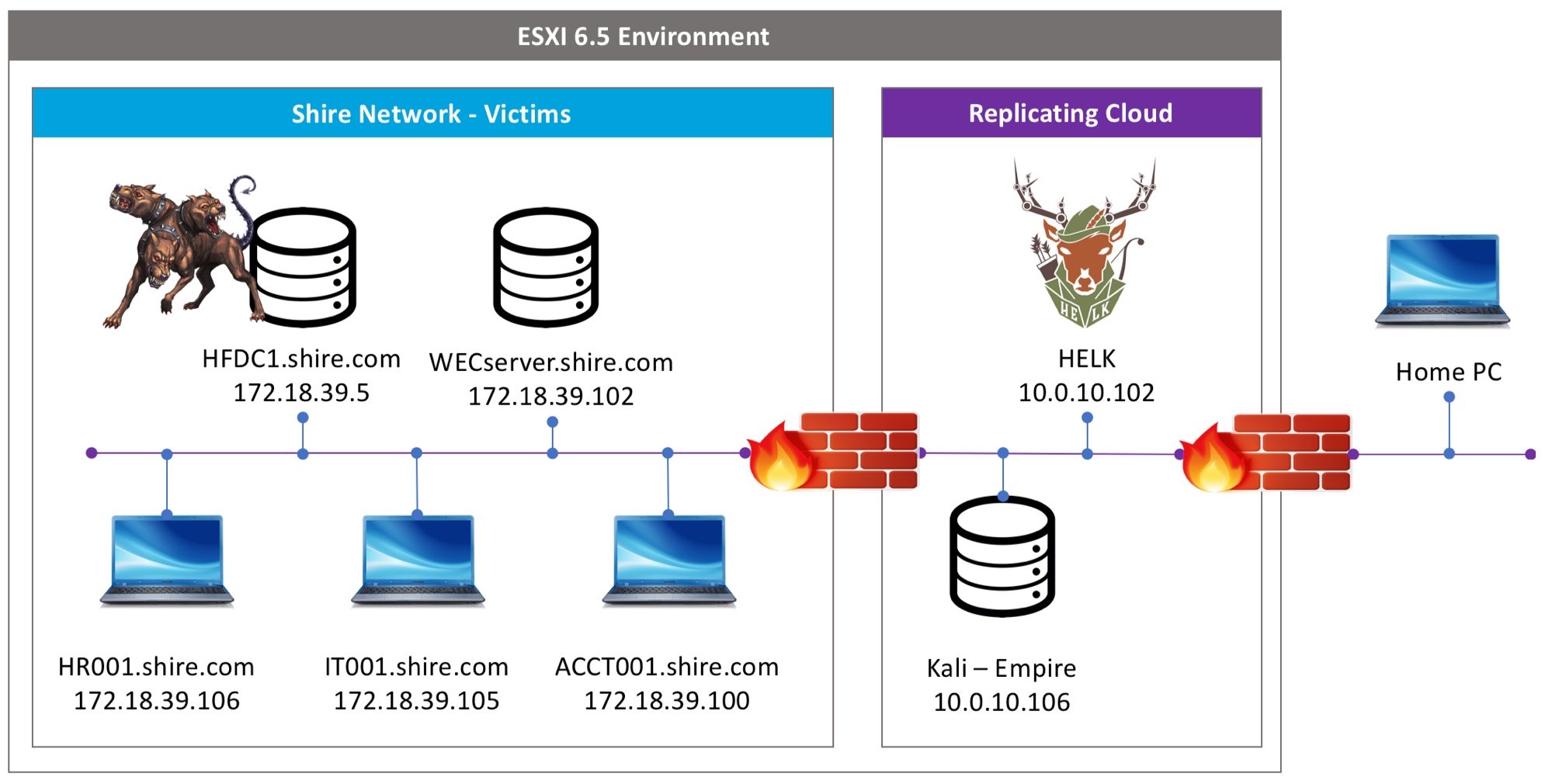
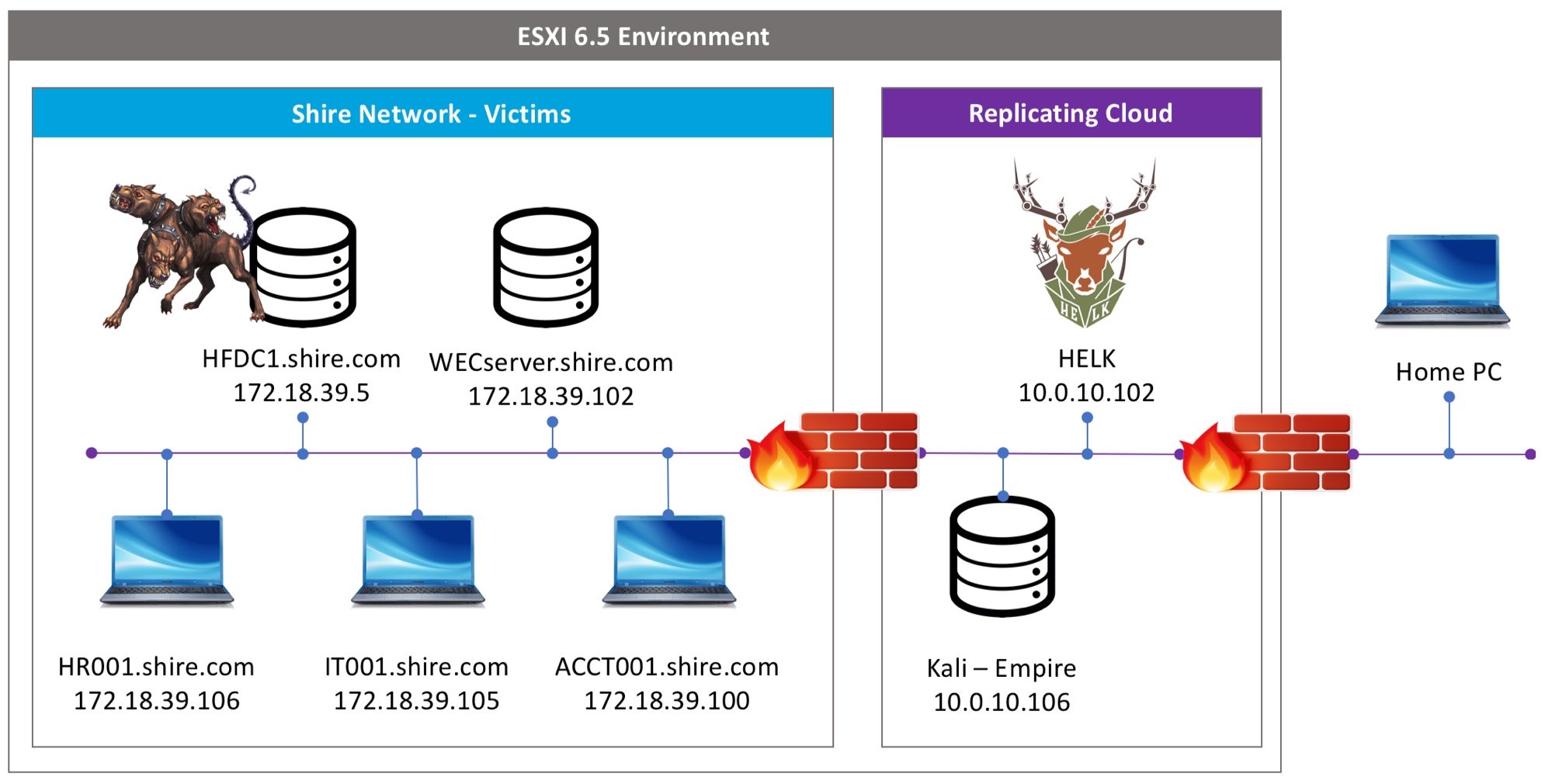
4.0Kmordor: provides pre-recorded security events
Mordor Gates The Mordor project provides pre-recorded security events generated by simulated adversarial techniques in the form of JavaScript Object Notation (JSON)...
-

 5.4K
5.4KBrave Browser – Next Generation Secure, Fast And Private Web Browser with Adblocker
The Brave Privacy Browser is your fast, safe private web browser with ad blocker, private tabs and pop-up blocker. Browse without being...
-

 565
565leprechaun: map out the network data flow
Leprechaun The purpose of this tool is to help penetration testers identify potentially valuable targets on the internal network environment. By aggregating...
-
 2.8K
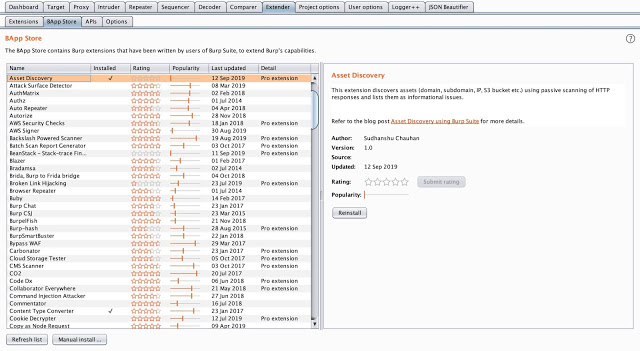
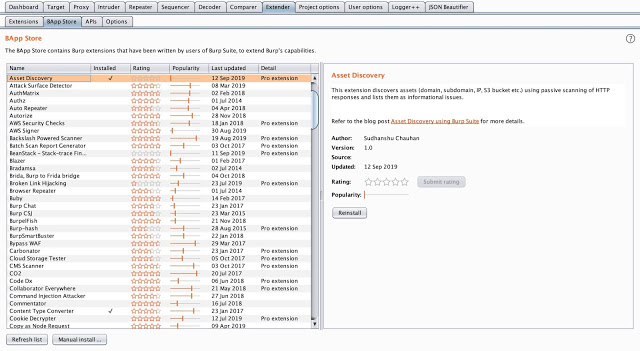
2.8KAsset Discover – Burp Suite Extension To Discover Assets From HTTP Response
Burp Suite extension to discover assets from HTTP response using passive scanning. Refer our blog Asset Discovery using Burp Suite for more...
-

 4.3K
4.3KFrom Code to Color – Understanding User Interface
Developing the next great app or a fully functional website is something every developer strives for. Crafting lines of code that roll...
-
 4.6K
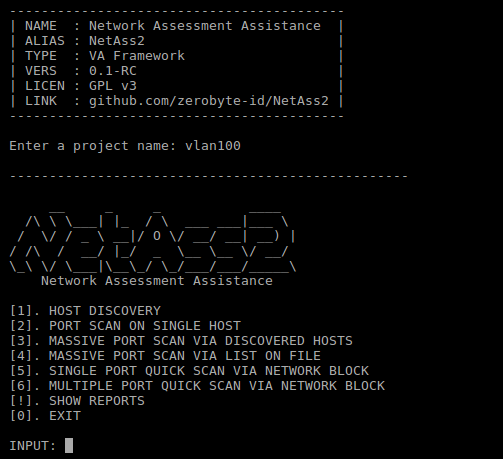
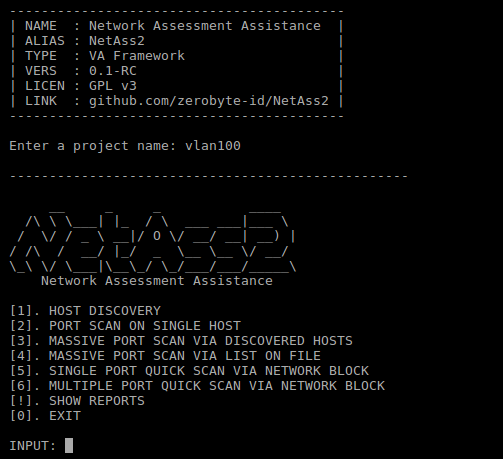
4.6KNetAss2 – Network Assessment Assistance Framework
Easier network scanning with NetAss2 (Network Assessment Assistance Framework). Make it easy for Pentester to do penetration testing on network. Dependencies nmap...
-
 4.9K
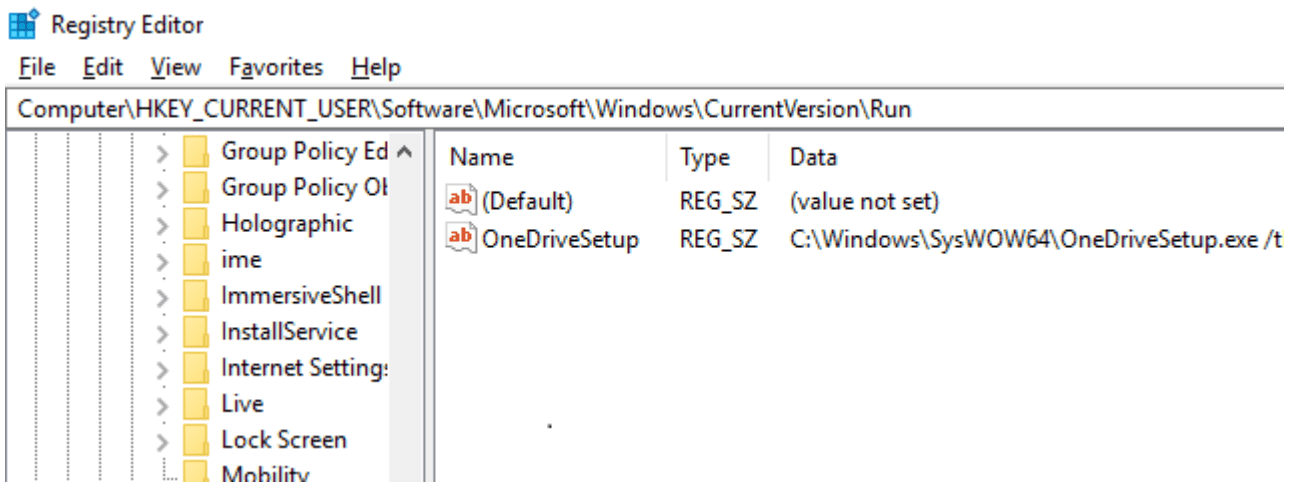
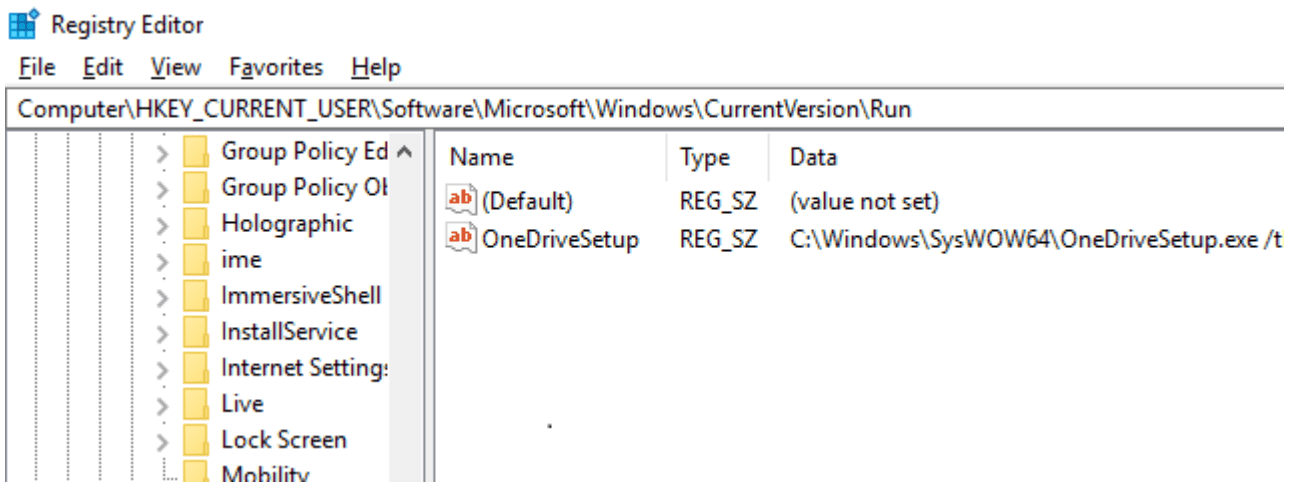
4.9KSharpHide: Tool to create hidden registry keys
SharpHide Just a nice persistence trick to confuse DFIR investigation. Uses NtSetValueKey native API to create a hidden (null-terminated) registry key. This...
-

 3.2K
3.2KRsdl – Subdomain Scan With Ping Method
Subdomain Scan With Ping Method. Flags Value Description –hostname example.com Domain for scan. –output Records the output with the domain name. –list...
-
 4.0K
4.0Kapk-mitm v0.5.3 releases: A CLI application that prepares Android APK files for HTTPS inspection
apk-mitm A CLI application that automatically prepares Android APK files for HTTPS inspection Inspecting a mobile app’s HTTPS traffic using a proxy...
-
 1.5K
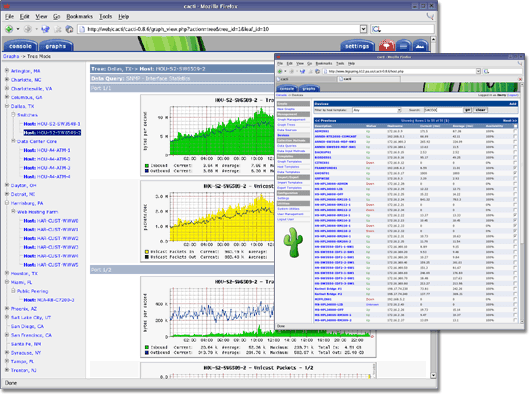
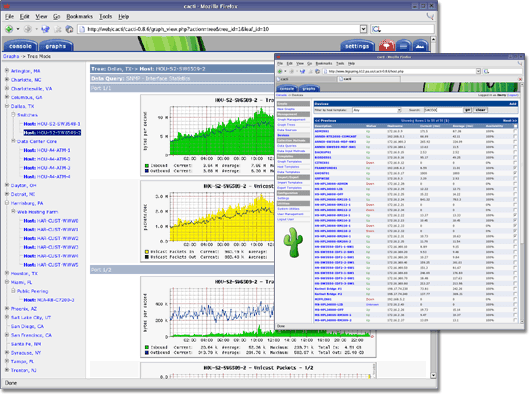
1.5KCacti – Complete Network Graphing Solution
IMPORTANTWhen using source or by downloading the code directly from the repository, it is important to run the database upgrade script if...






