Hack Tools
-

 219
219Seth – Perform a MitM Attack and Extract clear text Credentials from RDP
Seth is a tool written in Python and Bash to MitM RDP connections by attempting to downgrade the connection in order to...
-
 267
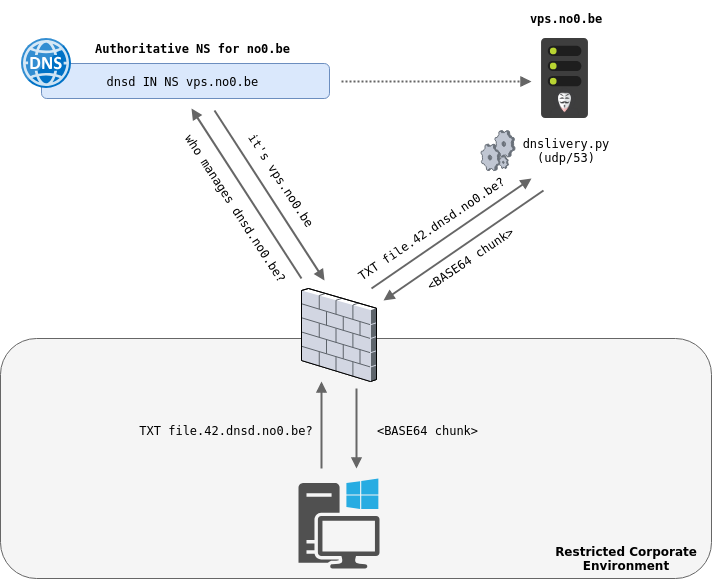
267DNSlivery – Files and Payloads Delivery Over DNS
DNSlivery allows to deliver files to a target using DNS as the transport protocol and has been inspired by PowerDNS and Joff...
-

 334
334Beemka – Electron Exploitation Toolkit
Beemka shows how vulnerabilities in the Electron Framework could allow an attacker to inject malicious code inside a legitimate application without raising...
-

 667
667Th3Inspector – All in one Tool for Information Gathering
One of the most useful tools for gathering information on someone, business, a domain, ip address and websites. Usage Short Form Long...
-

 421
421Network Penetration Testing Tools for Hackers and Security Professionals
Network Security tools for Penetration testing is more often used by security industries to test the vulnerabilities in network and applications. Here...
-

 1.1K
1.1KCardPWN – OSINT Tool to find Breached Credit Card Information
CardPwn Searches for the breached credit card details avaliable on the following 17 Websites:- * cl1p.net * dpaste * dumpz.org * hastebin...
-
 439
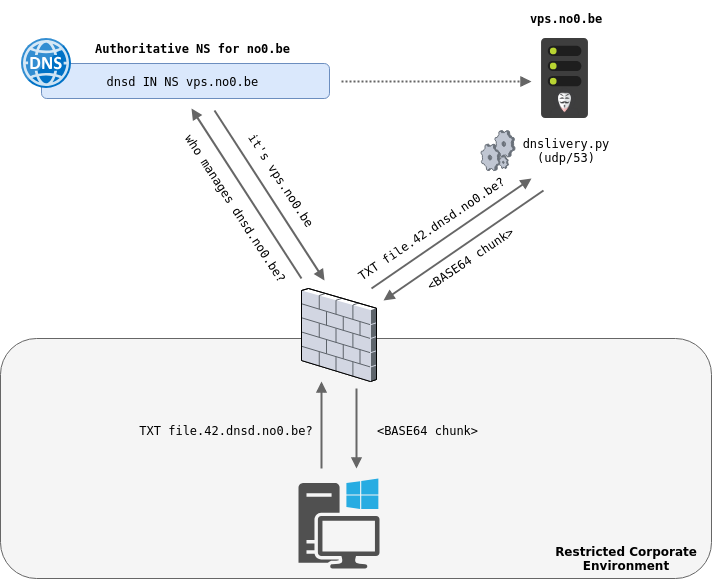
439Fingerprint All The Things – Pyshark Script for Extracting Network Metadata and Fingerprints from Pcap Files or Live Network Traffic
A script for extracting network metadata and fingerprints such as JA3 and HASSH from packet capture files (pcap) or live network traffic....
-
 257
257Kubolt – Utility for Scanning Public Kubernetes Clusters
Kubolt is simple utility for scanning public unauthinticated kubernetes clusters and run commands inside containers Why? Sometimes, the kubelet port 10250 is...
-
 312
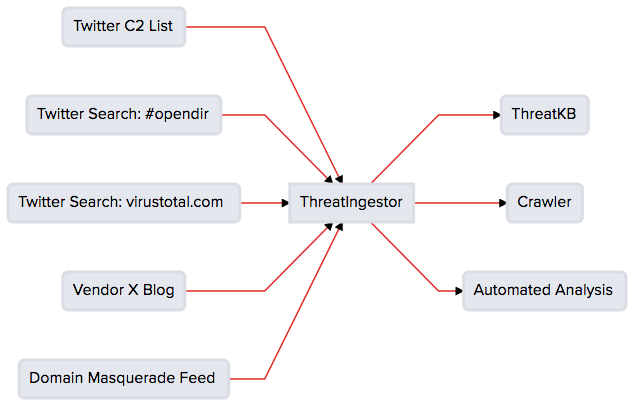
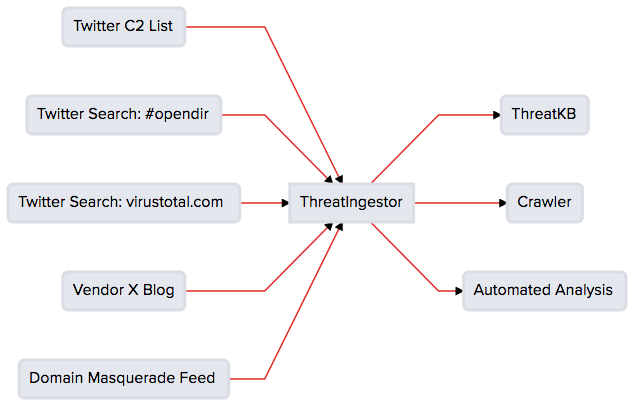
312ThreatIngestor – Extract and Aggregate Threat Intelligence
An extendable tool to extract and aggregate IOCs from threat feeds. Integrates out-of-the-box with ThreatKB and MISP, and can fit seamlessly into...
-
 303
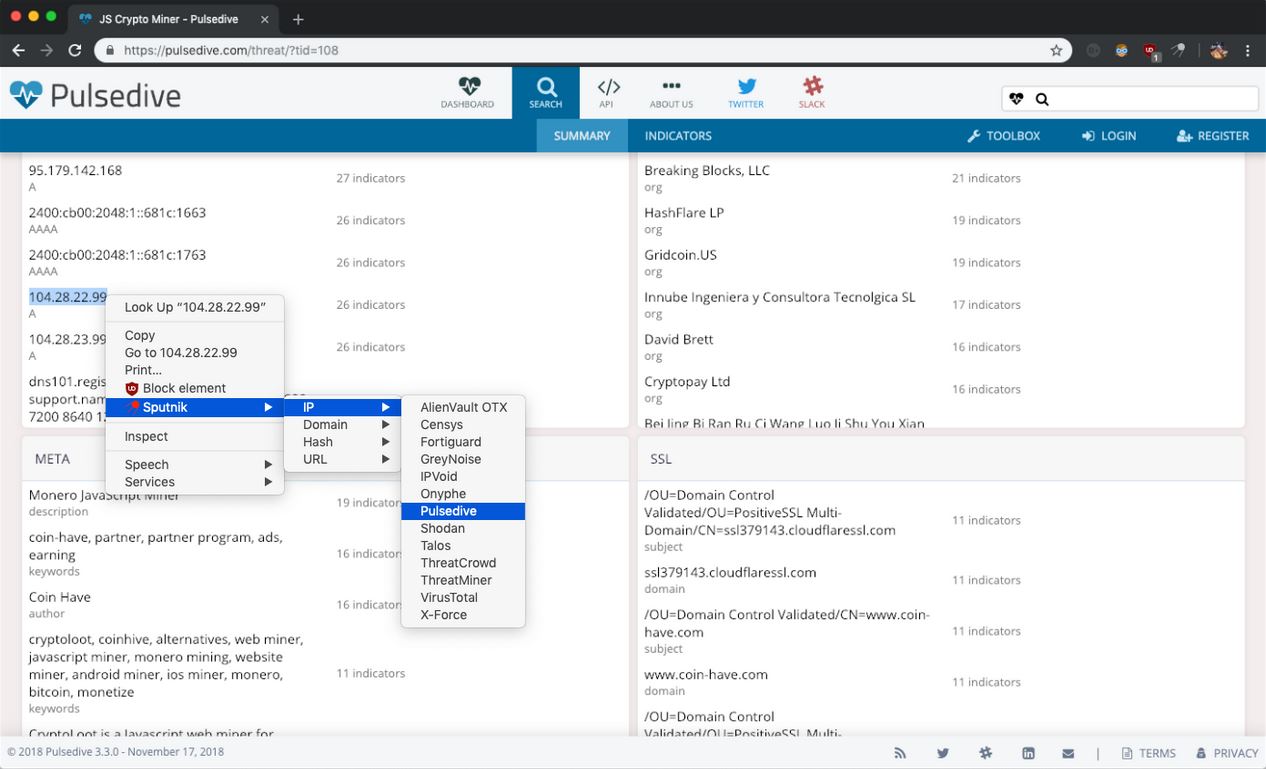
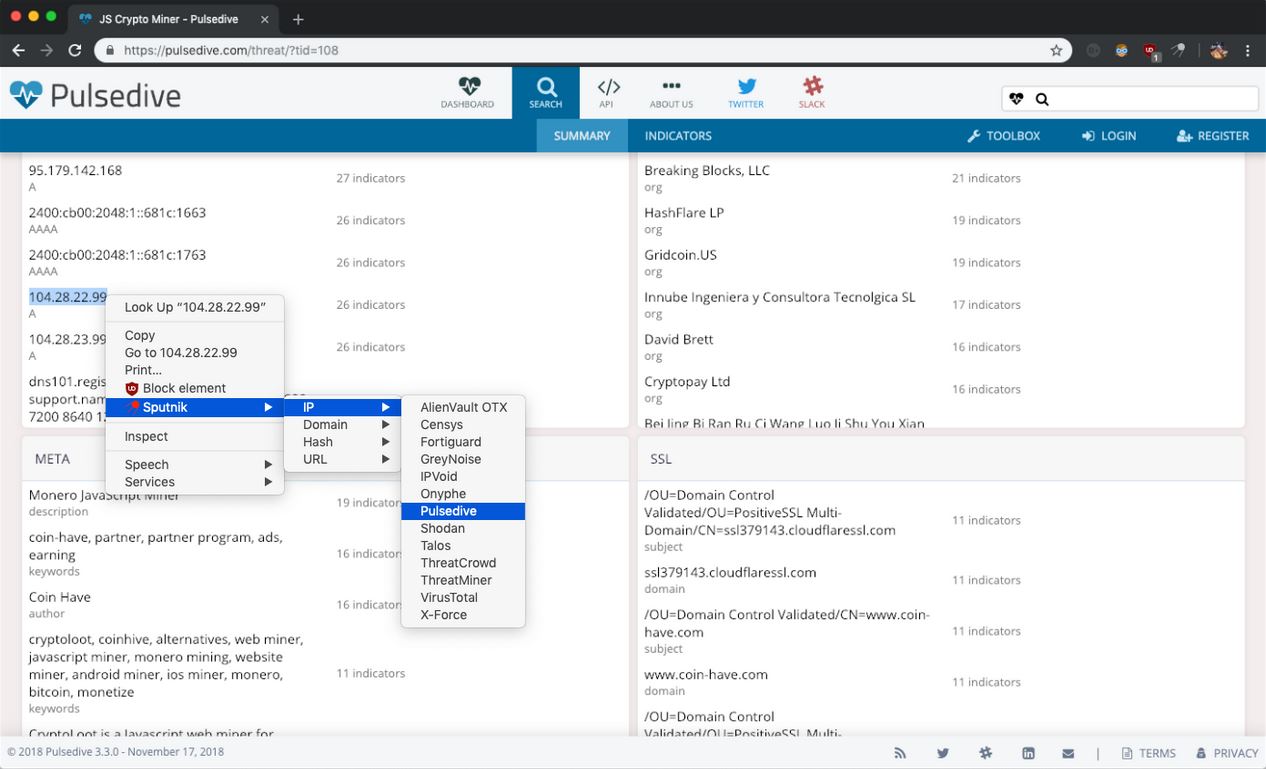
303Sputnik – Open Source Intelligence Browser Extension
Sputnik is an extension to quickly and easily search IPs, Domains, File Hashes, and URLs using free Open Source Intelligence (OSINT) resources....
-
 224
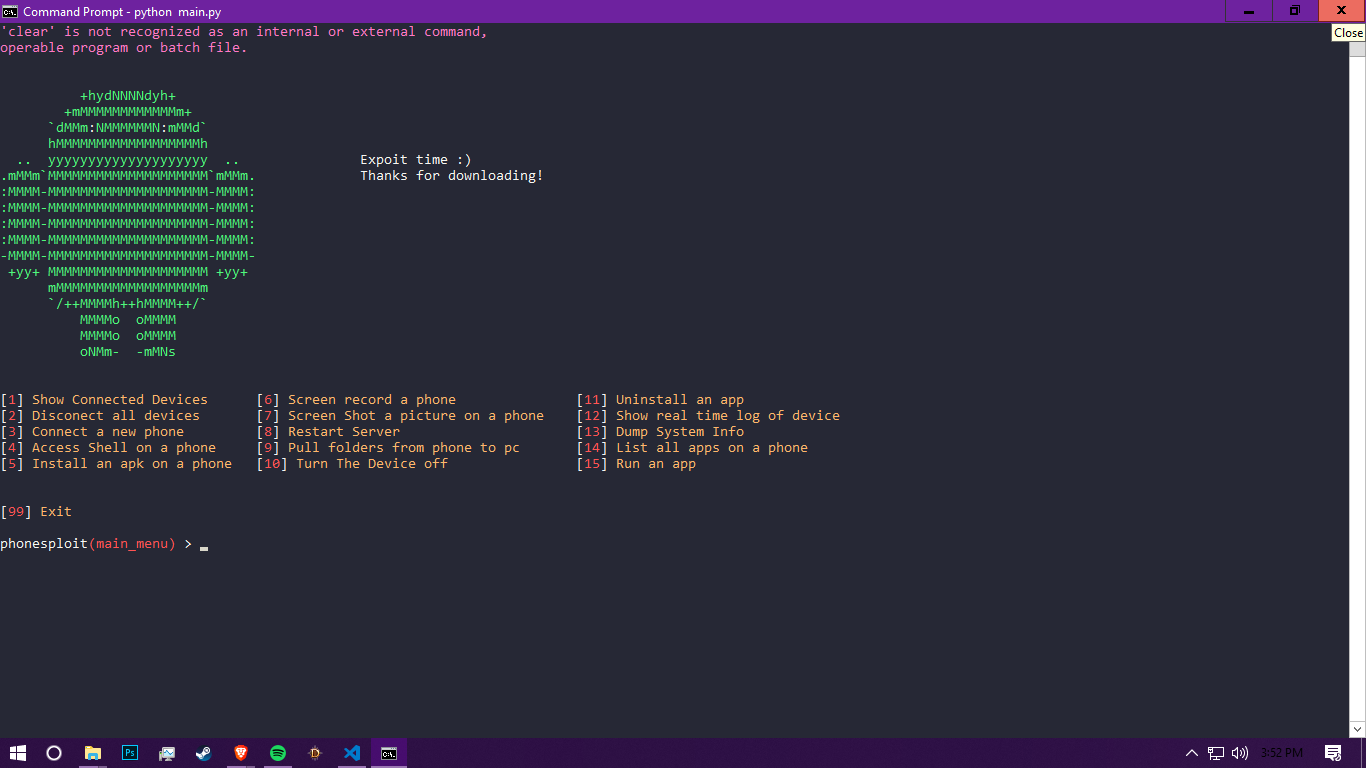
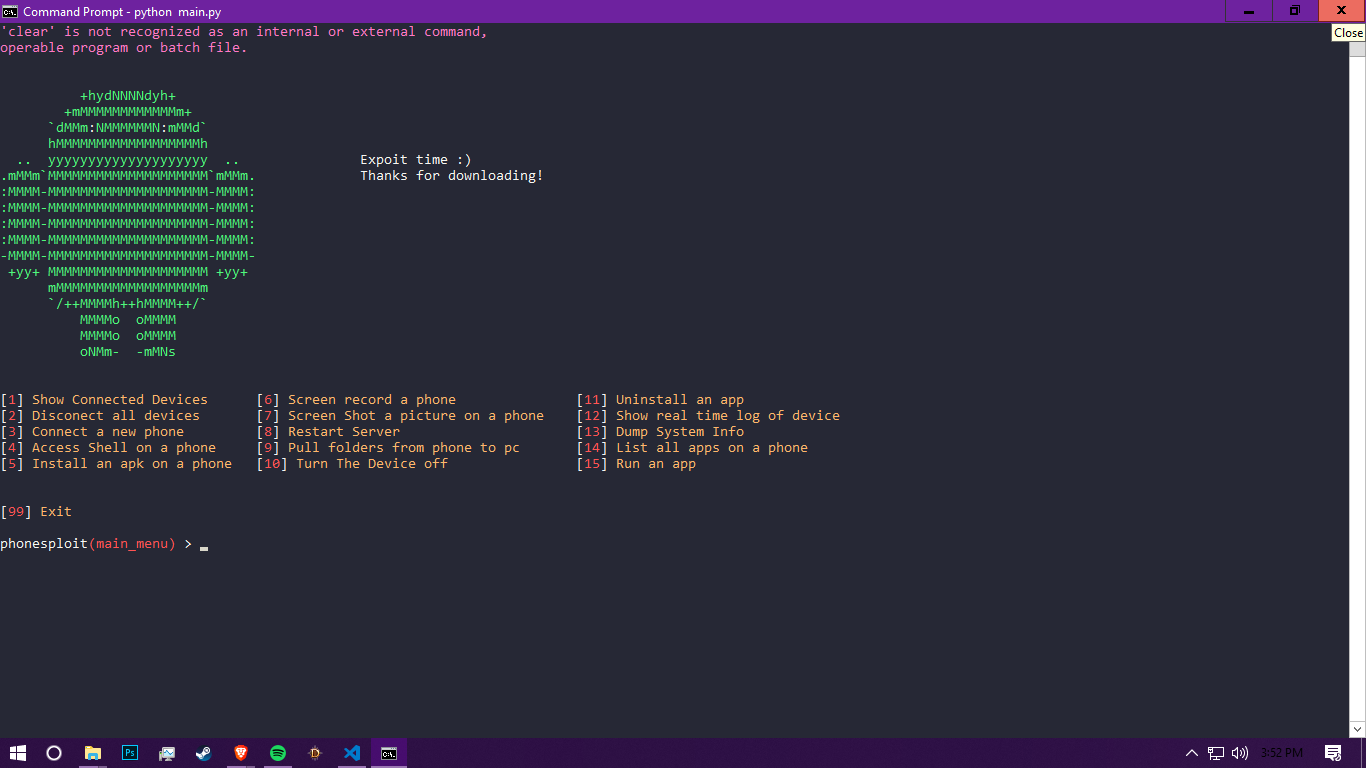
224PhoneSploit – Using Open Adb Ports We Can Exploit A Devive
Using open Adb ports we can exploit a device you can find open ports here https://www.shodan.io/search?query=android+debug+bridge+product%3A”Android+Debug+Bridge” To find out how to access...
-
 331
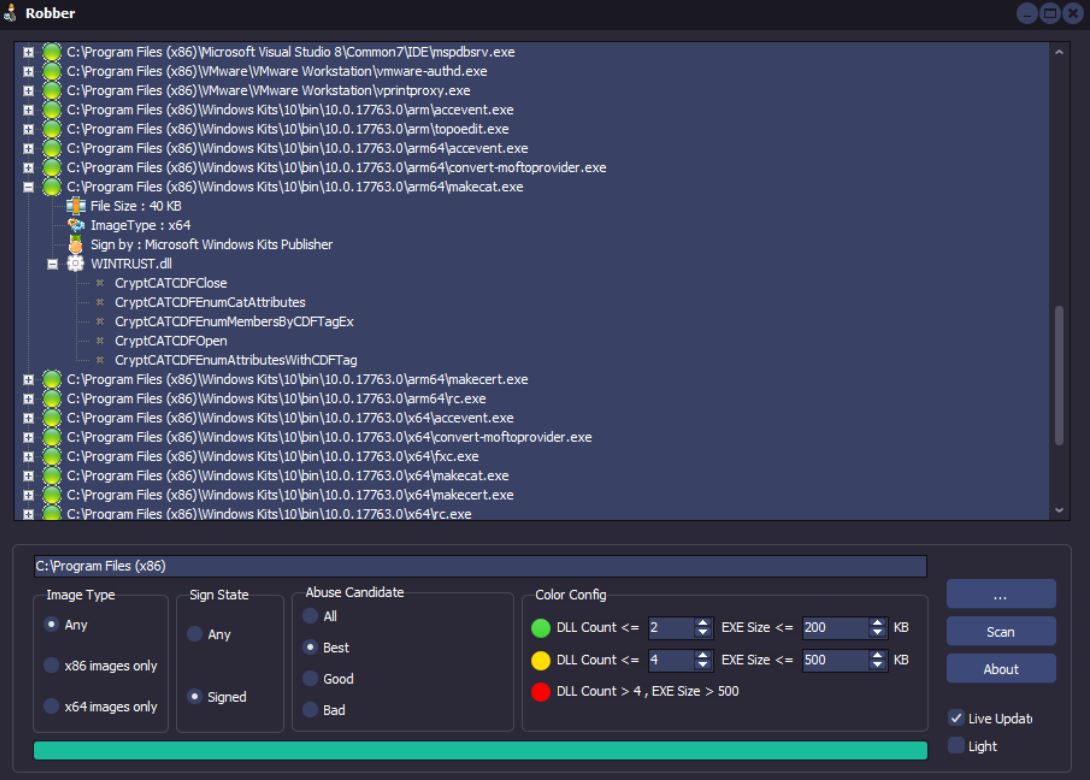
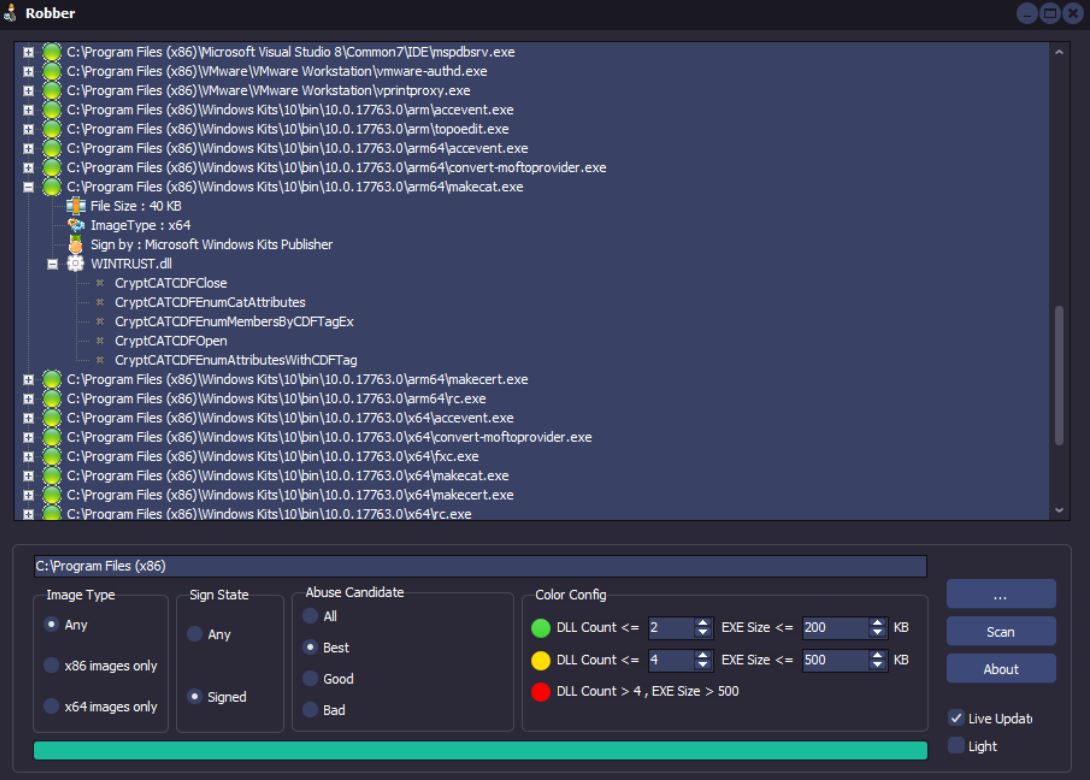
331Robber – Open Source Tool for Finding Executables Prone to DLL Hijacking
Robber is a free open source tool developed using Delphi XE2 without any 3rd party dependencies. What is DLL hijacking ? Windows...
-

 283
283Evil Limiter – Limits Bandwidth of Devices on the same Network Without Access.
A tool to limit the bandwidth (upload/download) of devices connected to your network without physical or administrative access. Evil limiter employs ARP...
-

 186
186Graffiti – A Tool To Generate Obfuscated One Liners To Aid In Penetration Testing
Graffiti is a tool to generate obfuscated oneliners to aid in penetration testing situations. Graffiti accepts the following languages for encoding: Python...
-
 214
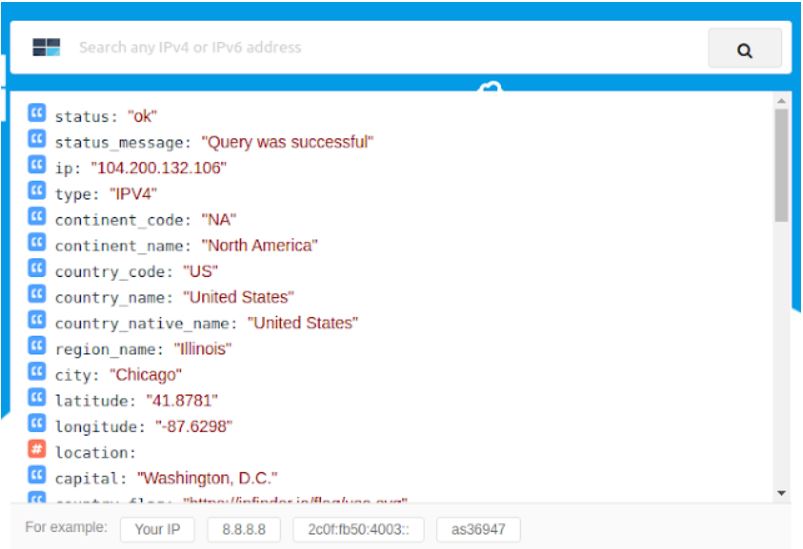
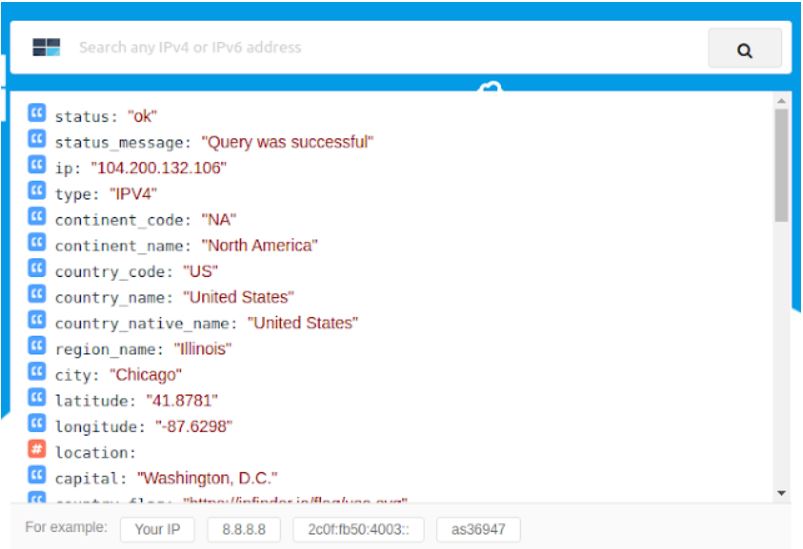
214IPFinder CLI – The Official Command Line Client For IPFinder
Locate and identify website visitors by IP address. IPfinder offers one of the leading IP to geolocation APIs and global IP database...
-

 245
245TeleShadow3 – Telegram Desktop Session Stealer
Stealing desktop telegrams has never been so easy. Advanced Telegram Desktop Session Hijacker. Set the email and sender details of the sender...
-

 344
344Trigmap – Wrapper for Nmap to Automate the Pentest
Trigmap is a wrapper for Nmap. You can use it to easily start Nmap scan and especially to collect informations into a...
-
 3.6K
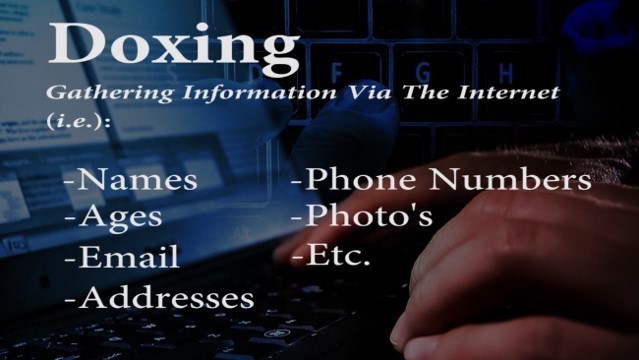
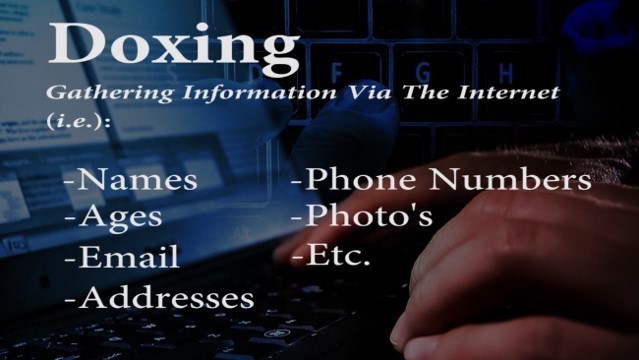
3.6KDoxing Tools
Doxing (also “doxxing”, or “d0xing”, a word derived from “documents”, or “docs”) consists in tracing and gathering information about someone using sources...
-
 182
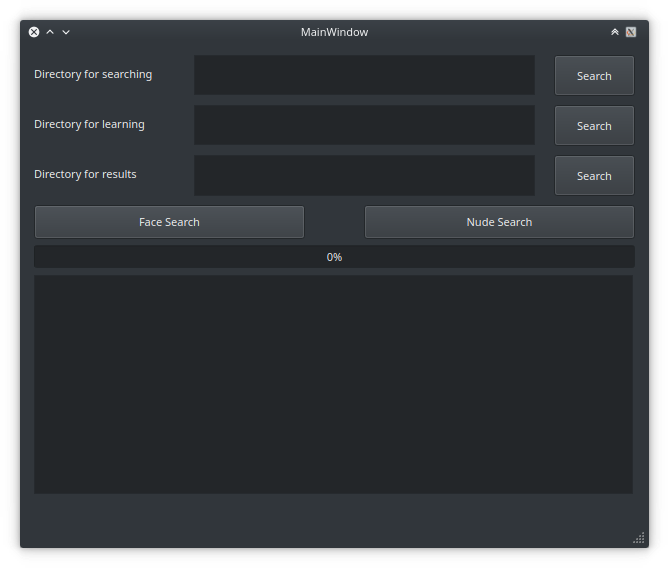
182PAnalizer – Pornography Analizer And Face Searching
PAnalizer is a forensic tool, you can search pornographic images in a specific directory, this is util in Pedestrian Detection. Also you...
-
 321
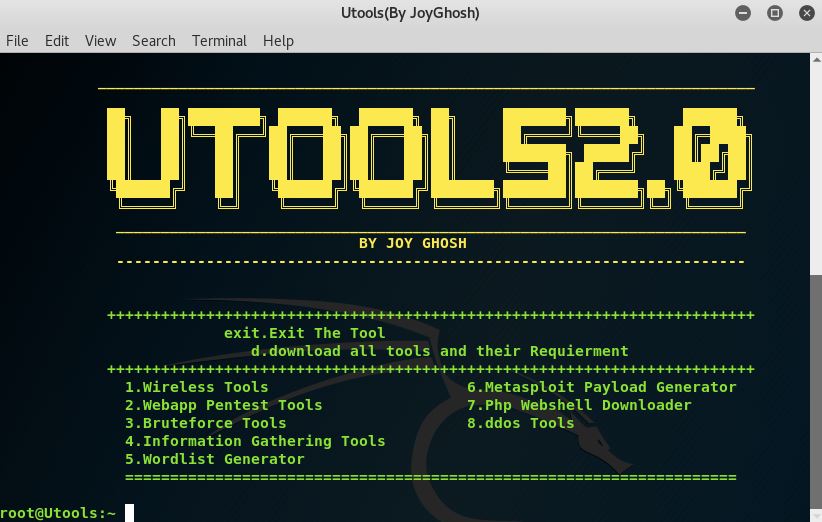
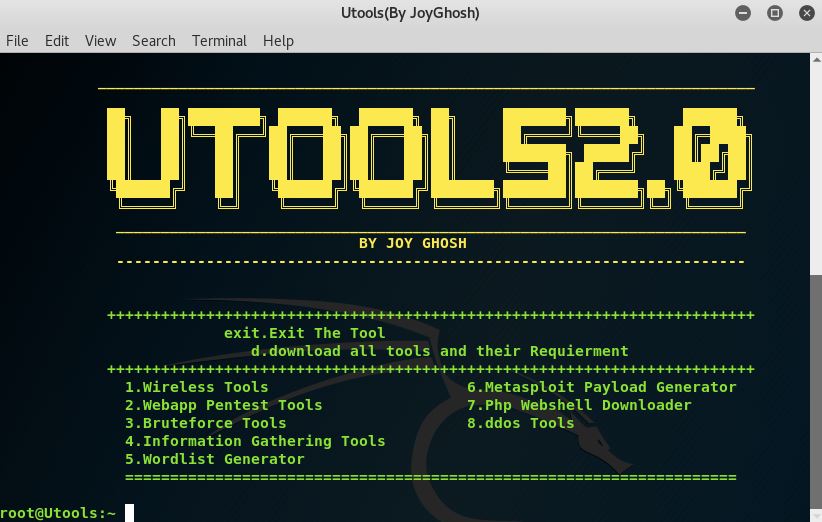
321Utools2 – Hacking Toolkit
A simple one click to install and download, Utools2 toolkit contains some of the best hacking tools used and compiled into one...
-

 326
326Red Team Powershell Scripts
Various PowerShell scripts that may be useful during a red team exercise. The repo includes the following scripts: Red Team Powershell Scripts...






