Hack Tools
-
 204
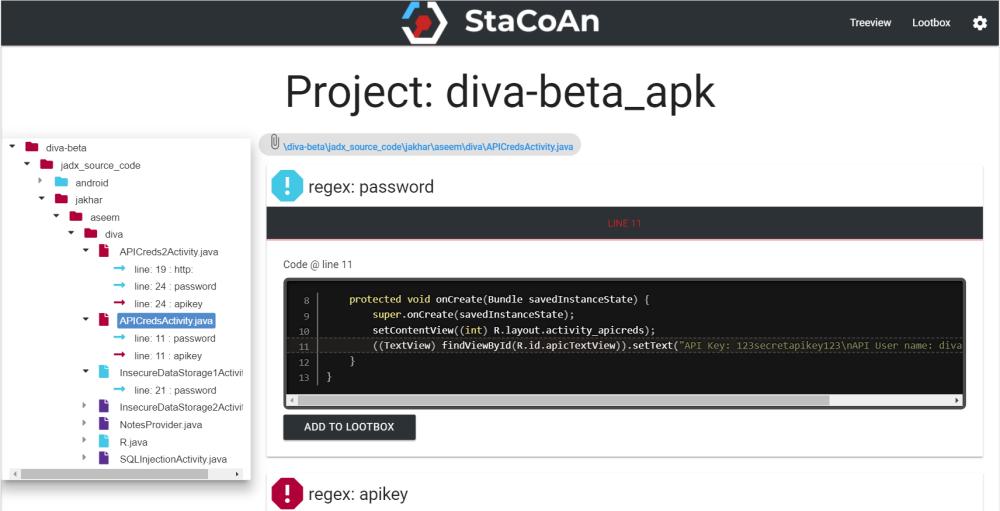
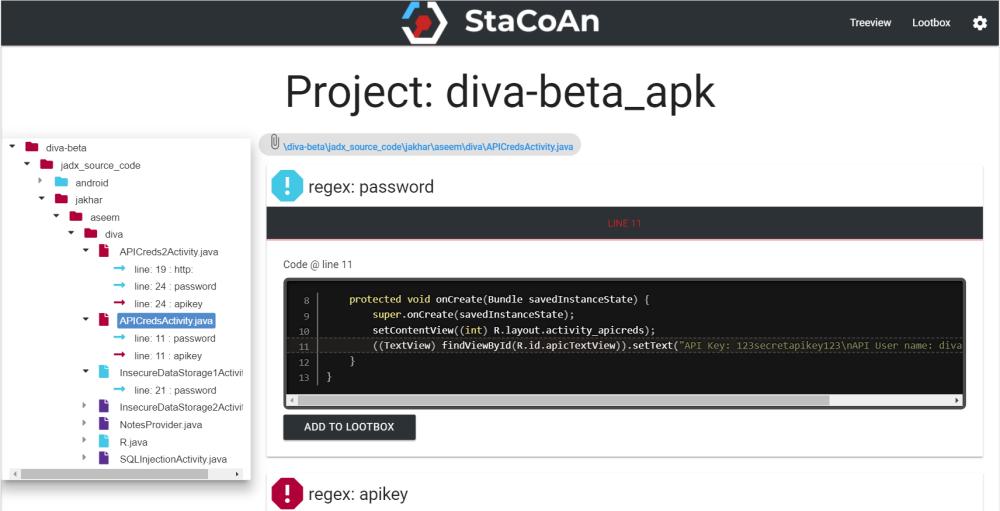
204StaCoAn – Open Source Static Code Analyser
StaCoAn is a crossplatform tool which aids developers, bugbounty hunters and ethical hackers performing static code analysis on mobile applications. This tool will look for interesting...
-

 219
219LanGhost – A LAN dropbox chatbot controllable via Telegram
Telegram Chatbot to control Lan network. Installation: You will need a Raspberry Pi with fresh Raspbian/Kali on the SD card, because you...
-
Bloodhound – Six Degrees of Domain Admin
BloodHound uses graph theory to reveal the hidden and often unintended relationships within an Active Directory environment. Attackers can use BloodHound to...
-

 193
193Bettercap – Extensible MITM Framework
Bettercap is a complete, modular, portable and easily extensible MITM tool and framework with every kind of diagnostic and offensive feature you...
-

 229
229Trojanizer – Trojanize your Payloads
The Trojanizer tool uses WinRAR (SFX) to compress the two files input by user, and transforms it into an SFX executable(.exe) archive....
-

 161
161Proxenet – Hacker Friendly Proxy for Web Application Pentests
Proxenet is a hacker-friendly DIY web proxy for pentesters. It is a C-based proxy that allows you to interact with higher level...
-
 196
196SQLiPy – A SQLMap Plugin for Burp Suite
SQLiPy is a Python plugin for Burp Suite that integrates SQLMap using the SQLMap API. SQLMap comes with a RESTful based server...
-
 179
179Yasuo – Tool For Detecting Vulnerable & Exploitable 3rd-party Web Applications
Yasuo is a ruby script that scans for vulnerable 3rd-party web applications. There are over 10,000 remotely exploitable vulnerabilities that exist in...
-

 302
302In-Spectre-Meltdown – Tool to Check Speculative Execution Side-Channel Attacks
This tool allows to check speculative execution side-channel attacks that affect many modern processors and operating systems designs. CVE-2017-5754 (Meltdown) and CVE-2017-5715...
-
 191
191ShellCheck – Static Analysis Tool for Shell Scripts
ShellCheck is a static analysis tool that gives warnings and suggestions for bash/sh shell scripts. How To Use ShellCheck There are a number...
-

 280
280Commix – Automated Command Injection and Exploitation Tool
Commix (short for [comm]and [i]njection e[x]ploiter) is an automated tool that you can use to test web-based applications with the view to...
-

 177
177Fsociety Hacking Tools Pack
Fsociety Contains All Tools Used In Mr Robot Series compiled into an easy to use Pentesting framework. Fsociety Menu Information Gathering Password...
-

 159
159Autorize – A Burp Suite Extension For Detecting Authorization Vulnerabilities
Autorize is an automatic authorization enforcement detection extension for Burp Suite. It helps you detect authorization vulnerabilities. It is sufficient to give to...
-

 119
119D-Link Password Decryptor – Tool for Recovering Passwords from D-Link Modems/Routers
D-Link Password Decryptor is a free program that allows you to instantly recover the Login Password of D-Link modem/router. It supports dual mode...
-

 169
169Kadimus – LFI Scan & Exploit Tool
Kadimus is a tool that allows you to detect and exploit the Local File Inclusion (LFI) vulnerability in sites. Features: Check all...
-
 271
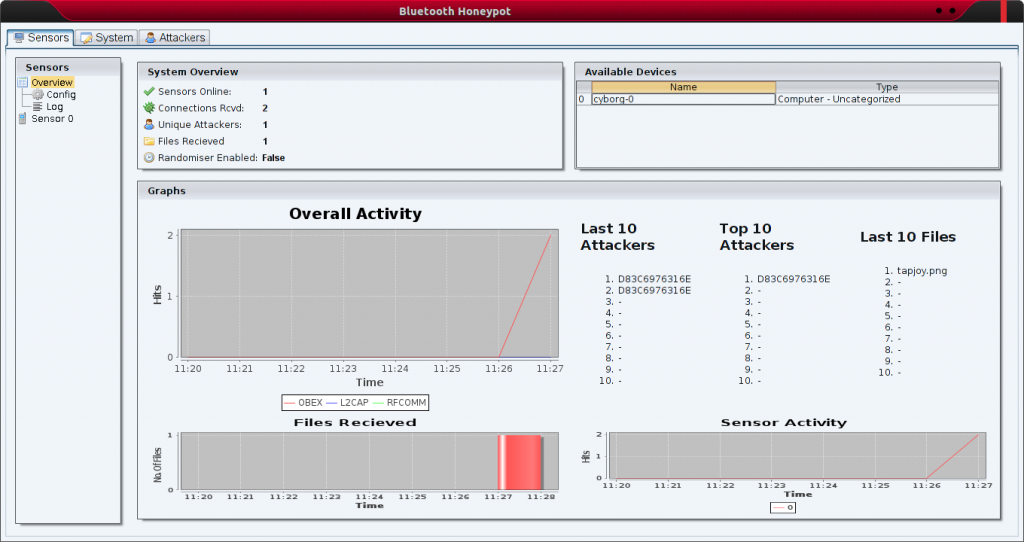
271Bluepot – Bluetooth Honeypot
Bluepot was a third year university project attempting to implement a fully functional Bluetooth Honeypot. A piece of software designed to accept...
-
 247
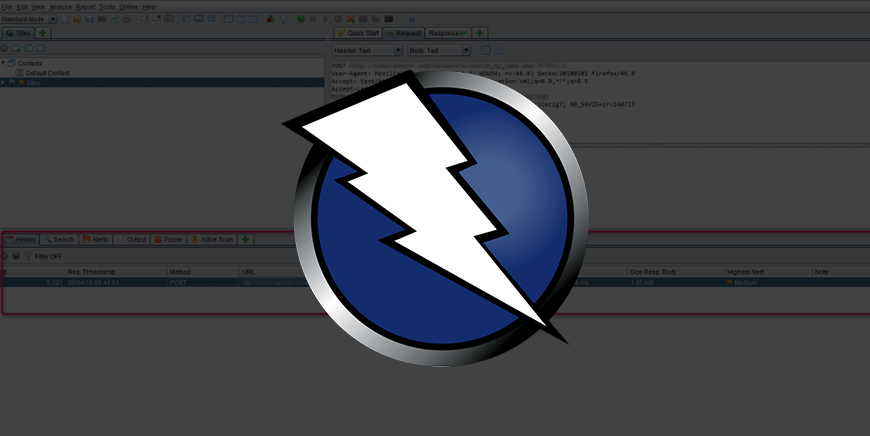
247OWASP ZAP 2.7.0 – Penetration Testing Tool for Testing Web Applications
The OWASP Zed Attack Proxy (ZAP) is one of the world’s most popular free security tools and is actively maintained by hundreds...
-
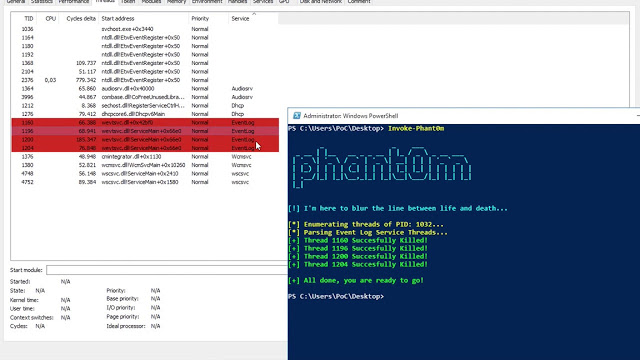
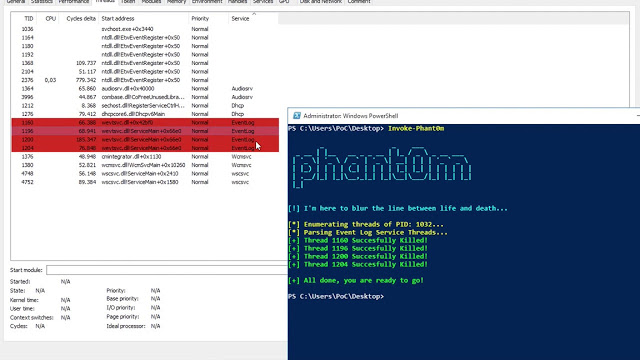 207
207Invoke-Phant0m – Windows Event Log Killer
Phant0m is a PowerShell script and targets the Windows Event Log Service in Windows operating system. Because the most traces of a...
-

 583
583Hacker’s Favorite Tool: Mimikatz 2.1.1 Released
Mimikatz is a post-exploitation tool written by Benjamin Delpy (gentilkiwi). It’s now well known for extracting plaintexts passwords, hash, PIN code and...
-

 222
222Invoke-PSImage – Tool to Embed Powershell Scripts in PNG Image Pixels
Invoke-PSImage takes a PowerShell script and embeds the bytes of the script into the pixels of a PNG image. It generates a...
-
 195
195PhEmail – Open Source E-mail Phishing Tool
PhEmail is a python based email phishing tool that automates the process of sending phishing emails as part of a social engineering...






