How To
-

 225
225How to Install Cinnamon on Ubuntu 14.04?
Cinnamon is a popular Linux desktop based on GTK+ that got its start as a fork of GNOME Shell . It is...
-
 220
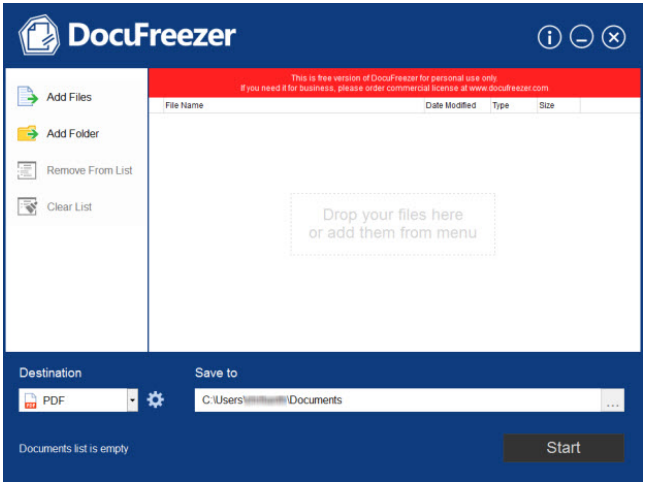
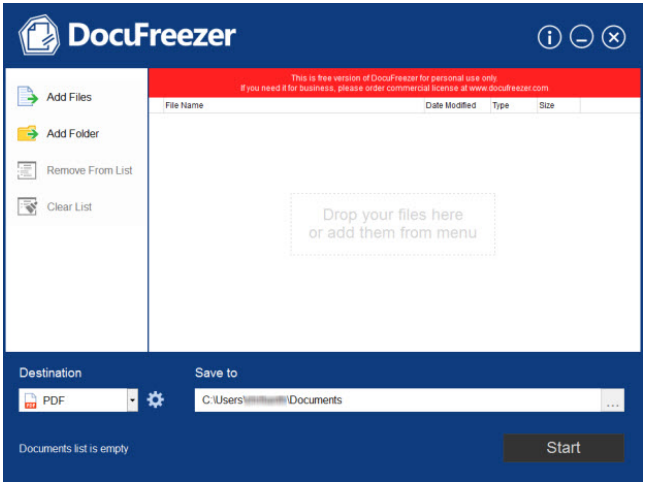
220DocuFreezer: Offline conversion of documents to PDF and JPEG’s demystified [Review]
People handling hundreds of documents weekly as part of their personal or professional work know how it feels when their internet connection...
-
 159
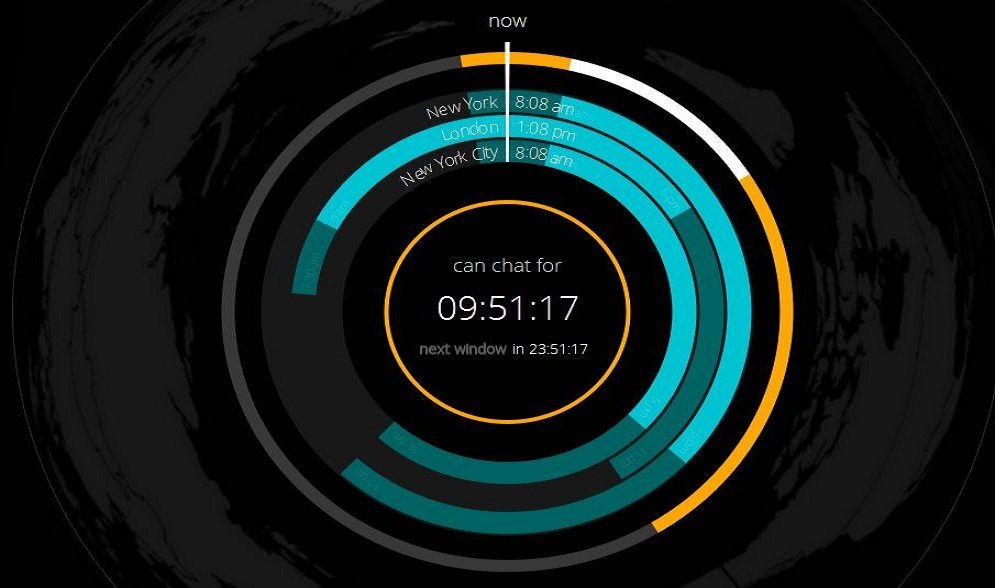
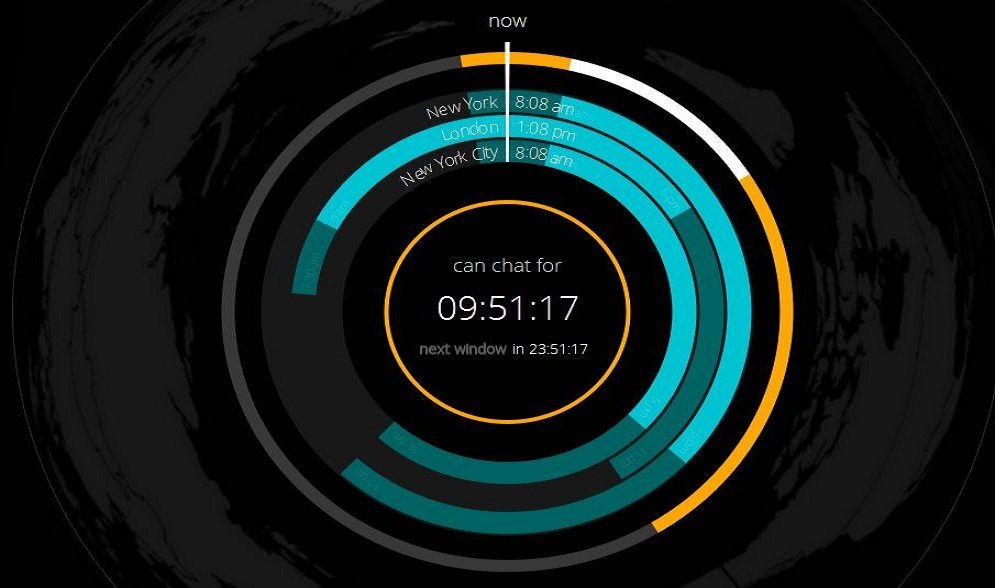
159How to Find Suitable Time to Chat/Talk Between Different Time Zones?
So you have contacts all around the world, or you are in a job that needs you to talk to people in...
-

 394
394How to Download Only Audio from a Youtube Video?
There would have been many times when you wanted to download just the audio of a YouTube video, but not finding any...
-

 91
91How to protect your identity at school
Young people are targeted for data theft at 35 times the rate of adults – they are considered an easy target for...
-
 173
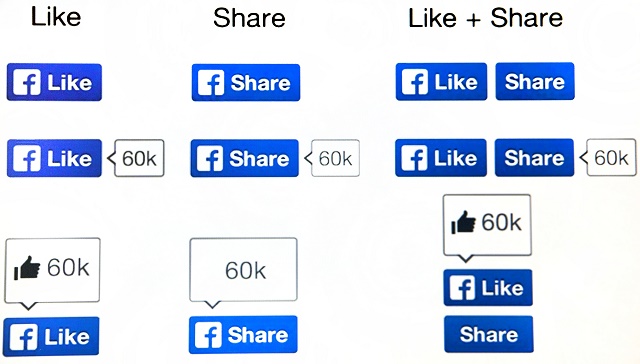
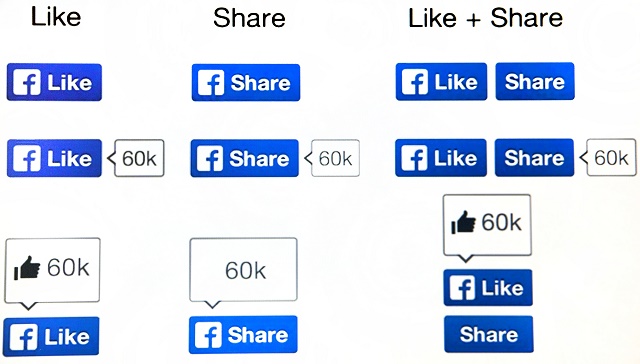
173Facebook scams – the ‘classics’ and how to avoid them
But some things on Facebook haven’t changed - namely, the scams. It’s not that cybercriminals are unoriginal - it’s just that there...
-
 192
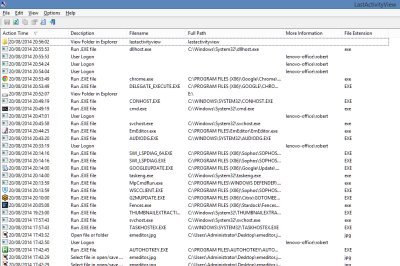
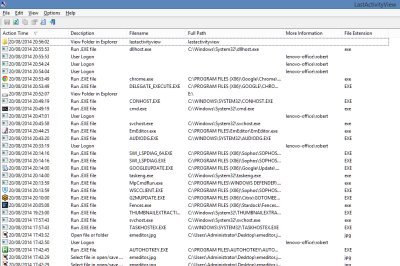
192Free Software to Monitor Your PC’s Activity
If you ever get asked to fix the PC of a friend or colleague which has been having problems, the first thing...
-
 200
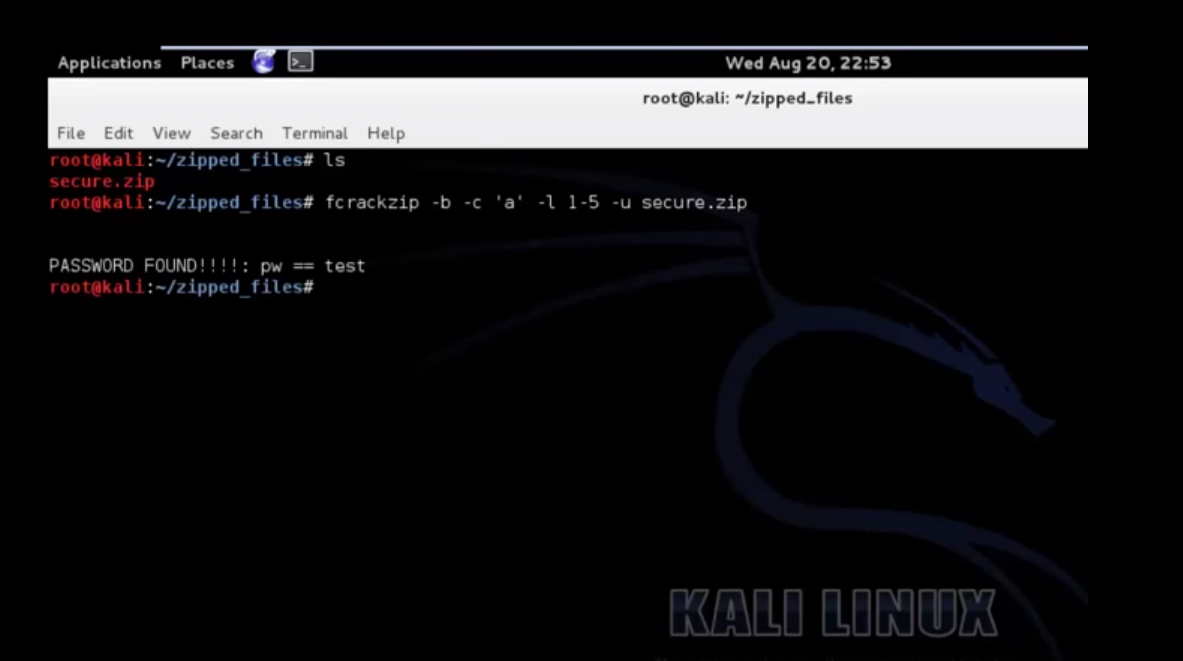
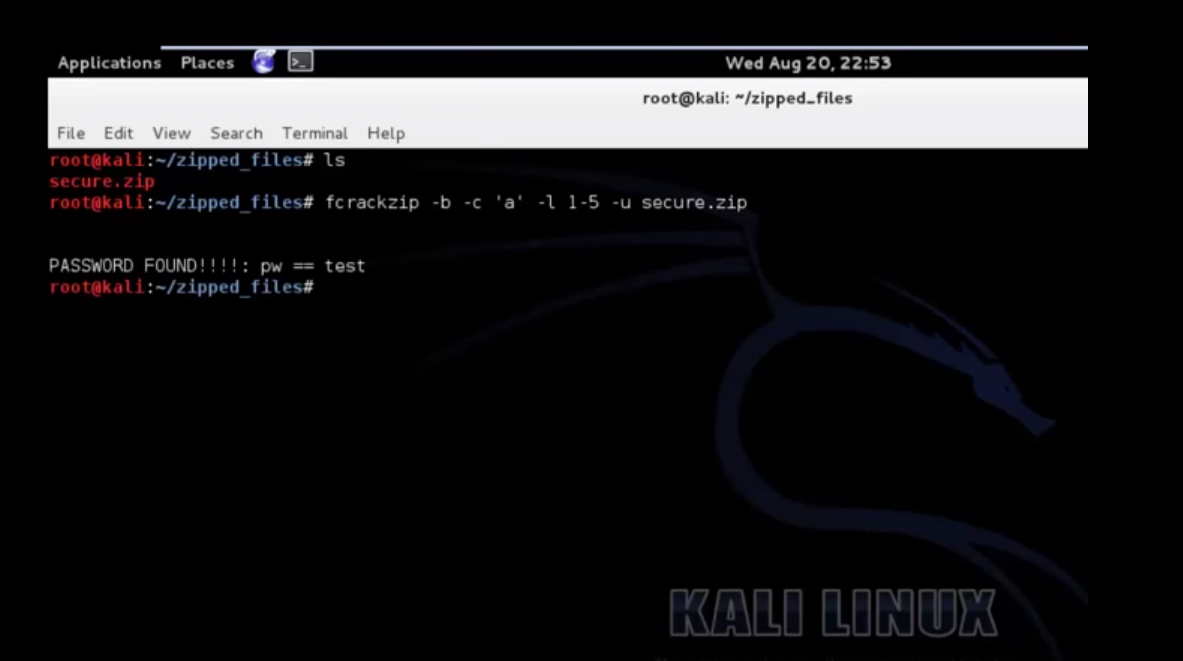
200Crack A Password Protected Zip File Using Kali
Also Read: Download Kali 2.0 Now
-

 240
240Is your Point of Sale machine protected against attacks?
Criminals are very interested in retailers’ Point of Sale (PoS) machines. Recently, a new type of malware has been found that specifically...
-

 417
417Comic‑Con 2014: Eight super‑powered digital safety tips
Over the past few years, Comic-Con has had over 130,000 attendees, and those attendees tend to be very digitally literate - so...
-
 221
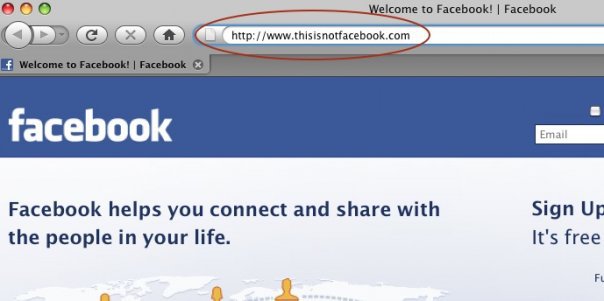
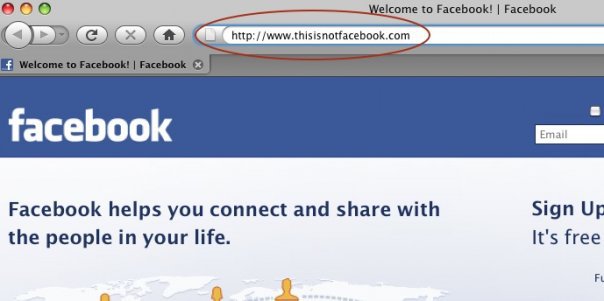
221How do Facebook accounts get hacked [Protect Yourself Against It]
Facebook phishing. Phishing is a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as...
-

 178
178Facebook settings – five steps for better privacy and security
Facebook has faced repeated controversy over privacy, with features such as Graph Search revealing information which users might have forgotten they ever...
-
 125
125Linux Kernel Local Privilege Escalation PoC
/** * CVE-2014-4014 Linux Kernel Local Privilege Escalation PoC * * Vitaly Nikolenko * http://hashcrack.org * * Usage: ./poc [file_path] * *...
-

 100
100Android malware: how to keep your device safe from filecoders (and everything else)
When ESET researchers analyzed the first Android ransomware controlled via Tor, it showed how quickly Android malware is evolving to match its...
-

 163
163Router attacks: Five simple tips to lock criminals out
Cybercriminals always look for the weakest link when planning their attacks – and failings in home routers can allow another "way in"....
-

 200
200How to retrieve your BitLocker Recovery key ?
if you are not using MBAM and don’t have access to your Active Directory and want to recover your BitLocker key for...
-

 101
101Xbox Kinect Hack Allows For Virtual Reality
It’s one thing to bring your mind into virtual reality. Get some snazzy VR goggles in front of your eyes, bump the...
-

 210
210Hack Androids lock screen with an Arduino
You can also find the code for this project below: /* Brute forcing Android 4 Digit PIN's To run the whole range...
-

 112
112Don’t forget flash: memory cards can be a data loss and infection vector
A reminder that malicious code can be spread via flash memory cards like SD cards, just as easily as it can spread...
-

 200
200Business continuity management: key to securing your digital future
Business continuity management is the key to securing your company's digital future despite disruptive incidents, from power outages and IT errors to...
-

 224
224How to run Kali on your Android device
This tutorial mainly created for Linux fans. Follow the given steps below to install Kali Linux on your Android phone. Step 1:...






