How To
-
 123
123Taxing Times: Dealing with tax identity fraud in America
Filing your taxes on April 15? What if someone has already filed “your” income tax return? Sadly, this can happen, and it...
-

 223
223How to Record Skype Video and Audio calls for Windows and Mac
Pamela [Win] It is free to download and allows you to record calls you make using Skype. It works on Windows devices...
-
 195
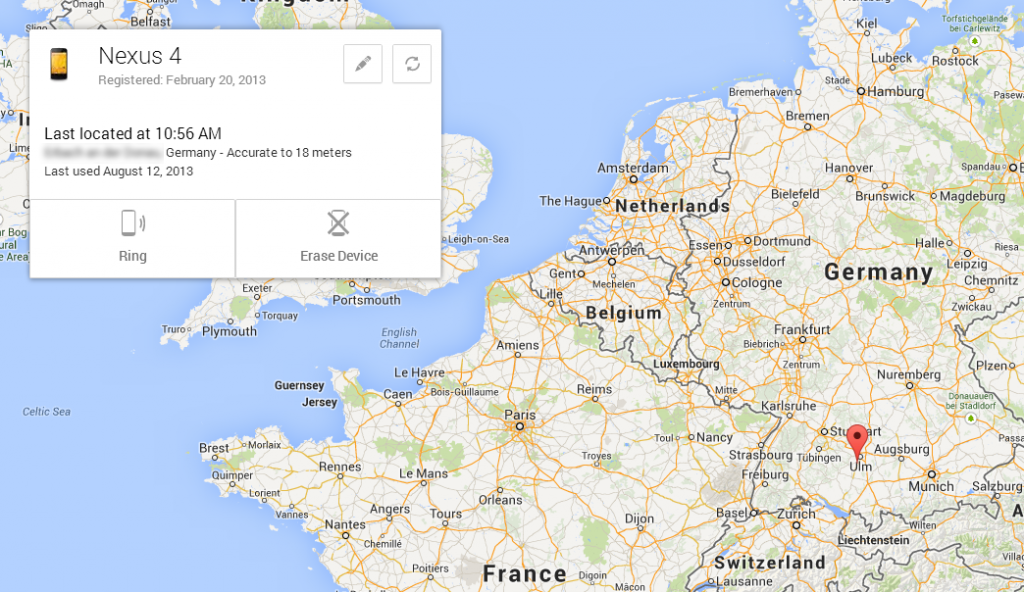
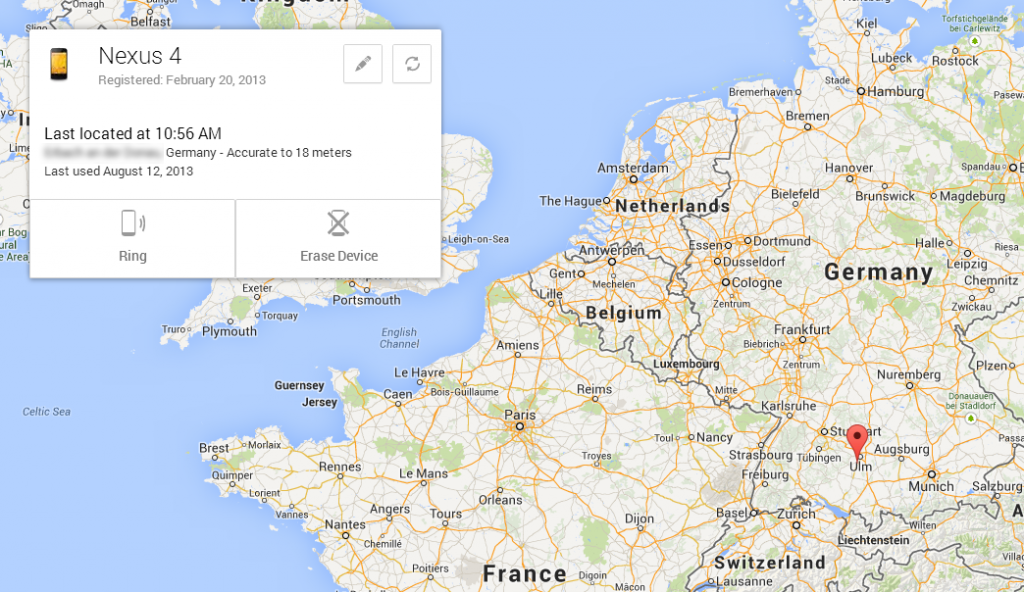
195How to Locate Your Lost Android Device Easily
Lost you android phone ..? Feeling to sad .. ? Dont worry Now we came with another Application which sorts out...
-

 136
136Ports That Are Commonly Targeted By Hackers
Common ports, such as TCP port 80 (HTTP), may be locked down — but other ports may get overlooked and be vulnerable...
-

 192
192Make Your Computer Work Faster In 10 Easy Steps
We all know that sinking feeling when your computer decides to slow down and barely function for no real reason. Why is...
-

 313
3135 Tips for protecting Windows XP machines after April 8, 2014
Microsoft will cease providing security updates for the Windows XP operating system on April 8, 2014. If you cannot get away from...
-

 94
94Master of Mavericks: How to secure your Mac using Apple’s latest update
Apple’s Mavericks update was the first free update to Mac OS X – itself a big step forward for security, as all...
-

 182
182Five tips to help control your privacy on Mac OS X
Apple’s Mac OS X Mavericks has some very neat privacy features built in - from a “Guest User” account which restricts people...
-

 215
215Tips for protecting against sextortion
It seems like every few days there is a new story involving teenaged girls being tricked or blackmailed into sending compromising pictures...
-

 98
98How can we as patients secure our medical data?
When someone says “data privacy” most people think about the information that is available on sites like Google and Facebook, or stored...
-
 123
123Smells phishy? New email scams – and why smartphone users need to stay alert
Phishing is unique among cyber attacks - it doesn’t rely on weaknesses in computer software, or new vulnerabilities - it relies, initially...
-

 560
560Two‑factor authentication: What is it – and why do I need it?
Over the past two years, many online services have started to offer ‘two-factor authentication’ - an extra security measure which often requires...
-

 95
95Make it stop! How to cleanse your PC of unwanted adware (and ‘badware’)
‘Adware’, software which delivers unwanted adverts, isn't as scary as some malware, but ESET's analysis of Win32/Boaxxe shows that 'malicious' adware is...
-

 89
89Attention Shoppers! Top tips for defending your accounts against card fraud
Read how to protect yourself if you've been shopping with credit or debit cards (and who hasn't?). As the scope of the...
-

 113
113Target breach expands: what does this mean?
Target's 2013 data breach is expanding in scope and scale, requiring additional vigilance on the part of shoppers to protect their accounts...
-
 107
107Greetings, Android! 12 tips to toughen up your new device for the real world
ESET’s Threat Trends Predictions report for 2014 found new Android malware increased 63% from 2012 to 2013 - so If you’re a...
-

 94
94Target breached: 5 defensive steps shoppers should take now
Tips for shoppers worried that their credit or debit cards may have been compromised by the massive security breach at Target stores.
-

 96
96Exploit Protection for Microsoft Windows
we provide more detail on the most exploited applications and advise a few steps users can (and should) take to further strengthen...
-

 111
111Can you hear us now? ESET researchers podcast every week
Have you checked out the weekly podcast by ESET security researchers? It's called the ESET Malware Report and it covers many security...
-

 187
187Why “crypto” isn’t just for spies: A beginner’s guide to keeping secrets
For years, "encryption" has sounded like James Bond technology to many PC users - but new systems have made "crypto" technology easier...
-

 263
263Why your small business needs an information security policy and a WISP
Information security policy can make a big difference for small business. Here we offer advice, resources, and a free recorded webinar on...






