Malware
-
 336
336New ViceLeaker Malware Attack on Android Devices With Backdoor Capabilities to Hijack Camera, Record Audio
Researchers discovered a new malware campaign called ViceLeaker that specifically targeting the Android users with sophisticated backdoor capabilities to Hijack camera, delete...
-

 5.0K
5.0KOSX/Linker Malware, A Weaponized Unpatched Security Bug
We rarely feature a story about MacOS security here in Hackercombat.com, as the platform is not really attractive for hackers to target....
-
 263
263New vulnerability on Mac is exploited with malware
IT security audit specialists from the cybersecurity firm Intego have reported supposed in the wild exploitation of an uncorrected vulnerability in some...
-
 394
394Chinese APT 10 Group Hacked Nearly 10 Telecom Networks and Stealing Users Call Records, PII, Credentials, Email Data and more
Infamous Chinese APT 10 hackers compromised over 10 Telecom networks around the world under the campaign called Operation Soft Cell and stealing various...
-
 299
299New Mac Malware Exploits GateKeeper Bypass Bug that Apple Left Unpatched
Cybersecurity researchers from Intego are warning about possible active exploitation of an unpatched security vulnerability in Apple’s macOS Gatekeeper security feature details...
-
 255
255Microsoft Warns about the new Campaign that Delivers FlawedAmmyy RAT via Weaponized MS Excel Documents
Microsoft uncovered a new campaign with a sophisticated infection chain delivering notorious FlawedAmmyy RAT as a final payload. The attack starts with...
-

 739
7394 Most Memorable Botnet In History
What is Botnets? Botnets are artificial networks created by malware, which can be controlled by the virus author remotely. Here in Hackercombat.com,...
-

 540
540Hackers Take Complete Control of Your Android Device by Launching MobOk Malware via Fake Photo Editing Apps in Google Play
Researchers discovered a fake photo editing apps which are used by cybercriminals to launch MobOk Malware that takes complete control of the...
-
 322
322This Cryptomining Malware Launches Linux VMs On Windows and macOS
Cybersecurity researchers from at least two firms today unveiled details of a new strain of malware that targets Windows and macOS systems...
-

 257
257Firefox 67.0.4 Released — Mozilla Patches Second 0-Day Flaw This Week
Okay, folks, it’s time to update your Firefox web browser once again—yes, for the second time this week. After patching a critical...
-

 287
287Waterbug APT Hackers Hijacked Another APT Group Infrastructure to Attack Governments and International Organizations
Waterbug APT Hackers used hijacked infrastructure to attack governments and international organizations through various campaigns using new and publically available malware. The...
-
 431
431LoudMiner: Cross‑platform mining in cracked VST software
The story of a Linux miner bundled with pirated copies of VST (Virtual Studio Technology) software for Windows and macOS
-

 314
314Plurox, the all-in-one malware infecting computers around the world
A few months ago, specialists in digital forensics analysis of security firm Kaspersky analyzed Plurox, a backdoor detected in some attacks that...
-
 248
248Plurox Modular Malware Spreads Over Local Network and Provide Access to Attackers for Installing Additional Malware
A new malware dubbed Plurox spread itself over the local network using EternalBlue exploit and let attackers gain access to the network...
-

 355
355New tool to remove GandCrab ransomware encryption
A group of web application security testing experts has released a new version of the tool to remove the encryption imposed by...
-
 294
294GandCrab Ransomware Decryption Tool [All Versions] — Recover Files for Free
Cybersecurity researchers have released an updated version of GandCrab ransomware decryption tool that could allow millions of affected users to unlock their...
-
 521
521Malicious Apps from Google PlayStore Bypassing SMS-Based Two-Factor Authentication and Steal OTPs in SMS
Researchers discovered new malicious Android apps from Google Play Store bypassing SMS-based two-factor authentication (2FA) mechanisms and steal the OTP without SMS’s...
-

 4.5K
4.5KWhat is Malware?
Any person who has ever used a computer has probably heard the term “malware.” It is everywhere, and the general consensus is...
-

 294
294Your IoT devices, such as cameras, washing machines, NAS storage will be affected by this new malware
A couple of years ago the Mirai botnet put thousands of system administrators in trouble before being dismantled; however, website security audit...
-

 254
254Malware sidesteps Google permissions policy with new 2FA bypass technique
ESET analysis uncovers a novel technique bypassing SMS-based two-factor authentication while circumventing Google’s recent SMS permissions restrictions
-
 326
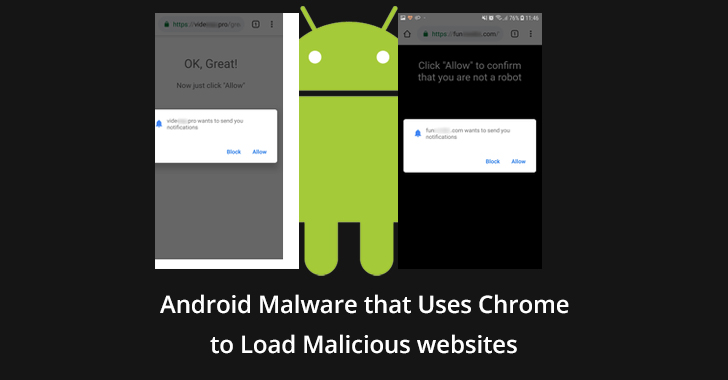
326New Android Malware that Uses Chrome to Load Malicious websites through Notifications
New malware spotted on Google play that directs users to malicious websites and subscribes users to advertising notifications. The malware is distributed...






