Malware
-

 2.8K
2.8KIs This The Start Of Open Source Malware for Linux?
Linux is considered a more secure and privacy-focused operating system than Windows, not only because of a low market share (only 2%...
-
 282
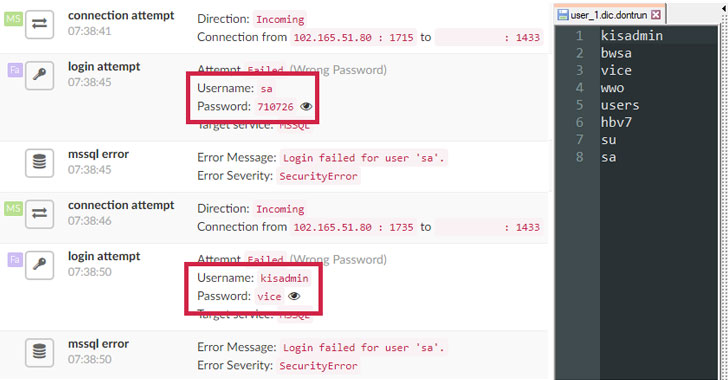
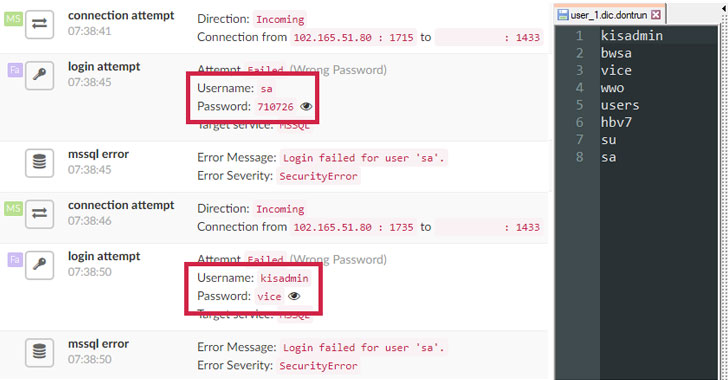
282Chinese Hackers Infect Over 50,000 Windows MS-SQL and PHPMyAdmin Servers Worldwide with 20 Different Payloads
A new China-based campaign dubbed Nansh0u targets Windows MS-SQL and PHPMyAdmin servers worldwide. The attack campaign primarily targets servers belonging to the...
-
 223
223Hackers Infect 50,000 MS-SQL and PHPMyAdmin Servers with Rootkit Malware
Cyber Security researchers at Guardicore Labs today published a detailed report on a widespread cryptojacking campaign attacking Windows MS-SQL and PHPMyAdmin servers...
-
 253
253A dive into Turla PowerShell usage
ESET researchers analyze new TTPs attributed to the Turla group that leverage PowerShell to run malware in-memory only
-
 358
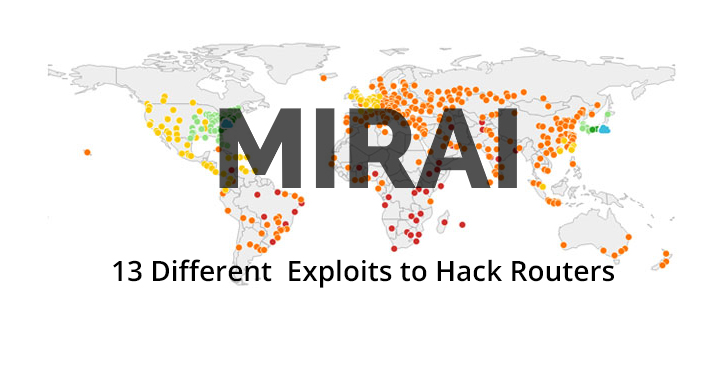
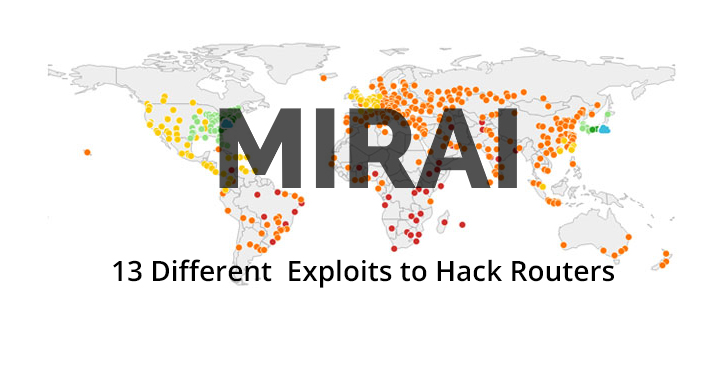
358New Variant of Mirai Malware Using 13 Different Exploits to Hack Routers Including D-Link, Linksys, GPON, Netgear, Huawei
Researchers discovered a new wave of Mirai Variant that used 13 different exploits to attack various router models and other network devices....
-
 420
420World’s Most Dangerous Laptop With 6 Popular Malware Sold at $1.3 million
The Laptop loaded with six most dangerous pieces of malware was sold at an auction. The malware present in the Laptop is...
-
 240
240Chinese APT 10 Hackers Attack Government and Private Organizations Through Previously Unknown Malware
Researchers discovered a new malware attacker against the government and private organizations from Chinese cyber espionage group APT10 using previously unknown malware with...
-

 286
286Hackers using HawkEye Keylogging Malware to Attack Enterprise Networks to Steal Application Data
Hackers behind the new HawkEye malware campaign targets business users to infect them with advanced keylogging malware that could download additional malware...
-
 356
356Hackers infect MySQL servers with GandCrab ransomware
Web application security course specialists report an attack campaign deployed by a group of Chinese hackers, which are looking for Windows servers...
-

 278
278Fancy Bear APT Hackers Owned Zebrocy Malware Opens Backdoor on Victims Machine to Control it Remotely
Cybercriminals from Sednit group, also known as Fancy Bear, APT28, Sofacy launching new Zebrocy Malware that indented to open backdoor on the...
-
 313
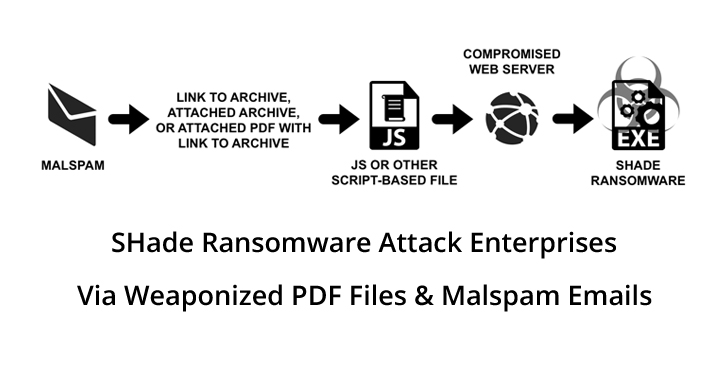
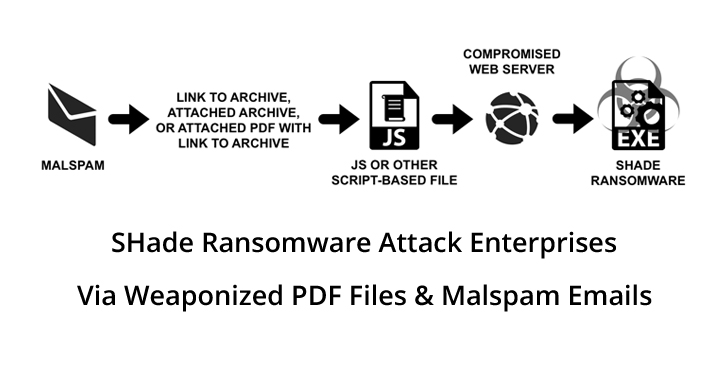
313Shade Ransomware Attack Enterprise Networks through Weaponized PDF Files & Malspam Emails
Shade Ransomware emerged in late 2014; it includes malicious spam emails or exploits kits as their primary attack vectors. In a recent...
-

 317
317Banking Malware grew 60% this year, how to protect your bank accounts
As mobile banking and online banking services grow, the threat actors’ interest in exploiting these platforms is also spreading. According to experts...
-
 356
356Should the Government of Baltimore or not pay ransom from cyberattack?
A few weeks ago website security audit specialists reported a ransomware attack on the Baltimore government’s computer infrastructure in which hackers managed...
-

 327
327Fake cryptocurrency apps crop up on Google Play as bitcoin price rises
ESET researchers have analyzed fake cryptocurrency wallets emerging on Google Play at the time of bitcoin’s renewed growth
-

 567
567A journey to Zebrocy land
ESET sheds light on commands used by the favorite backdoor of the Sednit group
-

 1.7K
1.7KAutomated Malware Analysis in the Cloud
Cybercriminals execute malware attacks using different attack vectors and using different methods. The number of malware strains is increasing in an unprecedented...
-
 312
312MuddyWater APT’s BlackWater Malware Campaign Install Backdoor on Victims PC to Gain Remote Access & Evade Detection
Researchers discovered a “Blackwater” malware campaign that suspected to associated with well known MuddyWater APT bypass the security control and install a...
-

 819
819Law Enforcement Operation Dismantles GozNym Banking Malware
An international law enforcement operation has led to the dismantling of the global cybercrime networkcybercrime network that used the GozNym banking malware...
-
 458
4588 Common Hacking Techniques & 3 Ways to Avoid Them All
Hackers come in many forms with sophisticated Hacking Techniques, While there has been a lot of discussion about online security in recent...
-

 256
256Hackers Launching Unique Windows and MacOS Malware via Fake WhatsApp Official Website
Researchers discovered a new malware that infect MacOS via malicious website by disguised as WhatsApp official website where it also drops a...
-

 370
370Hackers install backdoor on Asus computers using company update
Threat actors have compromised the Asus technology manufacturer update mechanism to install malware that allows installing a backdoor on compromised computers. According...






