Geek
-

 1.1K
1.1KWatch out as new PhoneSpy spyware hits Android devices
PhoneSpy spyware is currently targeting Android users in South Korea through third-party platforms. Zimperium zLabs researchers have revealed findings on PhoneSpy spyware...
-

 398
398Facebook sues Ukrainian man for scraping and selling 178m users’ data
Facebook tracked down the programmer after he mistakenly used his contact information on email and job portals. On October 21, 2021, Facebook...
-

 2.4K
2.4KWhy You Should Use Dynamic QR Code Generator
We cannot argue that proof of authenticity gives more credibility. To make your brand more authentic, you need to have a dynamic...
-

 2.5K
2.5KSquid Game app on Play Store was spreading Joker malware
Squid Game and Joker malware turn out to be a “killer combination” after all. Netflix’s biggest ever series Squid Game is a...
-

 1.4K
1.4KFacebook down with Messenger, Instagram, WhatsApp service disruption
Facebook down? Yes, Facebook is down along with Messenger, Instagram, WhatsApp, and Oculus VR due to DNS-related issues. You are not alone;...
-
 4.0K
4.0KTangleBot Android malware hijacks phone to steal login credentials
TangleBot Android malware is delivered through smishing and is currently targeting users in Canada and the US disguised as information about COVID-19...
-
 2.0K
2.0KChoosing a web hosting service that’s right for your business
With a web hosting service, a small business can focus on what its website should look like, what information it wants to...
-
 3.0K
3.0KGoogle, Microsoft and Oracle generated most vulnerabilities in 2021
Google holds the top slot with over 547 vulnerabilities, Microsoft is on number two with 432 unwanted exposure instances and Oracle is...
-
 5.3K
5.3KUrgent Chrome security update released to patch widely exploited 0-day
The vulnerability (CVE-2021-37973) impacts 2 Billion Chrome users worldwide therefore update your browser right now to the latest version. On Friday 24th,...
-
 1.7K
1.7KMicrosoft warns of Nobelium hackers using FoggyWeb backdoor
Microsoft has warned of a new FoggyWeb backdoor being used by Nobelium, the same state-sponsored hacking group believed to be responsible for...
-

 499
499Israeli firm Kape Technologies buys ExpressVPN raising privacy concerns
Kape Technologies is an Israeli cybersecurity firm that has bought ExpressVPN for $936 million. Kape Technologies, a leading Israeli cybersecurity firm, has...
-
 2.7K
2.7KMalicious Office documents make up 43% of all malware downloads
In the 3rd quarter of 2020, around 38% of all downloadable malware were found hidden in Office documents – In the first...
-

 4.4K
4.4KTop 6 SEO Conferences in the USA
Search engine optimization is one of those fields that’s akin to New York City – it never sleeps. It keeps evolving 24/7...
-

 1.8K
1.8KUnpatched Microsoft Exchange servers hit with ProxyShell attack
Researchers have identified 140+ webshells launched against 1,900 unpatched Microsoft Exchange servers. The Cybersecurity & Infrastructure Security Agency (CISA) issued an urgent...
-
 2.5K
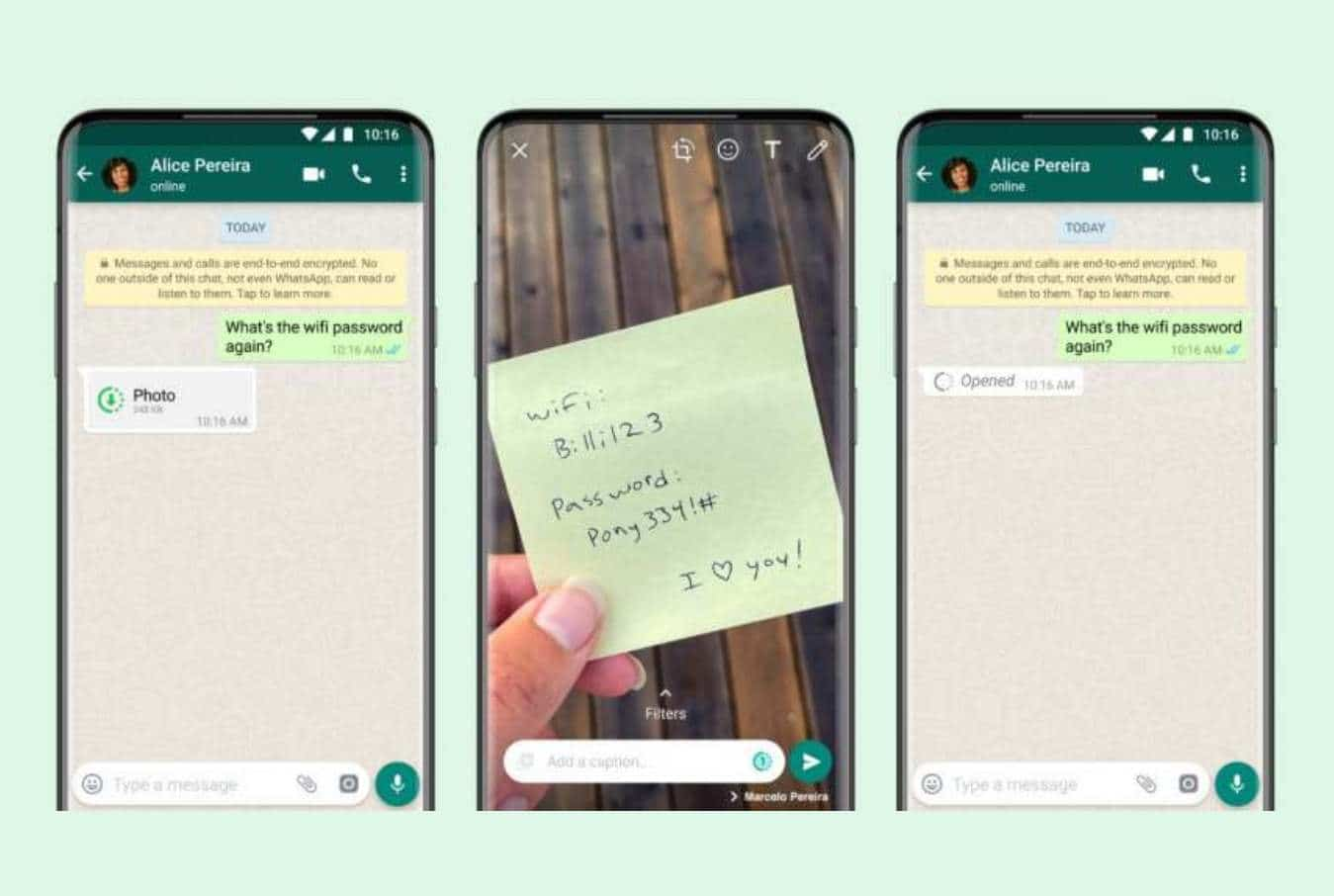
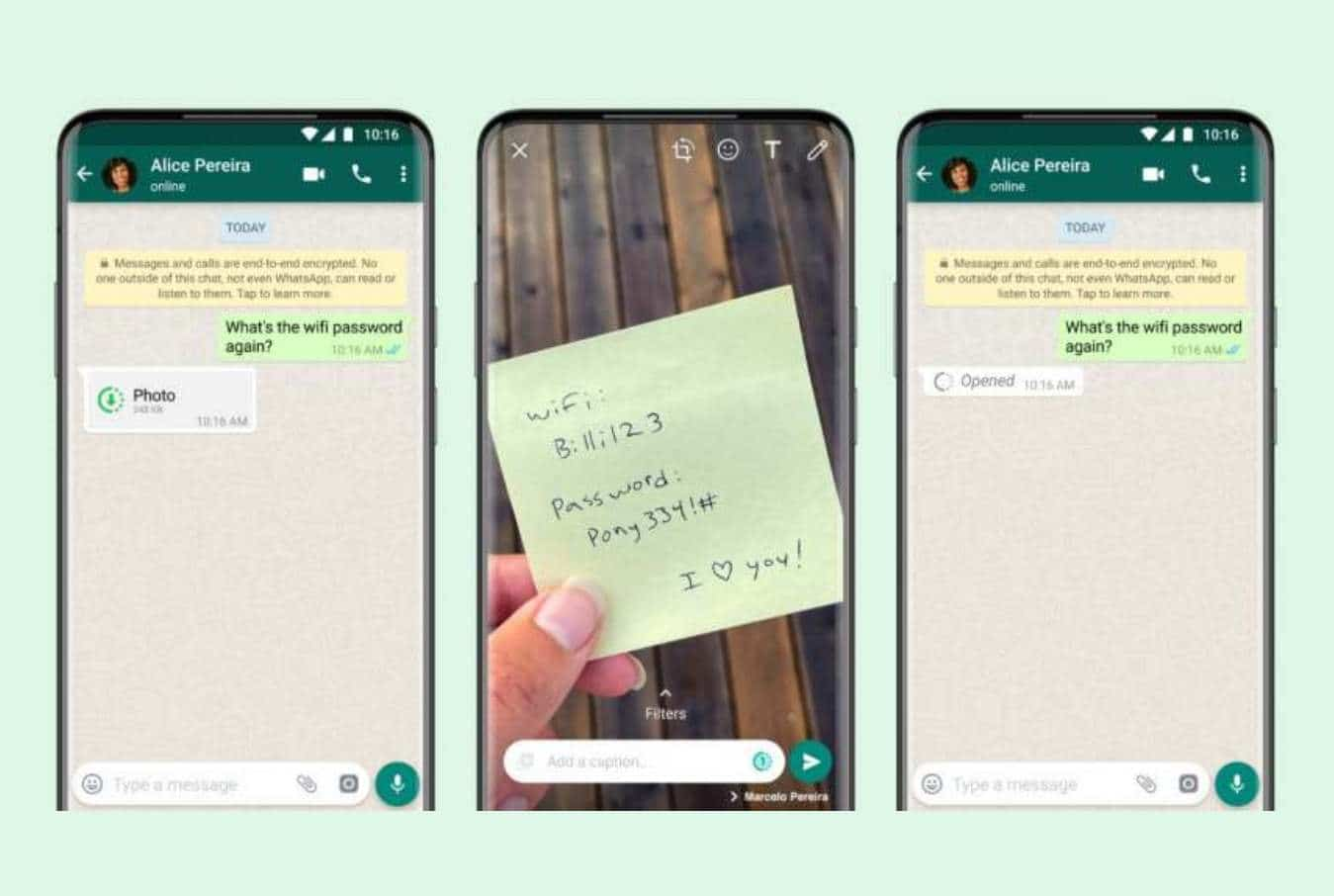
2.5KWhatsApp Introduces View Once Feature for Videos and Photos
View Once feature will keep the images accessible for a maximum of 14 days and expire afterward. It’s quite amusing that Facebook...
-

 951
951Why your remote employees may underperform? Top 10 problems
Organizing remote work is a challenge for any business owner. Read on to find workable strategies to maximize the output of your...
-
 2.2K
2.2KCrooks using phony call centers to spread ransomware via BazaCall attacks
In BazaCall, a “vishing-like” method is used in which victims receive email messages notifying them that subscription fees apply or their subscription...
-

 5.3K
5.3KMicrosoft warns of PetitPotam attack taking over Windows domains
Experts reveal that the PetitPotam attack forces remote Windows servers such as Domain Controllers to validate a malicious destination. Microsoft has released...
-
 1.4K
1.4KWindows Defender update caught removing zip, exe, source code files
Reportedly, the Windows Defender daily update flagged DeCSS DVD encryption software copy as a Trojan and quarantined it before deleting it after...
-
 2.2K
2.2KSolarWinds hackers exploited iOS 0-day to compromise iPhones
According to Google, SolarWinds hackers used the vulnerability to steal web security credentials from Western European government officials. Google published a report...
-
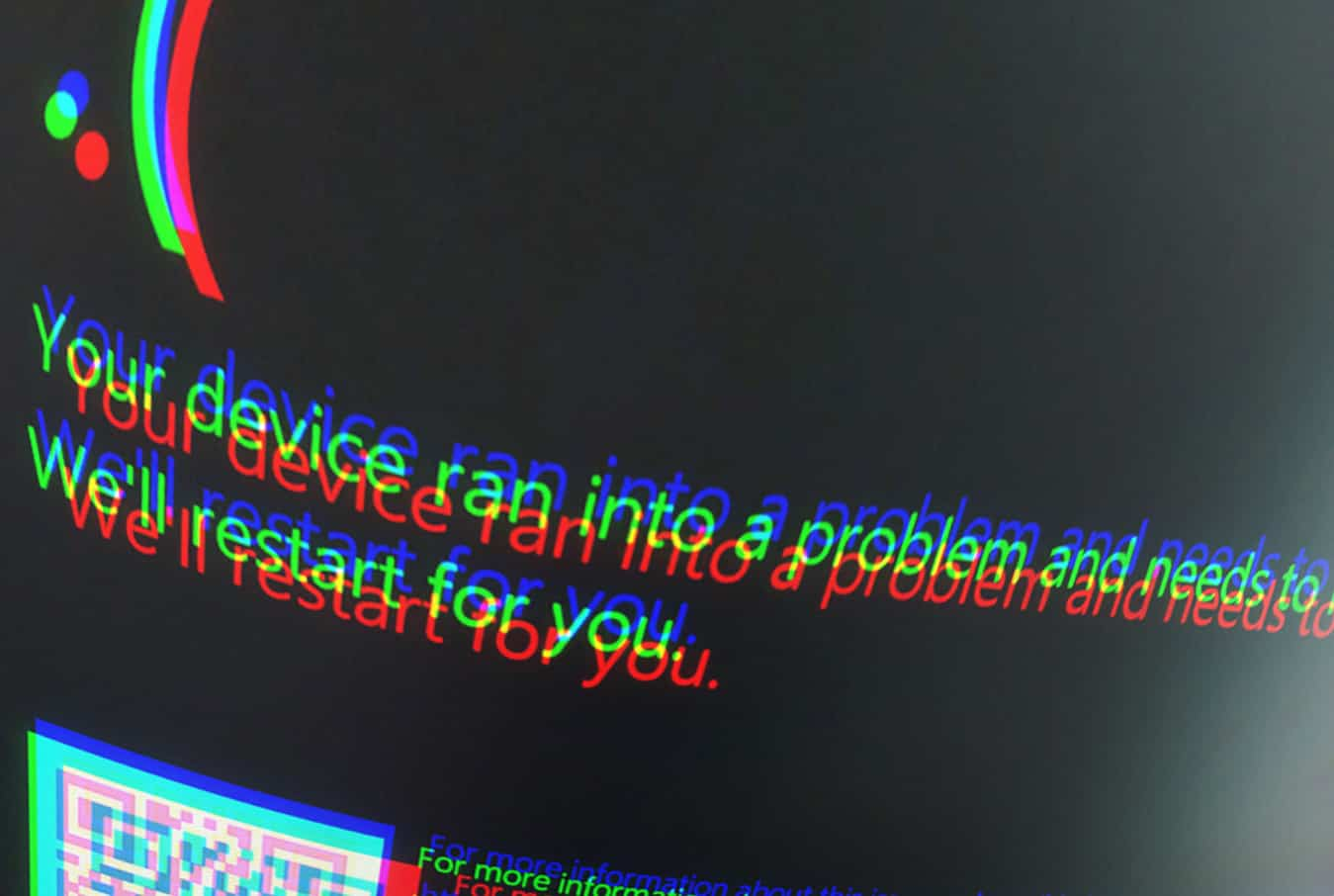
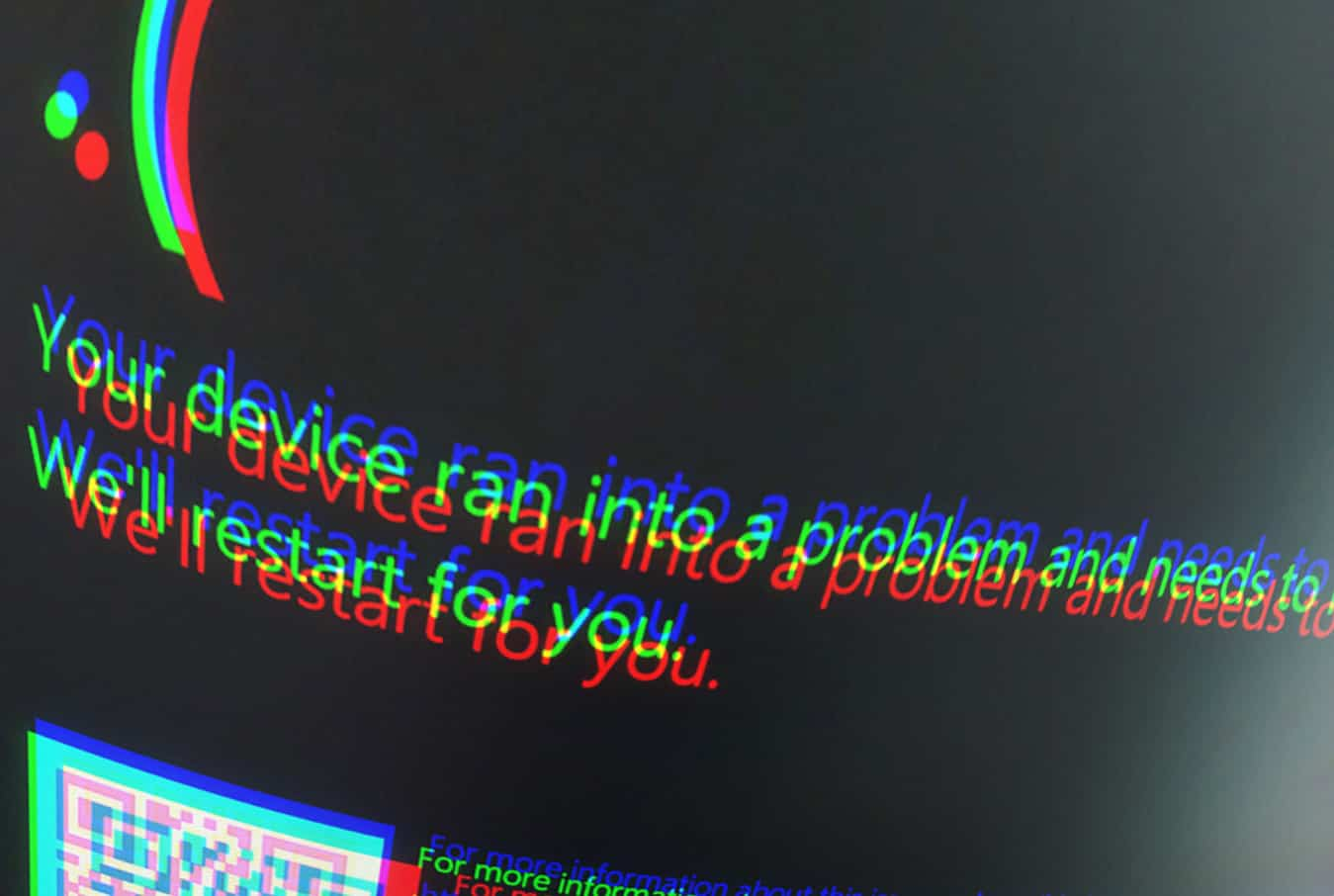 5.3K
5.3KBlue Screen of Death will be Black Screen of Death in Windows 11
Microsoft’s Blue Screen of Death Revamped for Windows 11. We thought that the start menu is the only element in Microsoft’s Windows...






