Tutorials
-

 3.0K
3.0KHow to do penetration testing of IoT devices easily
The Internet of Things (IoT) is probably one of the most widely used technological concepts in recent times, as it has implementations...
-

 951
951How to do digital forensics of a hacked network with TCPDUMP
Digital forensics is one of the most important elements of ethical hacking, as it allows researchers to learn as much as possible...
-

 4.7K
4.7KHow to hack into WAF (Web application firewall) using XSS attacks?
Cross-site scripting (XSS) attacks are a variant of code injection that involves the use of specially crafted scripts on legitimate websites for...
-

 2.8K
2.8KHow to do automatic vulnerability analysis and assessment of your applications & network free of cost?
The automatic analysis of potential security flaws has become one of the essential tasks for developers, researchers and experts in vulnerability assessment,...
-

 1.1K
1.1KHow to do digital forensics and reverse engineering on windows registries with free REGRIPPER tool
System logs analysis is one of the most useful hacking tasks for researchers and specialists in digital forensics and reverse engineering, so...
-

 2.2K
2.2KHow to easily copy Facebook, Instagram, Twitter Gmail cookies and browser stored passwords to a USB pendrive, all with just 15 commands
Gathering cookies is a popular hacking activity and can prove really useful for obtaining information from a target, so it is necessary...
-

 3.1K
3.1KHow to hack WPA2-PSK WiFi passwords easily with just 10 commands using this tool
Password cracking for WiFi networks is one of the hacking activities that most interest beginner researchers, cybersecurity experts and sporadic users alike...
-
 4.7K
4.7K8 techniques to protect your Windows network domains against Mimikatz credential stealing tool
One of the main variants of attack against Windows systems is the abuse of Active Directory using tools for credential theft such...
-
 5.2K
5.2KHow to hack and bypass a web application firewall WAF during penetrating testing
The term web application firewall (WAF) refers to a set of monitoring tools and filters designed to detect and block network attacks...
-
 1.2K
1.2KTop 6 remote access Trojans (RAT) used by Russian hackers. Which one is the best as per malware analysis experts?
Remote access Trojans (RATs) are one of the most popular hacking tools, as they allow attackers to remotely control a compromised system....
-

 3.9K
3.9K10 Best gadgets and tools for real hackers and cyber security professionals
The fight against cybercrime is one of the main responsibilities of the ethical hacking and cyber security community. This effort depends on...
-

 2.7K
2.7KTutorial to create phishing sites of 100 famous websites in minutes
Phishing remains one of the most common and dangerous criminal practices for users in general, and every day new and dangerous tools...
-

 4.4K
4.4KTutorial to create a free telegram bot to receive temporary email from hacked computers
Telegram has become one of the best instant messaging tools, currently being the main counterpart of WhatsApp thanks to its advanced privacy...
-

 1.8K
1.8KHow to hack WhatsApp in 2021 and how to protect it so that nobody can spy on your messages
WhatsApp is the world’s most popular messaging platform, with around 1.5 billion active users a month sending text messages, voice notes, multimedia...
-

 2.4K
2.4KDo background check of girlfriend or crush in 75 different social media networks in 10 minutes with just 5 commands
Collecting information is an important phase for investigation. Now days whenever user visits any blogger websites. Many websites ask for email addresses...
-
 4.0K
4.0KHow to Redirect Web Traffic Using Tor easily
Tor is the most famous web browser which provides anonymity/ privacy over the internet. Many companies/ whistle blowers uses TOR for working...
-

 1.7K
1.7KFind Firewall & CDN used a website during Pentest with VXSCAN
Information gathering phase shows how an pentester should prepare for his next phases. Because in this phase pentester have to collect information...
-

 1.4K
1.4KDifferent Ways for Wifi Cracking
Wireless Networks Wireless network which enables end-point devices to communicate with internet by connecting to an AP device. Wiresless device are also...
-
 3.1K
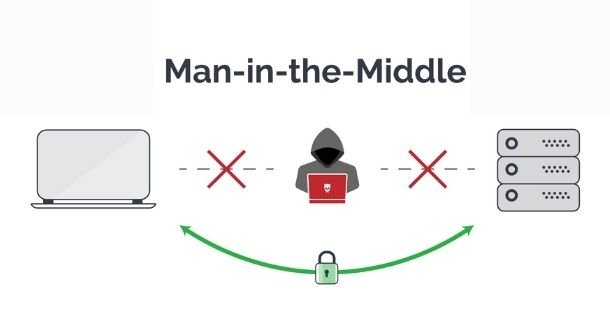
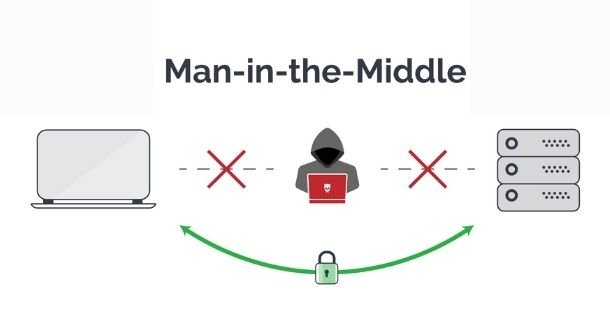
3.1KThe best 6 MiTM (Man-in-The-Middle) attack tools that every ethical hacker should have
Man-in-The-Middle (MiTM) attacks are one of the most popular hacking techniques nowadays, and occur when a third party arbitrarily breaks into an...
-
 4.0K
4.0KTop 10 utilities for your Linux server to check if it is hacked and monitoring activities
Users of Linux systems are sometimes not aware of all the tools and functions on the system. Thinking about this situation, digital...
-

 2.5K
2.5KTop 15 hacking tools for doing penetration testing from mobile phones
Pentesting has become one of the main practices of the cybersecurity community and even represents an important source of income for independent...






