Tutorials
-

 3.3K
3.3KHow to easily check if DOC, RTF, XLS, PPT, PPTX or PDF file has a malware without antivirus like a digital forensics expert
In most cyberattack variants threat actors use legitimate-looking documents loaded with malware, which is why researchers often say it all starts with...
-

 4.8K
4.8KETHICAL HACKING & PROTECTION FROM HACKERS: 60 BEST HACKING TOOLS USED BY CYBER SECURITY EXPERTS 2021 – PART 2
In the previous tutorial, experts in ethical hacking from the International Institute of Cyber Security (IICS) showed you dozens of the best...
-

 493
493ETHICAL HACKING & PROTECTION FROM HACKERS: 60 BEST HACKING TOOLS USED BY CYBER SECURITY EXPERTS 2021 – PART 1
Security agencies and hacking groups around the world use the most sophisticated network security and pentesting tools to detect vulnerabilities in a...
-
 2.5K
2.5KPROBIV: The most famous Russian black market to find job or buy illegal things
Currently, an illegal marketplace that can solve many problems for cyber criminals and affect everyone else exists, as mentioned by digital forensics...
-

 4.1K
4.1KSteps to create your own VPN
Alphabet Inc., through its cybersecurity subsidiary Jigsaw, announced the launch of Outline, a project that allows any user to create and run...
-

 4.8K
4.8KTop 7 apps to fake your WhatsApp live location in real time
Nowadays it is very easy to find unknown locations using GPS technology, Internet connection and a smartphone; unfortunately this has its disadvantages,...
-

 2.1K
2.1KTest your router’s security with your smartphone and only 9 commands
Although it is underestimated, router security is vital to protect our networks from intruders and take the most out of their features,...
-

 2.5K
2.5KHow to do cyber security audit of IP camera network? Pentesting a CCTV system tutorial
The security of Internet-connected cameras remains a very little explored topic. According to IT security audit specialists from the International Institute of...
-

 2.3K
2.3KComplete Guide to track planes of president, military and passenger planes
In-flight aircraft monitoring is a very entertaining way to learn how to use tracking tools, information security experts from the International Institute...
-

 3.5K
3.5KSteps to do RAM memory forensics to recover passwords & confidential information with mXtract
The information stored on a computer does not always end up on permanent storage drives (hard drives, solid-state drives, removable storage, among...
-

 3.4K
3.4KTop 15 torrents websites to download any file for free in 2021
When searching for torrents on the Internet it is necessary to use specialized search engines but how to know which is the...
-

 2.9K
2.9KRevenge of your enemies by crashing their phone with thousands of calls at once. Phone call attack with only 9 commands
Not many people know it, but it’s very easy to get in the way of a phone without the owner having any...
-

 3.9K
3.9KHOW TO DETECT HIDDEN CAMERAS OR SPY CAM IN A ROOM
Many users ignore it, but by using their laptop camera or any other camera with a WiFi connection, their MAC address will...
-

 2.5K
2.5KRevenge your ex-boss or ex-girlfriend by crashing their phone by SMS messages. Send thousands of SMS messages with just 12 commands
In this tutorial, experts in ethical hacking from the International Institute of Cyber Security (IICS) will show you how to send thousands...
-

 5.0K
5.0KStealing anyone’s Telegram channel or account session with just 4 commands
Telegram channel theft has become a frequent and completely real threat, mentioning mobile security specialists from the International Cyber Security Institute (IICS)....
-

 3.5K
3.5KHow to configure, run and automate OpenVAS: Free Vulnerability Scanner
Information security researchers often require plugins for vulnerability scanners in Kali Linux, although due to licensing restrictions these tools are not included...
-
 2.6K
2.6KFinding links on website where CloudFlare is not protecting. Attacking real IP address with CloudFail
Cloudflare is a denial of service (DDoS) protection mechanism for your servers or, so to speak, it is a barrier between the...
-

 1.3K
1.3KTop 5 apps to audit WiFi networks
WiFi security is an element that sometimes receives little attention from system administrators, although it is a fundamental factor in consolidating a...
-

 3.3K
3.3KRevenge your neighbor’s party by jamming any Bluetooth speaker. Creating a Bluetooth jammer with just 9 commands without any special hardware
We’ve all dealt with annoying neighbors who keep listening to music at a high volume, even in the early morning and thanks...
-
 1.2K
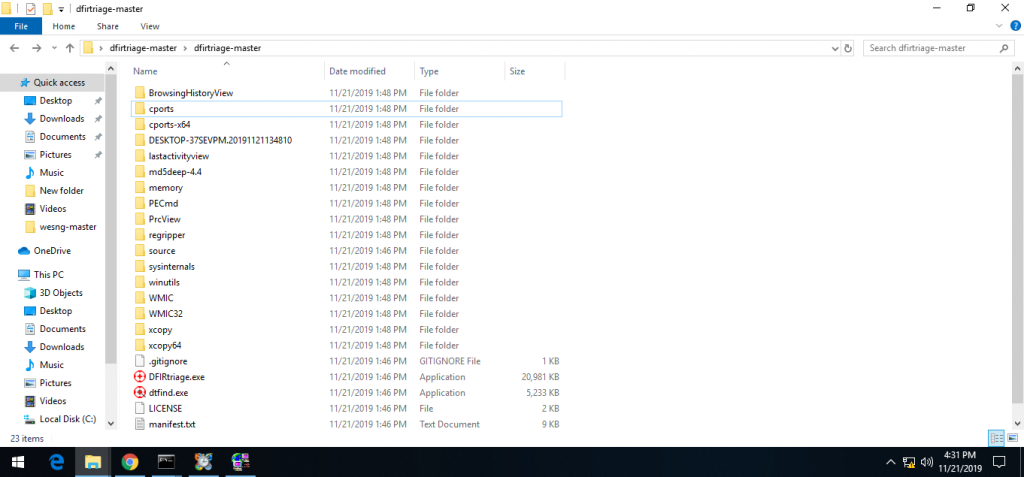
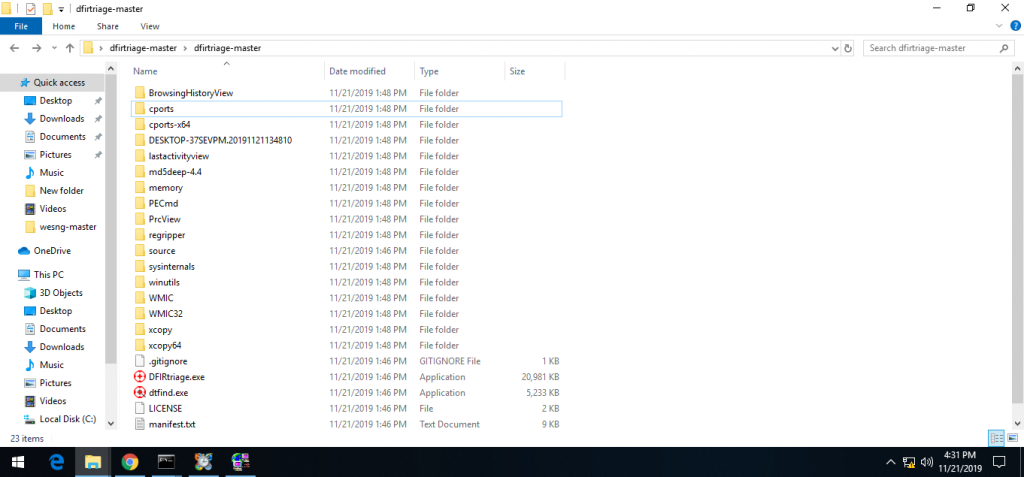
1.2KDigital forensics tools for Windows 10 Forensics and incident response
Windows is the most common operating system. There are many organizations who prefer windows OS. Windows is also most targeted operating system...
-

 2.1K
2.1KHow to find Vulnerabilities in CMS Websites
Finding vulnerabilities takes time for pentester/ security researcher. There are many tools & techniques for finding bugs in any URL. Earlier we...






