Geek News
Popular Posts
-
 5.1KVulnerabilities
5.1KVulnerabilitiesWordPress LiteSpeed Plugin Vulnerability Puts 5 Million Sites at Risk
A security vulnerability has been disclosed in the LiteSpeed Cache plugin for WordPress that...
-

 5.1KVulnerabilities
5.1KVulnerabilitiesMalicious Code in XZ Utils for Linux Systems Enables Remote Code Execution
The malicious code inserted into the open-source library XZ Utils, a widely used package...
-

 5.1KVulnerabilities
5.1KVulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
A security flaw impacting the Lighttpd web server used in baseboard management controllers (BMCs)...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
The maintainers of the PuTTY Secure Shell (SSH) and Telnet client are alerting users...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesUrgent: Secret Backdoor Found in XZ Utils Library, Impacts Major Linux Distros
Red Hat on Friday released an “urgent security alert” warning that two versions of...
-

 4.2KVulnerabilities
4.2KVulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
Multiple threat actors are weaponizing a design flaw in Foxit PDF Reader to deliver a variety of malware such as Agent Tesla,...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
All developers want to create secure and dependable software. They should feel proud to release their code with the full confidence they...
-

 3.7KMalware
3.7KMalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
A “multi-faceted campaign” has been observed abusing legitimate services like GitHub and FileZilla to deliver an array of stealer malware and banking...
-

 1.6KMalware
1.6KMalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
Cybersecurity researchers have observed a spike in email phishing campaigns starting early March 2024 that delivers Latrodectus, a nascent malware loader believed...
-

 2.8KMalware
2.8KMalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
The threat actors behind the Windows-based Grandoreiro banking trojan have returned in a global campaign since March 2024 following a law enforcement...
-
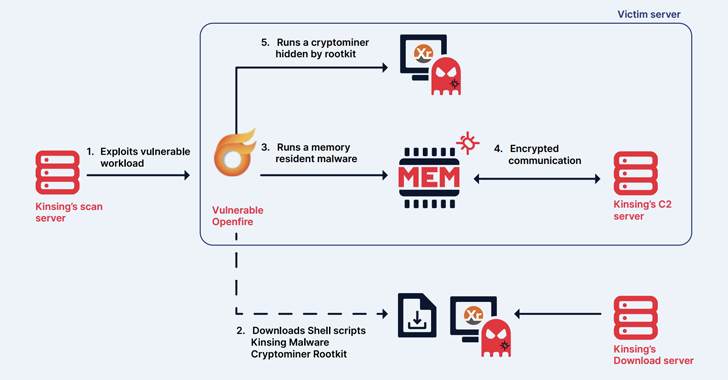
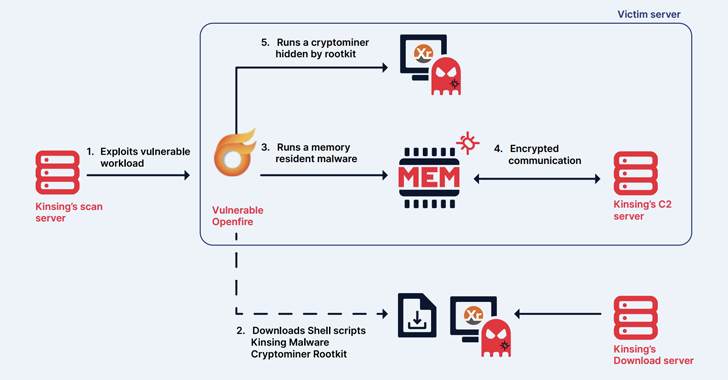 3.8KMalware
3.8KMalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
The cryptojacking group known as Kinsing has demonstrated an ability to continuously evolve and adapt, proving to be a persistent threat by...
-

 650Malware
650MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
Cybersecurity researchers have shed more light on a remote access trojan (RAT) known as Deuterbear used by the China-linked BlackTech hacking group...
-
 3.1KMalware
3.1KMalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
The Kimsuky (aka Springtail) advanced persistent threat (APT) group, which is linked to North Korea’s Reconnaissance General Bureau (RGB), has been observed...
-

 4.4KVulnerabilities
4.4KVulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
Researchers have discovered a new security vulnerability stemming from a design flaw in the IEEE 802.11 Wi-Fi standard that tricks victims into...
-
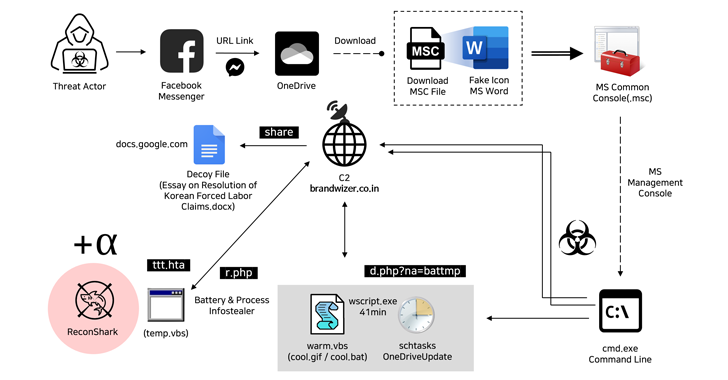
 4.3KMalware
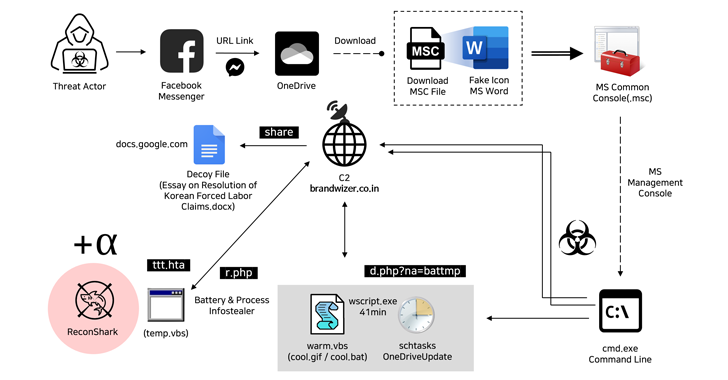
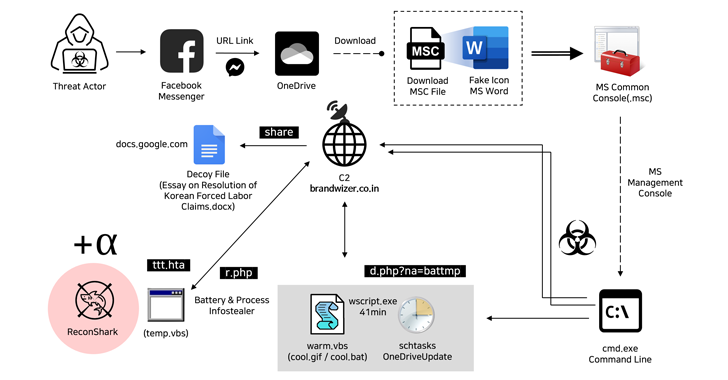
4.3KMalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
The North Korea-linked Kimsuky hacking group has been attributed to a new social engineering attack that employs fictitious Facebook accounts to targets...
-

 4.0KMalware
4.0KMalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
The Microsoft Threat Intelligence team said it has observed a threat actor it tracks under the name Storm-1811 abusing the client management...
-

 1.8KVulnerabilities
1.8KVulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
Google has rolled out fixes to address a set of nine security issues in its Chrome browser, including a new zero-day that...
-

 3.1KData Breach
3.1KData BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
Law enforcement agencies have officially seized control of the notorious BreachForums platform, an online bazaar known for peddling stolen data, for the...
-
 4.9KMalware
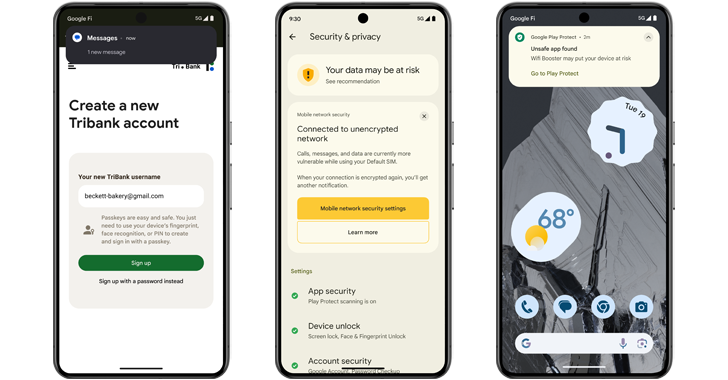
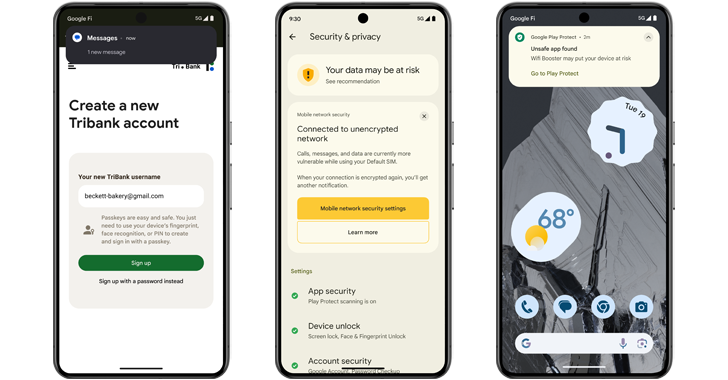
4.9KMalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
Google is unveiling a set of new features in Android 15 to prevent malicious apps installed on the device from capturing sensitive...
-

 4.9KMalware
4.9KMalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions
An unnamed European Ministry of Foreign Affairs (MFA) and its three diplomatic missions in the Middle East were targeted by two previously...
-

 2.4KVulnerabilities
2.4KVulnerabilities(Cyber) Risk = Probability of Occurrence x Damage
Here’s How to Enhance Your Cyber Resilience with CVSS In late 2023, the Common Vulnerability Scoring System (CVSS) v4.0 was unveiled, succeeding...
-

 4.8KMalware
4.8KMalwareEbury Botnet Malware Compromises 400,000 Linux Servers Over Past 14 Years
A malware botnet called Ebury is estimated to have compromised 400,000 Linux servers since 2009, out of which more than 100,000 were...
-

 827Cyber Attack
827Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
Microsoft has addressed a total of 61 new security flaws in its software as part of its Patch Tuesday updates for May...
-

 4.4KVulnerabilities
4.4KVulnerabilitiesVMware Patches Severe Security Flaws in Workstation and Fusion Products
Multiple security flaws have been disclosed in VMware Workstation and Fusion products that could be exploited by threat actors to access sensitive...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesNew Chrome Zero-Day Vulnerability CVE-2024-4761 Under Active Exploitation
Google on Monday shipped emergency fixes to address a new zero-day flaw in the Chrome web browser that has come under active...
The Latest
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
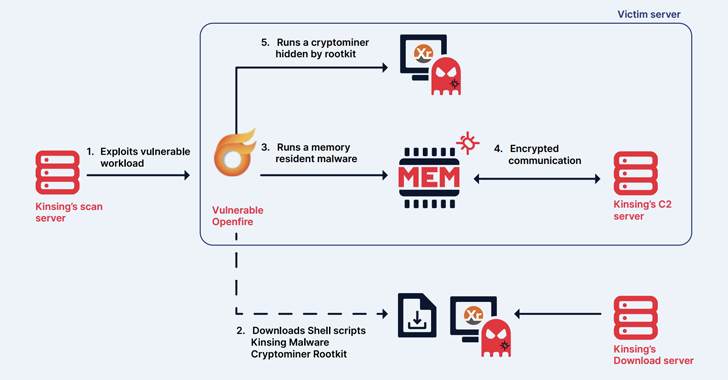 Malware
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
 Malware
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Malware
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions
-
 Vulnerabilities
Vulnerabilities(Cyber) Risk = Probability of Occurrence x Damage
-
 Malware
MalwareEbury Botnet Malware Compromises 400,000 Linux Servers Over Past 14 Years
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Vulnerabilities
VulnerabilitiesVMware Patches Severe Security Flaws in Workstation and Fusion Products
-
 Vulnerabilities
VulnerabilitiesNew Chrome Zero-Day Vulnerability CVE-2024-4761 Under Active Exploitation