Featured News
-

 199Vulnerabilities
199VulnerabilitiesMicrosoft Issues Optional Windows Update to Fix MouseJack Vulnerability
Update only addresses its own wireless devices. Along with its regular monthly security updates, Microsoft also released some optional updates, among which is...
-
 247Geek
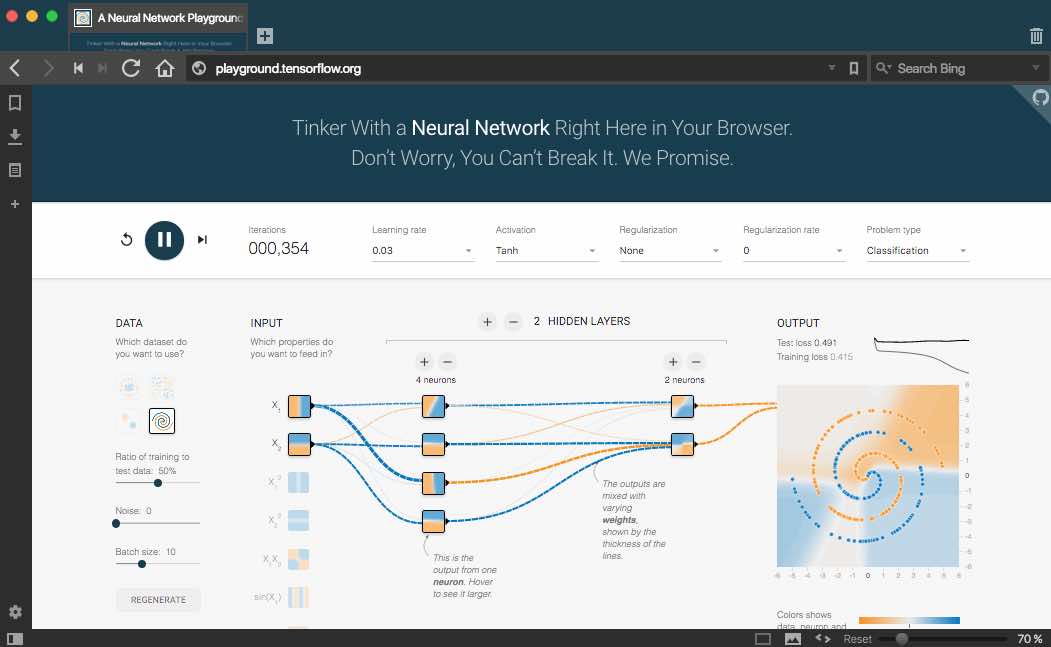
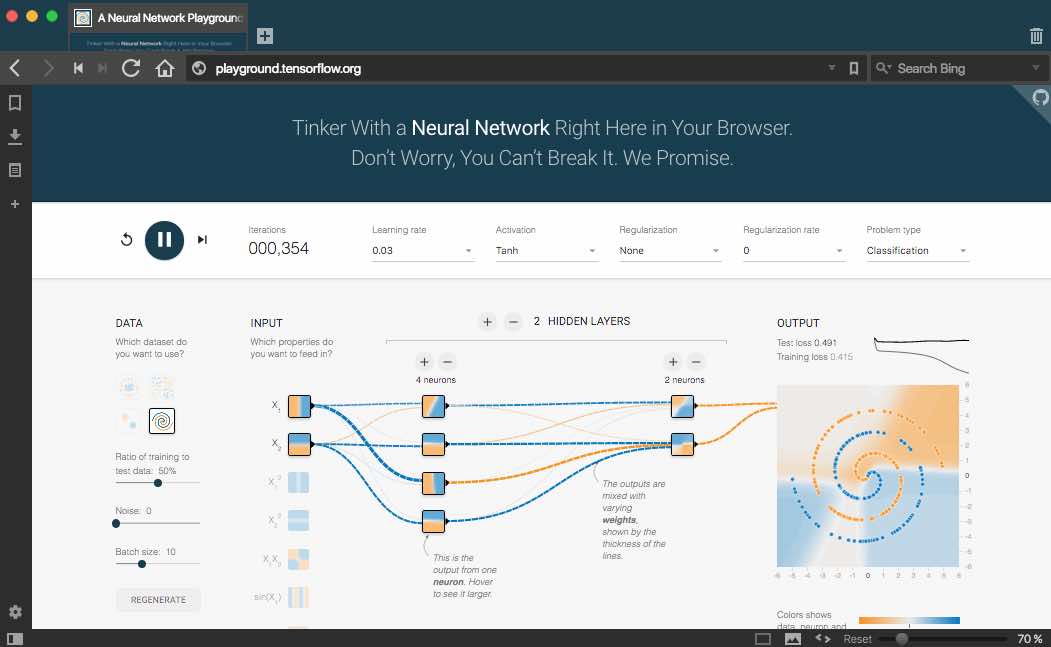
247GeekDeep Playground — How To Play With A Neural Network Right Here In Your Browser
Short Bytes: Deep Playground is an online visualization of how a neural network learns over the time and generates an output. Written...
-
 278Geek
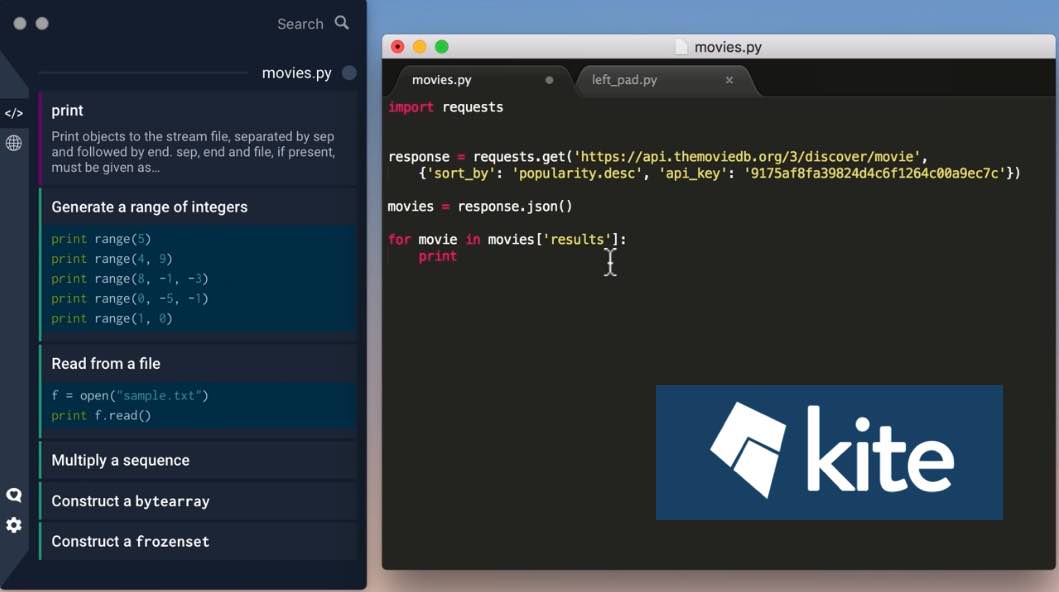
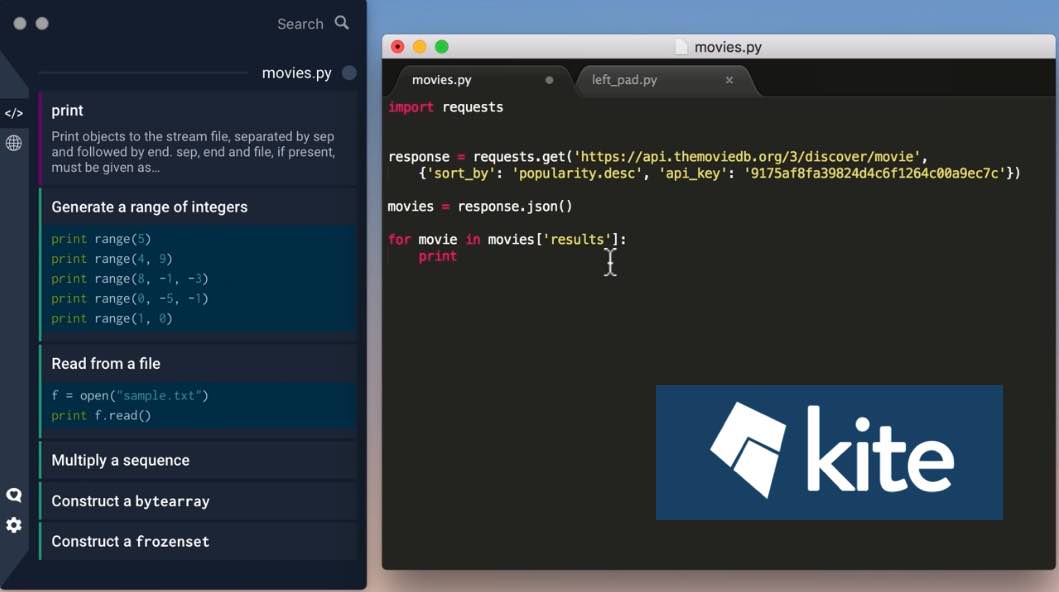
278GeekKite ‘Artificial Pair Programmer’ Is A Programmer’s New Best Friend
Short Bytes: Kite is an artificial pair programmer that runs alongside your text editor or terminal. It suggests you command examples, library...
-
 147Malware
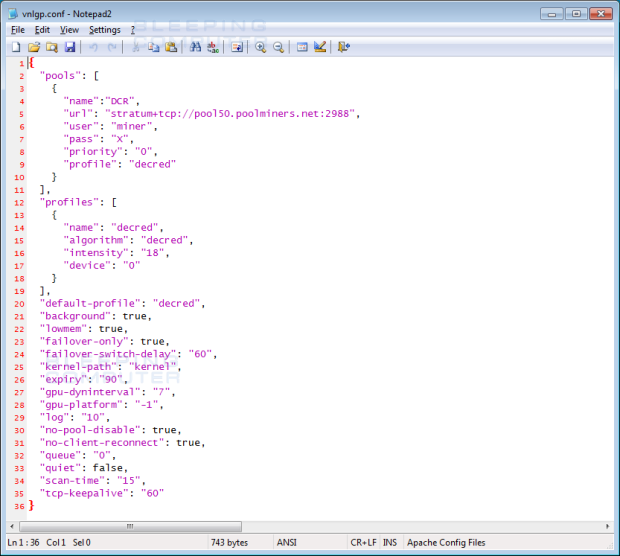
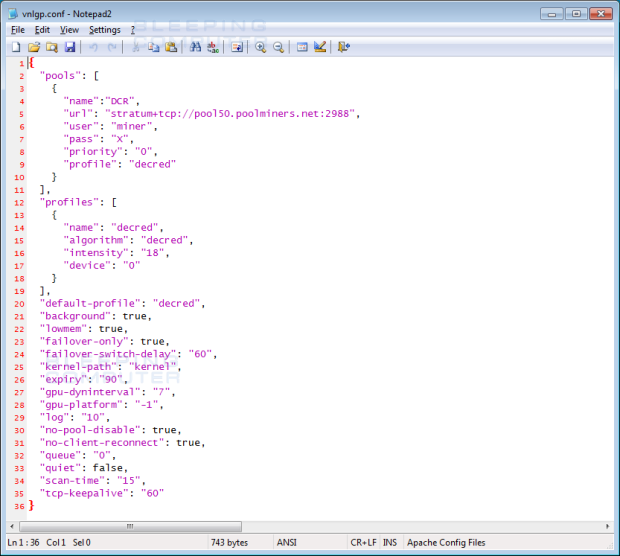
147MalwareAdware Bundlers pushing CryptoCurrency Miners on Unsuspecting Victims
Adware installers are out of control and with little or no law regulating them, the crap they push onto their victims is...
-
 157Vulnerabilities
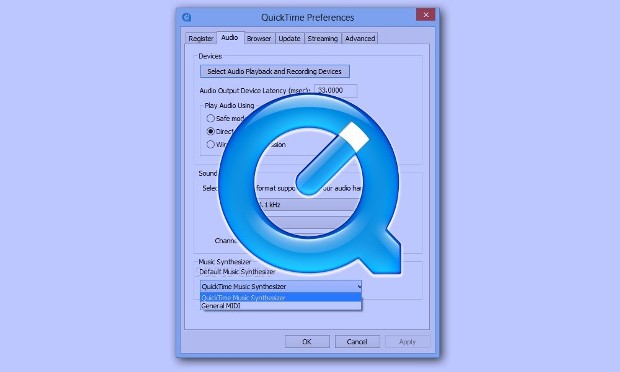
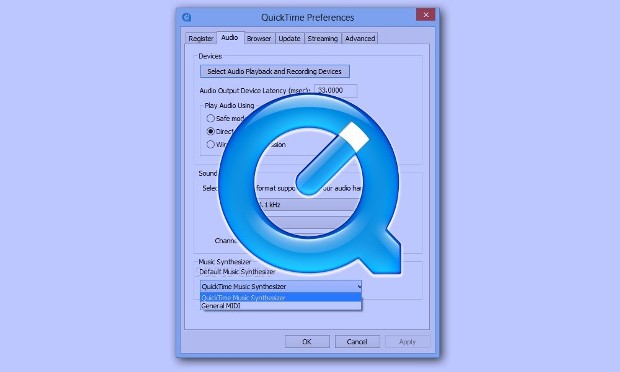
157VulnerabilitiesApple stops patching QuickTime for Windows despite 2 active vulnerabilities
Security firm urges Windows users to uninstall media player. If your Windows computer is running Apple’s QuickTime media player, now would be a...
-

 205Hacked
205HackedMicrosoft Sues U.S. Government To Protect YOUR Private Data From Snooping
Short Bytes: Very often governments ask the tech companies to provide the personal information of their customers and force them to remain...
-

 289Incidents
289IncidentsBlizzard And ‘World of Warcraft’ Taken Down By DDoS Attacks
DDOS attacks are a fact of life these days, it would seem. People were having trouble logging into Blizzard games such as...
-

 274Geek
274GeekSorry Folks Range Rover Sport 2016 Give Away is a Facebook Scam
Sorry Folks No Range Rovers being Given away—Stay Away from Free Range Rover Competition on Facebook The Facebook page of Free Range...
-

 279Data Security
279Data SecuritySamsung Galaxy Phones Prone to Hacking via USB Cable even if Locked
In various Samsung Galaxy devices, it is possible to send AT commands through USB cables — The most startling fact is that...
-

 222Cyber Events
222Cyber EventsSweden Says its critical infrastructure was under Attack by Russian Hackers
Sweden says its cyberspace was under sophisticated cyber attack from Russia Sweden sent a message to NATO and released alert all over...
-

 317Geek
317GeekMicrosoft Releases Open Source Visual Studio Code 1.0 For Windows, OS X, And Linux
Short Bytes: Microsoft’s open source text editor Visual Editor Code has finally hit the stable version 1.0. VS Code is now used...
-
 231Geek
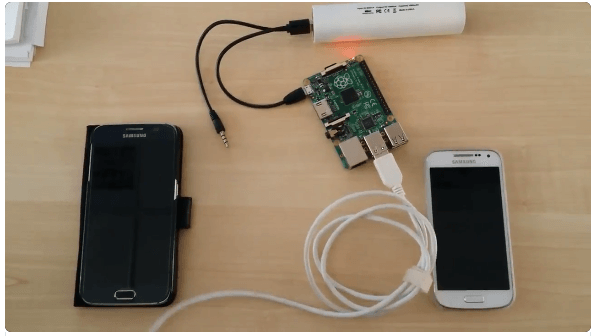
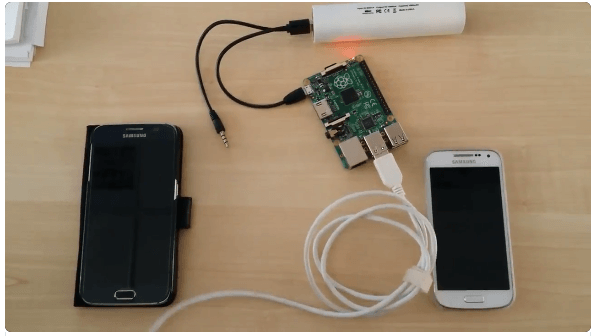
231GeekArduino Comes To Raspberry Pi And Other Linux ARM Devices
Short Bytes: The Arduino project has finally released Arduino IDE for Raspberry and other single-board ARM computers. Combining Raspberry Pi with Arduino is...
-

 221Scams
221ScamsMy video, My first video, Private video: Don’t fall for this Facebook scam
My video, My first video, Private video: Don’t fall for this Facebook scam, which is infecting accounts around the world with a...
-
 99Data Security
99Data SecurityLinux Computers Targeted by New Backdoor and DDoS Trojan
Threat level is not high, the virus requires users to give it root privileges in order to infect their computers. After being...
-
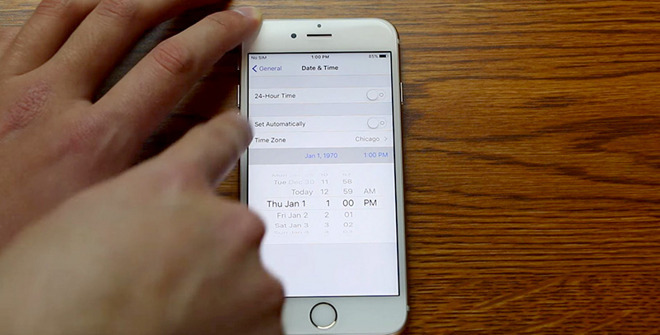
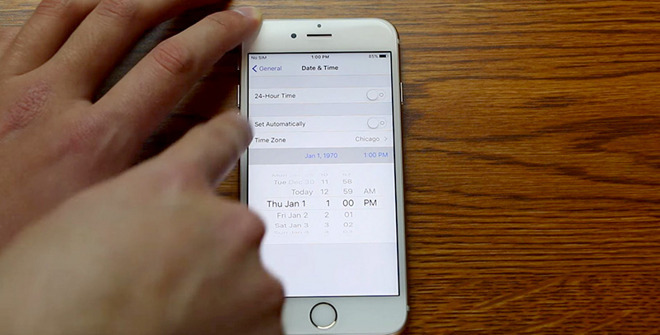 104Vulnerabilities
104VulnerabilitiesNew version of iOS ‘date bug’ being exploited through public Wi-Fi hotspots
You can still brick an iPhone running on iOS 9.3 using January 1, 1970 bug and public Wi-Fi. If you are sitting in...
-
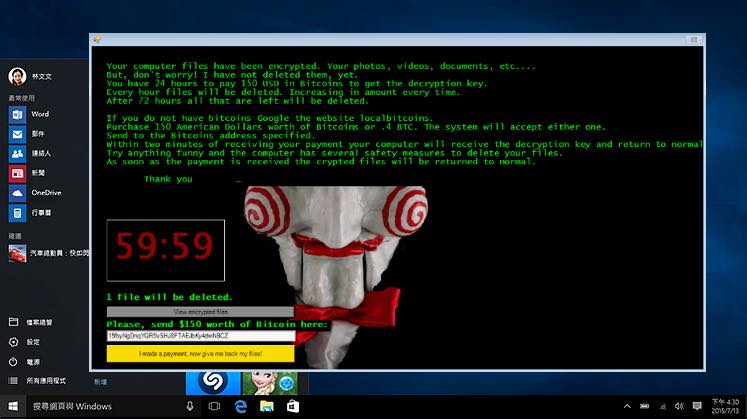
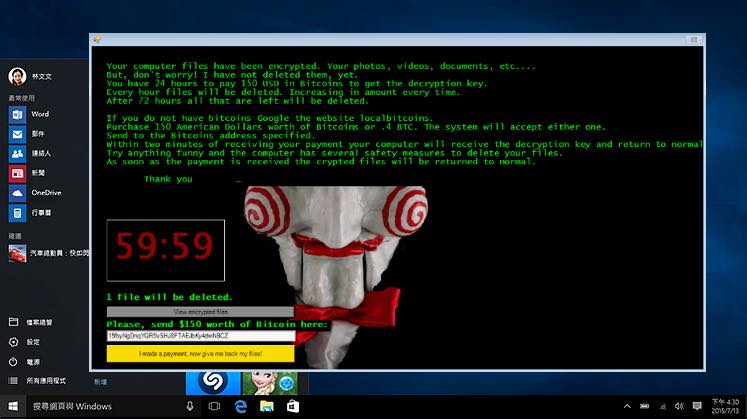 183Hacked
183HackedJigsaw: This Ransomware Wants To Play A “Scary” Game With Before Destroying Your Files
Short Bytes: Jigsaw ransomware is a new threat affecting the computers and demanding ransom in a scary manner. If you fail to...
-
 177Vulnerabilities
177VulnerabilitiesHacking Samsung Galaxy via Modem interface exposed via USB
Modems in a number of Samsung Galaxy devices are open to receiving AT commands over the USB cable even when they are...
-

 193Incidents
193IncidentsLottery security director used hacked DLL to manipulate and predict winning tickets
Lottery boss wins $16.5 million in six years by tampering random number generator. According to The Des Moines Register, in a case from...
-
 213How To
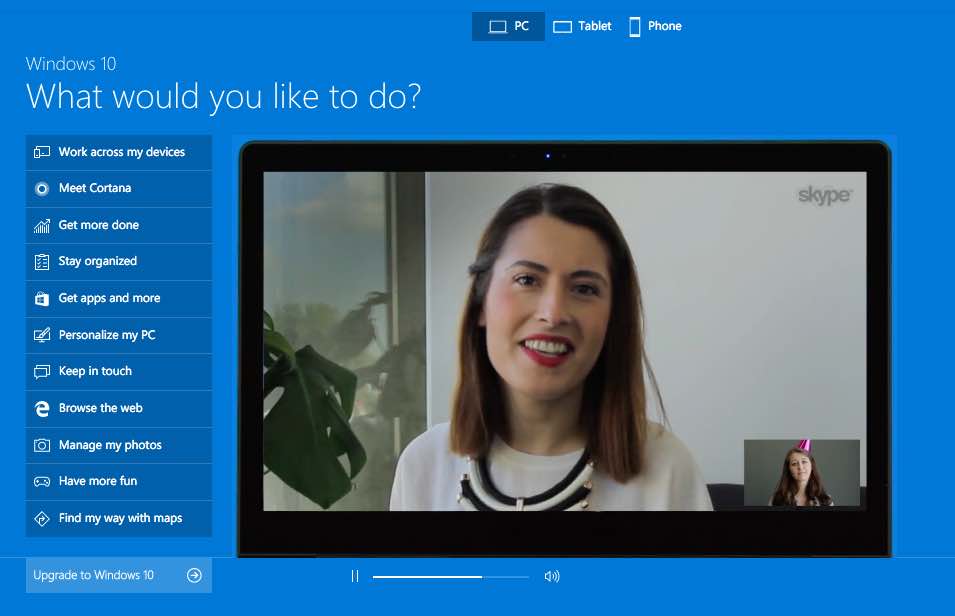
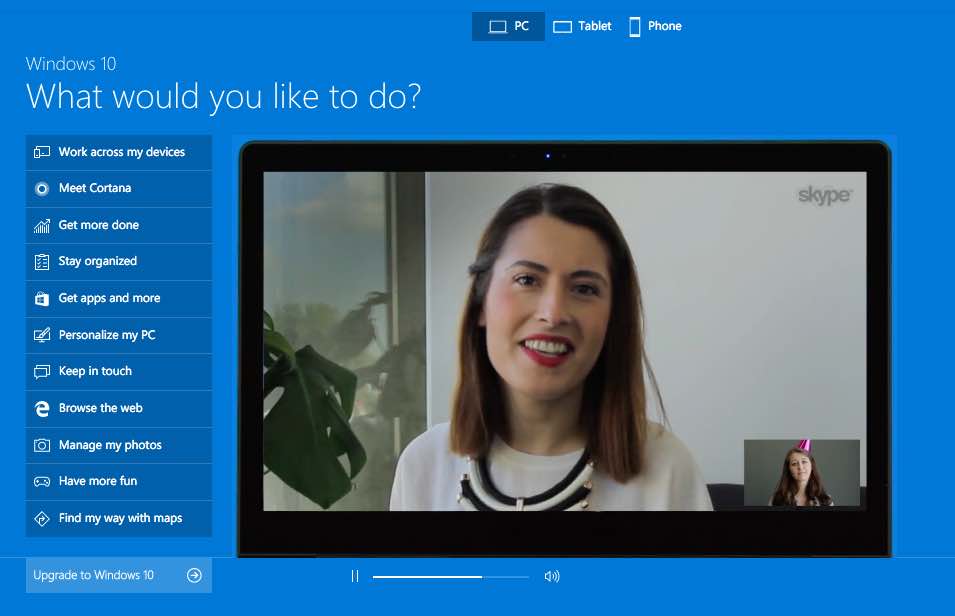
213How ToMicrosoft Launches An Online Windows 10 “Emulator” To Try The OS Without Installing
Short Bytes: Microsoft has unveiled a new section on a website and called it Windows 10 Emulator. However, it is more like...
-

 210Geek
210GeekDubai Issues Fatwa Against Using Neighbor’s Wifi without Permission
Dubai-Based Islamic scholars issue fatwa against WiFi theft after warning that falsely stealing it from your neighbor would not be proper Islamic conduct...
The Latest
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
 Malware
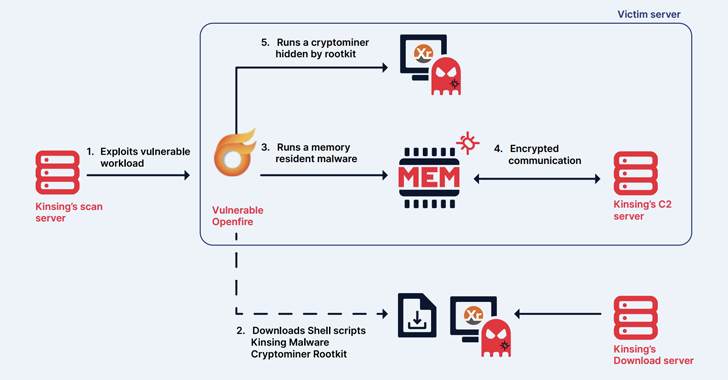
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
 Malware
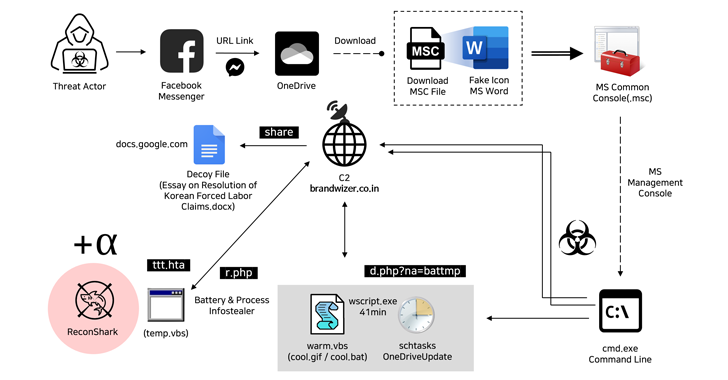
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Malware
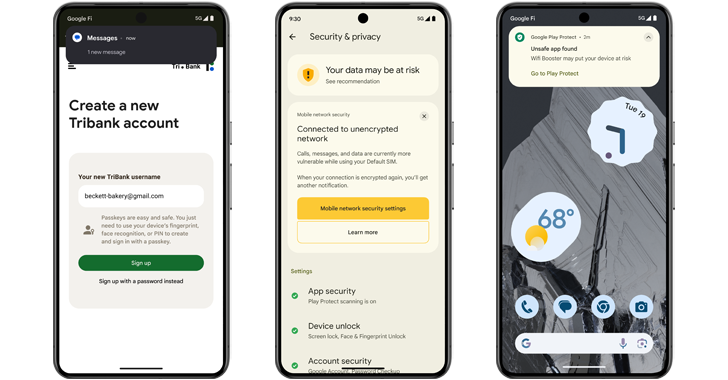
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions
-
 Vulnerabilities
Vulnerabilities(Cyber) Risk = Probability of Occurrence x Damage
-
 Malware
MalwareEbury Botnet Malware Compromises 400,000 Linux Servers Over Past 14 Years
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Vulnerabilities
VulnerabilitiesVMware Patches Severe Security Flaws in Workstation and Fusion Products
-
 Vulnerabilities
VulnerabilitiesNew Chrome Zero-Day Vulnerability CVE-2024-4761 Under Active Exploitation




