Featured News
-

 81News
81NewsEx-Mossad Agents Arrested for Hacking, Spying on Romanian Official
Two Israelis (ex-Mossad Agents) arrested by Romania for hacking and Spying on Anti-Corruption official Romania Insider reports that Romania is investigating the...
-

 220News
220NewsBritish Border Force Hacked Refugees’ Laptops and Phones for 3 Years
Reports indicate that immigration officials were given permission to hack into asylum seekers and refugees for the past three years. Rape and...
-

 90Vulnerabilities
90VulnerabilitiesApple just fixed an iMessage bug that researchers called easily exploitable
Your chat history on iMessage just went through a period when it was not altogether safe, but now, all wrongs have been...
-
 285Geek
285GeekHow To Upgrade To Ubuntu 16.04 LTS From Ubuntu 15.10
Short Bytes: The steps to upgrade to Ubuntu 16.04 Xenial Xerus from Ubuntu 15.10 are very simple. To make things even simpler,...
-
 194Data Security
194Data SecurityPetya Ransomware’s Encryption Defeated and Password Generator Released
An individual going by the twitter handle leostone was able to create an algorithm that can generate the password used to decrypt a Petya encrypted computer....
-

 194Data Security
194Data SecurityUK Teen That Sold DDoS Tools on the Dark Web Avoids Going to Prison
Grand Manser was the author of DDoS stressers like Dejabooter, Vexstresser, netspoof and Refinedstresser. Grant Manser, 20, of Kidderminster, a town near Birmingham,...
-
 103Malware
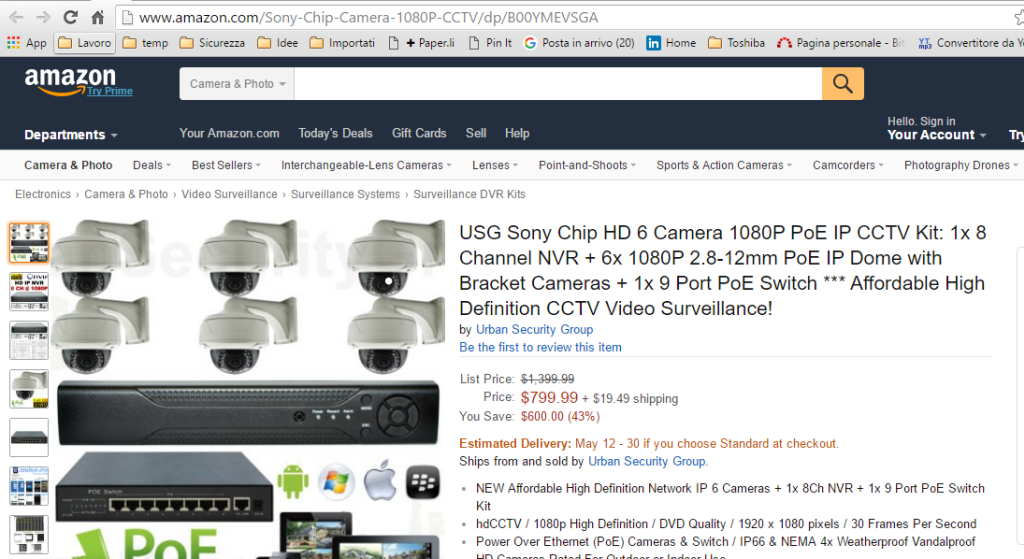
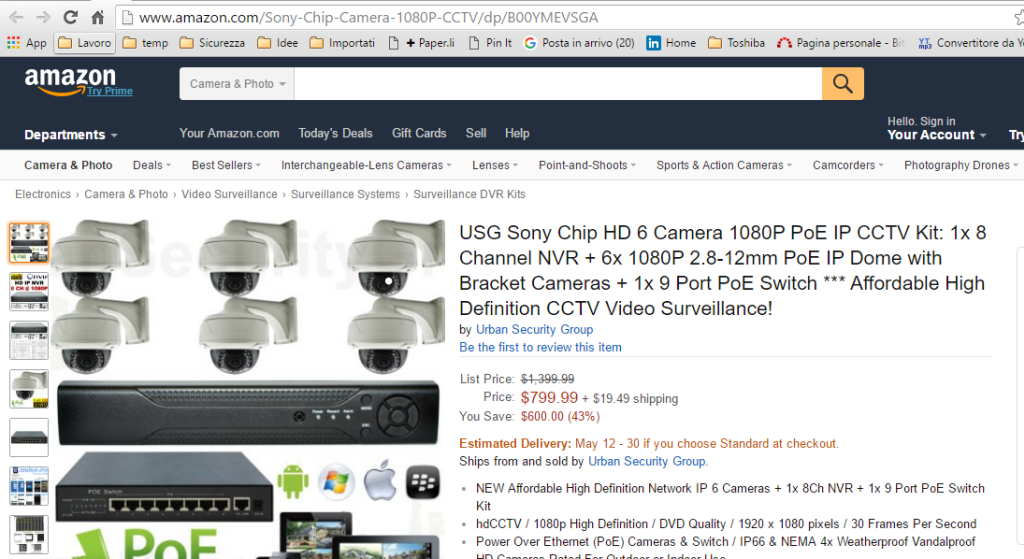
103MalwareBe careful products sold on Amazon are infected with malware
Beware, even things on Amazon come with embedded malware… this is the disconcerting discovery made by the expert Mark Olsen. The security expert Mike...
-

 291Data Security
291Data SecurityKickassTorrents Becomes First Torrent Site to Introduce Two-Factor Authentication
KickassTorrents add Two-Factor Authentication feature, vows to protect users’ account and privacy The Pirate Bay may be the most popular torrent site...
-
 273Geek
273GeekLinus Torvalds: “I’ll Spend Next 25 Years To Help Linux Beat Windows In Desktop War”
Short Bytes: While Linux and other open source technologies continue to rule the server and mobile markets, the desktop arena is still...
-

 169Hacked
169HackedBeware! More Than 135 Million Modems Are Vulnerable To DoS Attack
Short Bytes: A newly discovered flaw in the Arris modems has risked more than 135 million modems to DoS attacks. The flaw...
-

 255News
255NewsAnonymous Hack Italian Job Portals, Leak Trove of Data Against New Labour Laws
Anonymous has leaked personal details of CEOs, managers and other employees of hotshot companies in Italy to protest against the new labour...
-
 162Geek
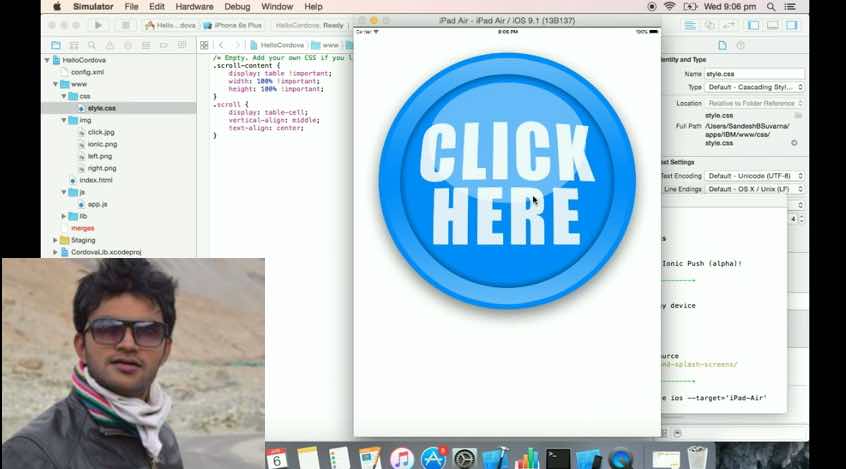
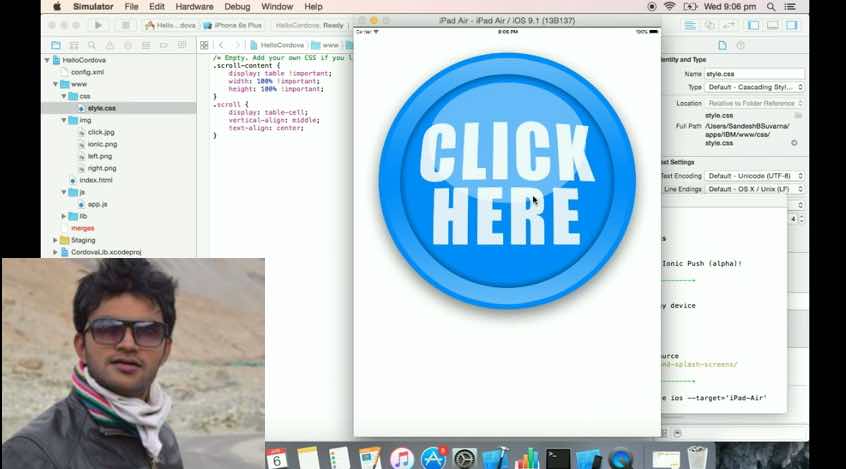
162GeekIndian Coder Shows How To Make IBM’s $1.4 million Randomized App In 4 Minutes
Short Bytes: An Indian techie, Sandesh Suvarna, has shown how to make IBM’s $1.4 million Randomizer app within 4 minutes. IBM made...
-

 365Cyber Crime
365Cyber CrimeLatest Facebook Phishing Scam Steals Login Data Using ‘Account Violation’ Policy
Latest Facebook Phishing Scam: ‘Account in Violation of Terms of Service’ You suddenly get a warning message seemingly from the Facebook Ads...
-

 88Tricks & How To's
88Tricks & How To'sAddmefast BOT – 2016
AddMeFast is a network that will help you grow your social presence by exchanging likes for Facebook / Youtube / Twitter etc....
-
 162Hack Tools
162Hack ToolsMorphVOX PRO Cracked – Anonymous voice changer
If you want to make sure that your true identity remains a secret even if you want to talk over the Internet,...
-
 75Data Security
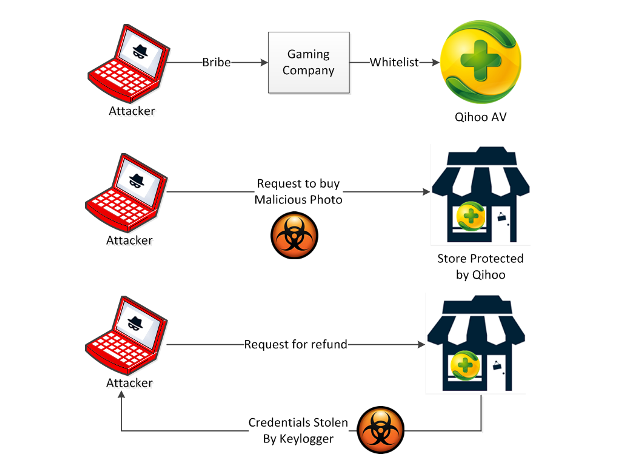
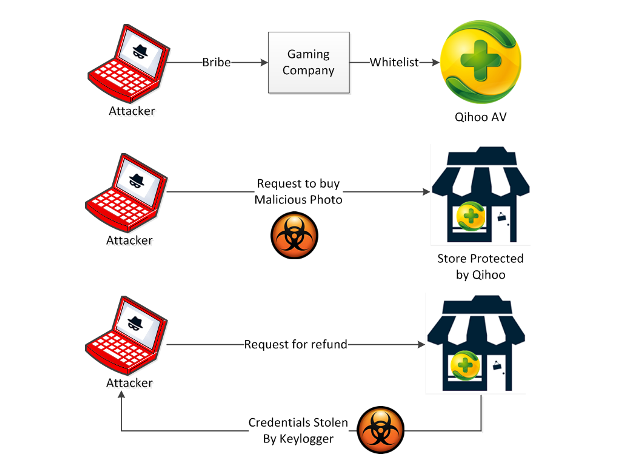
75Data SecurityQihoo 360: Just the Tip of the Whitelisted Malware Iceberg
The Check Point Mobile Threat Prevention team has long stressed how dangerous it can be to get apps from places other than...
-

 160Vulnerabilities
160VulnerabilitiesThe Open-source vulnerabilities database (OSVDB) shuts down permanently
The Open Sourced Vulnerability Database (OSVDB) shut down permanently in response to the lack of assistance from the industry. The Open Sourced Vulnerability...
-
 97Malware
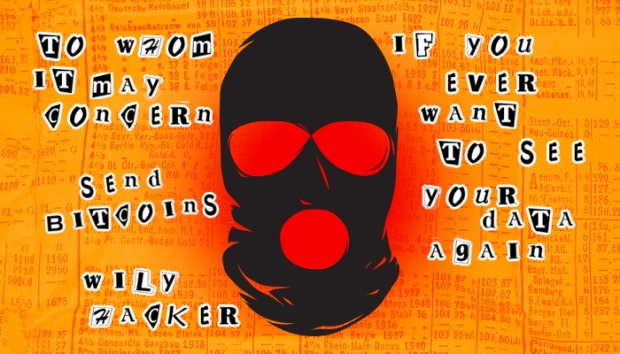
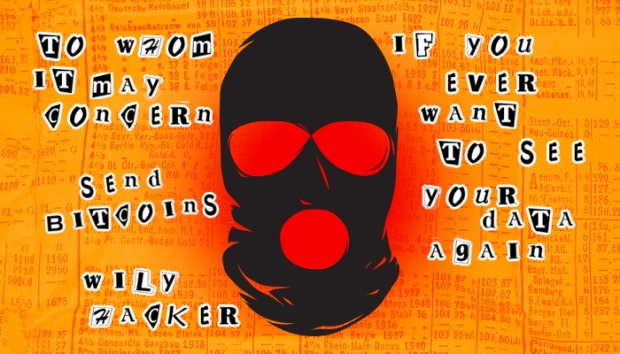
97MalwareOK, panic—newly evolved ransomware is bad news for everyone
Crypto-ransomware has turned every network intrusion into a potential payday. There’s something inherently world-changing about the latest round of crypto-ransomware that has been...
-

 120Data Security
120Data SecurityCryptoHost Decrypted: Locks files in a password protected RAR File
A new ransomware called CryptoHost was discovered by security researcher Jack that states that it encrypts your data and then demands a ransom of .33 bitcoins or...
-

 118Vulnerabilities
118VulnerabilitiesMore than 135 million ARRIS cable modems vulnerable to remote attacks
Attackers can exploit the flaws in the ARRIS SURFboard cable modems to remotely knock out the device, more than 135 million device...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




