Featured News
-
 199News
199News11 Tips to protect yourself against Ransomware
Ransomware can be very scary – the encrypted files can essentially be considered damaged beyond repair. But if you have properly prepared...
-

 279Geek
279GeekUbuntu Linux Is Coming To Windows 10 — Microsoft Partners With Canonical
Short Bytes: Microsoft and Canonical, Ubuntu Linux’s parent company, are partnering to allow you to use Ubuntu on Windows 10. The official...
-

 139Data Security
139Data SecurityTaiwan targeted with new cyberespionage back door Trojan
Backdoor.Dripion was custom developed, deployed in a highly targeted fashion, and used command and control servers disguised as antivirus company websites. In...
-

 180Incidents
180IncidentsHacked Websites Used in Black Hat SEO Campaign Redirecting Users to Adult Sites
Infected websites are hard to detect, only show up for users coming off search engines and for search bots. A new black hat...
-

 274Geek
274GeekBackdoor on Your Smartphone Already Exists — Explained
Though the FBI has already hacked into the iPhone of suspected San Bernardino shooter Syed Rizwan Farook, there’s something missing — Mr. Kokumai, President of...
-

 224Cyber Crime
224Cyber CrimeBitcoin Startup Quits Operation Due to Never-Ending DDoS Attacks
Bitcoin’s Secure Wallet Service Coinkite Inc. Closing Down due to never-ending DDoS Attacks and Governmental Nagging Bitcoin exchanges around the world face...
-

 301Geek
301GeekGoogle Maps reveal Batman’s cave and Bruce Wayne’s house in 360 degrees
You can now have in awesome inside look at Bruce Wayne’s amazing residence on Google Maps — Enjoy ✋? Batman fans have...
-

 335News
335NewsFBI Finally Hacks San Bernardino Gunman’s iPhone Proving Snowden Was Right
The FBI has hacked into the iPhone of Syed Rizwan Farook and it didn’t even require for Apple’s help The Federal Bureau of Investigation...
-

 165Data Security
165Data SecurityHacker Known As Weev Claims Responsibility for Anti Semitic Printer Blast
In-brief: Andrew Auernheimer, an online provocateur who uses the handle “Weev,” has taken credit for causing 30,000 Internet connected printers to spew...
-

 446Android Hacking
446Android HackingFaceniff – Hacking Facebook from your Android Device
Faceniff is probably the most easiest way to gain access to someone’s Facebook account and also works for twitter, YouTube, amazon, and...
-

 274Geek
274GeekHow To Become A ‘Smart’ Programmer That Gets Hired By Google And Facebook?
Short Bytes: Becoming a smart programmer that gets hired by tech giants isn’t an easy task. You must possess a mixture of...
-

 152Incidents
152IncidentsFBI hacks into terrorist’s iPhone without Apple
Although the government officially withdrew from its battle against Apple Monday, many observers sense the tech privacy war is just getting started. “This...
-
 70Malware
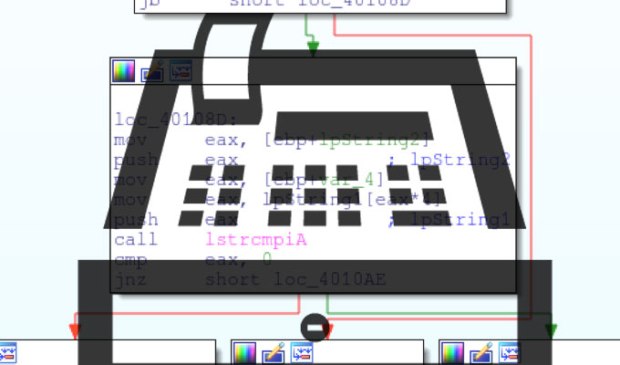
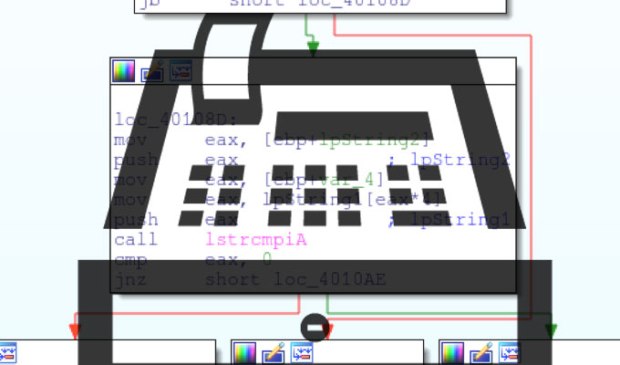
70MalwarePOS MALWARE TOOL ‘TREASUREHUNT’ TARGETS SMALL US-BASED BANKS, RETAILERS
As more US companies snuff out point of sale malware by deploying chip-and-PIN bankcard technology, attackers are rushing to exploit existing magnetic...
-
 287Hacked
287HackedFBI Hacks San Bernardino Gunman’s iPhone Without Apple’s Help
Short Bytes: The FBI has finally managed to break into the San Bernardino iPhone without Apple’s help. This development has also resulted in...
-

 161Vulnerabilities
161VulnerabilitiesPOPULAR SHOPPING CART APP PLUGS DOZENS OF XSS VULNERABILITIES
Popular open source shopping cart app Zen Cart is warning its users of dozens of cross-site scripting vulnerabilities found in its software....
-

 125Incidents
125Incidents1 million Gmail accounts victim of state-sponsored hacking
Google is improving its Gmail warning service to help protect the customers from state-sponsored hacking and surveillance activities. Google confirmed that one...
-

 257News
257NewsAnonymous Relaunches #OpCanary, Targets Canadian Mining Firm
BCGold Corp Becomes the Newest Victim of Anonymous’ Operation Against Multinationals A few years ago, the infamous hacker group Anonymous launched #OpCanary...
-
 161Privacy
161PrivacyFacebook fights back against creepy impersonating profiles
It's one of the creepiest things you can experience on Facebook. You stumble across the profile of "another" user who appears to...
-

 102Vulnerabilities
102VulnerabilitiesNuclear Plants in Germany Are Vulnerable to Terrorism Threats
According to a recent report, Germany nuclear plants are vulnerable to terrorists and there needs to be some serious dealing with this...
-
 200Data Security
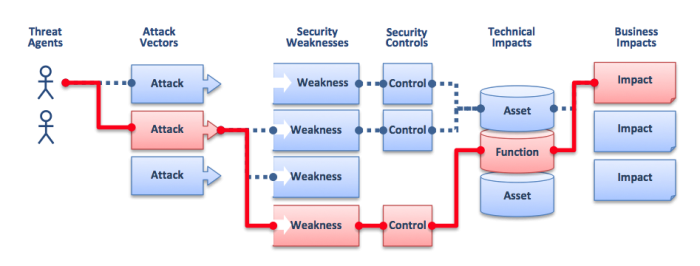
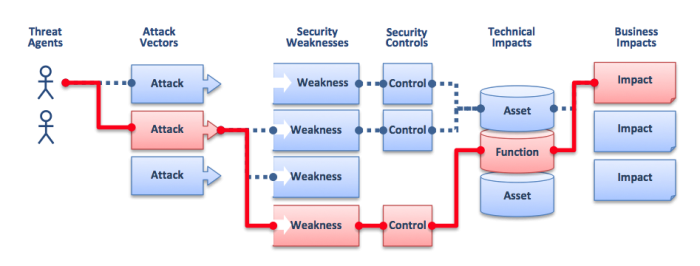
200Data SecurityWhat are web application security risks & attacks?
The websites and web applications are mission-critical business systems that must operate without security problems to process corporate confidential information. And to...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




