Featured News
-
 422Geek
422GeekVoCore: A Cheap And Coin-sized Linux Computer With Wi-Fi
Short Bytes: VoCore is an open hardware that runs OpenWRT Linux. This tiny computer comes with Wi-Fi, USB, 20+ GPIOs that will...
-
 73Incidents
73IncidentsTop Australian Classifieds Site Serves Malware In Malvertising Attack
Gumtree is a free classified advertising site and subsidiary of eBay particular popular in the UK, Australia, and South Africa. Gumtree is the number one local...
-

 229Hacked
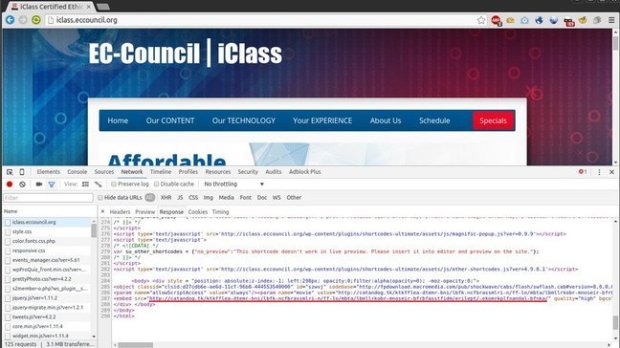
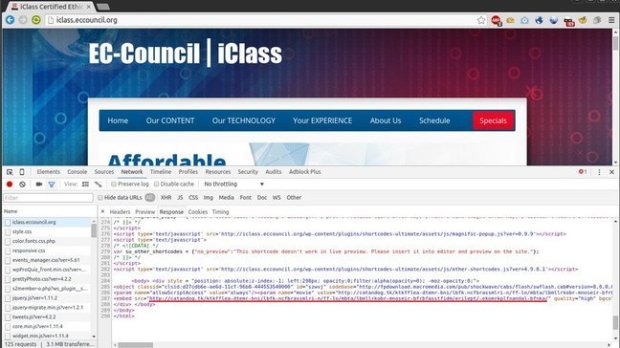
229HackedCrypto Ransomware Found On EC-Council Website That Runs A Certified Hacker Program
Short Bytes: A ransomware was found on the official website of EC-Council that runs Certified Ethical hacker program. After EC-Council did not...
-

 178Vulnerabilities
178VulnerabilitiesNode.js Package Manager Vulnerable to Malicious Worm Packages
Nothing is safe these days, not even Node’s npm.The Node.js Package Manager (or just npm) allows the author of a malicious package...
-

 273Vulnerabilities
273VulnerabilitiesRemotely Exploitable Flaw in Truecaller Leaves 100 Million Android Devices Vulnerable
Security researchers from the Cheetah Mobile Security Research Lab discovered a severe flaw in the call management application Truecaller. Recently, security researchers...
-
 189Geek
189GeekApple Watch saves life of 62-year-old man suffering heart attack
Apple Watch saved the life of a 62-year-old man in Canada who was suffering heart attack — Thanks to Apple Watch’s Health and...
-

 188Cyber Events
188Cyber EventsImpressed with Wikileaks, Brazilian Activists Launch BrasiLeaks
Brazil now has its own Wikileaks and they call it BrasiLeaks A group of Brazilian activists and privacy advocates have joined hands...
-

 308Lists
308ListsAmazing Google Chrome Tips And Tricks You Must Know
Short Bytes: Google Chrome is recognized as one of the best web browsers out there. Its simplicity and speed speak volumes for...
-

 321GPS & Radio
321GPS & RadioHow to send a spoofed SMS
SMS Spoofing occurs when a sender manipulates address information. Often it is done in order to impersonate a user that has roamed...
-

 336Lists
336ListsBest Android Phone 2016: Know The One Which Suits You The Best
Short Bytes: 2016 is going to see a flush of the Android phones and choosing the best Android phone among all will...
-

 299News
299NewsAnatomy of a Crypto-Ransomware attack
Ransomware is a type of malware that forces its victims to pay the ransom through certain online payment methods in order to...
-

 289Geek
289GeekWhat happens when Google Maps go wrong? Wrong House Gets Demolished
Demolition Company sabotages Wrong House, Employee Faults Google Maps A Texas-based demolition firm Billy “L Nabors Demolition” mistakenly damaged the wrong duplex...
-

 416News
416NewsVerizon Hacked Again, 1.5M Customers Data Available for Sale
San Francisco’s Verizon Enterprise solution’s computer security wing suffered an abrupt massive hack of 1.5 million customers’ records. Brian Krebs who is...
-

 362Geek
362GeekFacebook to be the biggest virtual graveyard by 2098
A recent survey suggests the social media giant Facebook will be the biggest virtual graveyard by the end of this century By...
-

 248Geek
248GeekCompany creates cover that turns your phone into vibrator
It’s not a joke, the product is expected to be launched this year In today’s world smartphones can do almost anything, but...
-
 212Data Security
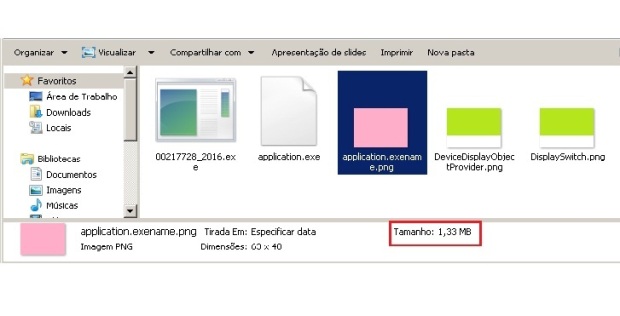
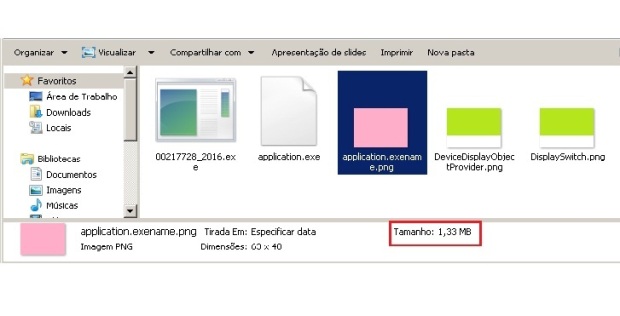
212Data SecurityPNG Embedded – Malicious payload hidden in a PNG file
One of the most complex tasks for the cybercriminals is to ensure their malicious code goes undetected by antivirus and achieves its...
-
 106Incidents
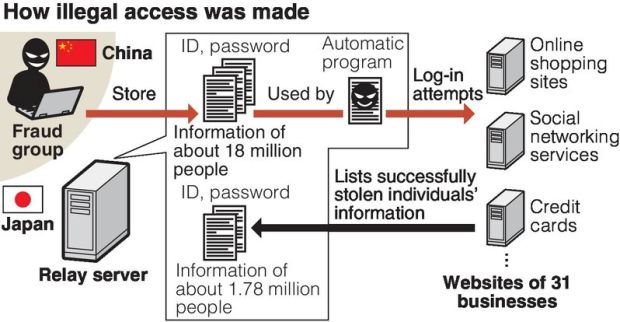
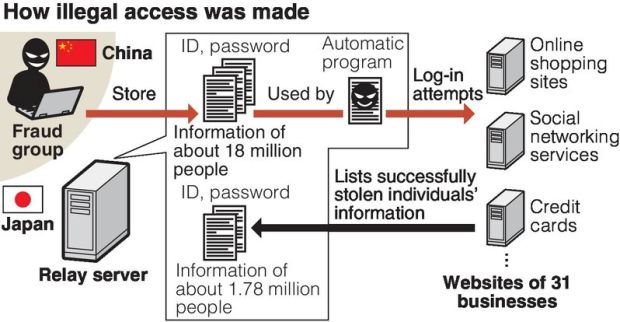
106Incidents18 million stolen IDs discovered on server / Criminals in China got illegal access
The IDs and passwords of about 18 million Internet users have been found on a computer server set up by a Tokyo...
-
 112Data Security
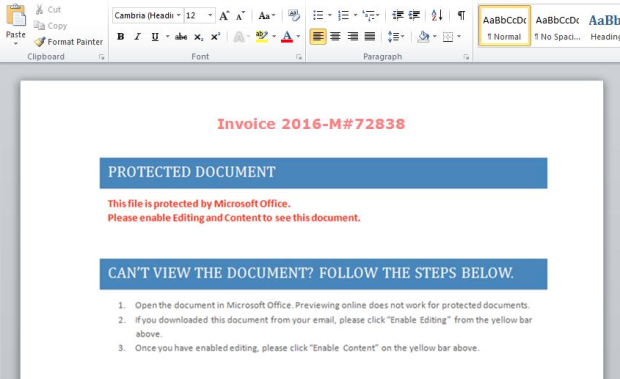
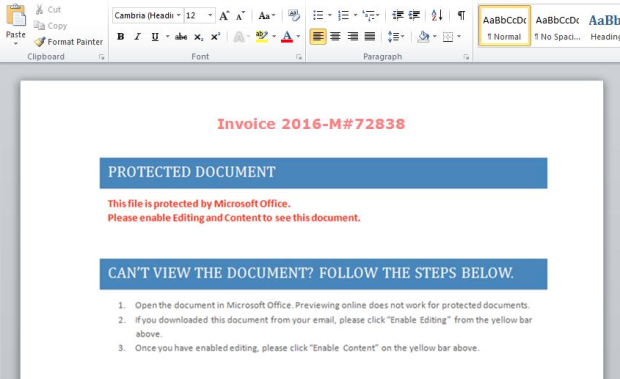
112Data Security“PowerWare,” New Ransomware Written in PowerShell, Targets Organizations via Microsoft Word
The Carbon Black Threat Research Team has recently discovered a new family of ransomware, which they dubbed “PowerWare,” that targets organizations via...
-
 149Incidents
149IncidentsEC Council Website Hacked and used to serve malicious code
Researchers at Fox-IT warn that the website of security certification provider EC Council has been compromised to host the malicious Angler Exploit...
-

 247Geek
247GeekSmartphone Lookalike Gun Coming This Year
A US based company is working on guns that look like smartphones — They may be easy to carry but they may...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




