Featured News
-

 160Malware
160MalwareThe evolution of Brazilian Malware
Brazilian malware continues to evolve day by day, making it increasingly sophisticated. If you want to know how the various malicious programs...
-

 89Malware
89MalwareMost prevalent Android ransomware in the West arrives in Japan
Android.Lockdroid ransomware expands to Asia by targeting Japan first. The malware poses as a system update and locks the device from use. One...
-

 168Data Security
168Data SecurityThe code to bypass Apple System Integrity Protection security mechanism fits in a Tweet
Security researchers from SentinelOne have discovered a security vulnerability affecting the Apple System Integrity Protection (SIP). Security researcher Pedro Vilaça from SentinelOne...
-

 266News
266NewsOpAfrica: Anonymous Hacks Kenyan Oil Refinery Website
After #OpCanary Anonymous Revives #OpAfrica with Targeting Kenya Petroleum Refineries Limited The online hacktivist Anonymous is seeking to wipe-out evils like child...
-

 147Data Security
147Data SecurityMarine Corps Cyberspace Warfare Group, the new hacker unit
The United States Marine Corps has launched on March 25th a new hacker support unit named Marine Corps Cyberspace Warfare Group. It is...
-

 217Geek
217GeekAbot — How To Make Your Own Digital Assistant With This Free And Open Source Tool
Short Bytes: Ever wished to create your own digital assistant that talks back to you and completes your day-to-day tasks? Now it’s...
-

 93Hacked
93HackedGoogle Was Also Ordered To Unlock A Phone, But Did Not Put Up A Fight
Short Bytes: After FBI hacked San Bernardino gunman’s iPhone without Apple’s help, most of us almost thought that Apple was the only company...
-

 112Malware
112MalwareThe KimcilWare Ransomware targets web sites running the Magento Platform
A new ransomware called KimcilWare has been discovered that appears to be targeting web sites using the Magento eCommerce solution. It is...
-
 200Hacked
200HackedThe TOR Project: “Our Developers Will Quit If Ordered To Backdoor TOR Browser”
Short Bytes: The TOR Project has expressed its commitment to researching and developing new ways to mitigate the threats of security failure....
-

 297Geek
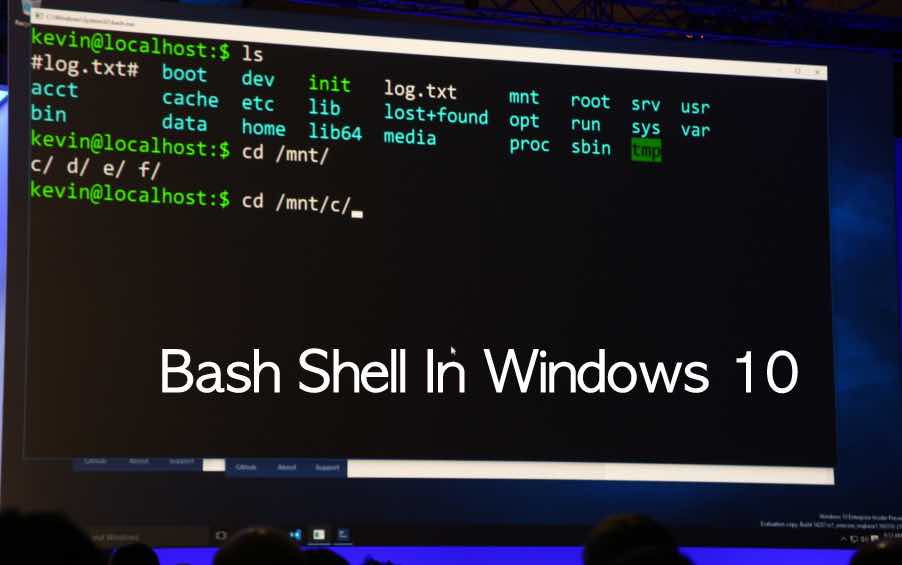
297GeekUbuntu Linux On Windows 10 — Here Are The First Pictures For You
Short Bytes: At the first day of Microsoft Build Developer Conference 2016, something amazing happened. Microsoft showed the world how Ubuntu on...
-

 114Vulnerabilities
114VulnerabilitiesPayPal flaw allowed hackers to send malicious emails
PayPal has just fixed a security vulnerability that could have been exploited to send malicious emails to users via its platform. Researchers at security...
-

 178Data Security
178Data SecurityHacker exposes thousands of insecure desktops that anyone can remotely view
VNC Roulette allows you to randomly view insecure desktops accessible over the internet. Recently, a new website has come up on the Internet,...
-

 201Cyber Crime
201Cyber CrimeScammers Distribute Malware to Drivers in Speeding Ticket Scam
Scammers Distribute Malware to Drivers in Pennsylvania using Accurate Speeding Data Scammers and their antics are simply unbelievable. This time, scammers have...
-
 211Geek
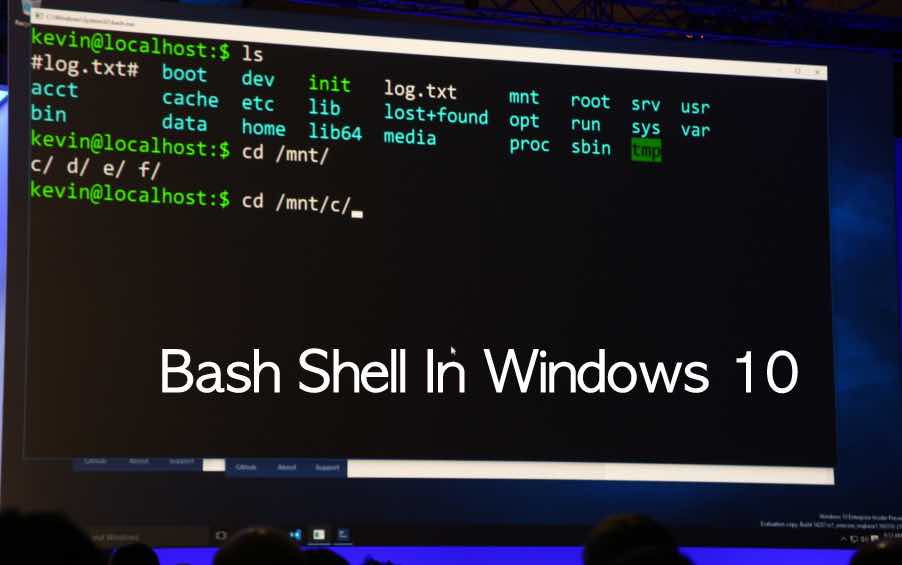
211GeekMicrosoft Officially Brings Your Favorite Bash Shell To Windows 10
Short Bytes: From the stage of Microsoft Developer Conference 2016, Microsoft once again showed off its love for developers. Redmond announced that GNU project’s...
-
 180Hacked
180HackedVNC Roulette: How One Hacker Is Exposing Thousands Of Hackable Computers
Short Bytes: A hacker has scanned the web for insecure systems using Virtual Network Computing (VNC) and collected an enormous amount of...
-

 74Malware
74MalwareMeet Remaiten – a Linux bot on steroids targeting routers and potentially other IoT devices
ESET researchers are actively monitoring malware that targets embedded systems such as routers, gateways and wireless access points. We call this new...
-

 156Data Security
156Data SecurityChinese Hacker Accused Of Stealing F-35 Fighter Lauded As Hero In China
Chinese state media is full of praise for the hacker accused of stealing a US F-35 Fighter Plane. A state-run media last Wednesday...
-

 187Hacked
187HackedFBI To Court: “No, We Won’t Reveal How We Hacked 1000+ TOR Users”
Short Bytes: FBI is pushing back against the order of a judge on revealing the technique it used to catch the defendant in...
-

 151Incidents
151IncidentsFollowing revelations on Paris attacks, US lawmakers target burner phones
Paris terrorists used burner phones and US lawmakers have proposed a bill that would force retailers to record the identity of the buyers...
-
 106Data Security
106Data SecurityFeds request Judge to review the order to reveal TOR Exploit Code
FBI is fighting back against the federal judge’s order to reveal the Tor Exploit and with DoJ filed a sealed motion requesting...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




