Featured News
-

 3.4KHacking Tutorials
3.4KHacking TutorialsHacking Facebook using Kali-Linux
Here we will discuss how to hack Facebook, as well as to develop understanding of how fake web pages are created, so...
-
 167Geek
167GeekApple’s Swift Programming Language Comes To Linux
Short Bytes: Apple has finally brought its Swift programming language to Linux. At this moment, this open source programming language supports Ubuntu...
-

 269Geek
269GeekGNOME 3.20 Delhi Released — 10 Best Features And How To Get It Guide
Short Bytes: GNOME 3.20 Delhi is finally released with many improvements in Web, Maps, Software, and other applications. Read more to know...
-

 65Data Security
65Data SecurityThe Art of the Maktub Locker Ransomware
A new ransomware has been discovered by security researcher Yonathan Klijnsma called Maktub Locker that shows the most attention to detail that I have...
-

 65Incidents
65IncidentsHackers stole records of 1.5 million customers of Verizon Enterprise
Hackers reportedly stole the records of 1.5 million customers of Verizon Enterprise which are offered for sale in the criminal underground. According...
-

 149Malware
149MalwarePetya Ransomware Uses DOS-Level Lock Screen, Prevents OS Boot Up
Petya uses old-school ransomware tactics, seems to be doing fine without employing powerful encryption. Malware experts from German security firm G DATA have...
-

 104Data Security
104Data SecurityBillions at risk of computer hack due to wireless mouse
Researchers say that wireless mouse could expose billions of computers to hacking Bastille Networks, a startup cyber security company that looks to better...
-

 180Incidents
180IncidentsSeven Iranian Hackers indicted by the US government for hacking
US authorities announced charges against seven Iranian hackers for attacking computer systems atUS authorities announced charges against seven Iranian hackers for attacking...
-

 306News
306NewsExpert Palestinian Hacker Indicted for Hacking Israeli Drones
The Jerusalem Post reports that the Palestinian Islamic Jihad (PIJ) movement’s main, expert hacker has been indicted by an Israeli judge. The...
-
 170Data Security
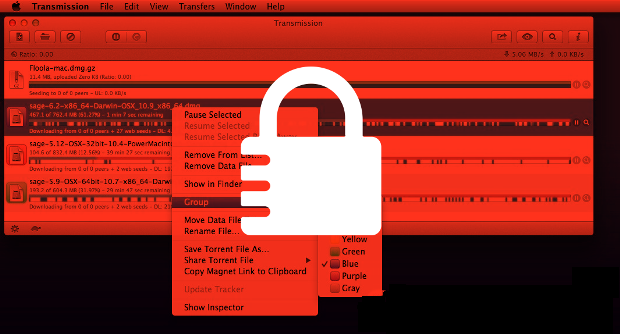
170Data SecurityThree US hospitals hit by ransomware
The IT systems of three US hospitals have been infected with ransomware, which encrypts vital files and demands money to unlock them....
-

 84Data Security
84Data SecurityMicrosoft chatbot is taught to swear on Twitter
A chatbot developed by Microsoft has gone rogue on Twitter, swearing and making racist remarks and inflammatory political statements. The experimental AI,...
-

 176Data Security
176Data SecurityNew self-protecting USB trojan able to avoid detection
A unique data-stealing trojan has been spotted on USB devices in the wild – and it is different from typical data-stealing malware. Each...
-

 293Data Security
293Data SecurityApple to release iOS 9.3 after fixing iMessages encryption vulnerability
Apple is a company that has maintained and reinforced the statement over and over again that it takes consumer privacy very seriously...
-

 381News
381NewsPakistan-Linked Hackers Conduct Third Cyber-Espionage Campaign Against India
Pakistan-Linked Hackers Successfully Conduct Third Cyber-Espionage Campaign Against Indian Military within a Month Operation C-Major is the name of the latest cyber-espionage...
-

 276Geek
276GeekMeet The Official Mascot Of Ubuntu 16.04 LTS Xenial Xerus
Short Bytes: Canonical has unveiled the official mascot of Ubuntu 16.04 Xenial Xerus. The next version of the open-source operating system is...
-

 193Hacked
193HackedUSB Thief — This Self-projecting USB Trojan Can Give You Nightmares
Short Bytes: Security researchers have identified a new malware named USB Thief that has the ability to steal data from air-gapped computers without leaving...
-
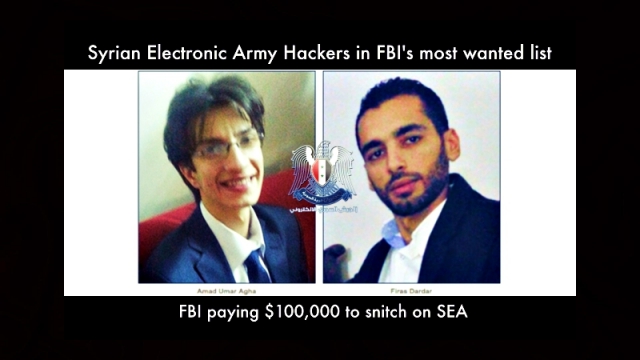
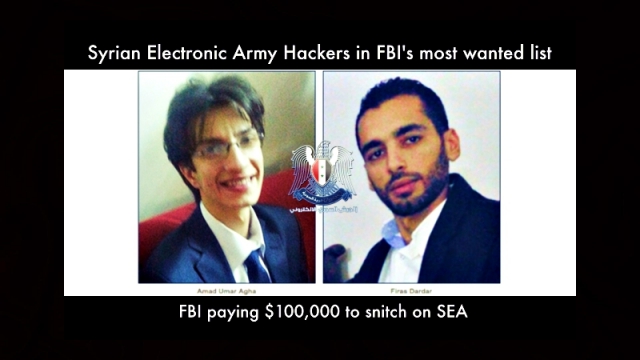 310Cyber Crime
310Cyber CrimeFBI Adds Syrian Electronic Army Hackers in Cyber’s Most Wanted List
FBI Adds three Syrian Electronic Army Members to its Cyber’s Most Wanted List and Charges Three for Hacking The three members of...
-

 376Malware
376MalwareESET discovers new USB‑based data stealing malware
ESET has discovered a new USB-based data stealer capable of stealthy attacks against air-gapped systems – it is also well-protected against detection...
-

 365Malware
365MalwareNew self‑protecting USB trojan able to avoid detection
A unique data-stealing trojan has been spotted on USB devices in the wild – and it is different from typical data-stealing malware,...
-
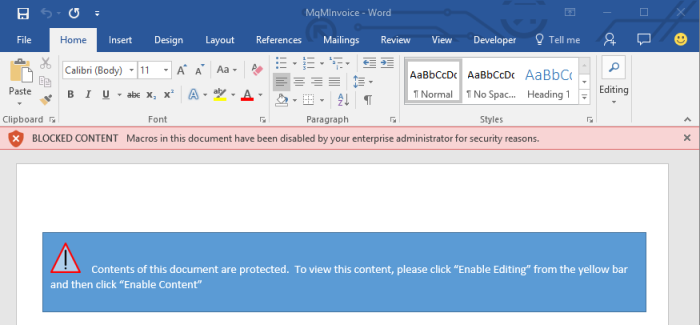
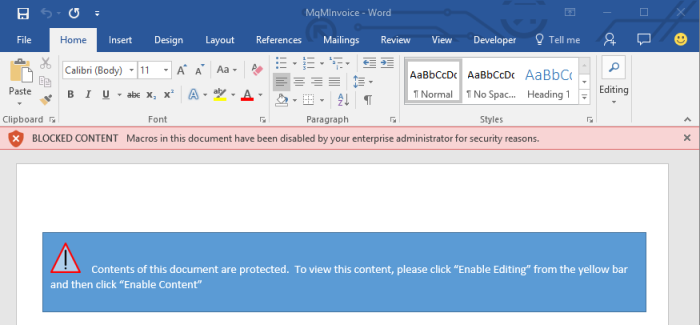 104Data Security
104Data SecurityMicrosoft Adds New Feature in Office 2016 That Can Block Macro Malware
How-to guide also included, showing sysadmins how to protect their enterprises from malicious macro malware. Microsoft is finally addressing the elephant in the...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




