Featured News
-

 343Geek
343GeekApple defiant in San Bernardino Shooting Case; says no to backdoor access
Judge Issues Order to Apple to Unlock iPhone Vital in the San Bernardino Shooting Case — Apple refuses to follow orders The...
-

 121Data Security
121Data SecuritySouthampton University Creates 5D Storage Disc That Can Store 360TB Data
The mindblowing invention will revolutionise the way we store data Last year the researchers came up with a processor capable of transmitting...
-

 176How To
176How ToHow To Access Your Chrome Passwords Remotely From Any Browser?
Short Bytes: Google has introduced a new online feature where a user can sync its passwords to Google and access Chrome passwords...
-

 317Cyber Crime
317Cyber CrimeCybercriminals Hack Hospital PCs Demand Whopping 9000 BTC Ransom
Ransomware Infects Hollywood HealthCare Facility Computers – Attackers Demand $3.6M Computers are an integral part of almost every field and industry nowadays...
-

 272Data Security
272Data SecurityThe NSA’s SKYNET program may be killing thousands of innocent people
“Ridiculously optimistic” machine learning algorithm is “completely bullshit,” says expert. In 2014, the former director of both the CIA and NSA proclaimed that...
-

 233Vulnerabilities
233VulnerabilitiesHow to bypass this LG smartphone’s fingerprint security in just 30 seconds
A troubling vulnerability has been uncovered that may make you think twice about ever even temporarily allowing a friend, partner or acquaintance...
-

 182Malware
182MalwareDridex: Financial Trojan aggressively spread in millions of spam emails each day
Built to harvest the banking credentials of victims, the virulent Dridex is now one of the most dangerous pieces of financial malware...
-
 146Vulnerabilities
146VulnerabilitiesExtremely severe bug leaves dizzying number of software and devices vulnerable
Since 2008, vulnerability has left apps and hardware open to remote hijacking. Researchers have discovered a potentially catastrophic flaw in one of the...
-

 102Malware
102MalwareBackdoor in MVPower DVR Firmware Sends CCTV Stills to an Email Address in China
IoT security experts from Pen Test Partners have confirmed the presence of a backdoor in the firmware used by some DVR devices...
-

 405Lists
405Lists10 Best Free VPN Services Of 2016: Which One Shall I Choose?
Short Bytes: Due to restrictions and localization of different internet services and sites like YouTube, Netflix, live sports etc., internet users like...
-
 227Data Security
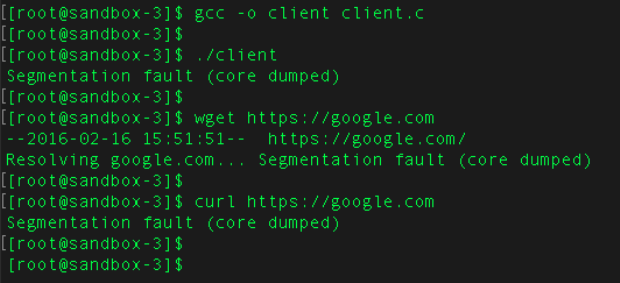
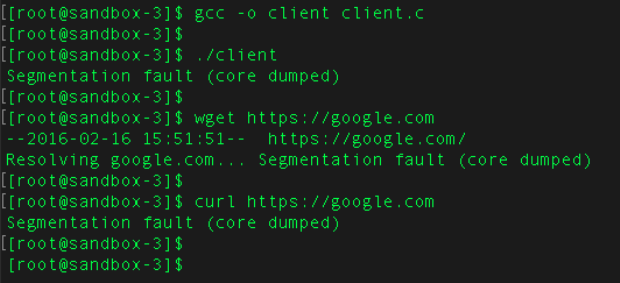
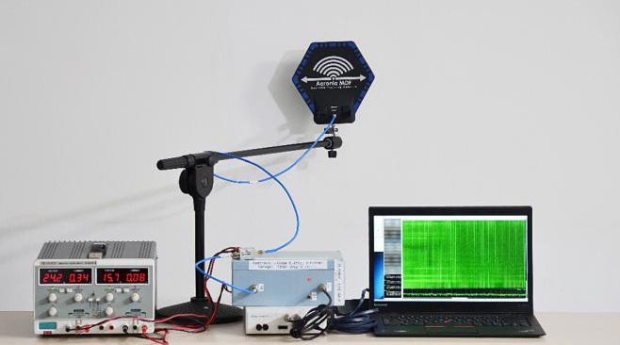
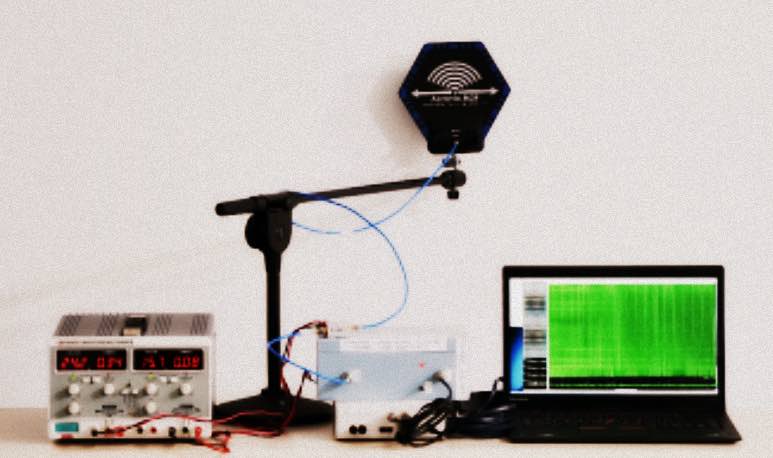
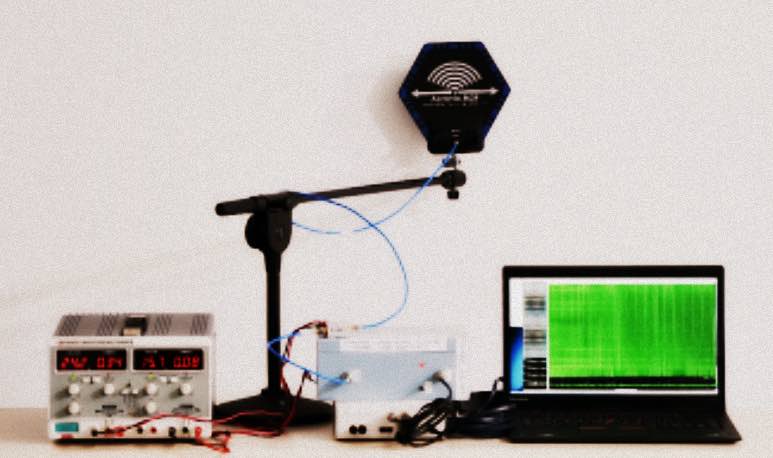
227Data SecurityHow White Hat Hackers Stole Crypto Keys from an Offline Laptop in Another Room
Last year, it was revealed that hackers can steal data from any computer via heat and how some technologies can hack into...
-

 262News
262NewsAnonymous’ #OpAfrica Claims 64,000 Workers Data of Tanzanian Telecom Firm
The online hacktivist Anonymous has breached into the server of a Tanzanian Telecom Firm and leaked personal data of about 64,000 employees. OpAfrica is...
-

 190News
190NewsHackers To Demonstrate How To Hack An Offline Laptop
White Hat Hackers show us how to Steal Crypto Keys from a Laptop in Another Room Sans Internet Connection Last year, it...
-

 374Hacked
374HackedEpic Troll: 82-Year-Old Great Granny Is Now An Internet Pirate
Short Bytes: Sheila Drew, who has lived her life for more than eight decades, has now been accused of being an Internet...
-
 119Hacked
119HackedHow White Hat Hackers Hacked An Offline Laptop In Another Room Within Seconds
Short Bytes: The researchers from Tel Aviv University and Technion have found a way to steal encryption keys from “safe” air-gapped machines. The attack...
-
 219News
219NewsHackers & Cybercrime: How To Avoid Becoming A Victim
Even though the annual cost of cybercrime to global business is a whopping £200bn, some members of staff still aren’t taking online...
-

 190News
190NewsBe careful of what you say in front our Smart TV, warns Samsung
Beware of Samsung Smart TVs—Voice Recognition Could be Recording and Sharing your Private Conversations Digital age has brought along countless blessings and...
-

 82Malware
82MalwareBiggest fears of EMEA companies? Malware ranks first
The most pressing IT security issue that companies in the EMEA region face is malware infection, reports Ondrej Kubovič. Enterprises are very...
-
 241Data Security
241Data SecurityGCHQ is allowed to hack into computers and smartphones
GCHQ is legally allowed to hack into computers, tablets and smartphones owned by the public, a tribunal has ruled, after a legal...
-

 114Data Security
114Data SecuritySkimmers Hijack ATM Network Cables
If you have ever walked up to an ATM to withdraw cash only to decide against it after noticing a telephone or...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




