Featured News
-

 186Geek
186GeekEyebrows Raised as The Pirate Bay Becomes Largest Video Streaming Portal
The brand new Torrents-Time browser plugin has helped The Pirate Bay take the industry of online video portal by storm as it...
-
 282News
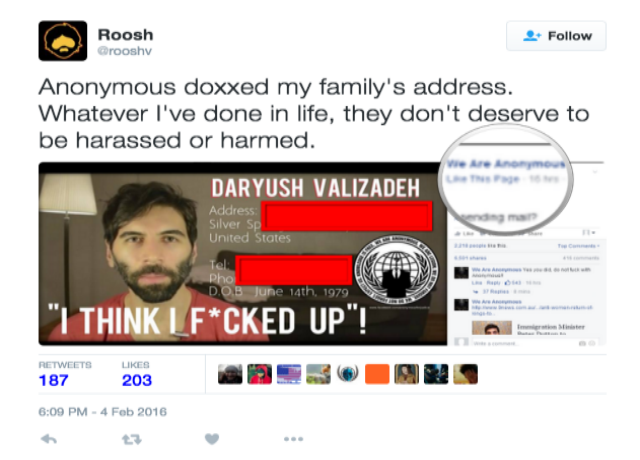
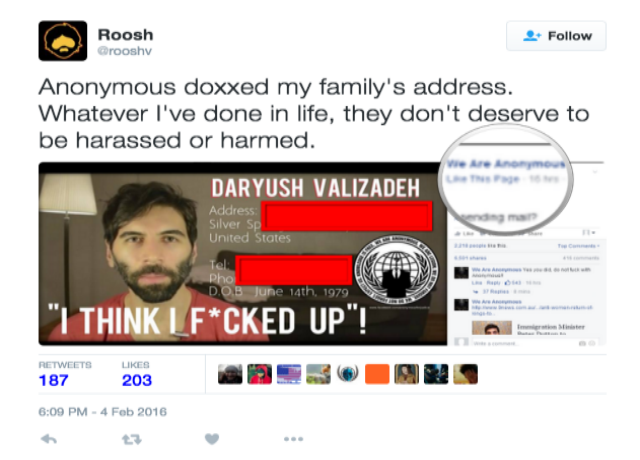
282NewsAnonymous Doxes and Forces Pro-Rape Pick-up Artist To Cancel His Meetings
Pro-rape and controversy child Roosh blames Hacktivists for hacking his family’s address and spreading hoax news The controversial ‘neo-masculinist” Roosh has claimed...
-
 194Hacked
194HackedWelcome To The Malware Museum: An Epic Online Collection Of Old-school Viruses
Short Bytes: Do you remember computer viruses from 1990’s that left you with no option but to reinstall your operating system? Well,...
-

 182Data Security
182Data SecurityBrazilian companies receive more than 40,000 spam emails in infostealer campaign
Spam campaign targets Portuguese-speaking firms in Brazil and other regions to deliver malware and steal sensitive data. Symantec has observed an ongoing...
-

 212Data Security
212Data SecurityJulian Assange’s 3.5-Year Detainment in Embassy Ruled Unlawful
THREE AND A half years after he sought temporary asylum in the Ecuadorean embassy in London only to find himself a captive...
-

 294Cyber Crime
294Cyber Crime7 Online Activities That Can Get You Arrested
Here are 7 activities that users should avoid doing on the Internet The Internet is a wonderland. It is a place where...
-
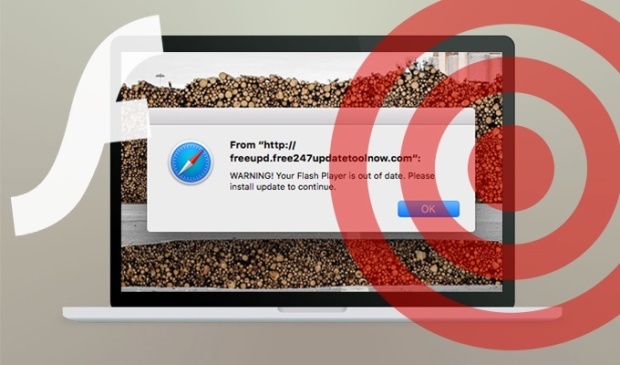
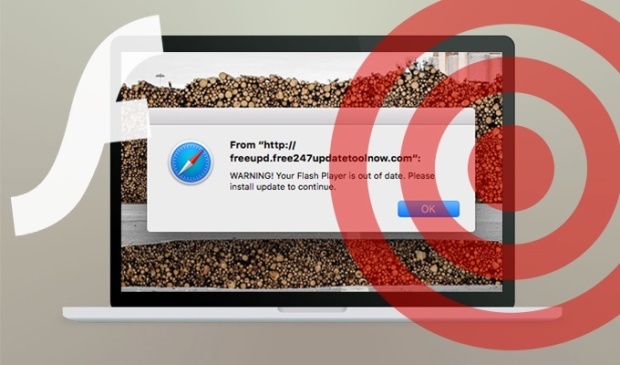 98Vulnerabilities
98VulnerabilitiesResearchers spotted a new OS X scareware campaign
Experts at the SANS Technology Institute spotted an OS X scareware campaign that leverages fake Adobe Flash Player installers. Johannes Ullrich, security...
-
 172Malware
172MalwareRoll up, roll up to the Malware Museum! Run classic DOS viruses in your web browser
Relive simpler times for some Friday fun. The Internet Archive has opened a new collection dubbed the Malware Museum that lets you run...
-

 230Incidents
230IncidentsAvast SafeZone Browser Lets Attackers Access Your Filesystem
Another antivirus maker decides to mess around with Chromium default security features and gets it totally wrong. Just two days after Comodo’s...
-
 237Geek
237GeekTwitter suspends 125,000 accounts for promoting terrorist acts
Twitter announced that since mid-2015 it has suspended over 125,000 accounts involved in promoting violent content. The social media giant Twitter has claimed...
-

 252Geek
252GeekChrome to Alert Users on Fake Play, Close, Download Buttons and Misleading Ads
Bad news for those website owners who trick their readers/users into clicking on fake ads and tricky downloads — Google Chrome is...
-

 191Cyber Events
191Cyber EventsTPP deal signed in New Zealand, a threat to Internet Freedom
The TPP deal is coming and things won’t be easy on the Internet The Trans-Pacific Partnership trade deal was signed by New...
-

 170News
170NewsUniversity of Central Florida Hacked, 63,000+ Social Security Numbers Stolen
Another day another data breach but this one has affected even those students who were part of the university in the 1980s....
-

 177Data Security
177Data SecurityAustralian NSW Government Department of Resources and Energy under attack. Is it Chinese cyber espionage?
According to the NSW Government Department of Resources and Energy Chinese hackers have launched a malware-based attack on its network in December....
-

 175Malware
175MalwareMystery hacker pwns Dridex Trojan botnet… to serve antivirus installer
Part of the distribution channel of the Dridex banking Trojan botnet may have been hacked, with malicious links replaced by installers for...
-

 167Vulnerabilities
167VulnerabilitiesDo you have a Netgear ProSAFE NMS300? Here you are the exploit to hack it
A security researcher has released the exploit code for two serious vulnerabilities in the Netgear ProSAFE NMS300 network management system. Do you have...
-

 334Hacked
334Hacked9 Out Of 10 Windows Security Flaws Could Be Avoided By Just Removing Admin Rights
Short Bytes: The security firm Avecto has just released its security report on Windows operating system. The report outlines an important result...
-

 238Incidents
238IncidentsLogin duplication allows 20m Alibaba accounts to be attacked
The reuse of login details on Alibaba’s Taobao has allowed an attack on 5 percent of the accounts on Alibaba’s Chinese retail...
-
 204Data Security
204Data SecurityDell Adds Boot Scanner to Protect Users Against Bootkit Malware
Dell and Cylance join the fight against bootkits. Dell has announced a partnership with Cylance, which will add a new security layer for...
-
 310News
310NewsNASA Denies AnonSec’s Claim of Hacking Global Hawk Drone
NASA has denied that its drone was hijacked by any hacking group — Earlier a group on Facebook claimed to have hijacked...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




