Featured News
-

 237Incidents
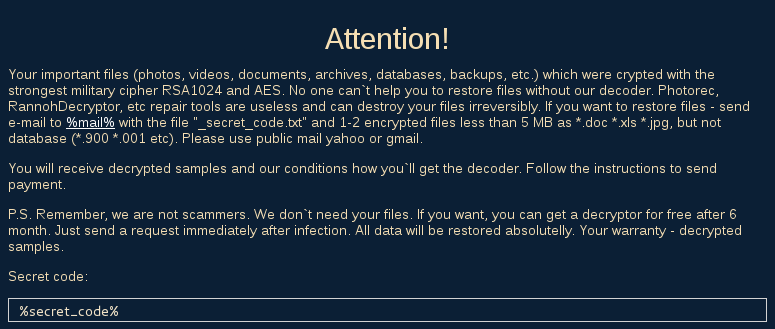
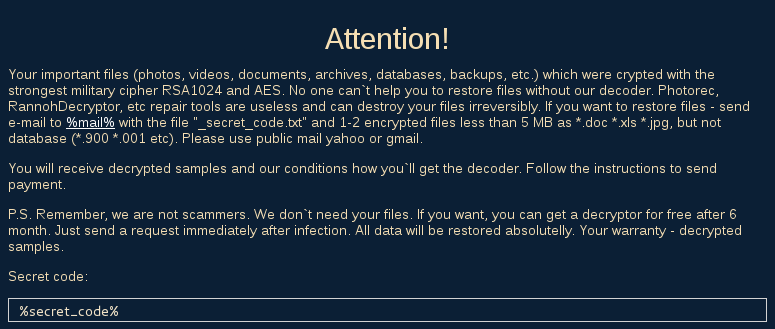
237IncidentsEDA2 Open-Source Ransomware Code Used in Real-Life Attacks
Another educational open-source ransomware project goes bad. Cyber-crooks have used the open-source code of the EDA2 ransomware to create the Magic ransomware...
-

 201News
201NewsAnonymous Shut Down Japanese Airport Website Against Dolphin Slaughter
Anonymous hackers shut down Japan’s Narita International Airport website against Dolphin slaughter. The online hacktivist Anonymous conducted a powerful DDoS attack on the...
-

 80Cyber Crime
80Cyber CrimeSkype finally hides your IP address, to protect against vengeful gamers
For too long streaming video gamers have suffered denial-of-service attacks and raids from police SWAT teams, often assisted by Skype leaking private...
-

 123Cyber Crime
123Cyber CrimeFBI Randomly Used Malware on TORMail Users While Busting Pedophiles
Report Hints on Possible Invading of TORMail users Privacy for Capturing Global Child Porn Gang by the FBI In 2013, the Federal...
-
 189Hacked
189HackedJohn McAfee: “Obama Administration Doesn’t Know The Meaning Of Privacy”
Short Bytes: The maker of McAfee antivirus and privacy advocate John McAfee is again in the headlines. In his latest op-ed, he stresses...
-

 452Social Media Hacking
452Social Media Hacking5 Tools to protect your Social Media accounts
You should have these five tools to protect your Facebook, Twitter, LinkedIn and other social media accounts Social media has taken the...
-

 266News
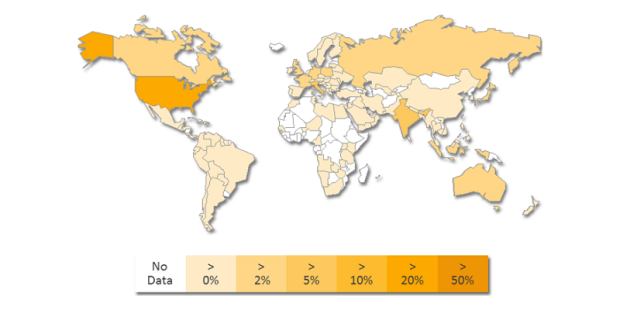
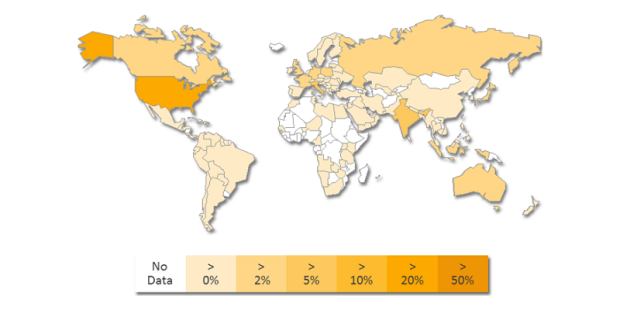
266NewsAzerbaijani Hackers Deface NATO-Armenia, Embassy Websites in 40 Countries
Azerbaijani Hackers have hacked NATO-Armenia and embassy websites in 40 countries giving a powerful reply to the Armenian hackers. The cyber war between...
-

 168Geek
168Geek“New Facebook Message” Email Not Only Drops Malware But Phish You
If you receive an email claiming to have a ”new message” from Facebook just delete it because the attachment contains Nivdort malware...
-

 191News
191NewsAnonymous Declares Michigan Governor Guilty Over Flint Water Crisis
The infamous hacktivists collective Anonymous has declared Michigan governor Rick Snyder guilty for the ongoing Flint water contamination crisis. On Wednesday, a...
-

 230Cyber Events
230Cyber Events8 Most Popular and Best Hacking Tools
The internet has as many downsides as well as upsides but it’s the lack of knowledge about dangers on users’ behalf makes...
-
 187Malware
187MalwareLeChiffre, Ransomware Ran Manually
LeChiffre is yet another ransomware that recently has been observed to cause some major damage (in Mumbai – read more here). Not...
-
 102Incidents
102IncidentsWeb Reconnaissance Attack Infects 3,500 Websites, Possibly WordPress
Attackers are adding unauthorized code at the top of infected websites, over 3,500 8sites already infected. Alarms are ringing in Symantec’s offices,...
-

 225Malware
225MalwareTrojan.DNSChanger circumvents Powershell restrictions
In recent variants of the infamous DNS-changer adware we have found that the coders use a particularly interesting method to bypass the...
-

 84Data Security
84Data SecurityTorMail hack, FBI surgical operation, or dragnet surveillance?
In 2013 the FBI agents seized TorMail, now new information are emerging on the operations. Someone believes it was a surgical ops...
-

 275Geek
275GeekThis mystery house is blamed for lost phones in Atlanta City
The people come to the house and demand their lost phone back from this couple probably because of some error in phone-finding apps Christina...
-
 344News
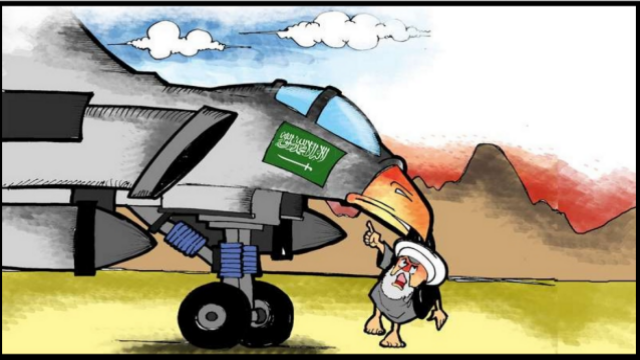
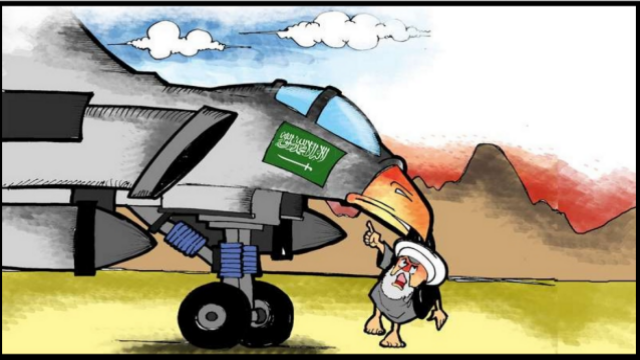
344NewsOfficial Web Portal of Supreme Leader of Iran Ruhollah Khomeini Hacked
The official web portal of founder and first supreme leader of Iran Ruhollah Khomeini has been hacked by Saudi hackers While tensions...
-

 238Lists
238ListsBest Windows 10 Cortana Features and Commands
ShortBytes: FossBytes brings you the list of the best Cortana features and commands available for the Windows users. You can search for...
-

 203Incidents
203IncidentsChinese Group Trying to Exploit Old Fortinet SSH Backdoor
Scans for Fortinet devices have intensified. An unknown group has been scanning the Internet for old Fortinet equipment that includes a secret SSH...
-

 65Cyber Crime
65Cyber CrimeIrish lottery and ticket terminals knocked offline by DDoS attack
It should have been a great week for the Irish Lottery, with the largest jackpot (12 million euros) for 18 months up...
-
 110Malware
110MalwareDon’t open that Facebook email attachment — it could be malware
Two weeks ago, the Comodo Threat Research Lab discovered a malware campaign aimed at businesses and consumers using the WhatsApp mobile messaging...
The Latest
-
 Cyber Attack
Cyber AttackCheck Point Warns of Zero-Day Attacks on its VPN Gateway Products
-
 Data Breach
Data BreachNew Research Warns About Weak Offboarding Management and Insider Risks
-
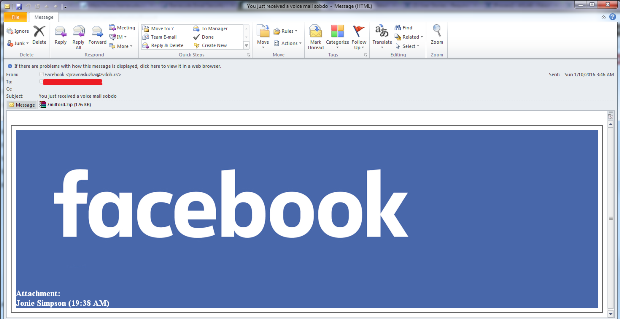
 Vulnerabilities
VulnerabilitiesExperts Find Flaw in Replicate AI Service Exposing Customers’ Models and Data
-
 Cyber Attack
Cyber AttackHackers Created Rogue VMs to Evade Detection in Recent MITRE Cyber Attack
-
 Malware
MalwareBeware: These Fake Antivirus Sites Spreading Android and Windows Malware
-
 Vulnerabilities
VulnerabilitiesUpdate Chrome Browser Now: 4th Zero-Day Exploit Discovered in May 2024
-
 Malware
MalwareJAVS Courtroom Recording Software Backdoored – Deploys RustDoor Malware
-
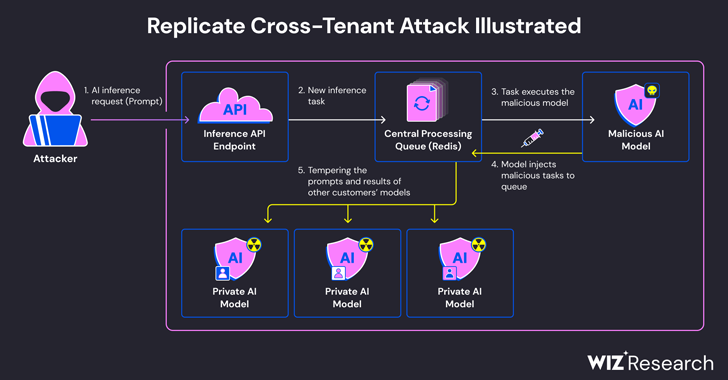
 Malware
MalwareStealthy BLOODALCHEMY Malware Targeting ASEAN Government Networks
-
 Vulnerabilities
VulnerabilitiesCISA Warns of Actively Exploited Apache Flink Security Vulnerability
-
 Malware
MalwareNew Frontiers, Old Tactics: Chinese Espionage Group Targets Africa & Caribbean Govts
-
 Malware
MalwareInside Operation Diplomatic Specter: Chinese APT Group’s Stealthy Tactics Exposed
-
 Data Breach
Data BreachAre Your SaaS Backups as Secure as Your Production Data?
-
 Vulnerabilities
VulnerabilitiesIvanti Patches Critical Remote Code Execution Flaws in Endpoint Manager
-
 Malware
MalwareResearchers Warn of Chinese-Aligned Hackers Targeting South China Sea Countries
-
 Vulnerabilities
VulnerabilitiesRockwell Advises Disconnecting Internet-Facing ICS Devices Amid Cyber Threats
-
 Malware
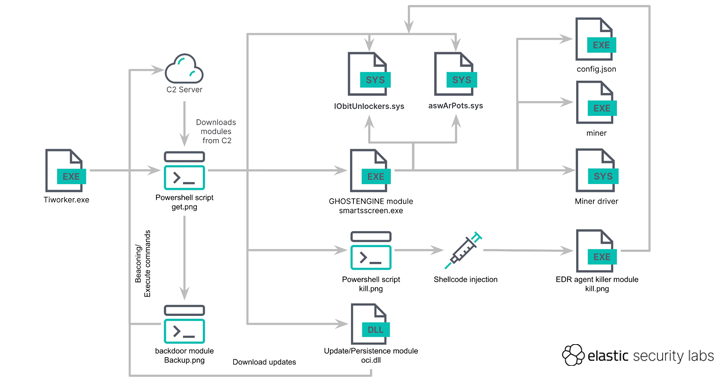
MalwareGHOSTENGINE Exploits Vulnerable Drivers to Disable EDRs in Cryptojacking Attack
-
 Data Breach
Data BreachMS Exchange Server Flaws Exploited to Deploy Keylogger in Targeted Attacks
-
 Vulnerabilities
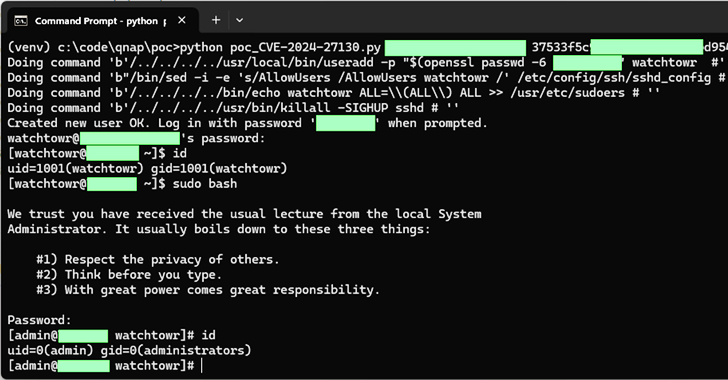
VulnerabilitiesQNAP Patches New Flaws in QTS and QuTS hero Impacting NAS Appliances
-
 Vulnerabilities
VulnerabilitiesCritical Veeam Backup Enterprise Manager Flaw Allows Authentication Bypass
-
 Vulnerabilities
VulnerabilitiesCritical GitHub Enterprise Server Flaw Allows Authentication Bypass




