Featured News
-

 225Geek
225GeekWindows 10 usage stats show user privacy is a very real concern
Microsoft has released stats regarding Windows 10 usage worldwide which proves the point that user privacy is a very real concern Although,...
-
 112Geek
112GeekOne Javascript Tip A Day, Keeps Code Bugs Away
Short Bytes: In this article, I bring to you a new project called Javascript Tips that promises to deliver you one Javascript tip per...
-

 138Privacy
138PrivacyShould I stay or should I go … to Windows 10?
It has been almost half a year since Microsoft released Windows 10, and the decision whether or not to migrate computers to...
-

 101Data Security
101Data SecurityRemote Exploitation of Microsoft Office DLL Hijacking (MS15-132) via Browsers
A number of weeks back, security researcher Parvez Anwar posted a number of DLL hijacking vulnerabilities within Microsoft Office on Twitter [1]....
-

 293Opinion
293OpinionCES 2016: Day 1 – surviving the swarm
As ever, ESET is once again in attendance at CES in Las Vegas, offering you expert insight into all the security aspects...
-

 183Vulnerabilities
183VulnerabilitiesDrupal Update Process Flawed by Multiple Bugs, Attackers Can Take Over Sites
IOActive’s Fernando Arnaboldi has sounded the alarm on three major flaws in Drupal’s update process that may allow attackers to poison Drupal...
-

 96Malware
96MalwareLet’s Encrypt Now Being Abused By Malvertisers
Encrypting all HTTP traffic has long been considered a key security goal, but there have been two key obstacles to this. First,...
-
 324Hacked
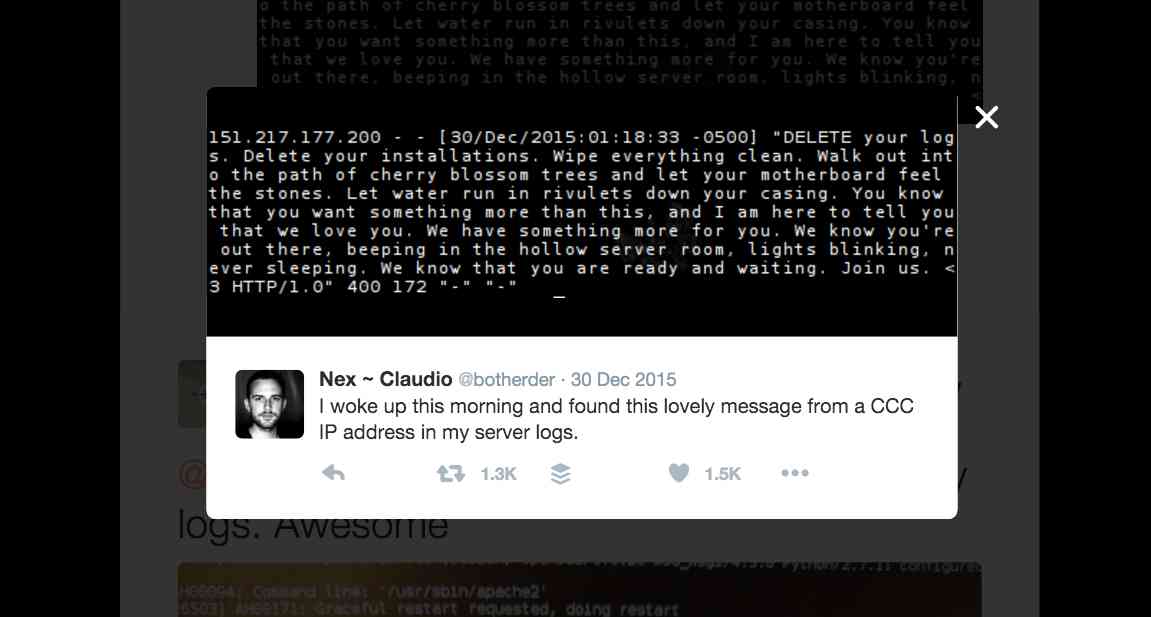
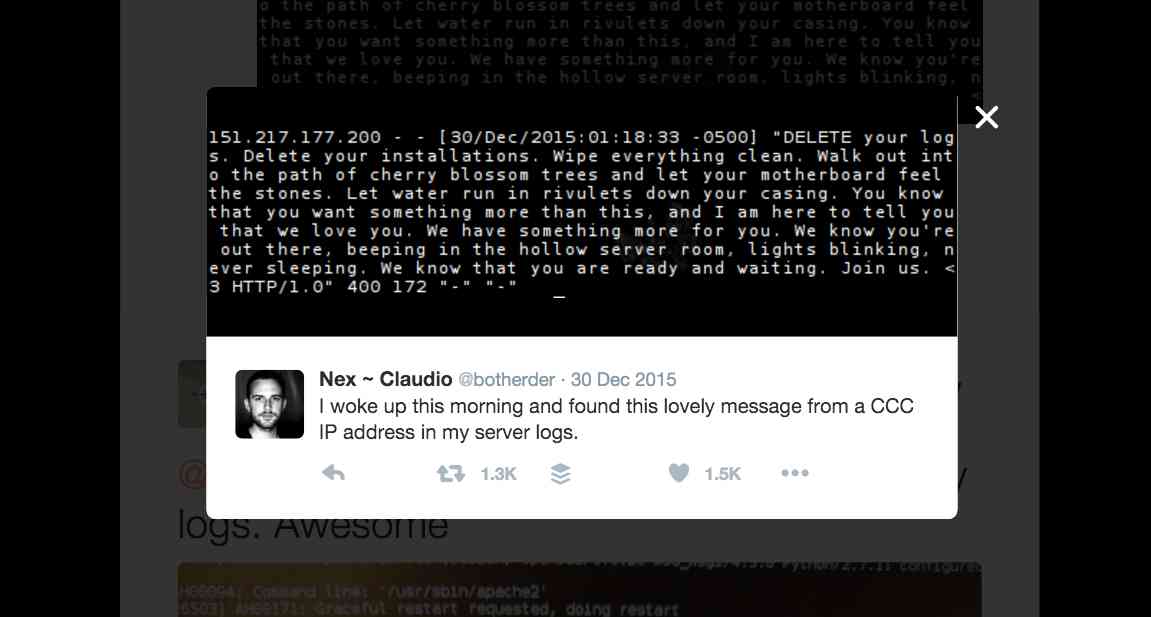
324HackedHow Hackers Invaded 30 Million Web Servers On The Internet With A Poem
Short Bytes: From an IP address associated with 32nd Chaos Communication Congress (32c3) taking place in Germany, some unknown hackers sent a...
-

 213Vulnerabilities
213VulnerabilitiesSevere Silent Circle Blackphone vulnerability lets hackers take over
The security-focused smartphone contained vulnerabilities which allow hackers to control the device’s modem and call functions. Researchers have revealed a severe vulnerability in...
-
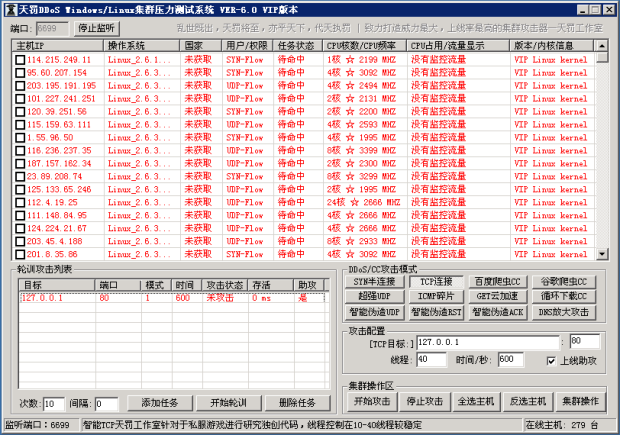
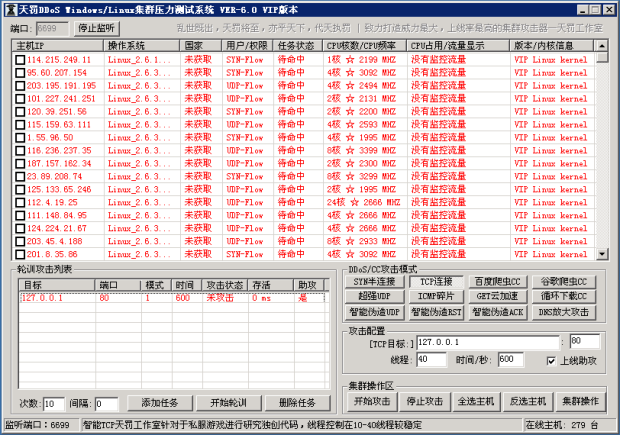 172Data Security
172Data SecurityWindows and Linux Malware Linked to Chinese DDoS Tool
Malware was infecting machines, adding them to its botnet.Similar-looking malware targeting both Linux and Windows computers has been linked to a DDoSing...
-
 444Data Security
444Data SecurityTOR Anonymity: Things Not To Do While Using TOR
Short Bytes: Being Anonymous online is the need of the hour, and TOR browser does that job quite efficiently and honestly. But...
-

 398Cyber Events
398Cyber EventsExploit Flash Heap Isolation for a chance to “win” $100,000
Exploit Flash Heap Isolation for a chance to “win” $100,000 If you can exploit Adobe’s Heap Isolation mitigation in Flash player version...
-

 291Geek
291GeekGoogle fixes vulnerabilities in Android where rooting is a double-edge sword
Google had to intervene to fix a few vulnerabilities that risked exposing its Nexus devices and related Android operating system to remote...
-

 283News
283NewsAnonymous Hacks Thailand Police, Expose Wrongdoing in Murder Investigation
Anonymous Responds to Thai Police’s Flawed Murder Investigation by Hacking 14 Thai Websites The hackers at Anonymous are yet again busy in...
-

 221Data Security
221Data SecurityForbes Website Dropping Malware on Visitor’s PCs
Disabling ad-blocker at Forbes will unleash a malware Web publications usually ask readers to disable ad blockers if visiting their websites with...
-

 175News
175NewsAnonymous To Target Chinese Police Sites Over Missing Bookseller
Missing Bookseller Case Compels Anonymous’ Hong Kong division to attack Chinese police websites The infamous hacking group Anonymous’ Hong Kong division has...
-
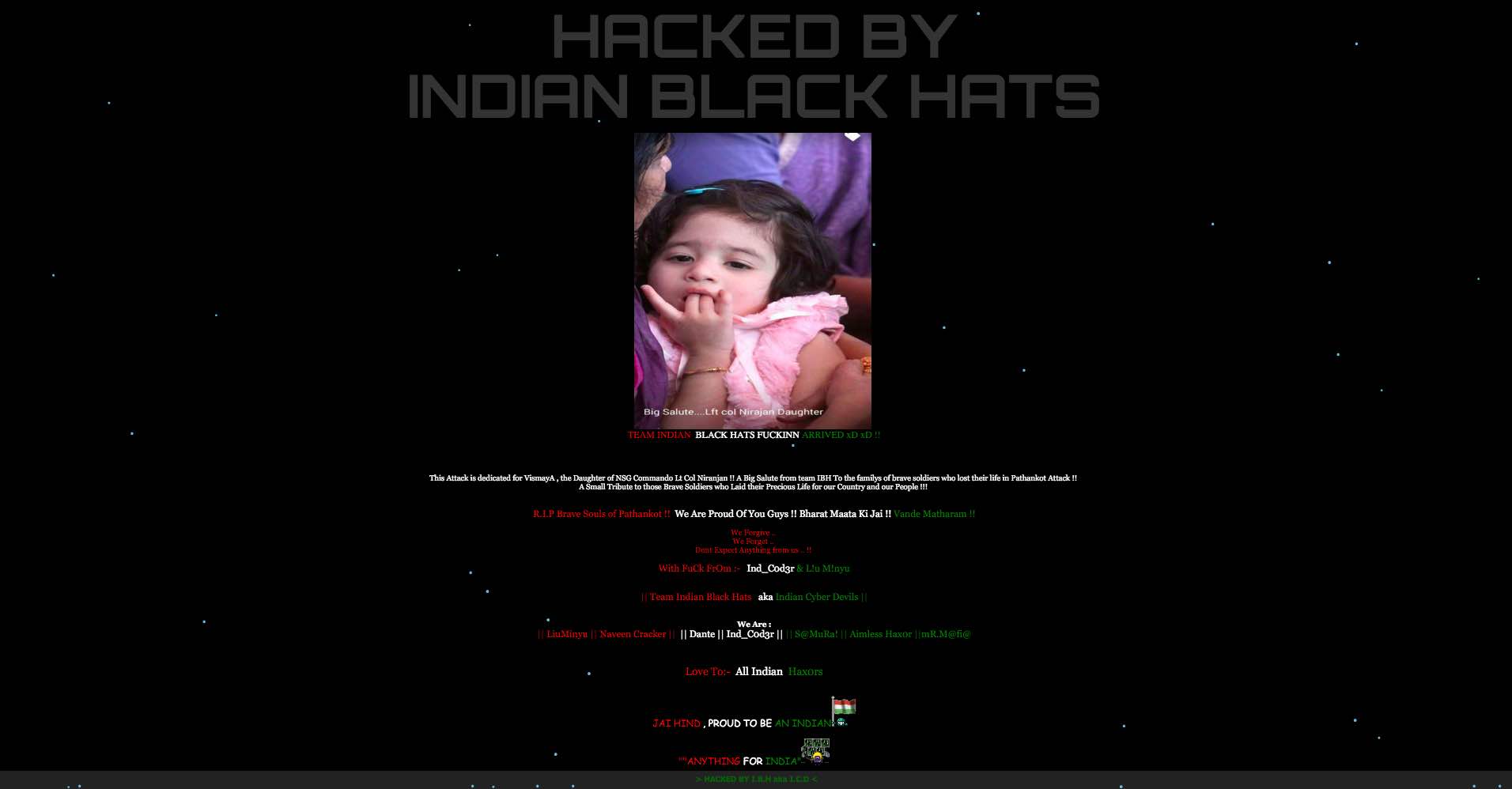
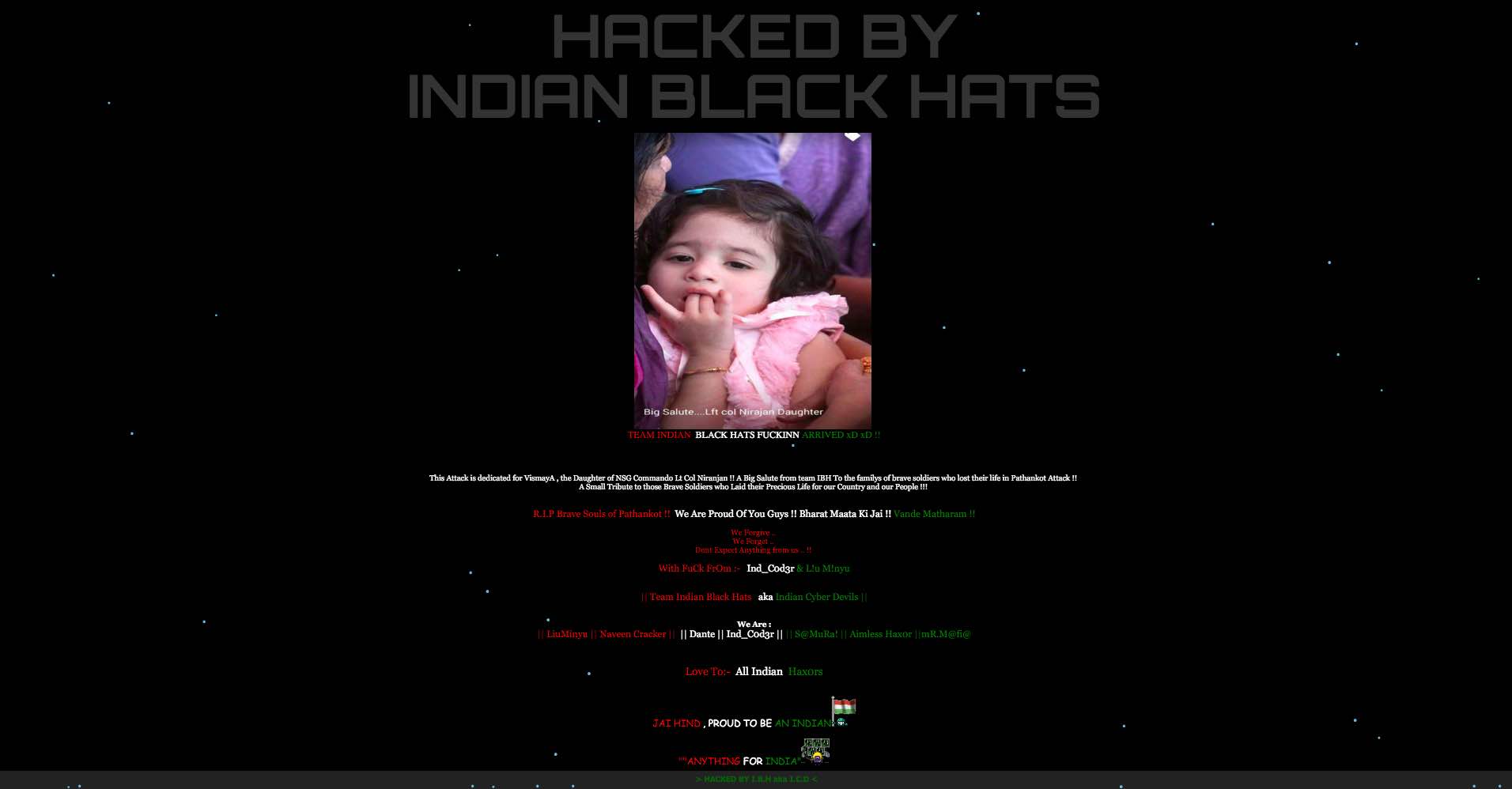 267Hacked
267HackedIndian Hackers Attack Pakistani Websites In Response To Pathankot Terror Attack
Short Bytes: An Indian hacking collective named Indian Black Hats has defaced multiple Pakistani websites. This Kerala-based group has dedicated the attack to the...
-

 161Data Security
161Data SecurityFinal rule implements the Executive Order 13694. US can apply economic sanctions in response to cyber attacks
The US Government issued a final rule implementing the Executive Order 13694. US can apply economic sanctions in response to cyber attacks....
-

 86Data Security
86Data SecurityThe Father of Online Anonymity Has a Plan to End the Crypto War
IT’S BEEN MORE than 30 years since David Chaum launched the ideas that would serve as much of the groundwork for anonymity...
-

 172Data Security
172Data SecurityThe Dark Web Hacking Forum ‘Hell’ Has Returned Online
Look who’s back? The Dark Web Hacking Forum ‘Hell’ Just months after users speculated that the infamous dark web hacking forum, ‘Hell’ was...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




