Featured News
-

 322Geek
322GeekUK Government Department Links Back To ISIS Twitter Handles
Nowadays, every individual who uses the internet is well aware of IP and MAC addresses but for those who don’t, MAC address...
-

 263News
263News11 Ongoing Anonymous Operations You Must Know About
Anonymous is known for conducting cyber attacks against injustice but not every operation makes it to the news — There are several...
-

 180Cyber Crime
180Cyber CrimeEuropol makes 12 arrests in Remote Access Trojan crackdown
Europol have been working alongside a number of European law enforcement authorities in an attempt to crackdown against the use of Remote...
-

 346News
346NewsMacKeeper Hacked: Researcher Finds 13 Million Credentials Online
ShortRead: MacKeeper, a utility software suite for Mac OS X faced a data breach which has exposed details in relation to its...
-
 262Hacked
262HackedGCHQ Open Sources Its Spy Software – So, Am I Going To Hate Them Less?
Image | GCHQ Short Bytes: NSA’s British counterpart GCHQ has just open sourced its spying tool named Gaffer. The software is written...
-

 214Data Security
214Data SecurityThis New Secom Drone Will Hunt The Suspects Down
Japanese company “Secom” has developed a drone that could be tough to handle for intruders trying to escape after committing any crime....
-
 264Hacked
264HackedAnonymous Hacker Tells How She Attacks ISIS In The Recent Video
Image | fossBytes Short Bytes: A hacker from Anonymous collective has come forward to explain how Anonymous locates ISIS-affiliated Twitter handles and...
-
 116Data Security
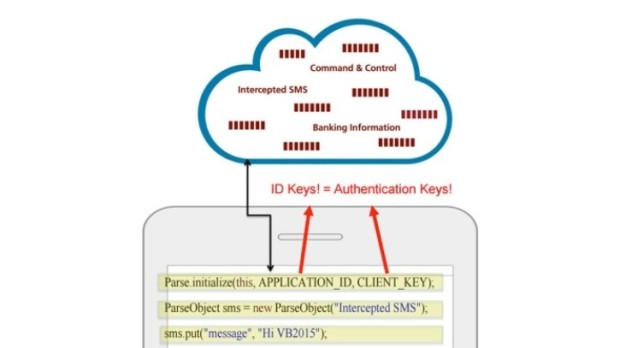
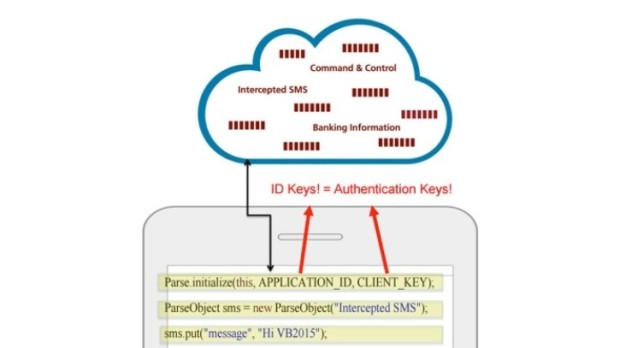
116Data SecurityTwo Mobile Banking Trojans Used Facebook Parse as C&C Server
Attackers carry out SMS fraud via the infected phones. The Android/OpFake and the Android/Marry malware families, two banking trojans targeting mobile devices, have...
-
 96Incidents
96IncidentsMacKeeper Exposed Details for 13 Million Users
Leaky database server left exposed online is at fault.For the past few weeks, security researcher Chris Vickery has been working on discovering...
-
 190Hacked
190HackedMacro Malware Is Back From The Dead, Here’s How To Defeat It
Short Bytes: The notorious macro malware from the 1990s is making a comeback in a big manner. The latest security reports suggest...
-

 195Data Security
195Data SecurityWhat the government should’ve learned about backdoors from the Clipper Chip
The Obama administration’s calls for backdoors echo the Clinton-era key escrow fiasco. In the face of a Federal Bureau of Investigation proposal...
-

 172Malware
172MalwareRAT trap: Norway police nab five in remote-access Trojan Europol swoop
Today’s arrests are part of a co-ordinated Europol initiative to crack down on all levels of computer crime. Norway’s Kripos national criminal...
-

 224Vulnerabilities
224VulnerabilitiesHackers actively exploit critical vulnerability in sites running Joomla
Wave of attacks grows. Researchers advise sites to install just-released patch. Attackers are actively exploiting a critical remote command-execution vulnerability that has...
-

 240Geek
240GeekResearchers Found Critical Vulnerabilities in Android Parking Apps
A new research has found out that numerous parking applications available in the smartphone market contain strong vulnerabilities that can allow hackers...
-

 250News
250NewsResearcher Claims To Jailbreak PS4, Posts FS Dump, PIDs Online
Sony’s Play Station 4 is one of the world’s most popular and most selling gaming consoles with more than 10 million users. In...
-
 317News
317NewsISIS Leakes Military Data Against ‘Anonymous ISIS Troll Day’
ShortRead: Anonymous trolled the ISIS terrorists a couple of days ago but rather than replying to the hacktivists, the group leaked personal...
-

 279Geek
279GeekIBM’s New Open Source OMR Project Will Boost Python, Ruby, And Other Languages
Short Bytes: IBM is taking the parts from its JVM project by separating it from Java and making them usable for any...
-
 292Data Security
292Data SecurityTor Hires Top Privacy Advocate Shari Steele As New Executive Director
Tor has hired a former Electronic Frontier Foundation (EFF) executive director to lead its project that is aimed for making the cyber...
-

 110Cyber Crime
110Cyber CrimeMoonfruit takes customers’ sites offline, as it prepares for DDoS attack
A UK company which helps consumers and small businesses create websites and online stores has taken itself and its customers' sites offline,...
-

 278Cyber Events
278Cyber EventsTwitter Alerting Users on State-Backed Attacks, Urging Use of Tor
After Facebook and Google, Twitter also has started warning message regarding state sponsored attack to some of its users — Alert urges...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




