Search results for "attack"
-

 606Malware
606MalwareHackers Exploit Netwrix Auditor RCE Flaw in Truebot Malware Attack
A newly found Truebot Malware targets both US and Canada-based organizations to exfiltrate sensitive information by exploiting vulnerabilities in the Netwrix Auditor...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesCybersecurity Agencies Sound Alarm on Rising TrueBot Malware Attacks
Cybersecurity agencies have warned about the emergence of new variants of the TrueBot malware. This enhanced threat is now targeting companies in...
-
 3.8KMalware
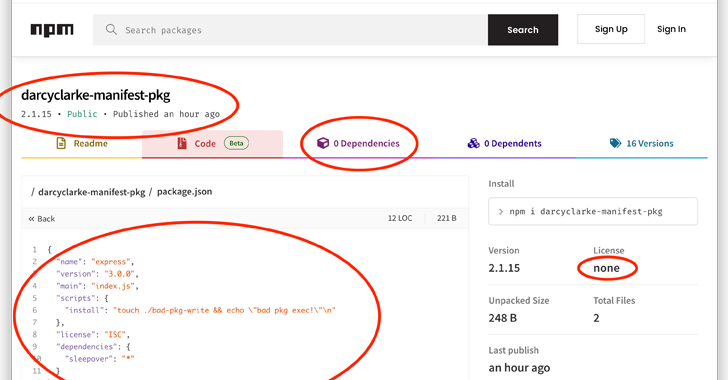
3.8KMalwareNode.js Users Beware: Manifest Confusion Attack Opens Door to Malware
The npm registry for the Node.js JavaScript runtime environment is susceptible to what’s called a manifest confusion attack that could potentially allow...
-

 4.4KMalware
4.4KMalwareHackers Use HTML Smuggling Technique to Attack European Government Entities
Over recent months, CPR (Check Point Research) monitored a Chinese threat actor attacking European Foreign Affairs ministries and embassies. Check Point Research...
-

 3.2KRansomware
3.2KRansomwareHeavy-Hitting 8Base Ransomware Attacking Industries in Various Sectors
The sudden surge in the activity of 8base ransomware in June 2023 shows it is a well-established organization to execute attacks that...
-

 948Malware
948MalwareGuLoader Malware is Attacking Law Firms Using Weaponized PDF File
The cybersecurity researchers at Morphisec Labs have been tracking the GuLoader campaign since April of this year and found that it has...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesNew Fortinet’s FortiNAC Vulnerability Exposes Networks to Code Execution Attacks
Fortinet has rolled out updates to address a critical security vulnerability impacting its FortiNAC network access control solution that could lead to...
-

 4.4KRansomware
4.4KRansomwareBeware! Mallox Ransomware Attacks IT Industries With a New Attack Pattern
A new variant of Mallox ransomware, also known as “Target company” ransomware, adopts a unique method of appending the name of the...
-

 1.7KMalware
1.7KMalwareJapanese Cryptocurrency Exchange Falls Victim to JokerSpy macOS Backdoor Attack
An unknown cryptocurrency exchange located in Japan was the target of a new attack earlier this month to deploy an Apple macOS...
-

 2.2KMalware
2.2KMalwareScarCruft Hackers Exploit Ably Service for Stealthy Wiretapping Attacks
The North Korean threat actor known as ScarCruft has been observed using an information-stealing malware with previously undocumented wiretapping features as well...
-
 808Vulnerabilities
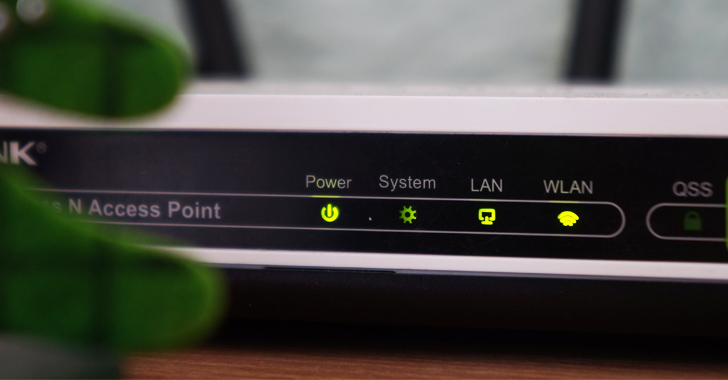
808VulnerabilitiesNew Condi Malware Hijacking TP-Link Wi-Fi Routers for DDoS Botnet Attacks
A new malware called Condi has been observed exploiting a security vulnerability in TP-Link Archer AX21 (AX1800) Wi-Fi routers to rope the...
-

 4.0KCyber Attack
4.0KCyber AttackExperts Uncover Year-Long Cyber Attack on IT Firm Utilizing Custom Malware RDStealer
A highly targeted cyber attack against an East Asian IT company involved the deployment of a custom malware written in Golang called...
-

 3.5KMalware
3.5KMalwareHackers Are Actively Using New Mystic Stealer Malware in Cyber Attacks
Recently, the cybersecurity researchers at CYFIRMA found that hackers are actively using “Mystic Stealer Malware,” a new information stealer. It’s been claimed...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesThird Flaw Uncovered in MOVEit Transfer App Amidst Cl0p Ransomware Mass Attack
Progress Software on Thursday disclosed a third vulnerability impacting its MOVEit Transfer application, as the Cl0p cybercrime gang deployed extortion tactics against...
-

 1.4KData Security
1.4KData SecurityBig german university shuts down every computer on campus after ransomware attack
Following events that have affected at least a half dozen other comparable institutions in recent months, the Kaiserslautern University of Applied Sciences...
-

 2.4KData Security
2.4KData SecurityNew AiTM Phishing Attack Technique Makes It Easy to Hack Business Email Accounts
Experts from Microsoft Defender discovered a multi-stage adversary-in-the-middle (AiTM) phishing and business email compromise (BEC) attack that targeted firms that provide banking...
-
 1.2KMalware
1.2KMalwareNew Kimsuky social engineering attack can be used to hack anyone
Researchers from SentinelLabs found a social engineering effort aimed at specialists in North Korean issues that was carried out by an advanced...
-

 4.5KVulnerabilities
4.5KVulnerabilitiesMOVEit Transfer Under Attack: Zero-Day Vulnerability Actively Being Exploited
A critical flaw in Progress Software’s in MOVEit Transfer managed file transfer application has come under widespread exploitation in the wild to...
-

 4.6KMalware
4.6KMalwareEvasive QBot Malware Leverages Short-lived Residential IPs for Dynamic Attacks
An analysis of the “evasive and tenacious” malware known as QBot has revealed that 25% of its command-and-control (C2) servers are merely...
-

 463Malware
463MalwareCyber attack forced a idaho hospital to send back their ambulances to other hospitals
Because of the damage caused to the hospital’s computer systems by a hack, ambulances servicing a wide population in Idaho are being...
-

 4.7KPhishing
4.7KPhishingShut Down Phishing Attacks – Types, Methods, Detection, Prevention Checklist
In today’s interconnected world, where digital communication and transactions dominate, phishing attacks have become an ever-present threat. By masquerading as trustworthy entities,...






