Search results for "attack"
-
 489Vulnerabilities
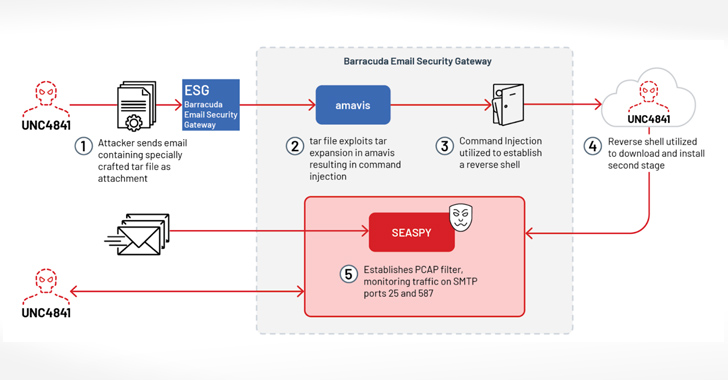
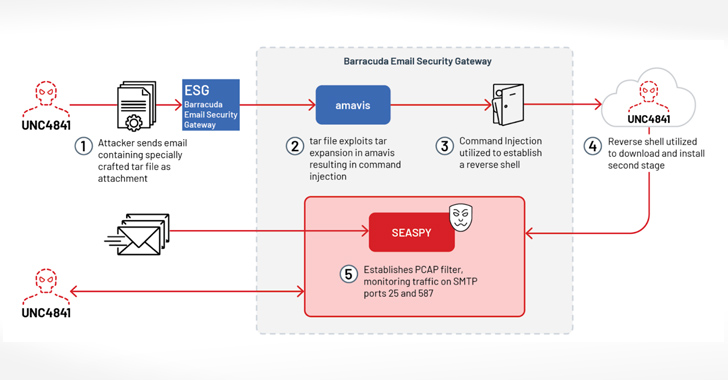
489VulnerabilitiesHackers Deploy “SUBMARINE” Backdoor in Barracuda Email Security Gateway Attacks
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday disclosed details of a “novel persistent backdoor” called SUBMARINE deployed by threat...
-

 2.7KVulnerabilities
2.7KVulnerabilitiesIvanti Warns of Another Endpoint Manager Mobile Vulnerability Under Active Attack
Ivanti has disclosed yet another security flaw impacting Endpoint Manager Mobile (EPMM), formerly known as MobileIron Core, that it said has been...
-
 4.5KData Security
4.5KData SecurityNew attack technique to hack Apache Tomcat Servers
This “pure Java” HTTP web server environment is provided by Apache Tomcat, which is a server that is both open-source and free...
-
 5.0KCyber Attack
5.0KCyber AttackA Data Exfiltration Attack Scenario: The Porsche Experience
As part of Checkmarx’s mission to help organizations develop and deploy secure software, the Security Research team started looking at the security...
-

 1.4KMalware
1.4KMalwareRust Infostealer Malware Attacks macOS Sonoma Ahead of Public Release
Based on recent reports, it was discovered that there has been info stealer malware that affects both Windows and macOS platforms. The...
-

 1.1KData Breach
1.1KData BreachNew SEC Rules Require U.S. Companies to Reveal Cyber Attacks Within 4 Days
The U.S. Securities and Exchange Commission (SEC) on Wednesday approved new rules that require publicly traded companies to publicize details of a...
-

 1.8KMalware
1.8KMalwaremacOS Under Attack: Examining the Growing Threat and User Perspectives
As the number of people using macOS keeps going up, so does the desire of hackers to take advantage of flaws in...
-
 742Vulnerabilities
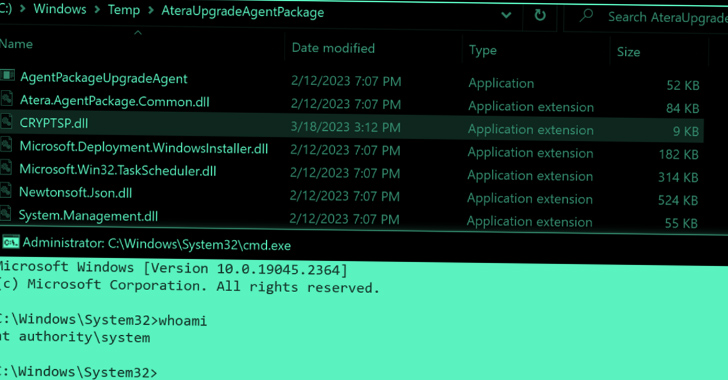
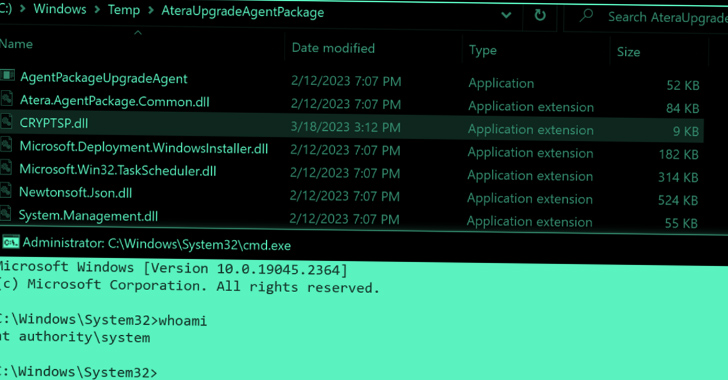
742VulnerabilitiesCritical Zero-Days in Atera Windows Installers Expose Users to Privilege Escalation Attacks
Zero-day vulnerabilities in Windows Installers for the Atera remote monitoring and management software could act as a springboard to launch privilege escalation...
-
Malware
Azure AD Token Forging Technique in Microsoft Attack Extends Beyond Outlook, Wiz Reports
The recent attack against Microsoft’s email infrastructure by a Chinese nation-state actor referred to as Storm-0558 is said to have a broader...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesDDoS Botnets Hijacking Zyxel Devices to Launch Devastating Attacks
Several distributed denial-of-service (DDoS) botnets have been observed exploiting a critical flaw in Zyxel devices that came to light in April 2023...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesCitrix NetScaler ADC and Gateway Devices Under Attack: CISA Urges Immediate Action
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued an advisory on Thursday warning that the newly disclosed critical security flaw in...
-
 648Vulnerabilities
648VulnerabilitiesCritical Flaws in AMI MegaRAC BMC Software Expose Servers to Remote Attacks
Two more security flaws have been disclosed in AMI MegaRAC Baseboard Management Controller (BMC) software that, if successfully exploited, could allow threat...
-

 3.3KMalware
3.3KMalwareFIN8 Revamped Hacking Toolkit with New Stealthy Attack Features
Syssphinx (aka FIN8) is a financially motivated cyber-crime group deploying revamped sardonic backdoor to deliver Noberus ransomware. This group has been active since...
-
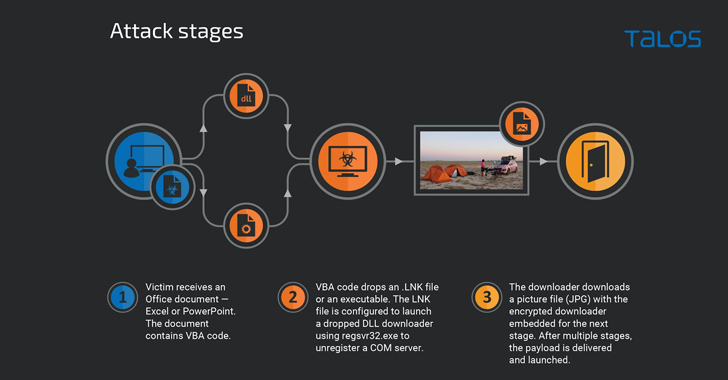
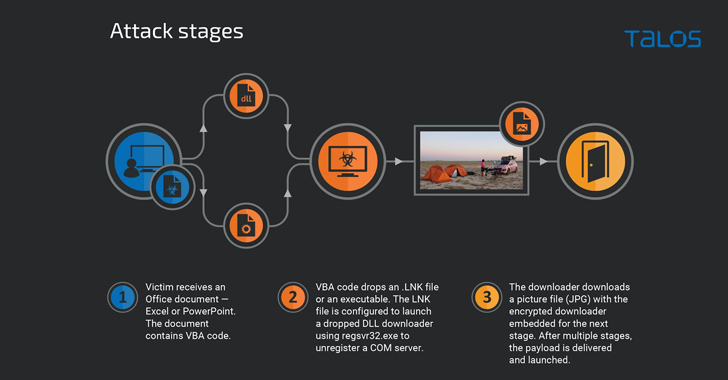 2.4KMalware
2.4KMalwarePicassoLoader Malware Used in Ongoing Attacks on Ukraine and Poland
Government entities, military organizations, and civilian users in Ukraine and Poland have been targeted as part of a series of campaigns designed...
-

 2.0KMalware
2.0KMalwareHackers Leverage USB Flash Drives to Attack Public and Private Sectors Globally
During the initial half of 2023, a notable surge occurred in attacks exploiting infected USB drives for secret theft. While the USB-based...
-

 1.5KCyber Attack
1.5KCyber AttackMicrosoft Thwarts Chinese Cyber Attack Targeting Western European Governments
Microsoft on Tuesday revealed that it repelled a cyber attack staged by a Chinese nation-state actor targeting two dozen organizations, some of...
-
 3.5KMalware
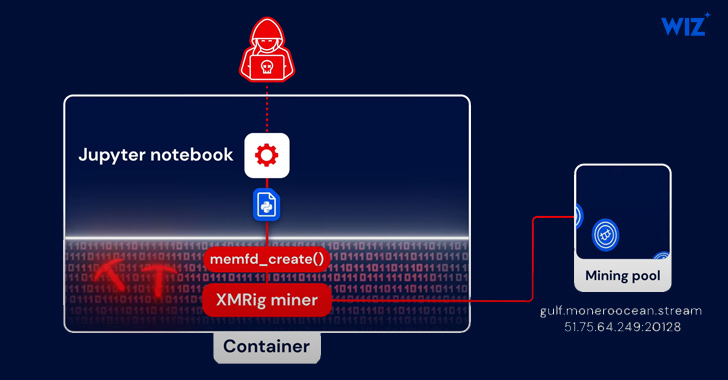
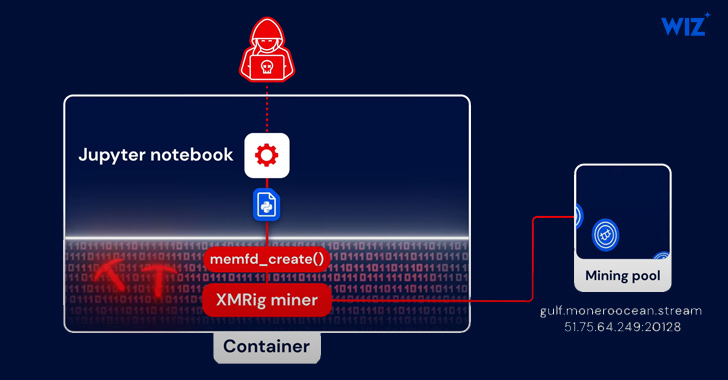
3.5KMalwarePython-Based PyLoose Fileless Attack Targets Cloud Workloads for Cryptocurrency Mining
A new fileless attack dubbed PyLoose has been observed striking cloud workloads with the goal of delivering a cryptocurrency miner, new findings...
-
 3.4KVulnerabilities
3.4KVulnerabilitiesMicrosoft Releases Patches for 132 Vulnerabilities, Including 6 Under Active Attack
Microsoft on Tuesday released updates to address a total of 132 new security flaws spanning its software, including six zero-day flaws that...
-
 2.5KMalware
2.5KMalwareHackers use Rekoobe Backdoor to Attack Linux Systems
Rekoobe is a notorious backdoor that primarily targets Linux environments, and it’s actively exploited by the threat actors, mainly a Chinese threat...
-
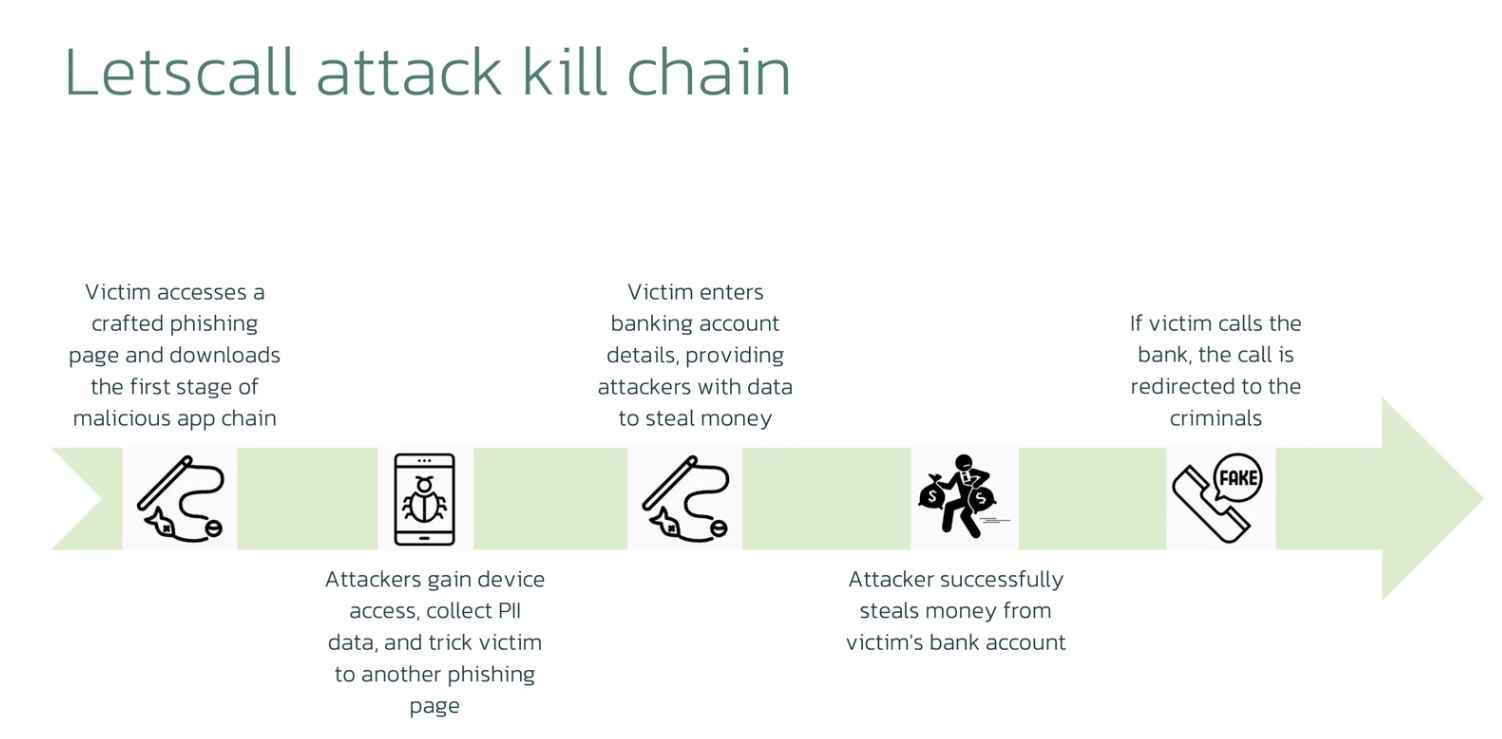
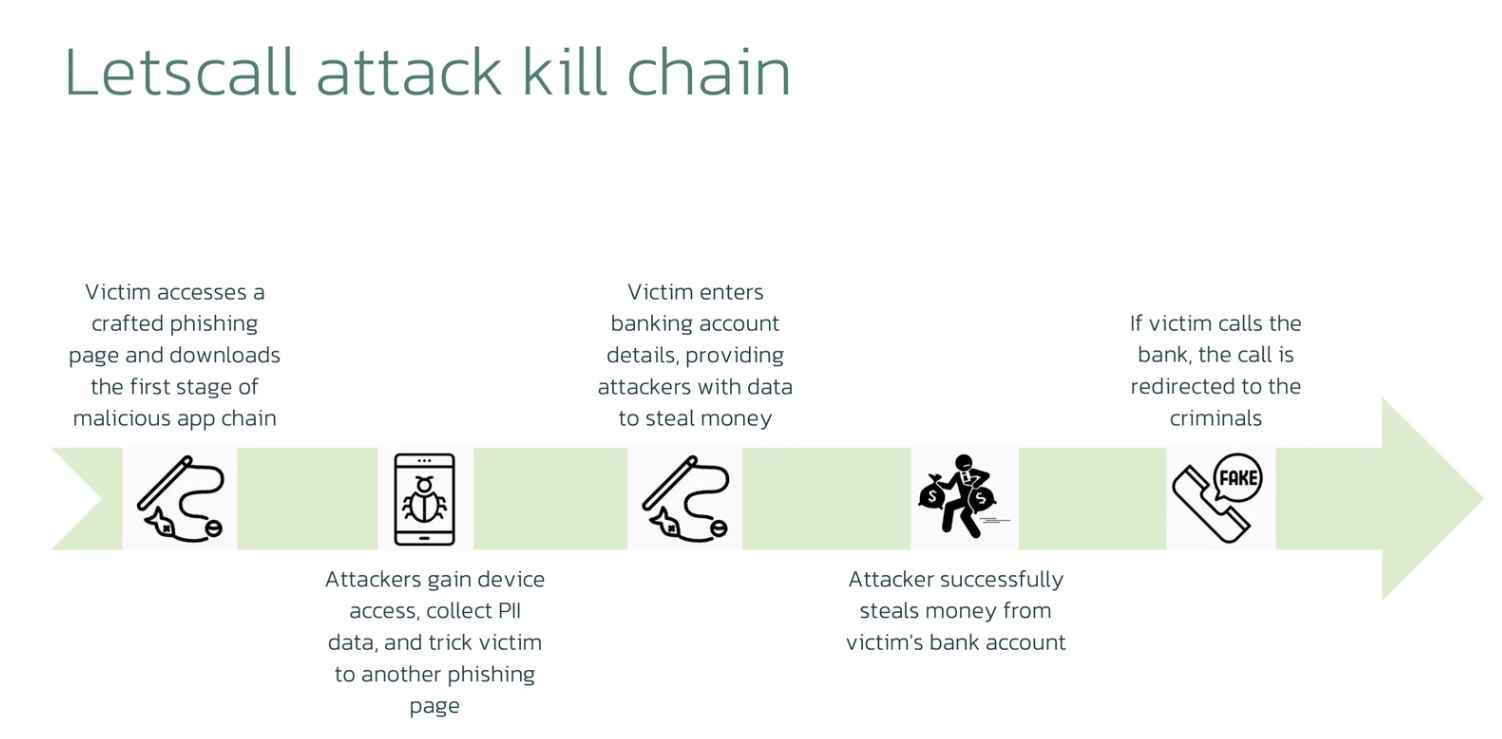 3.3KData Security
3.3KData SecurityVoIP phishing call to rob a bank. New Letscall attack technique
The cybersecurity researcher working for ThreatFabric made the discovery, and the company issued a warning, about a new and more sophisticated kind...
-

 3.3KCyber Attack
3.3KCyber AttackRevolut Faces $20 Million Loss as Attackers Exploit Payment System Weakness
Malicious actors exploited an unknown flaw in Revolut’s payment systems to steal more than $20 million of the company’s funds in early...






