Search results for "attack"
-

 2.4KVulnerabilities
2.4KVulnerabilitiesQualcomm Releases Details on Chip Vulnerabilities Exploited in Targeted Attacks
Chipmaker Qualcomm has released more information about three high-severity security flaws that it said came under “limited, targeted exploitation” back in October...
-

 1.0KMalware
1.0KMalwareWarning for iPhone Users: Experts Warn of Sneaky Fake Lockdown Mode Attack
A new “post-exploitation tampering technique” can be abused by malicious actors to visually deceive a target into believing that their Apple iPhone...
-
 5.2KVulnerabilities
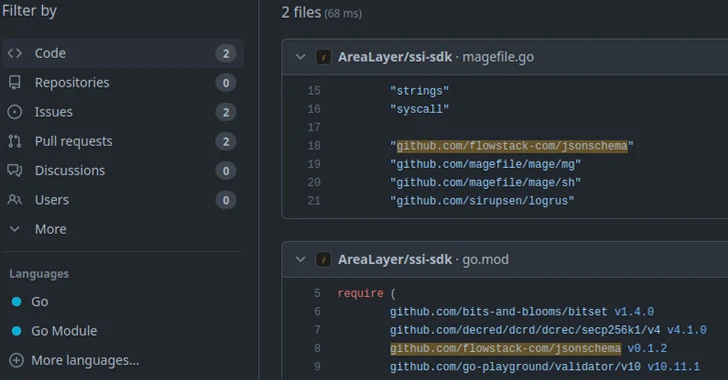
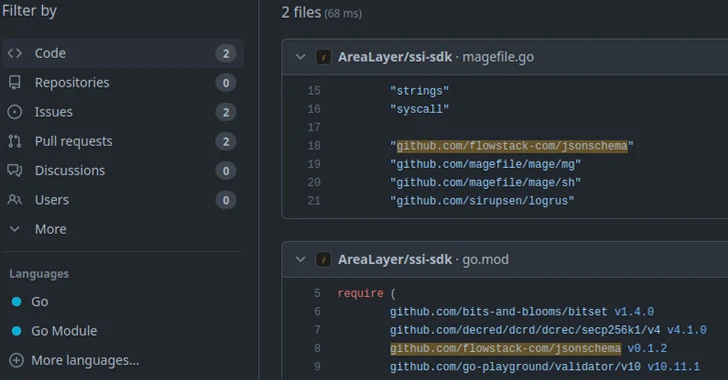
5.2KVulnerabilities15,000 Go Module Repositories on GitHub Vulnerable to Repojacking Attack
New research has found that over 15,000 Go module repositories on GitHub are vulnerable to an attack called repojacking. “More than 9,000...
-

 592Malware
592MalwareLogoFAIL: UEFI Vulnerabilities Expose Devices to Stealth Malware Attacks
The Unified Extensible Firmware Interface (UEFI) code from various independent firmware/BIOS vendors (IBVs) has been found vulnerable to potential attacks through high-impact...
-
 2.4KVulnerabilities
2.4KVulnerabilitiesCACTUS Ransomware Exploits Qlik Sense Vulnerabilities in Targeted Attacks
A CACTUS ransomware campaign has been observed exploiting recently disclosed security flaws in a cloud analytics and business intelligence platform called Qlik...
-

 4.8KCyber Attack
4.8KCyber AttackIranian Hackers Exploit PLCs in Attack on Water Authority in U.S.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) revealed that it’s responding to a cyber attack that involved the active exploitation of...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesZero-Day Alert: Google Chrome Under Active Attack, Exploiting New Vulnerability
Google has rolled out security updates to fix seven security issues in its Chrome browser, including a zero-day that has come under...
-
 4.8KData Breach
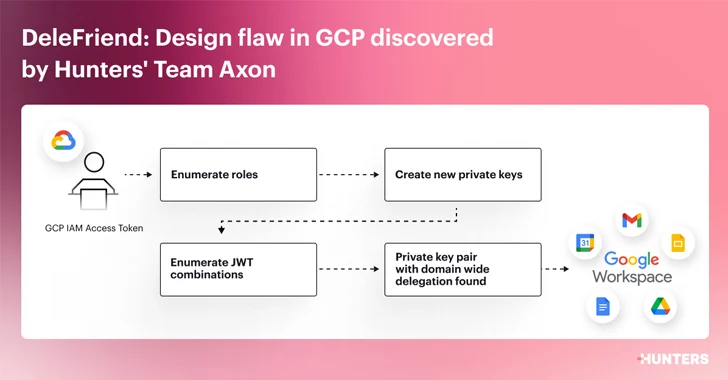
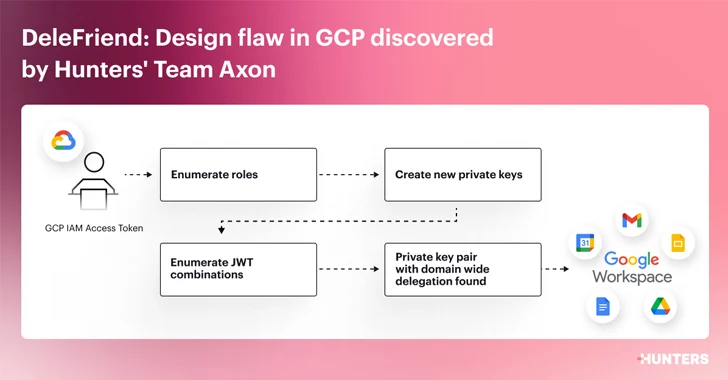
4.8KData BreachDesign Flaw in Google Workspace Could Let Attackers Gain Unauthorized Access
Cybersecurity researchers have detailed a “severe design flaw” in Google Workspace’s domain-wide delegation (DWD) feature that could be exploited by threat actors...
-

 603Malware
603MalwareNew ‘HrServ.dll’ Web Shell Detected in APT Attack Targeting Afghan Government
An unspecified government entity in Afghanistan was targeted by a previously undocumented web shell called HrServ in what’s suspected to be an...
-

 3.9KMalware
3.9KMalwareHamas-Linked Cyberattacks Using Rust-Powered SysJoker Backdoor Against Israel
Cybersecurity researchers have shed light on a Rust version of a cross-platform backdoor called SysJoker, which is assessed to have been used...
-
 4.1KVulnerabilities
4.1KVulnerabilitiesKonni Group Using Russian-Language Malicious Word Docs in Latest Attacks
A new phishing attack has been observed leveraging a Russian-language Microsoft Word document to deliver malware capable of harvesting sensitive information from...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesMirai-based Botnet Exploiting Zero-Day Bugs in Routers and NVRs for Massive DDoS Attacks
An active malware campaign is leveraging two zero-day vulnerabilities with remote code execution (RCE) functionality to rope routers and video recorders into...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesN. Korean Hackers Distribute Trojanized CyberLink Software in Supply Chain Attack
A North Korean state-sponsored threat actor tracked as Diamond Sleet is distributing a trojanized version of a legitimate application developed by a...
-
 4.0KMalware
4.0KMalwareNew Agent Tesla Malware Variant Using ZPAQ Compression in Email Attacks
A new variant of the Agent Tesla malware has been observed delivered via a lure file with the ZPAQ compression format to...
-

 1.9KMalware
1.9KMalwareHow Multi-Stage Phishing Attacks Exploit QRs, CAPTCHAs, and Steganography
Phishing attacks are steadily becoming more sophisticated, with cybercriminals investing in new ways of deceiving victims into revealing sensitive information or installing...
-

 2.6KMalware
2.6KMalwareDarkGate and PikaBot Malware Resurrect QakBot’s Tactics in New Phishing Attacks
Phishing campaigns delivering malware families such as DarkGate and PikaBot are following the same tactics previously used in attacks leveraging the now-defunct...
-

 1.8KVulnerabilities
1.8KVulnerabilitiesRussian Cyber Espionage Group Deploys LitterDrifter USB Worm in Targeted Attacks
Russian cyber espionage actors affiliated with the Federal Security Service (FSB) have been observed using a USB propagating worm called LitterDrifter in...
-

 1.1KMalware
1.1KMalwareCISA and FBI Issue Warning About Rhysida Ransomware Double Extortion Attacks
The threat actors behind the Rhysida ransomware engage in opportunistic attacks targeting organizations spanning various industry sectors. The advisory comes courtesy of...
-

 3.6KVulnerabilities
3.6KVulnerabilitiesRussian Hackers Linked to ‘Largest Ever Cyber Attack’ on Danish Critical Infrastructure
Russian threat actors have been possibly linked to what’s been described as the “largest cyber attack against Danish critical infrastructure,” in which...
-
 1.9KVulnerabilities
1.9KVulnerabilitiesNew PoC Exploit for Apache ActiveMQ Flaw Could Let Attackers Fly Under the Radar
Cybersecurity researchers have demonstrated a new technique that exploits a critical security flaw in Apache ActiveMQ to achieve arbitrary code execution in...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesChinese Hackers Launch Covert Espionage Attacks on 24 Cambodian Organizations
Cybersecurity researchers have discovered what they say is malicious cyber activity orchestrated by two prominent Chinese nation-state hacking groups targeting 24 Cambodian...






