Search results for "attack"
-
 1.2KVulnerabilities
1.2KVulnerabilitiesNew Hugging Face Vulnerability Exposes AI Models to Supply Chain Attacks
Cybersecurity researchers have found that it’s possible to compromise the Hugging Face Safetensors conversion service to ultimately hijack the models submitted by...
-
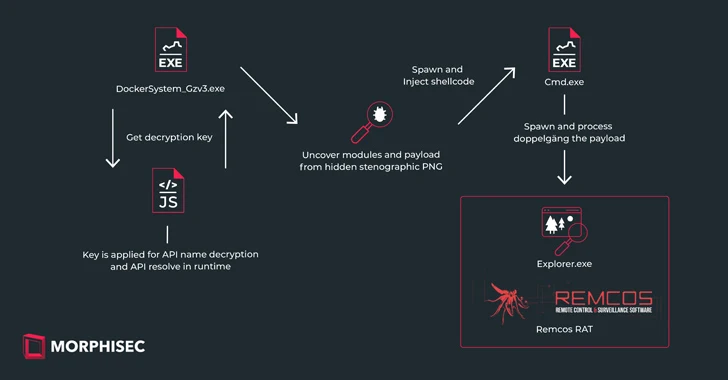
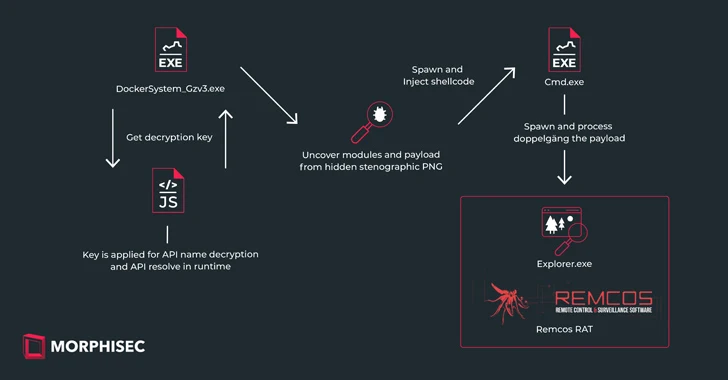 4.2KMalware
4.2KMalwareNew IDAT Loader Attacks Using Steganography to Deploy Remcos RAT
Ukrainian entities based in Finland have been targeted as part of a malicious campaign distributing a commercial remote access trojan known as...
-

 792Malware
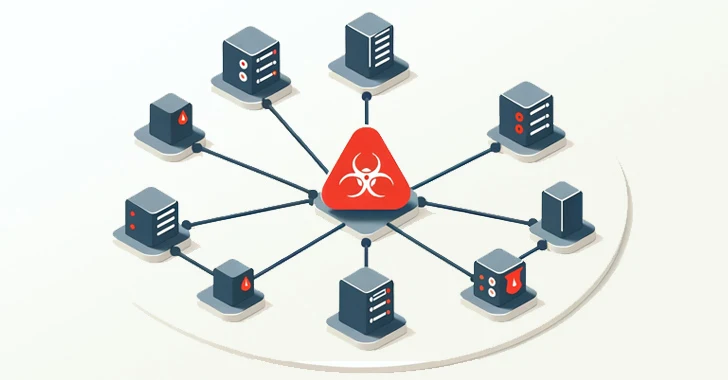
792MalwareCybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities. “SSH-Snake is a self-modifying...
-

 4.5KCyber Attack
4.5KCyber AttackIran and Hezbollah Hackers Launch Attacks to Influence Israel-Hamas Narrative
Hackers backed by Iran and Hezbollah staged cyber attacks designed to undercut public support for the Israel-Hamas war after October 2023. This...
-
 1.2KMalware
1.2KMalwareChinese Hackers Using Deepfakes in Advanced Mobile Banking Malware Attacks
A Chinese-speaking threat actor codenamed GoldFactory has been attributed to the development of highly sophisticated banking trojans, including a previously undocumented iOS...
-
 1.1KCyber Attack
1.1KCyber AttackMicrosoft, OpenAI Warn of Nation-State Hackers Weaponizing AI for Cyber Attacks
Nation-state actors associated with Russia, North Korea, Iran, and China are experimenting with artificial intelligence (AI) and large language models (LLMs) to...
-

 602Vulnerabilities
602VulnerabilitiesAlert: CISA Warns of Active ‘Roundcube’ Email Attacks – Patch Now
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a medium-severity security flaw impacting Roundcube email software to its Known...
-
 2.4KVulnerabilities
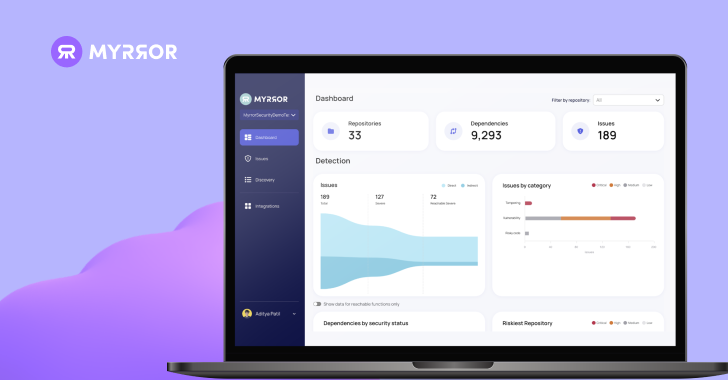
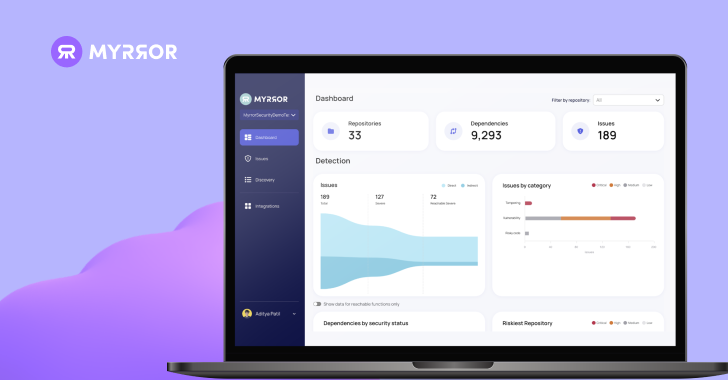
2.4KVulnerabilitiesHands-on Review: Myrror Security Code-Aware and Attack-Aware SCA
Introduction The modern software supply chain represents an ever-evolving threat landscape, with each package added to the manifest introducing new attack vectors....
-
 5.2KCyber Attack
5.2KCyber AttackU.S. Sanctions 6 Iranian Officials for Critical Infrastructure Cyber Attacks
The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) announced sanctions against six officials associated with the Iranian intelligence agency for...
-
 2.0KMalware
2.0KMalwareWarning: New Malware Emerges in Attacks Exploiting Ivanti VPN Vulnerabilities
Google-owned Mandiant said it identified new malware employed by a China-nexus espionage threat actor known as UNC5221 and other threat groups during...
-
 3.7KMalware
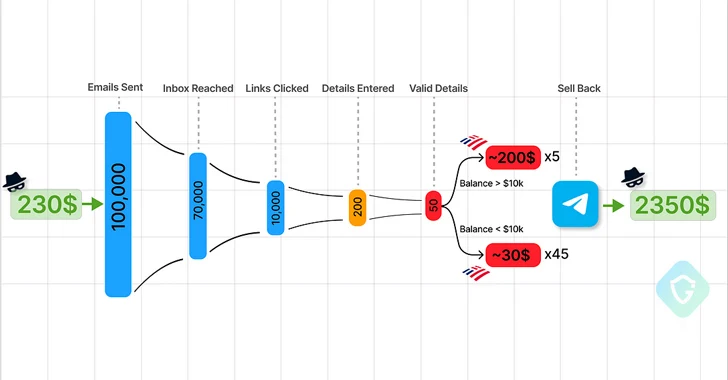
3.7KMalwareTelegram Marketplaces Fuel Phishing Attacks with Easy-to-Use Kits and Malware
Cybersecurity researchers are calling attention to the “democratization” of the phishing ecosystem owing to the emergence of Telegram as an epicenter for...
-

 1.0KCyber Attack
1.0KCyber AttackMicrosoft Warns of Widening APT29 Espionage Attacks Targeting Global Orgs
Microsoft on Thursday said the Russian state-sponsored threat actors responsible for a cyber attack on its systems in late November 2023 have...
-

 3.1KVulnerabilities
3.1KVulnerabilitiesCritical Jenkins Vulnerability Exposes Servers to RCE Attacks – Patch ASAP!
The maintainers of the open-source continuous integration/continuous delivery and deployment (CI/CD) automation software Jenkins have resolved nine security flaws, including a critical...
-

 1.8KVulnerabilities
1.8KVulnerabilities~40,000 Attacks in 3 Days: Critical Confluence RCE Under Active Exploitation
Malicious actors have begun to actively exploit a recently disclosed critical security flaw impacting Atlassian Confluence Data Center and Confluence Server, within...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesMavenGate Attack Could Let Hackers Hijack Java and Android via Abandoned Libraries
Several public and popular libraries abandoned but still used in Java and Android applications have been found susceptible to a new software...
-

 775Malware
775MalwareApache ActiveMQ Flaw Exploited in New Godzilla Web Shell Attacks
Cybersecurity researchers are warning of a “notable increase” in threat actor activity actively exploiting a now-patched flaw in Apache ActiveMQ to deliver...
-

 1.1KMalware
1.1KMalwareRemcos RAT Spreading Through Adult Games in New Attack Wave
The remote access trojan (RAT) known as Remcos RAT has been found being propagated via webhards by disguising it as adult-themed games...
-
 4.2KCyber Attack
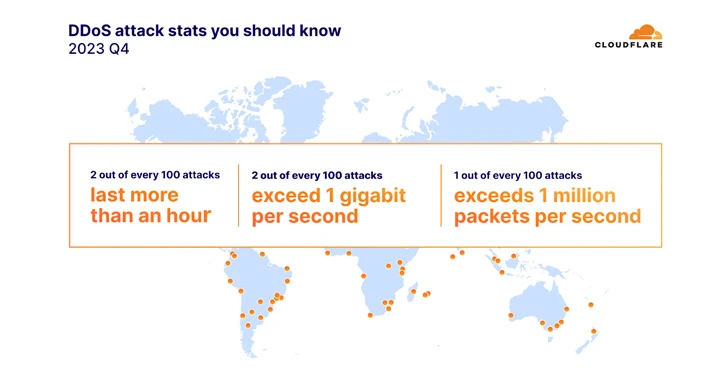
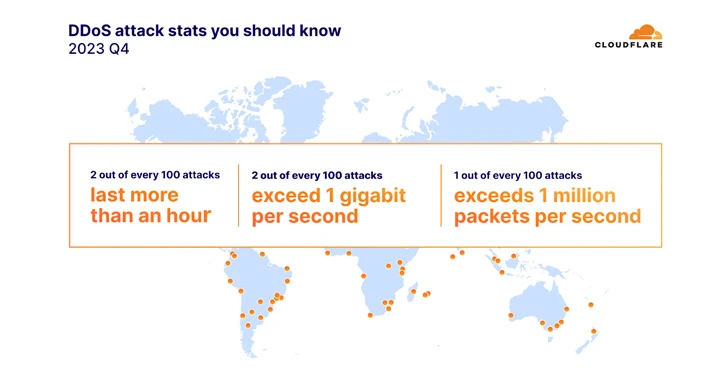
4.2KCyber AttackDDoS Attacks on the Environmental Services Industry Surge by 61,839% in 2023
The environmental services industry witnessed an “unprecedented surge” in HTTP-based distributed denial-of-service (DDoS) attacks, accounting for half of all its HTTP traffic....
-
 5.1KVulnerabilities
5.1KVulnerabilitiesNew Findings Challenge Attribution in Denmark’s Energy Sector Cyberattacks
The cyber attacks targeting the energy sector in Denmark last year may not have had the involvement of the Russia-linked Sandworm hacking...
-

 2.8KMalware
2.8KMalwareCryptominers Targeting Misconfigured Apache Hadoop and Flink with Rootkit in New Attacks
Cybersecurity researchers have identified a new attack that exploits misconfigurations in Apache Hadoop and Flink to deploy cryptocurrency miners within targeted environments....
-

 1.3KData Breach
1.3KData BreachGetting off the Attack Surface Hamster Wheel: Identity Can Help
IT professionals have developed a sophisticated understanding of the enterprise attack surface – what it is, how to quantify it and how...






