Search results for "attack"
-
 2.3KVulnerabilities
2.3KVulnerabilitiesCISA Flags 6 Vulnerabilities – Apple, Apache, Adobe, D-Link, Joomla Under Attack
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added six security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence...
-
 2.8KVulnerabilities
2.8KVulnerabilitiesWhy Public Links Expose Your SaaS Attack Surface
Collaboration is a powerful selling point for SaaS applications. Microsoft, Github, Miro, and others promote the collaborative nature of their software applications...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesNew Terrapin Flaw Could Let Attackers Downgrade SSH Protocol Security
Security researchers from Ruhr University Bochum have discovered a vulnerability in the Secure Shell (SSH) cryptographic network protocol that could allow an...
-

 3.2KCyber Attack
3.2KCyber AttackAlbanian Parliament and One Albania Telecom Hit by Cyber Attacks
The Assembly of the Republic of Albania and telecom company One Albania have been targeted by cyber attacks, the country’s National Authority...
-

 1.1KMalware
1.1KMalwareKimsuky Hackers Deploying AppleSeed, Meterpreter, and TinyNuke in Latest Attacks
Nation-state actors affiliated to North Korea have been observed using spear-phishing attacks to deliver an assortment of backdoors and tools such as...
-
 4.3KMalware
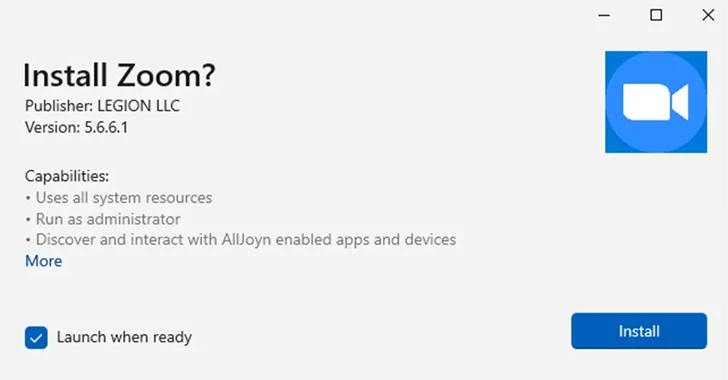
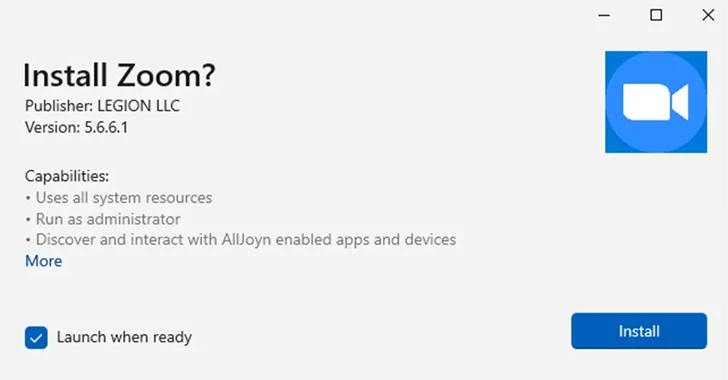
4.3KMalwareMicrosoft Disables MSIX App Installer Protocol Widely Used in Malware Attacks
Microsoft on Thursday said it’s once again disabling the ms-appinstaller protocol handler by default following its abuse by multiple threat actors to...
-

 5.2KVulnerabilities
5.2KVulnerabilitiesCritical Zero-Day in Apache OfBiz ERP System Exposes Businesses to Attack
A new zero-day security flaw has been discovered in Apache OfBiz, an open-source Enterprise Resource Planning (ERP) system that could be exploited...
-
 2.1KMalware
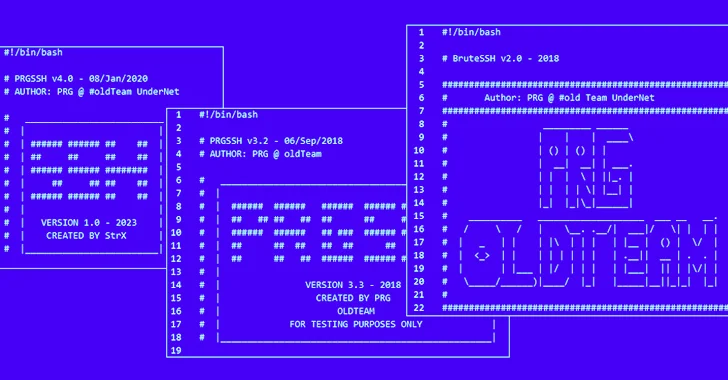
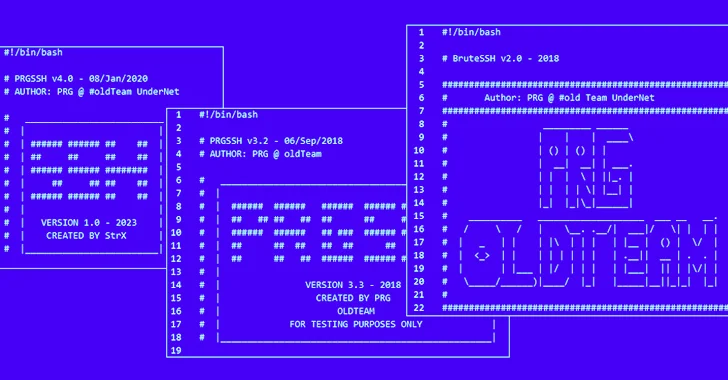
2.1KMalwareWarning: Poorly Secured Linux SSH Servers Under Attack for Cryptocurrency Mining
Poorly secured Linux SSH servers are being targeted by bad actors to install port scanners and dictionary attack tools with the goal...
-
 843Malware
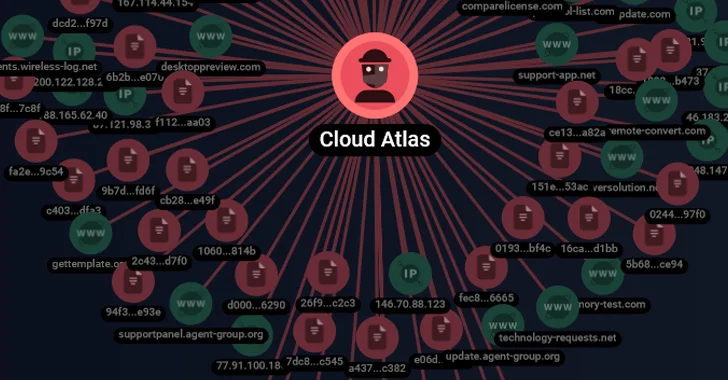
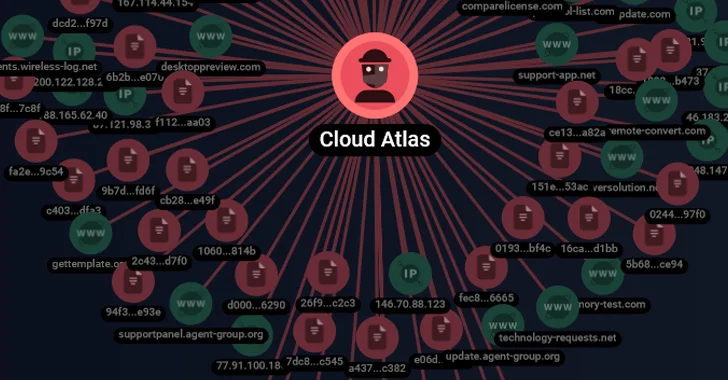
843MalwareCloud Atlas’ Spear-Phishing Attacks Target Russian Agro and Research Companies
The threat actor referred to as Cloud Atlas has been linked to a set of spear-phishing attacks on Russian enterprises. Targets included...
-

 1.9KData Breach
1.9KData BreachBritish LAPSUS$ Teen Members Sentenced for High-Profile Attacks
Two British teens part of the LAPSUS$ cyber crime and extortion gang have been sentenced for their roles in orchestrating a string...
-

 1.1KData Breach
1.1KData BreachRemote Encryption Attacks Surge: How One Vulnerable Device Can Spell Disaster
Ransomware groups are increasingly switching to remote encryption in their attacks, marking a new escalation in tactics adopted by financially motivated actors...
-

 1.7KMalware
1.7KMalwareIranian Hackers Using MuddyC2Go in Telecom Espionage Attacks Across Africa
The Iranian nation-state actor known as MuddyWater has leveraged a newly discovered command-and-control (C2) framework called MuddyC2Go in its attacks on the...
-

 2.2KTutorials
2.2KTutorialsSilent Email Attack CVE-2023-35628 : How to Hack Without an Email Click in Outlook
CVE-2023-35628 is a critical remote code execution (RCE) vulnerability affecting the Microsoft Windows MSHTML platform, with a Common Vulnerability Scoring System (CVSS)...
-
 1.6KMalware
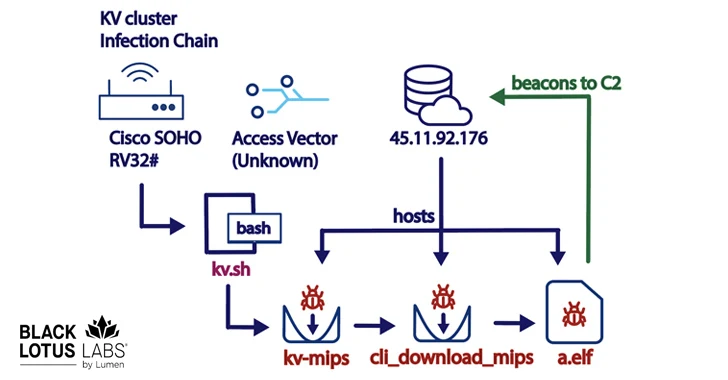
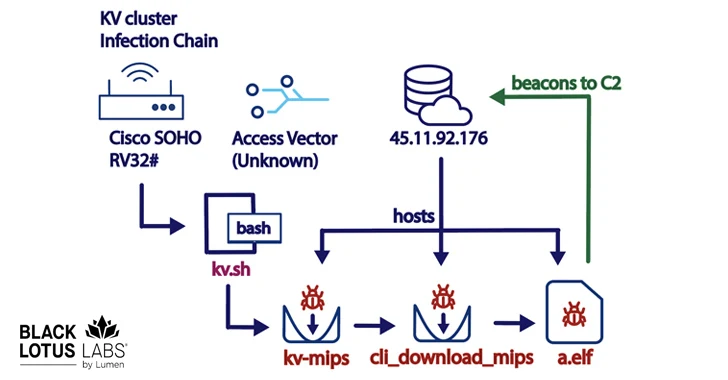
1.6KMalwareNew KV-Botnet Targeting Cisco, DrayTek, and Fortinet Devices for Stealthy Attacks
A new botnet consisting of firewalls and routers from Cisco, DrayTek, Fortinet, and NETGEAR is being used as a covert data transfer...
-

 1.7KMalware
1.7KMalwareNew NKAbuse Malware Exploits NKN Blockchain Tech for DDoS Attacks
A novel multi-platform threat called NKAbuse has been discovered using a decentralized, peer-to-peer network connectivity protocol known as NKN (short for New...
-

 915Malware
915MalwareRussian SVR-Linked APT29 Targets JetBrains TeamCity Servers in Ongoing Attacks
Threat actors affiliated with the Russian Foreign Intelligence Service (SVR) have targeted unpatched JetBrains TeamCity servers in widespread attacks since September 2023....
-
 2.3KVulnerabilities
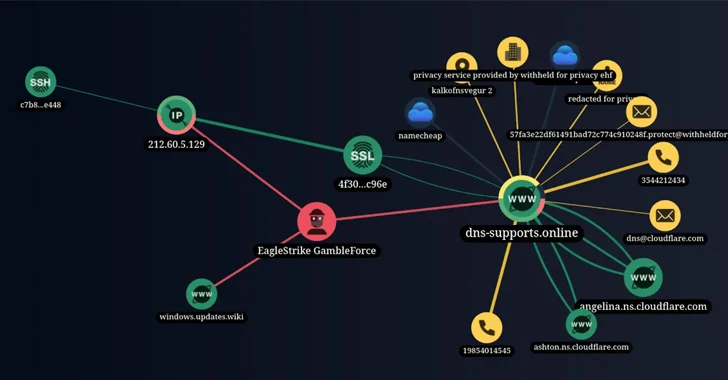
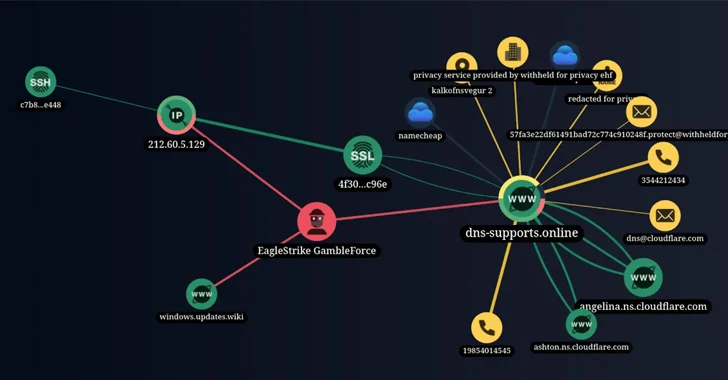
2.3KVulnerabilitiesNew Hacker Group ‘GambleForce’ Tageting APAC Firms Using SQL Injection Attacks
A previously unknown hacker outfit called GambleForce has been attributed to a series of SQL injection attacks against companies primarily in the...
-

 4.0KCyber Attack
4.0KCyber AttackMajor Cyber Attack Paralyzes Kyivstar – Ukraine’s Largest Telecom Operator
Ukraine’s biggest telecom operator Kyivstar has become the victim of a “powerful hacker attack,” disrupting customer access to mobile and internet services....
-
 4.8KTutorials
4.8KTutorialsHow to Bypass EDRs, AV with Ease using 8 New Process Injection Attacks
In the ever-evolving landscape of cybersecurity, researchers are continually uncovering new methods that challenge existing defense mechanisms. A recent study by SafeBreach,...
-

 564Vulnerabilities
564VulnerabilitiesWordPress Releases Update 6.4.2 to Address Critical Remote Attack Vulnerability
WordPress has released version 6.4.2 with a patch for a critical security flaw that could be exploited by threat actors by combining...
-

 5.2KMalware
5.2KMalwareSierra:21 – Flaws in Sierra Wireless Routers Expose Critical Sectors to Cyber Attacks
A collection of 21 security flaws have been discovered in Sierra Wireless AirLink cellular routers and open-source software components like TinyXML and...






