Search results for "attack"
-
 3.9KCyber Attack
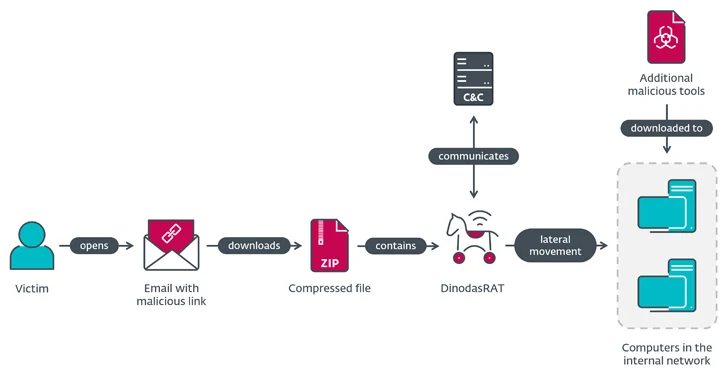
3.9KCyber AttackGuyana Governmental Entity Hit by DinodasRAT in Cyber Espionage Attack
A governmental entity in Guyana has been targeted as part of a cyber espionage campaign dubbed Operation Jacana. The activity, which was...
-
 2.1KMalware
2.1KMalwareRogue npm Package Deploys Open-Source Rootkit in New Supply Chain Attack
A new deceptive package hidden within the npm package registry has been uncovered deploying an open-source rootkit called r77, marking the first...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesOpenRefine’s Zip Slip Vulnerability Could Let Attackers Execute Malicious Code
A high-severity security flaw has been disclosed in the open-source OpenRefine data cleanup and transformation tool that could result in arbitrary code...
-
 1.2KMalware
1.2KMalwareFBI Warns of Rising Trend of Dual Ransomware Attacks Targeting U.S. Companies
The U.S. Federal Bureau of Investigation (FBI) is warning of a new trend of dual ransomware attacks targeting the same victims, at...
-
 969Vulnerabilities
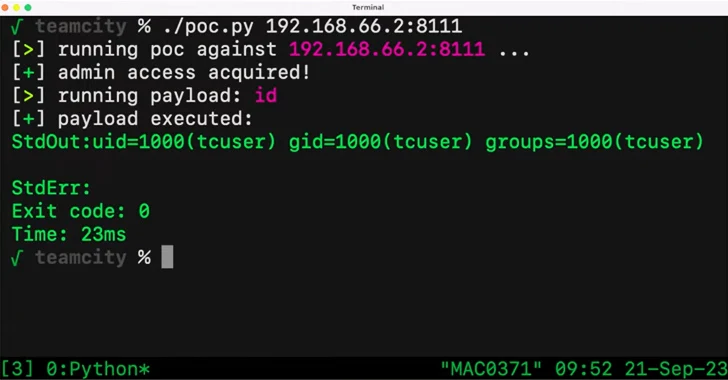
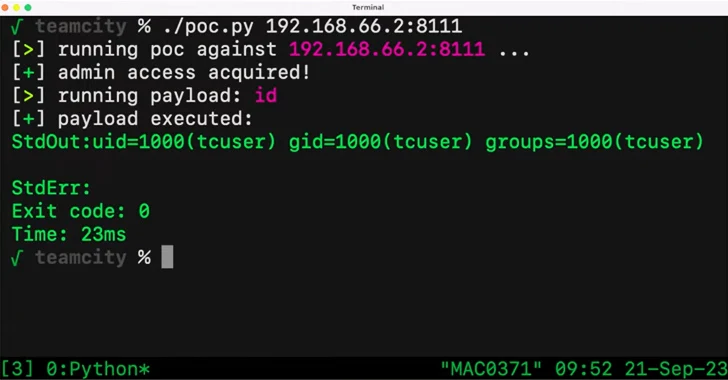
969VulnerabilitiesCritical JetBrains TeamCity Flaw Could Expose Source Code and Build Pipelines to Attackers
A critical security vulnerability in the JetBrains TeamCity continuous integration and continuous deployment (CI/CD) software could be exploited by unauthenticated attackers to...
-
 4.9KMalware
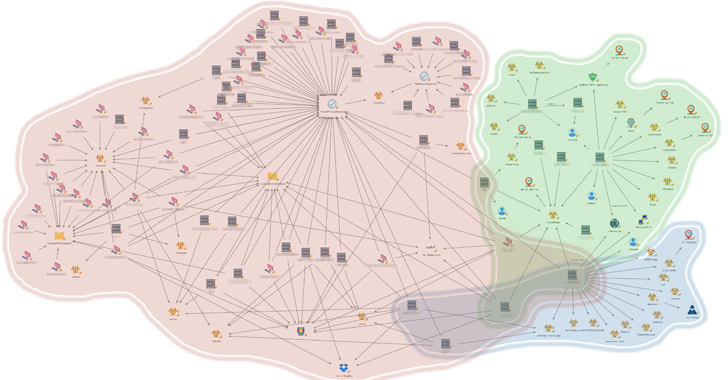
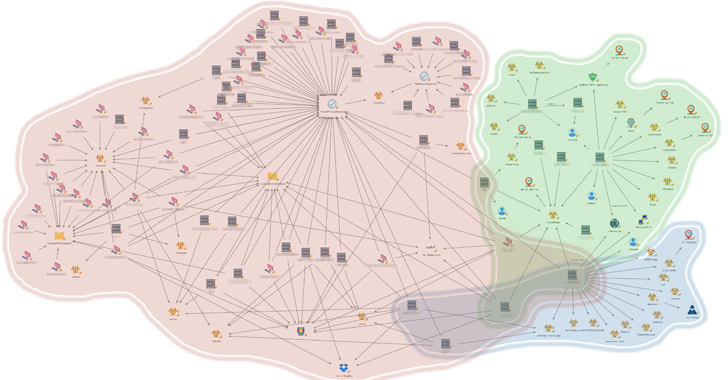
4.9KMalwareNew Report Uncovers 3 Distinct Clusters of China-Nexus Attacks on Southeast Asian Government
An unnamed Southeast Asian government has been targeted by multiple China-nexus threat actors as part of espionage campaigns targeting the region over...
-
 5.0KMalware
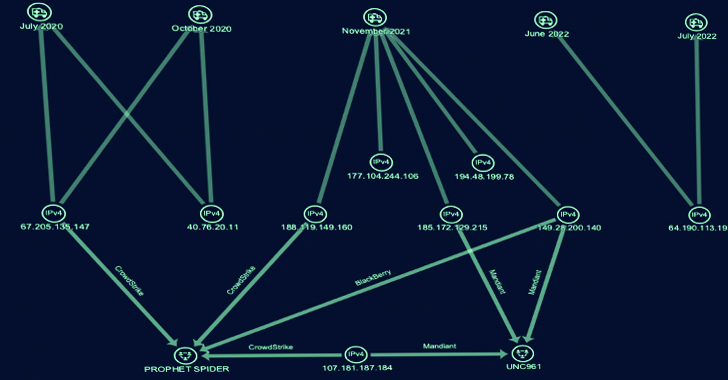
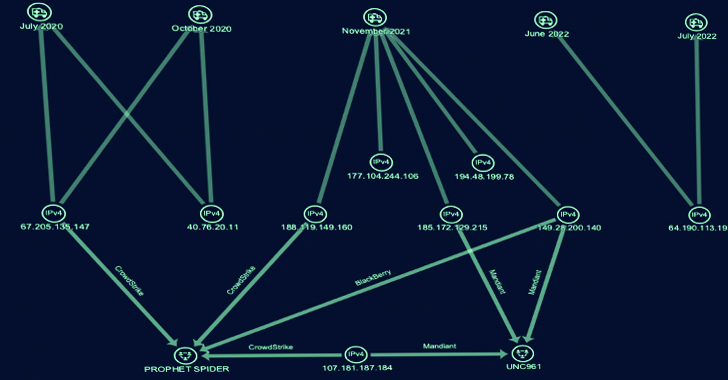
5.0KMalwareCyber Group ‘Gold Melody’ Selling Compromised Access to Ransomware Attackers
A financially motivated threat actor has been outed as an initial access broker (IAB) that sells access to compromised organizations for other...
-
 243Malware
243MalwareUkrainian Hacker Suspected to be Behind “Free Download Manager” Malware Attack
The maintainers of Free Download Manager (FDM) have acknowledged a security incident dating back to 2020 that led to its website being...
-

 2.9KMalware
2.9KMalwareHow Cyberattacks Are Transforming Warfare
There is a new battlefield. It is global and challenging to defend. What began with a high-profile incident back in 2007, when...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesCritical GitHub Vulnerability Exposes 4,000+ Repositories to Repojacking Attack
A new vulnerability disclosed in GitHub could have exposed thousands of repositories at risk of repojacking attacks, new findings show. The flaw...
-
 3.4KMalware
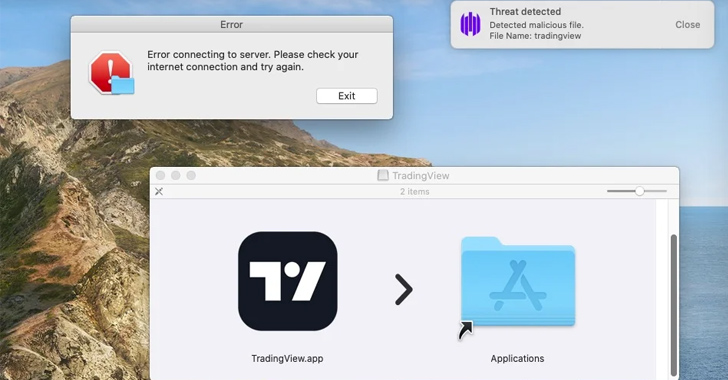
3.4KMalwareBeware: MetaStealer Malware Targets Apple macOS in Recent Attacks
A new information stealer malware called MetaStealer has set its sights on Apple macOS, making the latest in a growing list of...
-
 1.1KMalware
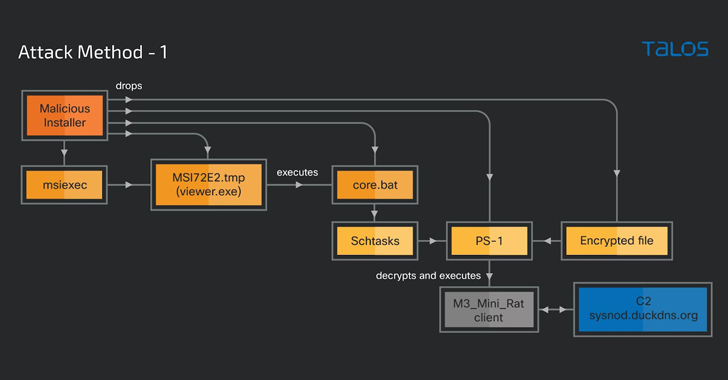
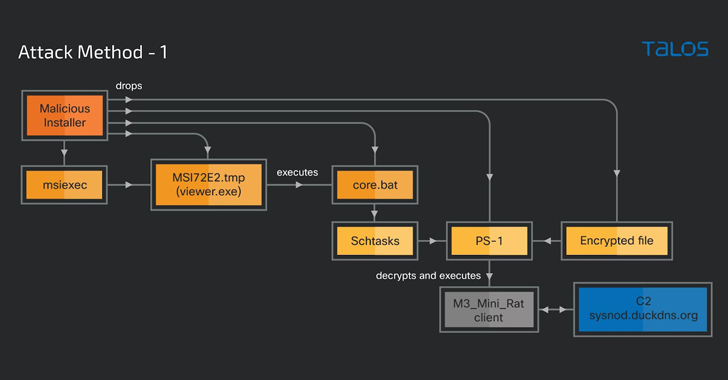
1.1KMalwareCybercriminals Weaponizing Legitimate Advanced Installer Tool in Crypto-Mining Attacks
A legitimate Windows tool used for creating software packages called Advanced Installer is being abused by threat actors to drop cryptocurrency-mining malware...
-

 3.4KData Security
3.4KData SecurityCaldera: Free Operational technology OT Attack Emulation Tool to secure ICS, SCADA and PLC devices
MITRE and the US Cybersecurity and Infrastructure Security Agency (CISA) have collaborated to develop a new open source tool that simulates cyber-attacks...
-

 1.3KData Security
1.3KData SecurityTwo world’s biggest telescopes hacked by Ransomware attack
Several telescopes are still down weeks after a cybersecurity attack was discovered by US National Science Foundation (NSF) researchers. There is presently no...
-
 1.0KData Security
1.0KData Security“Prompt injection”attack allows hacking into LLM AI chatbots like ChatGPT, Bard
A kind of attack known as prompt injection is directed against LLMs, which are the language models that are the driving force...
-
Malware
New SuperBear Trojan Emerges in Targeted Phishing Attack on South Korean Activists
A new phishing attack likely targeting civil society groups in South Korea has led to the discovery of a novel remote access...
-

 4.8KCyber Attack
4.8KCyber AttackNumbers Don’t Lie: Exposing the Harsh Truths of Cyberattacks in New Report
How often do cyberattacks happen? How frequently do threat actors target businesses and governments around the world? The BlackBerry® Threat Research and...
-
 1.6KVulnerabilities
1.6KVulnerabilitiesAlert: Juniper Firewalls, Openfire, and Apache RocketMQ Under Attack from New Exploits
Recently disclosed security flaws impacting Juniper firewalls, Openfire, and Apache RocketMQ servers have come under active exploitation in the wild, according to...
-

 386Vulnerabilities
386VulnerabilitiesCritical Vulnerability Alert: VMware Aria Operations Networks at Risk from Remote Attacks
VMware has released software updates to correct two security vulnerabilities in Aria Operations for Networks that could be potentially exploited to bypass...
-

 1.0KVulnerabilities
1.0KVulnerabilitiesCyberattacks Targeting E-commerce Applications
Cyber attacks on e-commerce applications are a common trend in 2023 as e-commerce businesses become more omnichannel, they build and deploy increasingly...
-

 817Data Breach
817Data BreachKroll Suffers Data Breach: Employee Falls Victim to SIM Swapping Attack
Risk and financial advisory solutions provider Kroll on Friday disclosed that one of its employees fell victim to a “highly sophisticated” SIM...






