Featured News
-

 172Hacked
172HackedBaidu’s Corrupt SDK Puts 100 Million Android Users Open To Backdoor Attacks
Short Bytes: Baidu, the Chinese analogous to Google has distributed a software development kit (SDK), Moplus, which has reportedly made over 100...
-

 257Geek
257GeekLearn How To Work On Git and GitHub With Its New Free Training Course
Short Bytes: Are you new to the world of Git and GitHub, finding it a little bit scary? Well, to erase these...
-
 112Data Security
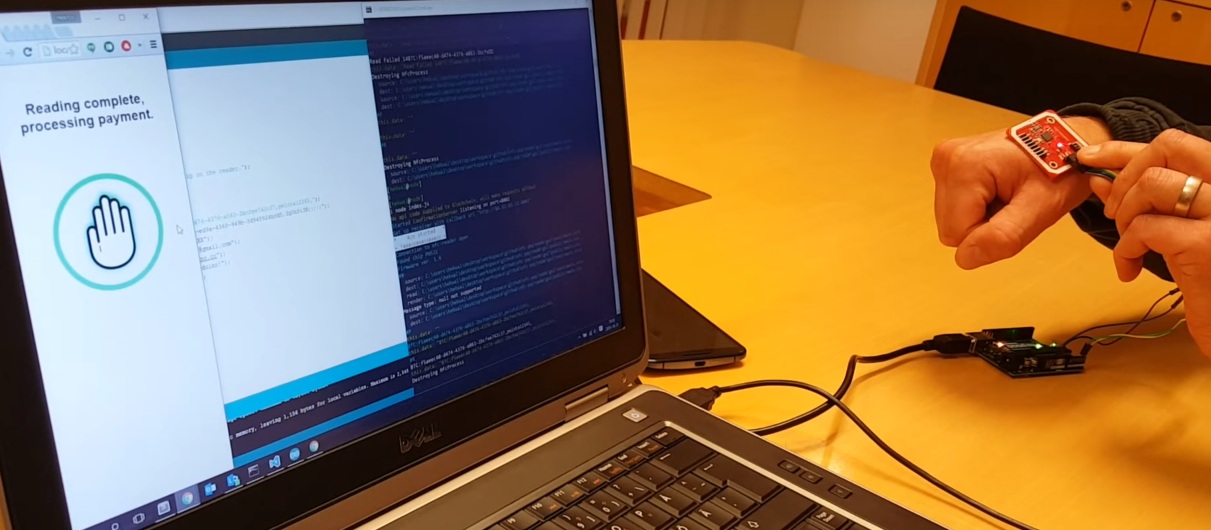
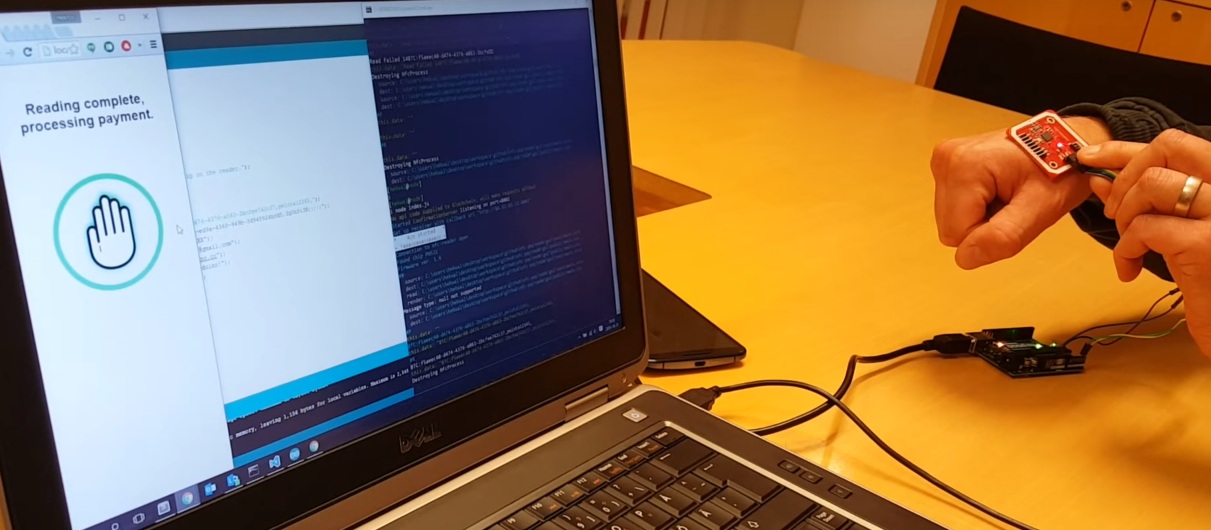
112Data SecurityThis Chip Is Implanted Under The Skin And Used To Pay For Things Using Bitcoin
Wallets are becoming more integrated with other things. Soon, we might all use our phones as a way to pay for things....
-
 155Incidents
155IncidentsThird man arrested over TalkTalk hack as Vodafone reveals cyberattack of its own
Vodafone is the second British telecommunications company in two weeks to be on the receiving end of a serious hack. Yet another...
-

 215Incidents
215IncidentsMaine Mendoza’s Twitter account hacked by ‘Anonymous Philippines’
A group of hackers who claimed responsibility for the hacking of numerous government and even Chinese websites since 2012 has found a...
-
 139Data Security
139Data SecurityBrowser-Based iOS 9.1/9.2 Jailbreak Wins $1M Bounty, Will Be Sold for Corporate and Government Use
Earlier this month, exploit acquisition platform Zerodium debuted an iOS 9 bug bounty that would pay out up to three million dollars...
-

 123Data Security
123Data SecurityAndroid Malware Disguises itself as MS Word Doc, Spies on Your Phone
Researchers have discovered an Android malware disguising itself as a Microsoft word document which triggers a malicious code once opened. This Android malware was...
-

 348Hacked
348HackedHackers Win $1 Million Bounty for Remotely Hacking iPhones Running iOS 9
Short Bytes: Zerodium’s million dollar iOS 9 jailbreak bounty program has expired and it has resulted in a new iOS jailbreak. But,...
-

 335Geek
335GeekLinus Torvalds Goes All Crazy And Angry Over Some ‘Sh*t Code’
Short Bytes: Linus Torvalds says, “Talk is cheap. Show me the code.” What if you show him some code and it pisses...
-

 192Data Security
192Data SecurityHow to exploit new Facebook feature to access personal photos of people without being their friend?
Facebook’s is always changing and its team is adding new functionality every couple of months. With new changes there are chances of...
-

 214Hacked
214HackedLatest Adobe Flash Zero-Day Bug Already Part of Angler and Nuclear Exploit Kits
Short Bytes: Adobe Flash Player continues to remain the favorite target of the cyber attackers. The recent zero-day exploits that were earlier...
-

 90Data Security
90Data SecurityYahoo’s “crypto witch” exploits web security feature, learns your site history
Timing attacks are an interesting part of computer security. As an extreme example, imagine that your computer took one second to verify...
-

 253Data Security
253Data SecuritySnapchat to save, modify and republish your private photos
Snapchat’s new term and conditions have resulted in outrage from its users and twitter has been flooded with tweets from users rejecting...
-

 127Data Security
127Data SecurityLeaving Laptops in Hotel Rooms: A Bad Idea
A laptop filled with data? An external HDD filled with even more data? There’s bound to be a phone – possibly two...
-

 334Data Security
334Data SecurityVodafone Hacked, Customers’ Personal Data, Banking Information Stolen
In the wake of the TalkTalk Scandal, Vodafone finally admitted that hackers did manage to steal around 20,000 Vodafone customers’ bank details....
-

 91Data Security
91Data SecurityHome Network Analysis: DVRs and my Network Interact
My last on-topic post pontificated about the dangers and surprise of letting third parties into your house or codebase, where I discussed the...
-

 284Surveillance
284SurveillanceTor Messenger Now Available for Mac, Linux and Windows
Tor team is one step closer to launch the Tor messenger as they have finally launched the first beta version after three...
-

 314Cyber Crime
314Cyber CrimeScammers Targeting PayPal Users with “Suspicious Activity” Phishing Scam
PayPal has been one of the most attractive platforms for the hackers and spammers. During a recent year, PayPal users have been...
-

 128News
128NewsWIN Free Gadgets, Pen Drives, T-Shirts using Gokano
GOKANO is a new service that offers you gadgets, electronics, free t-shirts and many more things. Now winning is just like a...
-
 226Software
226SoftwareTOR releases Anonymous Instant Messenger – Here’s how to get it
The Tor Project has officially launched the first beta version of Tor Messenger, an open source and Encrypted instant messaging client that...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




