Featured News
-
 320Data Security
320Data SecurityThe Economist’s Ad-Blocker was Hacked, Delivered Malware to Windows Users
Economist’s anti-ad blocking analytics service got hacked on 31st October (company’s officials didn’t disclose until 5th November) and the exposed site made...
-

 325Geek
325GeekWhich Programming Language Is Perfect For Me?
Short Bytes: Learning the programming is something that you can do at your own terms – either in the best universities of...
-

 148Data Security
148Data SecurityNew Android Malware Surfaced, Only Way Out Throw Away Your Phone
Researchers at Lookout Security have found a Shuanet malware that masquerades as some of the most downloaded apps like Facebook, Twitter, and...
-

 179Data Security
179Data SecurityRansomware Found Targeting Linux Servers and Coding Repositories
Malware operators are taking aim at Web developers. A newly discovered ransomware is attacking Linux Web servers, taking aim at Web development environments...
-

 78Data Security
78Data SecurityHIDDEN IN PLAIN SIGHT: BRUTE FORCING SLACK PRIVATE FILES
Last year we switched to using Slack for all our internal communication and it’s working out nicely. It’s very developer centric in...
-

 95Vulnerabilities
95VulnerabilitiesThe Vulnerability That Will Rock the Entire Java World
Major bug goes unnoticed in one of Java’s most popular libraries, despite getting a CVSS vulnerability score of 10 Back in late...
-

 123Data Security
123Data SecurityEpic Fail: Power Worm Ransomware Accidentally Destroys Victim’s Data During Encryption
A variant of the Power Worm ransomware is infecting computers, encrypting their data files, and throwing away the encryption key, all because...
-
 101Data Security
101Data SecurityCIA Email Hackers Return With Major Law Enforcement Breach
HACKERS WHO BROKE into the personal email account of CIA Director John Brennan have struck again. This time the group, which goes...
-

 202Incidents
202IncidentsFCC fines Cox for falling for Lizard Squad scam, exposing customer data
“Hi, I’m from IT” call yielded access to customer records, lulz; Cox fined $596k. What’s the cost of giving up customers’ information...
-

 274Hacked
274HackedHow An SQL Injection Attack Works: Infographic
Short Bytes: Just like DDoS attacks, SQL injection attacks too are pretty infamous in the internet world. They are responsible for about...
-
 238Cyber Events
238Cyber EventsBosnian Band Releases Epic Video Song in Support of The Pirate Bay
A Bosnian music group has released a song in support of The Pirate Bay (TPB) and bashing the authorities on copyright related...
-

 376Cyber Events
376Cyber EventsUK companies have ‘misplaced confidence’ on cyber security
A majority of British businesses are convinced that they won’t fall victim to a damaging cyber attack, despite that fact that high-profile...
-

 357Cyber Crime
357Cyber CrimeNSA-proof ProtonMail Service DDoSed, Forced to Pay $6000 as Ransom
In 2014, a team of privacy advocates launched ProtonMail and claimed that it’s an NSA-proof email service. The service was such a massive hit...
-

 99Cyber Crime
99Cyber CrimeNearly 157,000 TalkTalk customers had their personal details hacked
TalkTalk talks numbers - revealing that "only 4%" of its users were affected by the hacking attack on its systems.
-

 283How To
283How ToHow Search Engine Works and Makes Your Life Easier?
Short Bytes: Search Engine is a software that allows the display of relevant webpage results based on the search query input by...
-

 150Data Security
150Data SecurityQuick Q&A with the Author of Mabouia, First Mac OS X Ransomware
Rafael Salema Marques is a Brazilian cyber-security researcher and, above all, a devoted Mac user. Today, Mr. Marques published a LinkedIn blog...
-

 84Cyber Crime
84Cyber CrimeProtonMail hit with another DDoS attack
After experiencing an onslaught of DDoS attacks, which saw it hand over the ransom that was demanded, ProtonMail has once again been...
-
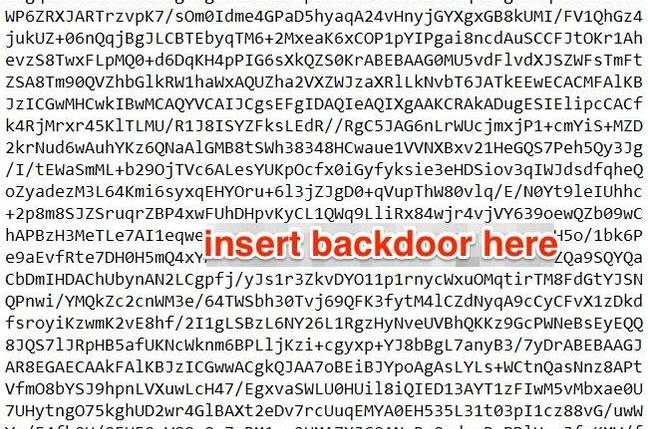
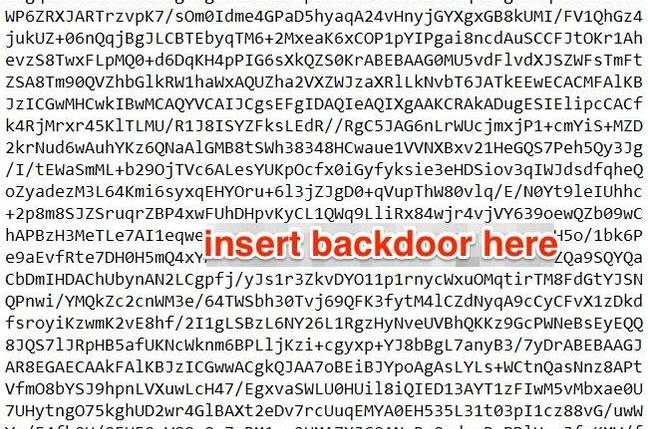 92Data Security
92Data SecurityTop FBI lawyer: You win, we’ve given up on encryption backdoors
We’re your servants, says general counsel unconvincingly After spending months pressuring tech companies to add backdoors into their encryption software, the FBI...
-
 82Malware
82MalwarejQuery.min.php Malware Affects Thousands of Websites
Fake jQuery injections have been popular among hackers since jQuery itself went mainstream and became one of the most widely adopted JavaScript...
-
 107Data Security
107Data SecurityCrypto e-mail service pays $6,000 ransom, gets taken out by DDoS anyway
Follow-on attacks show capabilities “commonly possessed by state-sponsored actors.” A provider of end-to-end encrypted e-mail said it paid a ransom of almost...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




