Featured News
-

 169Data Security
169Data SecurityBrazilian Army Gets Hacked Following Cyber-Games Cheating Accusations
Hackers leak data of over 7,000 officers. Hackers who declined to name themselves hacked the servers of the Brazilian Army, and later leaked...
-

 234Malware
234MalwarePoS Malware Spread via Weaponized Microsoft Word Documents
Distributed via Word files and the Angler EK. Cyber-crooks are diversifying their activities by including as many threats as possible inside their malware-delivery...
-

 156Data Security
156Data SecurityCSI: CYBER SOMEHOW DIDN’T GET CAR HACKING TOTALLY WRONGCSI: CYBER SOMEHOW DIDN’T GET CAR HACKING TOTALLY WRONG
CSI: Cyber is known more for absurd drama than technical coherence, but it’s a big deal that hacking’s become so visible that...
-

 270Data Security
270Data SecurityResearchers Discover Two New Strains of POS Malware
Point of sale malware has gotten more sophisticated as we inch closer to the two-year anniversary of the Target data breach. Now,...
-

 315News
315NewsDid Russian Hackers Breach Spotify Accounts?
Newsweek has revealed that Spotify (One of the giants of the Music industry) faced a hacking attack last week and thousands of...
-

 203Cyber Crime
203Cyber CrimeJail Time for US Citizen Who Posted Pro-ISIS GIF Image
The US government has started arresting people who are showing support for the so-called Islamic State (IS, previously ISIS/ISIL) on social media. Whether it be...
-

 161Hacked
161HackedThis Flaw Lets Hackers Completely Control Any Android Phone With Single Click
Short Bytes: A new discovery at the PacSec Conference at Tokyo unveiled a great threat prevailing in the Android OS that hands...
-

 73Cyber Crime
73Cyber CrimeJail for British DDoS attacker, who said too much on Twitter
Although it's far from always possible to determine the perpetrators of a denial-of-service attack and bring them to justice, there are plenty...
-

 98Vulnerabilities
98VulnerabilitiesOil and Gas Companies Indirectly Put at Risk by Vulnerabilities in ERP Systems
Vulnerabilities in SAP and Oracle products expose companies to crippling attacks, oil market fraud or equipment sabotage. A talk delivered at the Black...
-

 157Privacy
157PrivacyReclaim privacy with operational security says Snowden
Edward Snowden has been offering advice on operational security to ordinary people, advocating, among other things, two-factor authentication and encryption.
-

 74Cyber Crime
74Cyber Crime7 things you need to know about car hacking
Car hacking may sound like something out of the latest Die Hard or James Bond film, but it’s newsworthy, real and likely...
-
 132Incidents
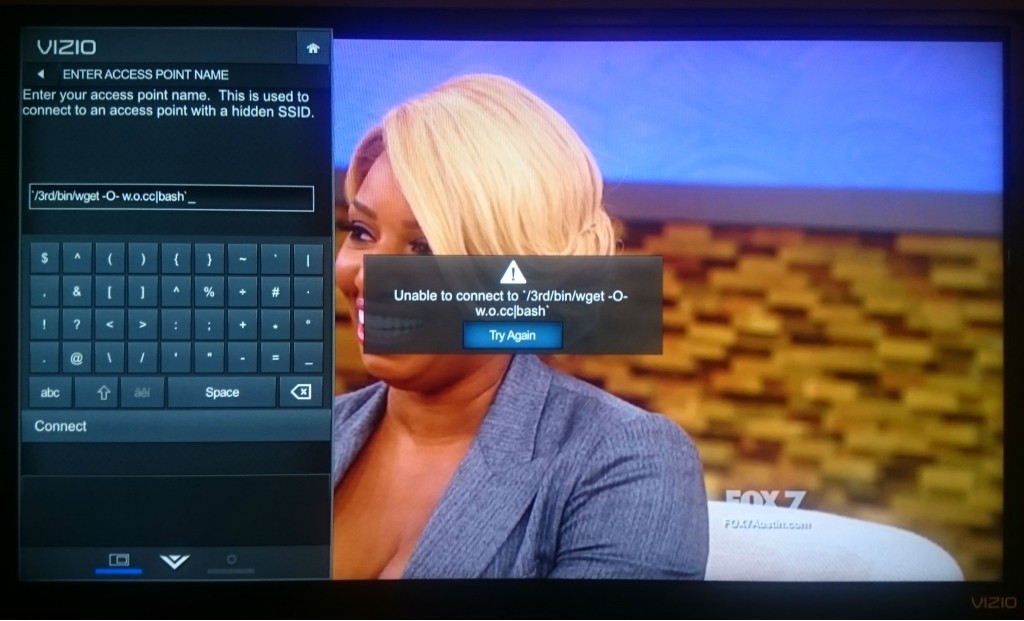
132IncidentsVizio Smart TV Hacked to Give Attackers Access to Home WiFi Network
Avast confirms the recent Vizio Smart TV snooping scandal Security researchers at Avast have hacked a Vizio smart TV and gained access...
-
 147Vulnerabilities
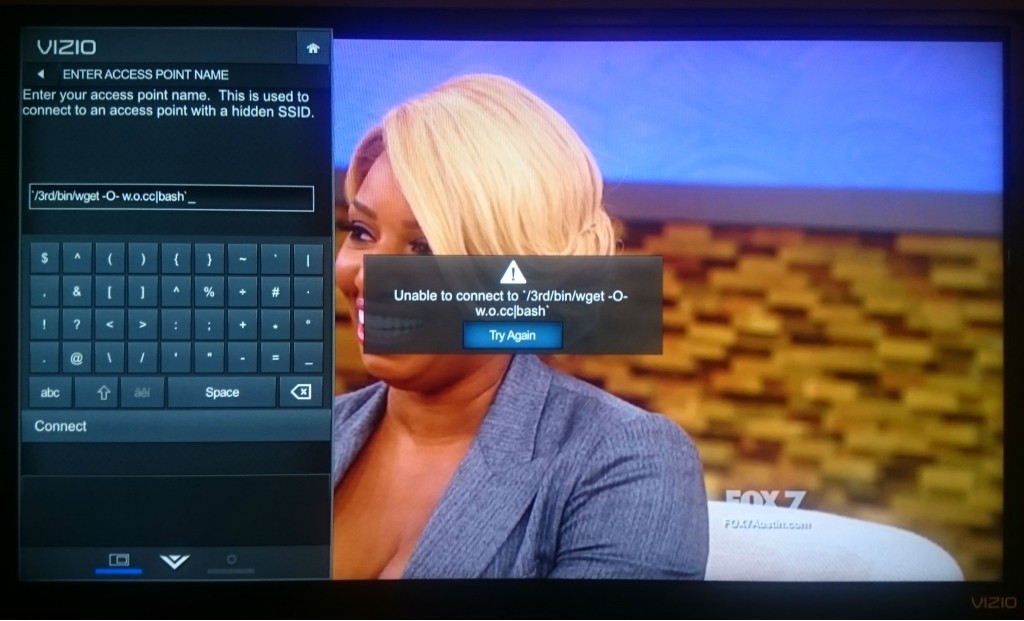
147VulnerabilitiesChrome for Android Has a Hidden Vulnerability, Quite Simple to Exploit
Google’s Chrome staff got in contact with the security researcher and has already started working on a fix A Chinese security researcher...
-
 244Incidents
244IncidentsFour Indicted in Massive JP Morgan Chase Hack
FEDERAL AUTHORITIES HAVE indicted four men on charges that they hacked into multiple financial institutions and operated a stock-pumping scheme and online...
-
 92Data Security
92Data SecurityTor: FBI Paid CMU $1 Million to De-Anonymize Users
More than a year ago, the Tor Project patched its software against a vulnerability being exploited by researchers at Carnegie Mellon University,...
-
 168Malware
168MalwarePay or we’ll knock your site offline—DDoS-for-ransom attacks surge
One of the Internet’s oldest and crudest attacks experiences a resurgence. A number of sites have been hit by distributed denial-of-service attacks...
-

 298Tricks & How To's
298Tricks & How To'sHack Chat | Private Disappearing Chatrooms
If you would like to build your personal private chatting system without any hassle besides entering a different Address in your web...
-
 76Cyber Crime
76Cyber CrimeFastMail the latest victim of a sustained DDoS offensive
The premium email provider FastMail has revealed that a cybercriminal has launched multiple DDoS attacks on its systems and made a ransom...
-

 177Hacked
177HackedRussia Doesn’t Want Its Users’ Twitter Data To Leave Country
Short Bytes: Russia has yet again displayed stifling laws as it demanded the micro-blogging site Twitter to set up local data centres...
-

 242Hacked
242HackedTor Director Accuses FBI of Spending $1 Million to Attack Tor Users
Short Bytes: In a blog post, Tor Director has outlined the unethical ways that were employed by FBI to unmask Tor users....
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




