Featured News
-
 317Vulnerabilities
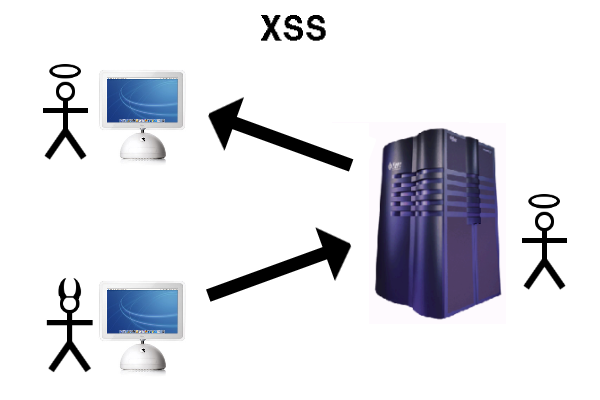
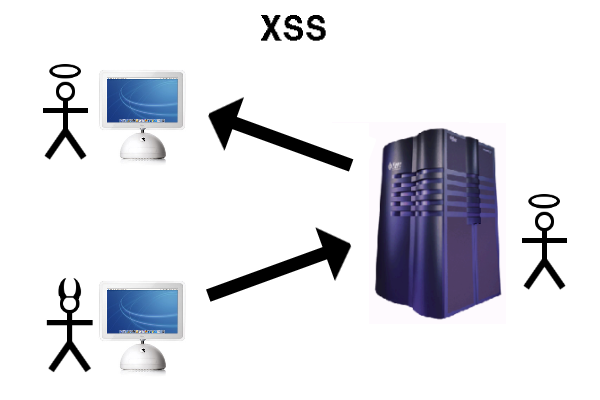
317VulnerabilitiesXSS in Hidden Input Fields
At PortSwigger, we regularly run pre-release builds of Burp Suite against an internal testbed of popular web applications to make sure it’s...
-
 324Data Security
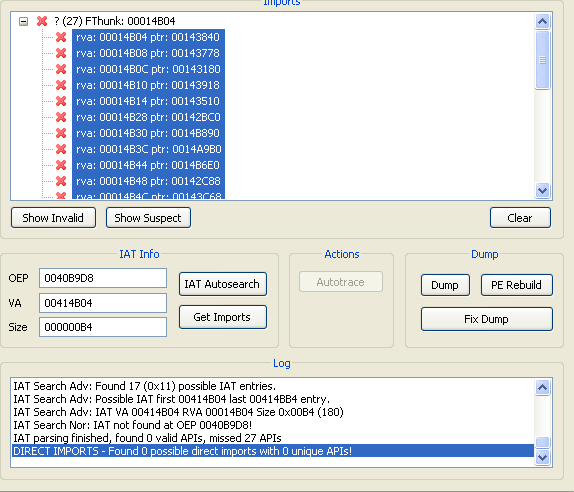
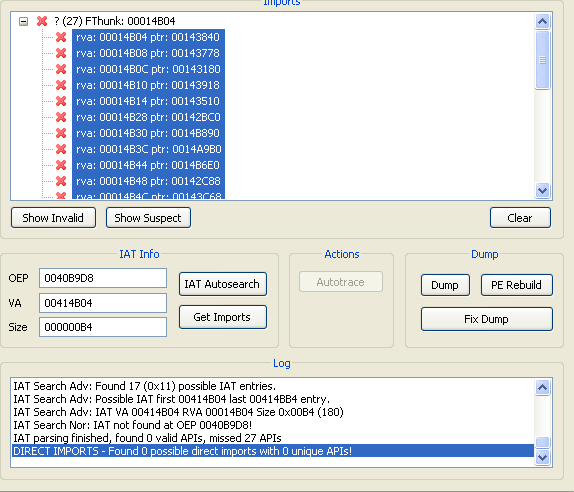
324Data SecurityA Guide to Malware Binary Reconstruction
Often we come across times where binary reconstruction while analyzing malware / unpacking malware is required . Taking leverage of automated tools...
-

 341Data Security
341Data SecurityBitLocker popper uses Windows authentication to attack itself
Microsoft squashes offline logic flaw that makes lost laptops dynamite. Blackhat Europe Synopsys security boffin Ian Haken says un-patched PCs in enterprises...
-

 138Data Security
138Data SecurityLinux.Encoder.1 Ransomware Spreads to 3,000 Websites
Expect a new ransomware version in the coming weeks.The Linux.Encoder.1 ransomware, a special strand that has a taste for Web hosting and...
-

 309Data Security
309Data SecurityHacker Develops Undisputed KillerRat to Spy on Windows PCs
Egyptian Hacker Uses njRAT Codebase to Create KillerRat — The RAT goes completely hidden upon scanning. A new Remote Access Trojan/RAT has...
-

 269Geek
269GeekPhotoshop Fail: Sikh Man in Canada Smeared as Suspected Paris Terrorist
Someone photoshopped this guy’s pic from an iPad to a Quran and the mainstream media took it as real and made it viral....
-

 202News
202NewsCyberwar games lead to foul play resulting in leaked Brazilian Army data
Earlier this week the servers of Brazilian Army got hacked leading to private details of around 7,000 military officials getting stolen. Hackers...
-

 230Geek
230GeekFacebook’s New Feature Will Let You Search within Individual Profiles
Going through Facebook profiles will now be a different experience with Facebook experimenting a new feature, which will allow anyone visiting user...
-

 306News
306NewsAnonymous Waging War on ISIS, Vows to Hunt Down Terrorists After Paris Attacks
The online hacktivist group Anonymous has announced a new series of cyber attacks against the ISIS/ISIL terrorist group. This Friday, terrorists targeted...
-

 178Malware
178MalwareMore POS malware, just in time for Christmas
VXers stuff evidence-purging malware in retailer stockings. Threat researchers are warning of two pieces of point of sales malware that have gone...
-
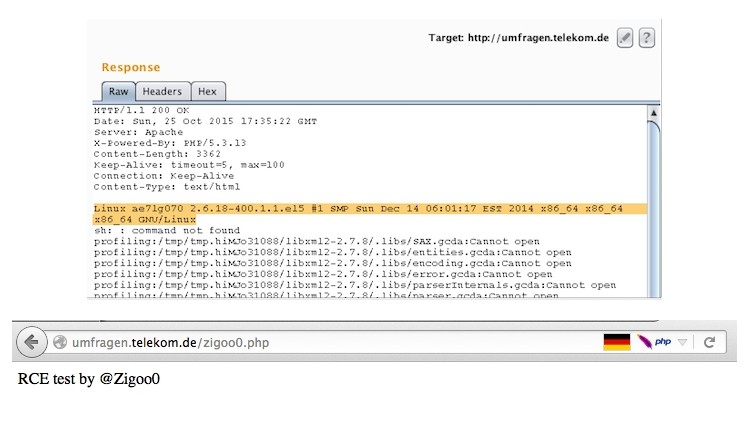
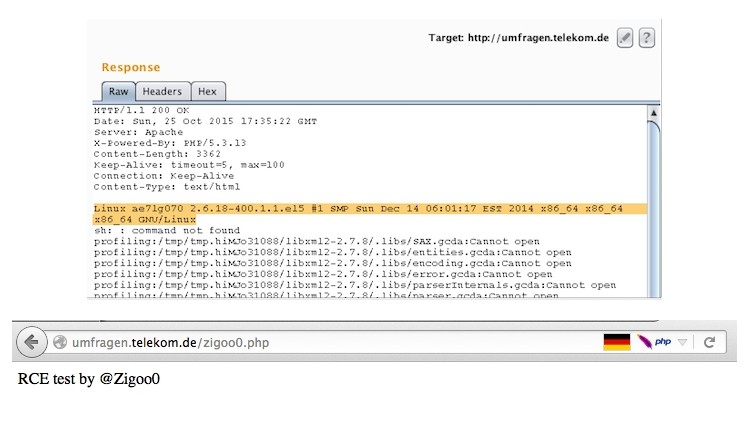 134Vulnerabilities
134VulnerabilitiesRCE Vulnerability Fully Compromises Deutsche Telekom Server
Attackers could have had full control over DT’s Web server. Independent Egyptian security researcher Ebrahim Hegazy has found another vulnerability, and this one...
-

 262Hacked
262HackedYes, You Are Now Allowed To Hack Your WiFi Router
Short Bytes: After facing tons of criticism over the new proposed rules governing the 5GHz spectrum devices (basically your WiFi routers), the...
-
 93Vulnerabilities
93VulnerabilitiesPNG pongs: critical bug patched in ubiquitous libpng
Crafted image crashes apps, server processes. This will not be fun: the graphics processing library libpng has a vulnerability and needs to...
-

 161Data Security
161Data SecurityAnonymous Announces Payback for ISIS Paris Attacks
It didn’t take long for Anonymous members to rally and swear payback for the recent ISIS terror attacks that took place in...
-

 174Geek
174GeekSecurity Flaw in Samsung Galaxy Devices Lets Attackers Record Phone Calls
A telephone tower-like device (IMSI-catcher) can be used for recording phone calls from the latest versions of Samsung Galaxy, demonstrated by two...
-

 303Hacked
303HackedAnonymous Announces Revenge Campaign For Paris Attacks By ISIS #OpParis
Short Bytes: In response to the Paris attacks, Hacktivist group Anonymous was quick to issue a warning to its long-time foe ISIS....
-

 300News
300NewsFacebook blocked anti-ISIS group setup by Anonymous hours before Paris attacks.
Just hours before the Paris attacks, Facebook blocked a group “Report ISIS accounts” that was made by anonymous members for unmasking ISIS...
-

 232Geek
232GeekJava Makes a Comeback, One in Every Five Lines of Code Is Now Written in Java
Short Bytes: The popularity of programming languages is measured using various factors. The TIOBE index is often used as the best way...
-

 378Geek
378GeekSamsung Galaxy S6 Edge Saves Guy’s Life During Paris Terror Attacks
Smartphones have taken our lives to a different level, besides helping us to connect with others, they also save lives; just like...
-

 265Geek
265GeekFacebook’s Photo Magic Can Scan Your Camera Roll to find Photos of Your Friends
Facebook’s Photo Magic Can Scan Users’ Camera Roll to find Photos of their Friends — We learned about Facebook’s new feature called...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




