Featured News
-

 327Geek
327GeekWhich Programming Language Is Perfect For Me?
Short Bytes: Learning the programming is something that you can do at your own terms – either in the best universities of...
-

 149Data Security
149Data SecurityNew Android Malware Surfaced, Only Way Out Throw Away Your Phone
Researchers at Lookout Security have found a Shuanet malware that masquerades as some of the most downloaded apps like Facebook, Twitter, and...
-

 179Data Security
179Data SecurityRansomware Found Targeting Linux Servers and Coding Repositories
Malware operators are taking aim at Web developers. A newly discovered ransomware is attacking Linux Web servers, taking aim at Web development environments...
-

 78Data Security
78Data SecurityHIDDEN IN PLAIN SIGHT: BRUTE FORCING SLACK PRIVATE FILES
Last year we switched to using Slack for all our internal communication and it’s working out nicely. It’s very developer centric in...
-

 95Vulnerabilities
95VulnerabilitiesThe Vulnerability That Will Rock the Entire Java World
Major bug goes unnoticed in one of Java’s most popular libraries, despite getting a CVSS vulnerability score of 10 Back in late...
-

 123Data Security
123Data SecurityEpic Fail: Power Worm Ransomware Accidentally Destroys Victim’s Data During Encryption
A variant of the Power Worm ransomware is infecting computers, encrypting their data files, and throwing away the encryption key, all because...
-
 102Data Security
102Data SecurityCIA Email Hackers Return With Major Law Enforcement Breach
HACKERS WHO BROKE into the personal email account of CIA Director John Brennan have struck again. This time the group, which goes...
-

 202Incidents
202IncidentsFCC fines Cox for falling for Lizard Squad scam, exposing customer data
“Hi, I’m from IT” call yielded access to customer records, lulz; Cox fined $596k. What’s the cost of giving up customers’ information...
-

 274Hacked
274HackedHow An SQL Injection Attack Works: Infographic
Short Bytes: Just like DDoS attacks, SQL injection attacks too are pretty infamous in the internet world. They are responsible for about...
-
 239Cyber Events
239Cyber EventsBosnian Band Releases Epic Video Song in Support of The Pirate Bay
A Bosnian music group has released a song in support of The Pirate Bay (TPB) and bashing the authorities on copyright related...
-

 377Cyber Events
377Cyber EventsUK companies have ‘misplaced confidence’ on cyber security
A majority of British businesses are convinced that they won’t fall victim to a damaging cyber attack, despite that fact that high-profile...
-

 358Cyber Crime
358Cyber CrimeNSA-proof ProtonMail Service DDoSed, Forced to Pay $6000 as Ransom
In 2014, a team of privacy advocates launched ProtonMail and claimed that it’s an NSA-proof email service. The service was such a massive hit...
-

 99Cyber Crime
99Cyber CrimeNearly 157,000 TalkTalk customers had their personal details hacked
TalkTalk talks numbers - revealing that "only 4%" of its users were affected by the hacking attack on its systems.
-

 283How To
283How ToHow Search Engine Works and Makes Your Life Easier?
Short Bytes: Search Engine is a software that allows the display of relevant webpage results based on the search query input by...
-

 151Data Security
151Data SecurityQuick Q&A with the Author of Mabouia, First Mac OS X Ransomware
Rafael Salema Marques is a Brazilian cyber-security researcher and, above all, a devoted Mac user. Today, Mr. Marques published a LinkedIn blog...
-

 84Cyber Crime
84Cyber CrimeProtonMail hit with another DDoS attack
After experiencing an onslaught of DDoS attacks, which saw it hand over the ransom that was demanded, ProtonMail has once again been...
-
 92Data Security
92Data SecurityTop FBI lawyer: You win, we’ve given up on encryption backdoors
We’re your servants, says general counsel unconvincingly After spending months pressuring tech companies to add backdoors into their encryption software, the FBI...
-
 82Malware
82MalwarejQuery.min.php Malware Affects Thousands of Websites
Fake jQuery injections have been popular among hackers since jQuery itself went mainstream and became one of the most widely adopted JavaScript...
-
 108Data Security
108Data SecurityCrypto e-mail service pays $6,000 ransom, gets taken out by DDoS anyway
Follow-on attacks show capabilities “commonly possessed by state-sponsored actors.” A provider of end-to-end encrypted e-mail said it paid a ransom of almost...
-
 272Cyber Events
272Cyber EventsAnonymous stands true to its words, leaks more data on alleged KKK members
The online hacktivist Anonymous released what they called a list of Ku Klux Klan members and sympathizers on Thursday. As reported earlier, the Anonymous...
The Latest
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
 Malware
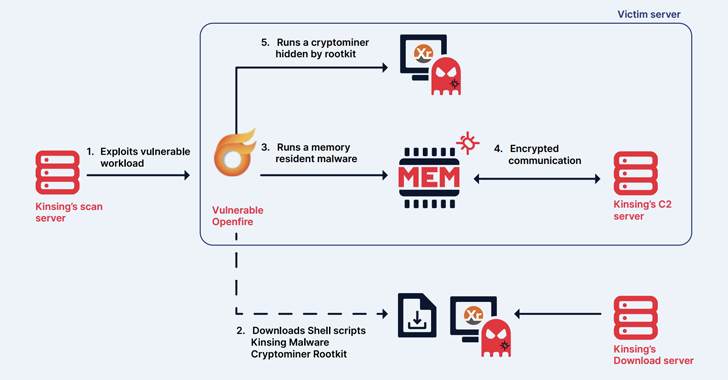
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
 Malware
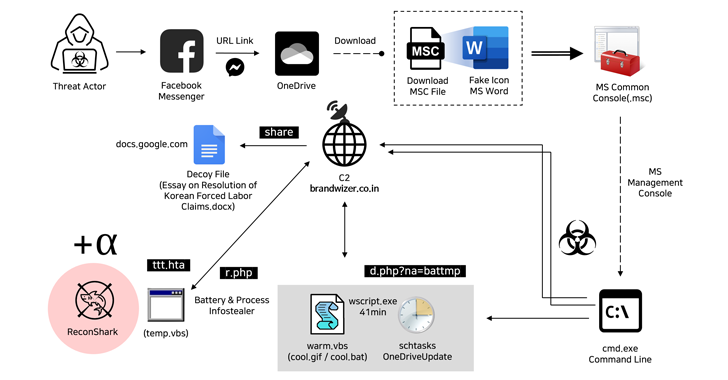
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Malware
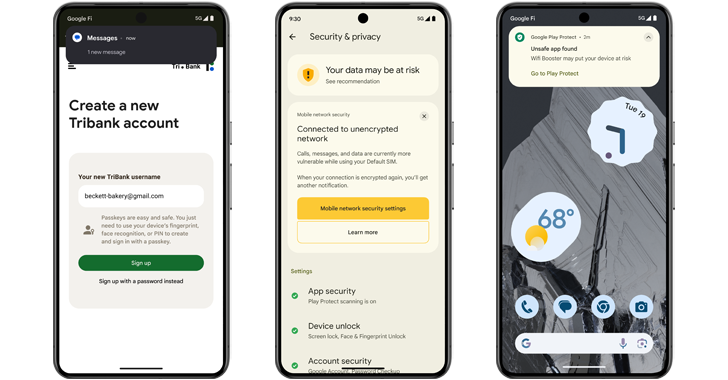
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions
-
 Vulnerabilities
Vulnerabilities(Cyber) Risk = Probability of Occurrence x Damage
-
 Malware
MalwareEbury Botnet Malware Compromises 400,000 Linux Servers Over Past 14 Years
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Vulnerabilities
VulnerabilitiesVMware Patches Severe Security Flaws in Workstation and Fusion Products
-
 Vulnerabilities
VulnerabilitiesNew Chrome Zero-Day Vulnerability CVE-2024-4761 Under Active Exploitation




