Featured News
-

 210Data Security
210Data SecuritySecurity Researcher Creates Tool to Extract Passwords from KeePass Databases
Denis Andzakovic, a security researcher for Security Assessment, has created a tool that can fool the KeePass password manager into exporting its...
-
 268Vulnerabilities
268VulnerabilitiesvBulletin password hack fuels fears of serious Internet-wide 0-day attacks
Software maker issued security patch hours after reports surfaced it was breached. Developers of the vBulletin software package for website forums released...
-

 73Cyber Crime
73Cyber CrimeUS man jailed for attempting to hire cybercriminal to wipe fines
A US man who posted an advert on Craigslist requesting the services of a cybercriminal has been handed a two-year prison sentence....
-

 427Cyber Crime
427Cyber CrimeGermany’s Industrie 4.0 – the challenges in IT‑Security
Time after time we have experienced revolutions in our societies, in the way we work and thus in the Industry. In the...
-

 250Hacked
250HackedKim Dotcom Is Building His Own Private Internet Called Meganet
Short Bytes: Kim Dotcom, the founder of notorious file-sharing website Megaupload, has said that he is working on an internet alternative called...
-

 166Hacked
166HackedBaidu’s Corrupt SDK Puts 100 Million Android Users Open To Backdoor Attacks
Short Bytes: Baidu, the Chinese analogous to Google has distributed a software development kit (SDK), Moplus, which has reportedly made over 100...
-

 251Geek
251GeekLearn How To Work On Git and GitHub With Its New Free Training Course
Short Bytes: Are you new to the world of Git and GitHub, finding it a little bit scary? Well, to erase these...
-
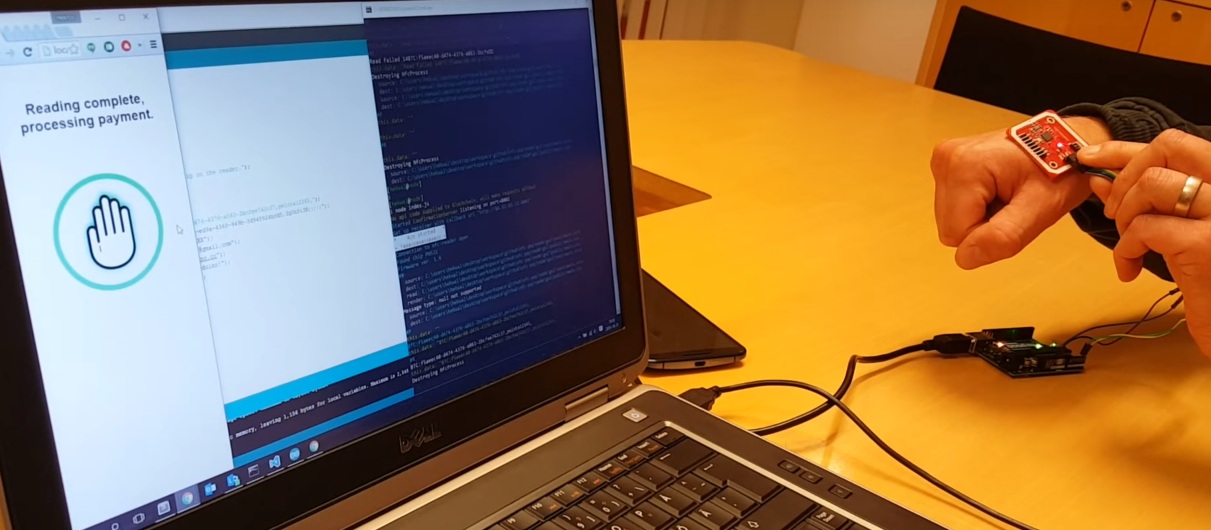
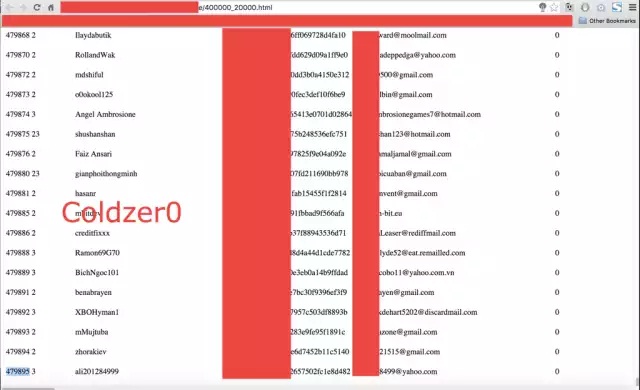
 106Data Security
106Data SecurityThis Chip Is Implanted Under The Skin And Used To Pay For Things Using Bitcoin
Wallets are becoming more integrated with other things. Soon, we might all use our phones as a way to pay for things....
-
 145Incidents
145IncidentsThird man arrested over TalkTalk hack as Vodafone reveals cyberattack of its own
Vodafone is the second British telecommunications company in two weeks to be on the receiving end of a serious hack. Yet another...
-

 211Incidents
211IncidentsMaine Mendoza’s Twitter account hacked by ‘Anonymous Philippines’
A group of hackers who claimed responsibility for the hacking of numerous government and even Chinese websites since 2012 has found a...
-
 132Data Security
132Data SecurityBrowser-Based iOS 9.1/9.2 Jailbreak Wins $1M Bounty, Will Be Sold for Corporate and Government Use
Earlier this month, exploit acquisition platform Zerodium debuted an iOS 9 bug bounty that would pay out up to three million dollars...
-

 116Data Security
116Data SecurityAndroid Malware Disguises itself as MS Word Doc, Spies on Your Phone
Researchers have discovered an Android malware disguising itself as a Microsoft word document which triggers a malicious code once opened. This Android malware was...
-

 339Hacked
339HackedHackers Win $1 Million Bounty for Remotely Hacking iPhones Running iOS 9
Short Bytes: Zerodium’s million dollar iOS 9 jailbreak bounty program has expired and it has resulted in a new iOS jailbreak. But,...
-

 324Geek
324GeekLinus Torvalds Goes All Crazy And Angry Over Some ‘Sh*t Code’
Short Bytes: Linus Torvalds says, “Talk is cheap. Show me the code.” What if you show him some code and it pisses...
-

 184Data Security
184Data SecurityHow to exploit new Facebook feature to access personal photos of people without being their friend?
Facebook’s is always changing and its team is adding new functionality every couple of months. With new changes there are chances of...
-

 207Hacked
207HackedLatest Adobe Flash Zero-Day Bug Already Part of Angler and Nuclear Exploit Kits
Short Bytes: Adobe Flash Player continues to remain the favorite target of the cyber attackers. The recent zero-day exploits that were earlier...
-

 84Data Security
84Data SecurityYahoo’s “crypto witch” exploits web security feature, learns your site history
Timing attacks are an interesting part of computer security. As an extreme example, imagine that your computer took one second to verify...
-

 247Data Security
247Data SecuritySnapchat to save, modify and republish your private photos
Snapchat’s new term and conditions have resulted in outrage from its users and twitter has been flooded with tweets from users rejecting...
-

 120Data Security
120Data SecurityLeaving Laptops in Hotel Rooms: A Bad Idea
A laptop filled with data? An external HDD filled with even more data? There’s bound to be a phone – possibly two...
-

 326Data Security
326Data SecurityVodafone Hacked, Customers’ Personal Data, Banking Information Stolen
In the wake of the TalkTalk Scandal, Vodafone finally admitted that hackers did manage to steal around 20,000 Vodafone customers’ bank details....
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




