Featured News
-

 167Hacked
167HackedBaidu’s Corrupt SDK Puts 100 Million Android Users Open To Backdoor Attacks
Short Bytes: Baidu, the Chinese analogous to Google has distributed a software development kit (SDK), Moplus, which has reportedly made over 100...
-

 252Geek
252GeekLearn How To Work On Git and GitHub With Its New Free Training Course
Short Bytes: Are you new to the world of Git and GitHub, finding it a little bit scary? Well, to erase these...
-
 109Data Security
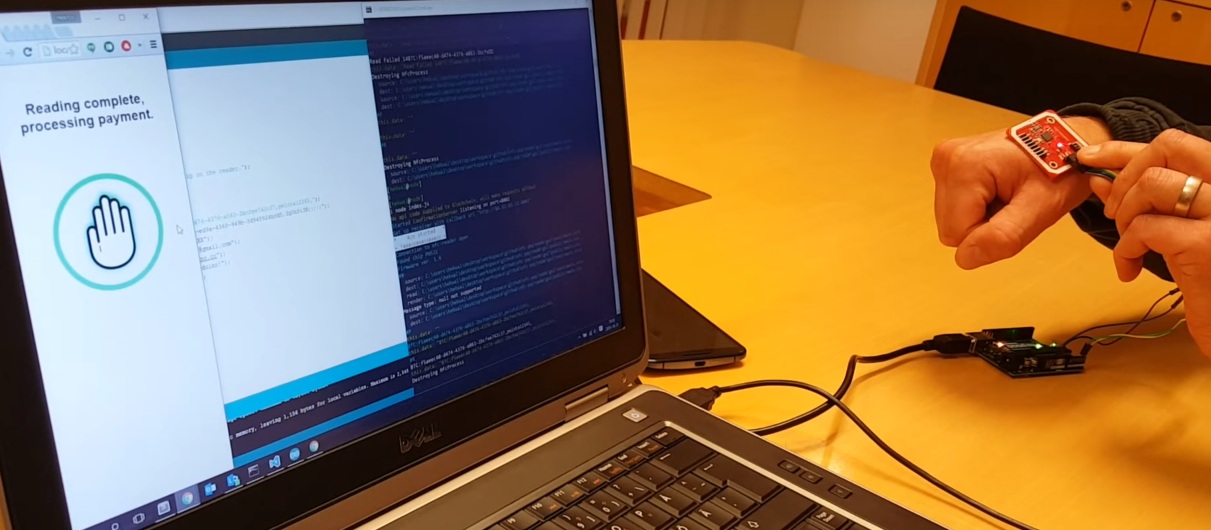
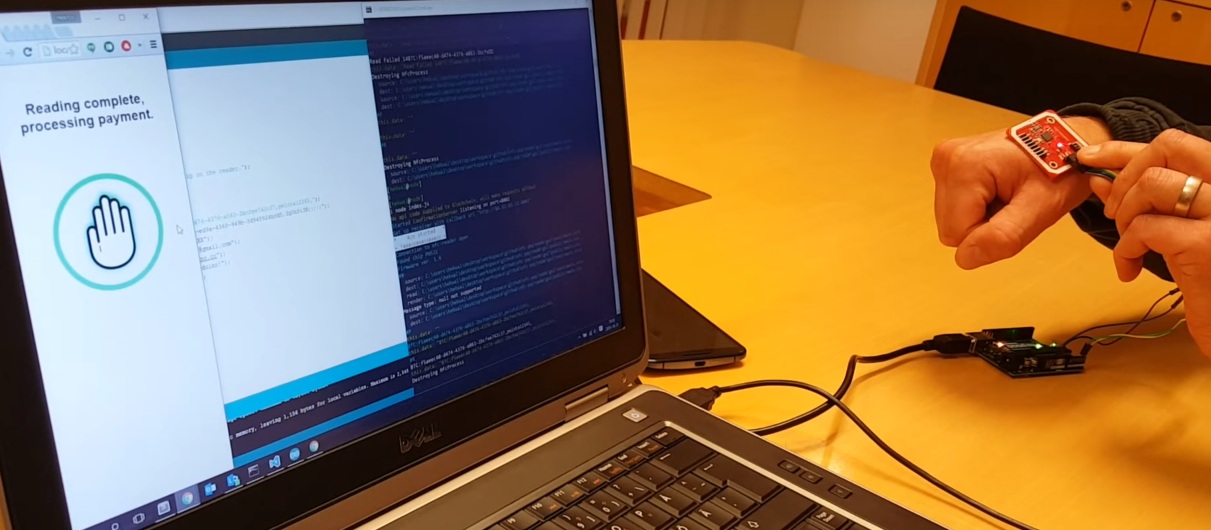
109Data SecurityThis Chip Is Implanted Under The Skin And Used To Pay For Things Using Bitcoin
Wallets are becoming more integrated with other things. Soon, we might all use our phones as a way to pay for things....
-
 149Incidents
149IncidentsThird man arrested over TalkTalk hack as Vodafone reveals cyberattack of its own
Vodafone is the second British telecommunications company in two weeks to be on the receiving end of a serious hack. Yet another...
-

 212Incidents
212IncidentsMaine Mendoza’s Twitter account hacked by ‘Anonymous Philippines’
A group of hackers who claimed responsibility for the hacking of numerous government and even Chinese websites since 2012 has found a...
-
 135Data Security
135Data SecurityBrowser-Based iOS 9.1/9.2 Jailbreak Wins $1M Bounty, Will Be Sold for Corporate and Government Use
Earlier this month, exploit acquisition platform Zerodium debuted an iOS 9 bug bounty that would pay out up to three million dollars...
-

 119Data Security
119Data SecurityAndroid Malware Disguises itself as MS Word Doc, Spies on Your Phone
Researchers have discovered an Android malware disguising itself as a Microsoft word document which triggers a malicious code once opened. This Android malware was...
-

 342Hacked
342HackedHackers Win $1 Million Bounty for Remotely Hacking iPhones Running iOS 9
Short Bytes: Zerodium’s million dollar iOS 9 jailbreak bounty program has expired and it has resulted in a new iOS jailbreak. But,...
-

 329Geek
329GeekLinus Torvalds Goes All Crazy And Angry Over Some ‘Sh*t Code’
Short Bytes: Linus Torvalds says, “Talk is cheap. Show me the code.” What if you show him some code and it pisses...
-

 188Data Security
188Data SecurityHow to exploit new Facebook feature to access personal photos of people without being their friend?
Facebook’s is always changing and its team is adding new functionality every couple of months. With new changes there are chances of...
-

 209Hacked
209HackedLatest Adobe Flash Zero-Day Bug Already Part of Angler and Nuclear Exploit Kits
Short Bytes: Adobe Flash Player continues to remain the favorite target of the cyber attackers. The recent zero-day exploits that were earlier...
-

 85Data Security
85Data SecurityYahoo’s “crypto witch” exploits web security feature, learns your site history
Timing attacks are an interesting part of computer security. As an extreme example, imagine that your computer took one second to verify...
-

 247Data Security
247Data SecuritySnapchat to save, modify and republish your private photos
Snapchat’s new term and conditions have resulted in outrage from its users and twitter has been flooded with tweets from users rejecting...
-

 120Data Security
120Data SecurityLeaving Laptops in Hotel Rooms: A Bad Idea
A laptop filled with data? An external HDD filled with even more data? There’s bound to be a phone – possibly two...
-

 330Data Security
330Data SecurityVodafone Hacked, Customers’ Personal Data, Banking Information Stolen
In the wake of the TalkTalk Scandal, Vodafone finally admitted that hackers did manage to steal around 20,000 Vodafone customers’ bank details....
-

 83Data Security
83Data SecurityHome Network Analysis: DVRs and my Network Interact
My last on-topic post pontificated about the dangers and surprise of letting third parties into your house or codebase, where I discussed the...
-

 278Surveillance
278SurveillanceTor Messenger Now Available for Mac, Linux and Windows
Tor team is one step closer to launch the Tor messenger as they have finally launched the first beta version after three...
-

 310Cyber Crime
310Cyber CrimeScammers Targeting PayPal Users with “Suspicious Activity” Phishing Scam
PayPal has been one of the most attractive platforms for the hackers and spammers. During a recent year, PayPal users have been...
-

 122News
122NewsWIN Free Gadgets, Pen Drives, T-Shirts using Gokano
GOKANO is a new service that offers you gadgets, electronics, free t-shirts and many more things. Now winning is just like a...
-
 222Software
222SoftwareTOR releases Anonymous Instant Messenger – Here’s how to get it
The Tor Project has officially launched the first beta version of Tor Messenger, an open source and Encrypted instant messaging client that...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




