Featured News
-

 192Geek
192GeekFacebook, WhatsApp Users can be tracked down by hackers
A group of researchers have demonstrated how locations of Facebook and WhatsApp users can be exposed by a security flaw in 4G networks....
-

 434Password
434Password11‑year‑old sets up cryptographically secure password business
An 11-year-old girl from New York has set up her own business selling cryptographically secure passwords, using a technique known as diceware.
-

 130Cyber Crime
130Cyber CrimeThe great car hacking debate
Can cars be hacked remotely or is the idea of remotely hackable cars still only a hypothetical threat? Evidence is presented to...
-
 204Hacked
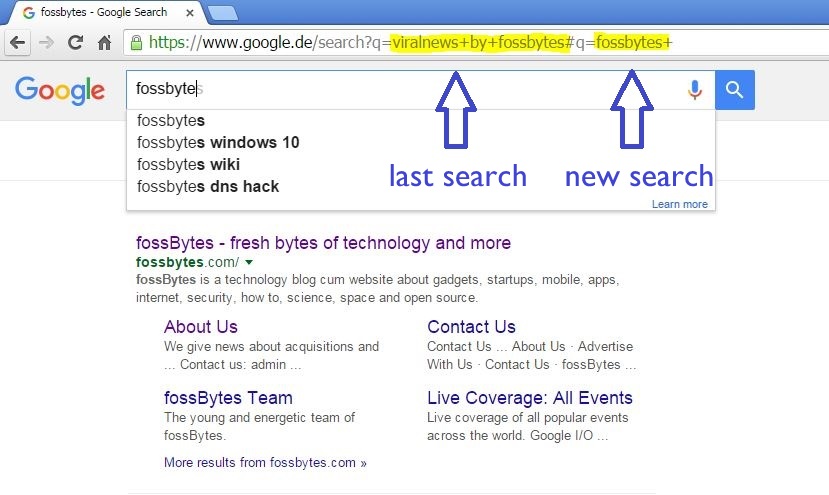
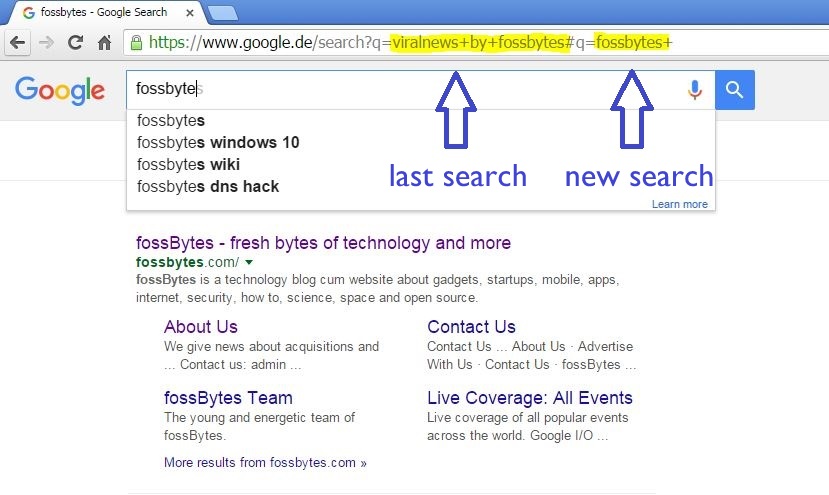
204HackedHow Innocent Copy-Paste Leaks Your Previous Embarrassing Google Searches
Short Bytes: Our innocent habit of copy-paste is reflected when we send the URLs of search pages as some reference to our...
-
 196Malware
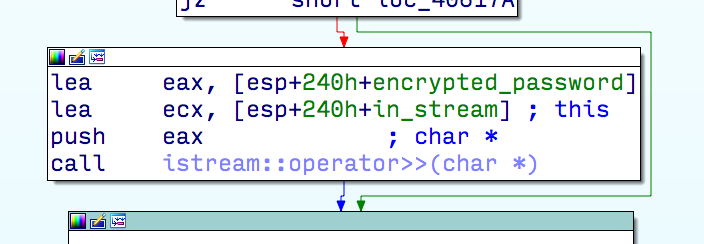
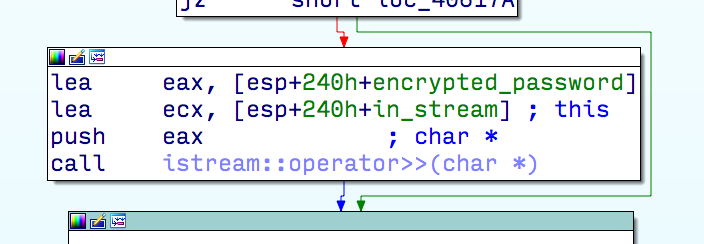
196MalwareMulti-stage exploit installing trojan
ESET researchers receive and analyze thousands of new malware samples every day. Earlier this year, one of them caught our attention because...
-
 95Data Security
95Data SecurityGoogle HTTP Search, yes, it is still possible
Google began to implement SSL on its search engine back in 2010. First on its own domain name, then as a...
-

 166Vulnerabilities
166VulnerabilitiesFewer IPsec VPN Connections at Risk from Weak Diffie-Hellman
A challenge has been made against one of the conclusions in a potentially blockbuster academic paper on cryptographic weaknesses that may be...
-

 181Vulnerabilities
181VulnerabilitiesJaguar car hack in New Zealand
A Jaguar XFR may have been stolen using hacking techniques increasingly seen on keyless cars. This unidentified thief did not have the...
-

 292Cyber Events
292Cyber EventsAnonymous Vows To Leak Personal Information of 1,000 KKK Members
The online hacktivist Anonymous is planning to leak personal information of around 1000 members of the white supremacist Christian organization the Ku Klux Klan...
-
 221Geek
221GeekFacebook “Message Requests” Lets You Talk to People You’re Not Friends With
The most common problem you may face on social media platforms like Facebook is receiving unwanted messages from strangers. But, Facebook’s new feature...
-

 77Data Security
77Data SecurityUS Army Experts Call for military bug bounty program AVRP
US Army Military experts urge the establishment of an Army Vulnerability Response Program (AVRP), a sort of military bug bounty program. What...
-
 229Data Security
229Data SecurityTiming attack vulnerability in most Zeus server-sides
Timing attacks has proven practical since 96′ as shown in a paper by Paul C. Kocher. In his paper Paul demonstrate how,...
-
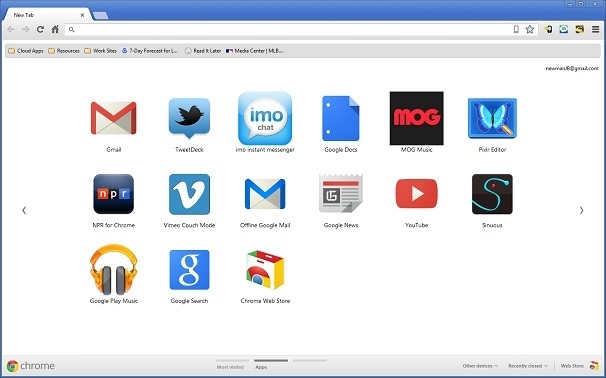
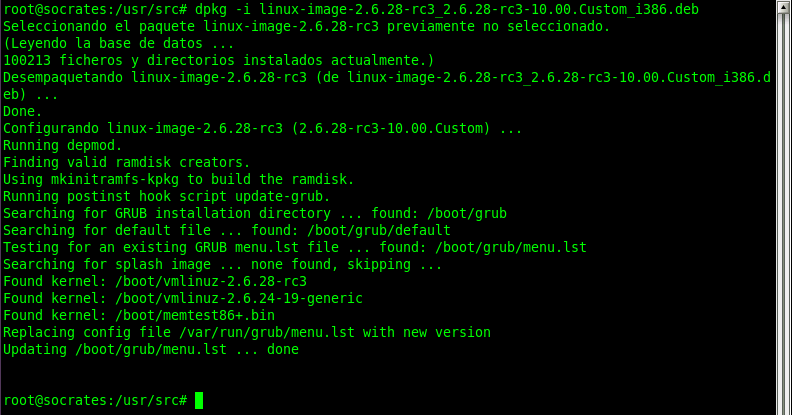
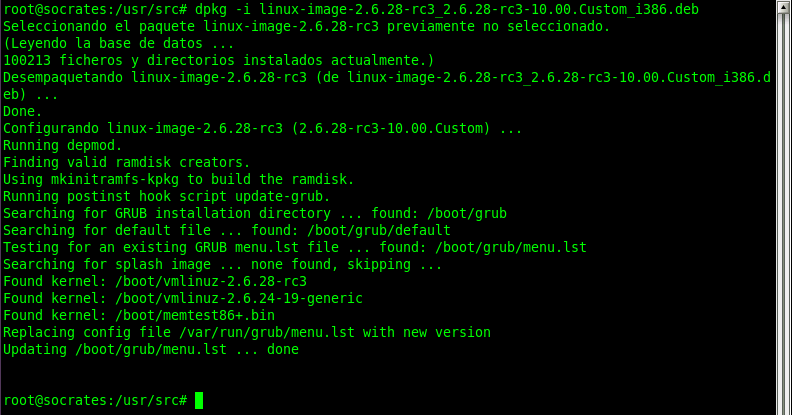
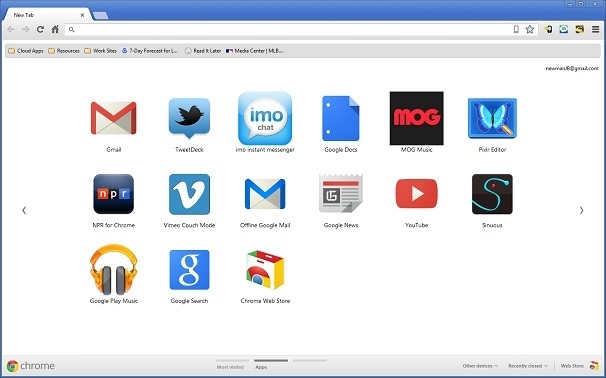 90Data Security
90Data SecurityFake Chrome browser replaces real thing and serves up unwanted ads
Does your Chrome browser seem a little “off”, but you can’t figure out why? Maybe it’s eFast. Here’s another reason to slow...
-

 76Data Security
76Data SecurityTrain rider has his contactless card e-pickpocketed
It could have been just another one of those jostlings that happen on the train: a man bumped into a writer for...
-

 193Hacked
193HackedGermany Suspects, Will Investigate Google and Facebook Over Data Transfers
Short Bytes: The European Union has many a times been apprehensive of the US-based tech companies, especially on the matters of privacy and...
-

 297Data Security
297Data SecurityFBI Wants You To “Just Pay The Ransom” to Cyber Criminals
The Federal Bureau of Investigation (FBI) has stated that it’s completely fine to pay ransom to cyber criminals. If you are a fan...
-

 131Data Security
131Data SecuritySenate Passes Controversial Cybersecurity Act
Despite its controversial nature, the US Senate has passed the Cybersecurity Information Sharing Act (CISA). Detractors are concerned because CISA would open...
-

 332Cyber Crime
332Cyber CrimeHackers Target Video Gamers with Sophisticated Phishing Scam
Video gamers have found themselves the target of a new type of scam. No malware or hacking into the games rather a simple...
-
 284Geek
284GeekNew App Aims to Cure Blindness For Visually Impaired
With computers starting to help normal human beings to navigate better around the world, robotics and AI are all set to help...
-

 275Hacked
275HackedWhich Antivirus Software Protect Themselves From Hacking Attacks?
Short Bytes: Even though the number of users aware about the basic security practices is increasing day-by-day, most of us are unaware...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




