Featured News
-
 160Malware
160MalwarePay or we’ll knock your site offline—DDoS-for-ransom attacks surge
One of the Internet’s oldest and crudest attacks experiences a resurgence. A number of sites have been hit by distributed denial-of-service attacks...
-

 286Tricks & How To's
286Tricks & How To'sHack Chat | Private Disappearing Chatrooms
If you would like to build your personal private chatting system without any hassle besides entering a different Address in your web...
-
 69Cyber Crime
69Cyber CrimeFastMail the latest victim of a sustained DDoS offensive
The premium email provider FastMail has revealed that a cybercriminal has launched multiple DDoS attacks on its systems and made a ransom...
-

 169Hacked
169HackedRussia Doesn’t Want Its Users’ Twitter Data To Leave Country
Short Bytes: Russia has yet again displayed stifling laws as it demanded the micro-blogging site Twitter to set up local data centres...
-

 237Hacked
237HackedTor Director Accuses FBI of Spending $1 Million to Attack Tor Users
Short Bytes: In a blog post, Tor Director has outlined the unethical ways that were employed by FBI to unmask Tor users....
-

 172Data Security
172Data SecurityTablets with Pre-installed Trojan Being Sold on Amazon
Recently, researchers from the Cheetah Mobile Security Lab have found a dangerous Trojan, dubbed Cloudsota, pre-installed on certain Android tablets. Tablets infected...
-

 100Incidents
100IncidentsOfficial Premier League Fantasy Website infected with malware
Soccer, or rather football aficionados in the UK may have had their computers infected whilst browsing the Premier League’s official fantasy website...
-
 282Incidents
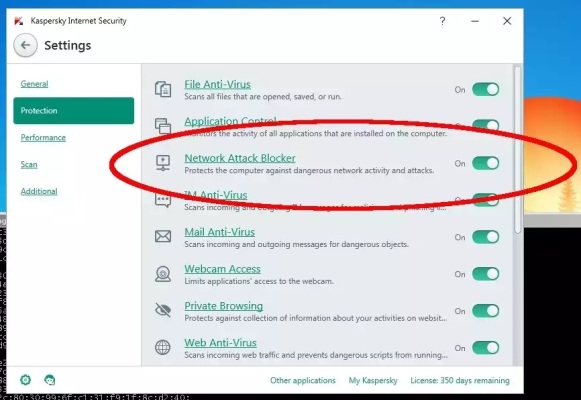
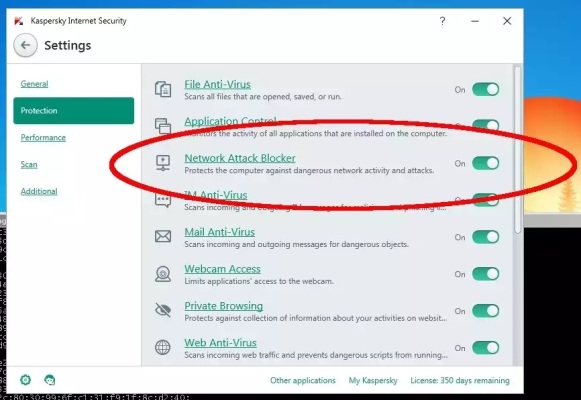
282IncidentsHackers Exploit Kaspersky, Microsoft Security Products to Install Snooping Trojan
Recently, while researching attacks on targets in Thailand, Unit 42 discovered a tool that initially appeared to be a variant of the...
-

 76Data Security
76Data SecuritySAP Security Patch for November 2015 Released
This post by SAP Product Security Response Team shares information on Patch Day Security Notes* that are released on second Tuesday of...
-

 105Incidents
105IncidentsRansomware infected the UK Parliament’s computer networks
A ransomware infected several PC at the UK Parliament, for the first time a threat hit the internal computer network, the Parliamentary...
-

 263Cyber Events
263Cyber EventsAnonymous Exposes Identity of Alleged Halifax Rapist, Police Reopens The Case
Halifax police forced to re-open investigation in a sexual assault case after Anonymous exposes the identity of the alleged culprit. The online...
-

 246Geek
246GeekHuman biology merges with technology as Biohackers implant LED’s under the skin
Biohackers have unveiled something that could be termed as “Technology for future”. The technology is a silicone implant that is LED equipped...
-

 233Tricks & How To's
233Tricks & How To's8 Firefox Add-ons used by Hackers
Ethical hacking could be great fun if you know about these add-ons. The creation of penetration testing labs in Kali Linux or...
-

 93Data Security
93Data SecurityFacebook told by Belgian court to stop tracking non-users
A court has given Facebook 48 hours to stop tracking people in Belgium who are not members of its social network. Facebook...
-
 221Malware
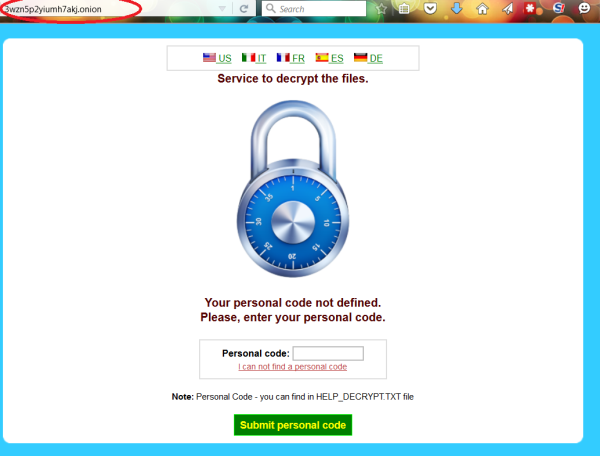
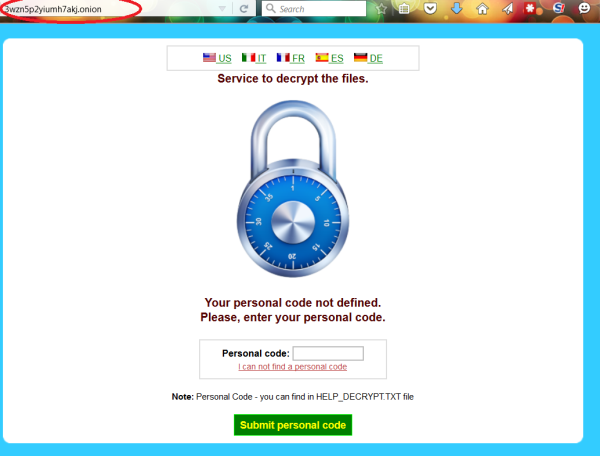
221MalwareCryptoWall 4.0 released with new Features such as Encrypted File Names
CryptoWall 4.0 has been released that displays a redesigned ransom note, new filenames, and now encrypts a file’s name along with its data. We...
-

 100Data Security
100Data SecurityFlaw in Linux.Encoder1 ransomware reveals the decryption key
Experts at Bitdefender have discovered a flaw in Linux Encryption Ransomware Linux.Encoder1 that exposes the decryption Key used to lock the files....
-

 165Data Security
165Data SecurityBadly coded ransomware locks away data forever
Coding mistakes in a malicious program that encrypts data mean anyone hit by the Power Worm virus will not be able to...
-

 88Data Security
88Data SecurityUS banks attacked, manipulated and left (heart)bleeding
In April 2014 the cybersecurity world was rocked by the discovery of Heartbleed, the name given to a vulnerability found in one...
-

 317Geek
317GeekCourt Orders Facebook to Stop Tacking Non-Users or Pay €250K Fine Daily
A Belgian court has ordered Facebook to stop tracking internet users within next 48 hours or they will impose fines of up...
-

 111Cyber Crime
111Cyber CrimeResearchers Expose Iranian Phishing Servers Targeting Opposition
A group of researchers from Checkpoint Security firm claimed that they have breached phishing servers that were used by the Rocket Kitten....
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




